Microsoft Windows 10 Ransomware Protection Details
Microsoft discloses some details about Windows 10 inbuilt ransomware protection, revealing new layers of defense against this growing threat. This new built-in protection delves into the technical aspects of ransomware detection and prevention, promising a stronger security posture for Windows 10 users. The details encompass various methods for detecting and preventing attacks, from the underlying algorithms to practical use cases.
The discussion will explore how this feature compares to existing security measures and analyze its impact on the overall system security.
The protection mechanisms detailed by Microsoft are designed to enhance the user experience while remaining effective in safeguarding against a wide range of ransomware threats. This in-depth look will cover technical details, potential limitations, and future implications, offering a comprehensive understanding of Microsoft’s approach to ransomware protection.
Overview of Windows 10 Inbuilt Ransomware Protection
Microsoft has recently disclosed details about the enhanced ransomware protection features integrated into Windows 10. These improvements aim to bolster the operating system’s defenses against increasingly sophisticated ransomware attacks, providing a layered approach to security. This enhanced protection signifies a proactive stance by Microsoft to safeguard user data and systems.
Microsoft’s recent disclosure about Windows 10’s built-in ransomware protection is interesting, but it’s worth considering other security vulnerabilities. For example, there’s been a significant security breach in Azure Cosmos DB, a cloud database service. Check out the details about the vulnerability here: Azure Cosmos DB Vulnerability Details. Knowing about these vulnerabilities helps us understand the broader security landscape, and ultimately, helps us better understand the need for robust security measures in Windows 10.
So, while the new Windows 10 ransomware protection is a step in the right direction, we need to be vigilant about potential weaknesses in other Microsoft products.
Key Features of Inbuilt Ransomware Protection
Microsoft’s enhanced ransomware protection leverages a combination of proactive and reactive measures. The key features Artikeld involve a multifaceted approach to identify and thwart attacks before they can cause significant damage. The integration of these technologies into the core OS framework provides users with an additional layer of security beyond traditional antivirus solutions.
| Feature | Description | Impact |
|---|---|---|
| File System Integrity Monitoring | This feature constantly monitors critical system files and directories for unauthorized modifications. Any suspicious activity, such as changes to essential system files, triggers an alert. This includes checking for alterations to file attributes and metadata. | Early detection of malicious activity, preventing ransomware from encrypting critical files. Potentially preventing system instability. |
| Application Control | Application Control restricts the execution of untrusted or potentially malicious applications. This is achieved by implementing a whitelist of approved applications, thereby preventing unauthorized software from running. This method can also be used to restrict the execution of malicious scripts or files. | Reduces the attack surface by limiting the execution of malicious applications, preventing exploitation of vulnerabilities. Enhanced protection against zero-day exploits. |
| Real-time Threat Detection | Advanced threat intelligence is integrated to identify and block known ransomware strains in real-time. This proactive approach is based on constantly updated threat intelligence databases. This feature is designed to block ransomware at the point of execution. | Immediate prevention of known ransomware attacks. Reduced chances of data encryption. |
| Cloud-Based Protection | Windows 10 leverages cloud-based threat intelligence to detect and respond to emerging threats. This is achieved through constant analysis of user behavior and threat patterns across the network. This allows for dynamic updates to the protection mechanisms based on real-time data. | Adaptive response to new and evolving ransomware tactics. Improved detection of unknown ransomware variants. |
| Data Loss Prevention (DLP) | Data Loss Prevention (DLP) features limit unauthorized data exfiltration and protect sensitive data from being copied or moved to unauthorized locations. This involves monitoring file access and transmission patterns. | Reduced risk of data leakage and theft, preventing unauthorized access and distribution of sensitive data. Enhanced data security by limiting the potential for lateral movement of the ransomware within the system. |
Methods of Ransomware Detection and Prevention
The protection mechanisms described utilize a combination of techniques to detect and prevent ransomware attacks.
- Behavioral Analysis: The system observes the behavior of applications to identify anomalies that could indicate malicious activity, such as unusual file access patterns or attempts to encrypt files.
- Machine Learning: Machine learning algorithms analyze vast amounts of data to identify patterns and anomalies that might indicate ransomware attacks. This learning enables the system to adapt to evolving ransomware tactics.
- Security Hardening: The OS is configured with security hardening practices, such as limiting user privileges, disabling unnecessary services, and configuring strong passwords, to reduce the attack surface.
- Anti-Evasion Techniques: The system employs techniques to detect and prevent ransomware from evading security measures, such as anti-virtualization and anti-sandbox technologies. These techniques are designed to detect the presence of malicious processes in virtualized environments or sandboxes.
Comparison with Other Security Measures
Microsoft’s recent disclosure regarding enhanced in-built ransomware protection in Windows 10 reveals a layered approach to security. This new feature sits within the broader context of existing Windows 10 security mechanisms, interacting with and potentially complementing them. Understanding how this new protection stacks up against other defenses is crucial for a complete picture of the OS’s security posture.This comparison highlights the interplay between the disclosed ransomware protection and other existing Windows 10 security layers, identifying potential overlaps and gaps in the overall security strategy.
By analyzing these interactions, we can better assess the effectiveness and completeness of the comprehensive security approach.
Existing Security Layers in Windows 10
Windows 10 boasts a robust set of built-in security layers designed to defend against various threats. These include features like Windows Defender Antivirus, the Windows Firewall, and the User Account Control (UAC) system. Each layer plays a distinct role in the overall security architecture, often working in tandem to protect against different attack vectors. These layers form a complex network of security measures that work together to defend the system.
Comparison of Ransomware Protection with Other Security Layers
The following table contrasts the disclosed ransomware protection features with existing Windows 10 security layers, illustrating their potential overlaps and differences. It highlights how each layer contributes to the overall security strategy.
| Security Feature | Description | Overlap with Ransomware Protection | Gaps/Potential Conflicts |
|---|---|---|---|
| Windows Defender Antivirus | Real-time scanning, threat detection, and removal. | Potentially overlapping in detecting malicious code, but ransomware protection focuses on preventing encryption. | Possible redundancy in some cases, requiring careful integration to avoid conflicts. |
| Windows Firewall | Controls network traffic and prevents unauthorized access. | Limited overlap, as ransomware often involves network connections for data exfiltration. Protection might focus on preventing network communication from infected machines. | May not fully address the threat if ransomware exploits vulnerabilities within the system. |
| User Account Control (UAC) | Prompts user interaction before installing software or making system changes. | Limited direct overlap. Ransomware protection can be viewed as an additional layer of control that prevents the execution of potentially malicious code. | Ransomware may still find ways to bypass UAC. The protection mechanism might require further integration with UAC for greater effectiveness. |
| Windows Information Protection (WIP) | Provides data loss prevention features. | Potentially complementary, particularly in protecting sensitive data from being encrypted by ransomware. | Effectiveness hinges on the proper configuration and use of WIP, which may not be sufficient in all scenarios. |
Potential Overlaps and Gaps in the Security Strategy
The table highlights potential overlaps between the disclosed ransomware protection and existing features like Windows Defender. However, there might be gaps where one layer doesn’t adequately address certain aspects of ransomware attacks. The firewall, for instance, may not prevent the encryption process itself if the attack originates from within the network. Future enhancements might focus on bridging these gaps and enhancing the overall effectiveness of the security ecosystem.
The approach of a multi-layered defense is essential, as no single mechanism can fully eliminate the ever-evolving threat of ransomware.
Technical Details and Implementation
Microsoft’s Windows 10 inbuilt ransomware protection isn’t a magic bullet, but rather a layered defense system. Understanding its technical underpinnings reveals a sophisticated approach to combating this ever-evolving threat. This section dives into the specific mechanisms, algorithms, and protocols that make up this integrated security layer.
Ransomware Detection Mechanisms
The core of the protection system lies in its ability to detect suspicious activity. This involves a combination of heuristic analysis and behavioral monitoring. Heuristic analysis uses predefined rules and patterns to identify potentially malicious actions. Behavioral monitoring observes file system activity, registry changes, and network communication for anomalies that might indicate ransomware. For example, rapidly encrypting numerous files across different drives is a key indicator.
File System Integrity Monitoring
Windows 10’s built-in ransomware protection closely monitors changes to the file system. This includes tracking file creation, modification, and deletion times. If the system detects rapid and unusual changes, particularly encryption operations, it triggers an alert. The system maintains a baseline of expected file system activity, enabling it to identify anomalies more effectively.
Network Traffic Analysis
Suspiciously high network activity, such as communication with known malicious IP addresses or domains, is another crucial detection method. The system analyzes network traffic patterns, looking for connections that align with ransomware tactics, such as data exfiltration or command-and-control communication. This is further reinforced by the use of blacklists and whitelists.
System-Level Monitoring
The ransomware protection extends beyond file system and network monitoring. It includes comprehensive system-level monitoring. This involves observing process behavior, registry changes, and memory allocations. This is designed to catch unusual processes that might be involved in encrypting data or communicating with external servers. For instance, a process that attempts to create hidden files across multiple locations, or one that rapidly copies large files to a network share, would be flagged.
Underlying Algorithms and Technologies
The precise algorithms employed are proprietary, but the core technologies include machine learning algorithms for anomaly detection and signature-based identification. Machine learning models are trained on vast datasets of known ransomware behaviors to identify subtle patterns and adapt to new threats.
Security Protocols and Processes
The security protocols are integrated into the Windows operating system kernel, ensuring they run in a secure environment. These protocols work in tandem to enhance detection accuracy. The system employs cryptographic hashes to verify the integrity of files, ensuring that any changes are flagged immediately.
Technical Components of Ransomware Protection
| Component | Description |
|---|---|
| File System Watcher | Monitors file system activity for unusual patterns. |
| Network Traffic Analyzer | Analyzes network communication for malicious activity. |
| System-Level Monitor | Observes process behavior, registry changes, and memory allocations. |
| Machine Learning Engine | Identifies anomalies and patterns using machine learning algorithms. |
| Cryptographic Hashing | Verifies file integrity to detect modifications. |
Impact and Effectiveness
Microsoft’s built-in ransomware protection for Windows 10 represents a significant step towards bolstering the security of user systems. Understanding its potential impact, effectiveness against various attack vectors, and any limitations is crucial for users to assess the added layer of security. This analysis delves into these aspects, providing a comprehensive overview of the protection’s capabilities.
Potential Impact on Overall Security Posture
The introduction of built-in ransomware protection directly enhances the security posture of Windows 10 systems by providing a proactive defense mechanism. It complements existing security measures, like antivirus software, by focusing specifically on ransomware threats. This proactive approach is particularly beneficial in scenarios where users may not have up-to-date antivirus software or where traditional security measures have proven insufficient.
This proactive defense could drastically reduce the likelihood of successful ransomware attacks, thereby safeguarding user data and systems.
Effectiveness Against Ransomware Attack Vectors
The effectiveness of the protection against various ransomware attack vectors depends on several factors, including the sophistication of the attack, the specific ransomware variant, and the user’s system configuration. This protection likely employs multiple layers of defense, including file system monitoring, process analysis, and network traffic inspection. For example, real-time monitoring of suspicious file operations, such as encryption attempts, can effectively prevent or mitigate the damage caused by ransomware.
Limitations and Weaknesses
While the built-in protection is a positive development, it’s crucial to acknowledge potential limitations. One potential weakness is the ability of advanced, targeted attacks to circumvent the built-in defenses. Sophisticated ransomware, designed to evade detection mechanisms, could still pose a risk. Furthermore, the effectiveness of the protection hinges on the user’s system configuration and timely updates. A poorly configured system or outdated software could create vulnerabilities that the protection might not be able to address.
Potential Ransomware Attack Scenarios and Protection Response
| Ransomware Attack Scenario | Potential Protection Response |
|---|---|
| Brute-force attack targeting known vulnerabilities | The protection should detect and block the attack, preventing the exploitation of known vulnerabilities in the system. |
| Social engineering attack targeting user credentials | The protection is likely not directly targeted at social engineering attacks. The protection mechanism focuses on the actual encryption process, not the method of gaining access to the system. A robust user awareness training program is still essential. |
| Targeted attack using zero-day exploits | The protection’s effectiveness against zero-day exploits is uncertain. The ability to detect previously unknown attack vectors depends on the system’s proactive learning mechanisms and the speed of updates. |
| Ransomware delivered via malicious email attachment | If the protection identifies a suspicious file or process associated with the email attachment, it should block the encryption process. User caution is still a critical factor. |
Future Implications and Directions
Windows 10’s built-in ransomware protection represents a significant step forward in the fight against this pervasive threat. However, the digital landscape is constantly evolving, and the future implications of these enhancements are multifaceted and require careful consideration. This section explores potential future developments, their impact on the ransomware landscape, and the direction Microsoft might take to further bolster this crucial security feature.
Potential Future Enhancements
The inherent nature of ransomware necessitates continuous adaptation. Future enhancements to Windows 10’s inbuilt protection should consider proactive measures, rather than just reactive ones. These enhancements should also be designed to adapt to emerging attack vectors and sophisticated evasion techniques. For instance, incorporating machine learning algorithms to detect and respond to zero-day exploits could significantly improve protection.
Impact on the Ransomware Landscape
The introduction of robust built-in ransomware protection in Windows 10 is likely to influence the ransomware landscape in several ways. Criminals may shift their tactics, focusing on systems not yet equipped with these protections, or develop new techniques to bypass the enhanced defenses. Alternatively, they might adapt by using more sophisticated, targeted attacks against specific industries or organizations.
This dynamic response necessitates continuous innovation in security measures.
Potential Future Enhancements and Implications
| Potential Enhancement | Implications |
|---|---|
| Integration with cloud-based threat intelligence | Improved threat detection capabilities through real-time information sharing and analysis of global attack patterns. This would allow for quicker identification and response to emerging threats, leading to a proactive security posture. |
| Advanced threat hunting capabilities | Enable automated detection and response to malicious activities beyond the scope of standard security protocols. This would enhance the ability to identify and contain threats that evade traditional detection mechanisms, thereby increasing the efficacy of ransomware protection. |
| Enhanced user awareness and education features | Integration of tools that educate users about common ransomware attack methods. This would empower users to identify and report suspicious activities, acting as a crucial line of defense against phishing attempts or social engineering tactics. |
| Improved compatibility with third-party security solutions | Enable seamless integration and collaboration between Windows 10’s inbuilt protection and existing security tools. This enhanced synergy would allow for a more comprehensive and robust defense against diverse ransomware tactics. |
Anticipated Impact on Future Attacks
The introduction of inbuilt ransomware protection in Windows 10 signals a shift in the ransomware landscape. Criminals will likely need to adjust their tactics, potentially focusing on vulnerabilities in less protected systems or employing more targeted, sophisticated attacks. The enhanced protection could potentially make mass ransomware campaigns less effective, forcing attackers to resort to more personalized, targeted approaches.
This adaptive response necessitates a constant cycle of innovation and improvement in security measures to stay ahead of evolving threats.
User Experience and Ease of Use: Microsoft Discloses Some Details About Windows 10 Inbuilt Ransomware Protection
Windows 10’s built-in ransomware protection aims for seamless integration without disrupting the user experience. The design prioritizes user-friendliness, making it accessible to both tech-savvy and less experienced users. This section delves into the specifics of how users interact with the protection features and the ease of use of the system.
Microsoft’s recent disclosure about Windows 10’s built-in ransomware protection is a step in the right direction, but the real challenge lies in proactively securing code. We need to deploy AI code safety goggles, like those discussed in Deploying AI Code Safety Goggles Needed , to identify and mitigate vulnerabilities before they become exploited. Ultimately, robust defenses like the Windows 10 features are crucial, but a proactive approach to code security is essential for a truly layered defense strategy.
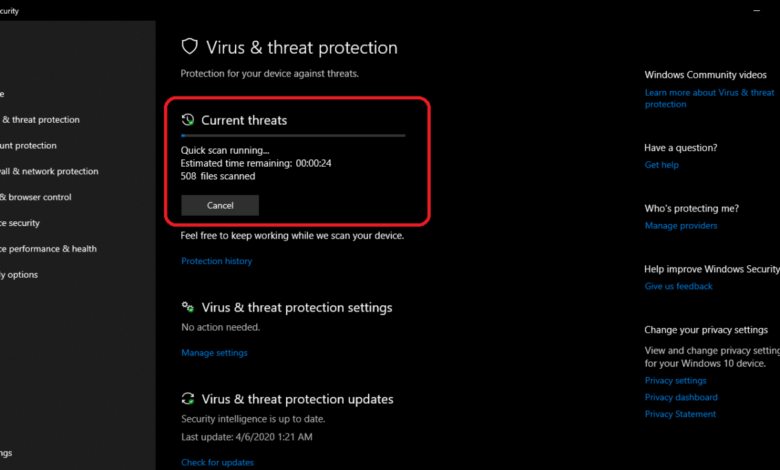
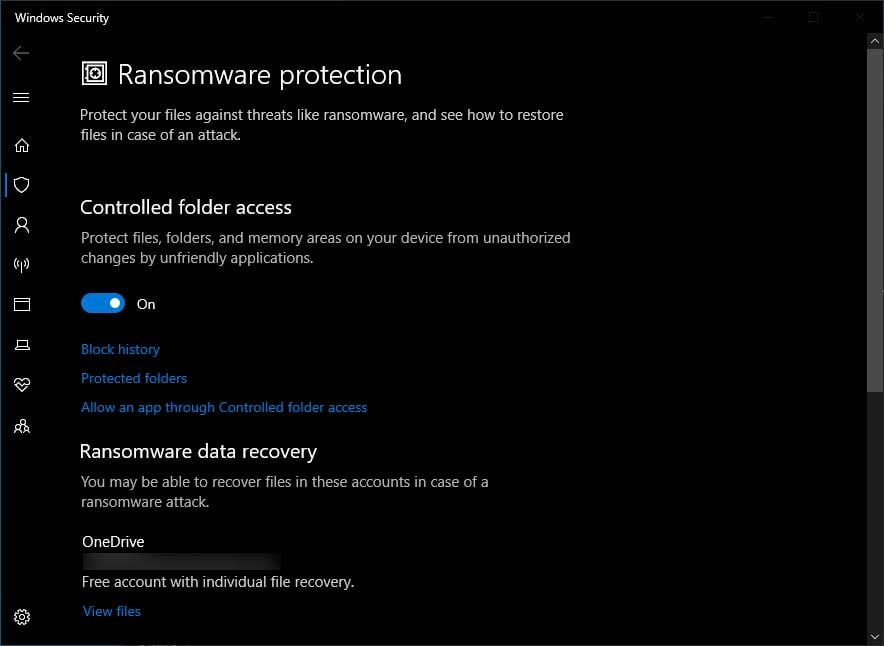
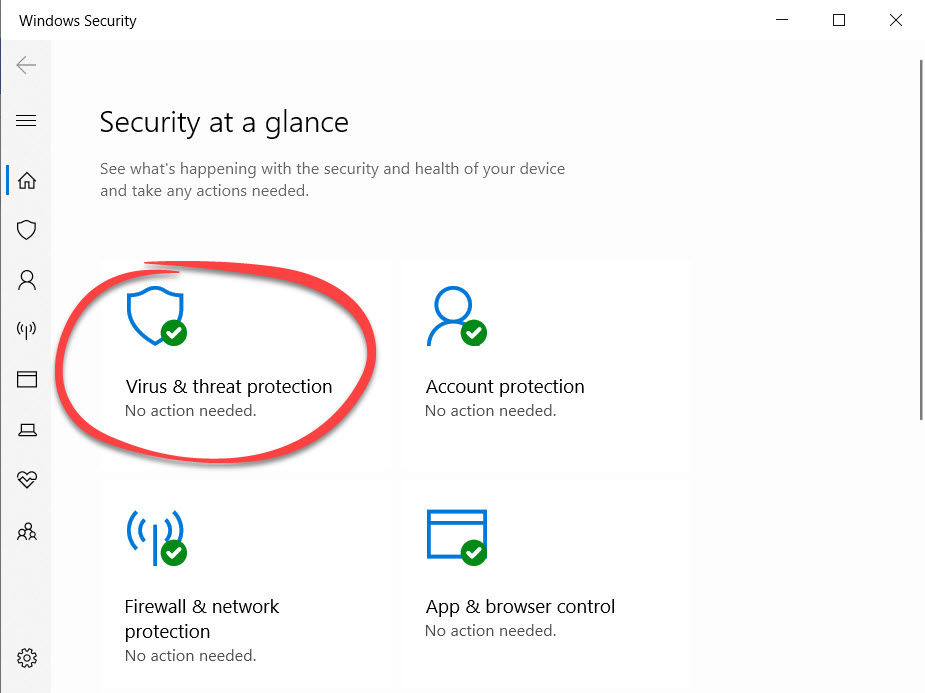
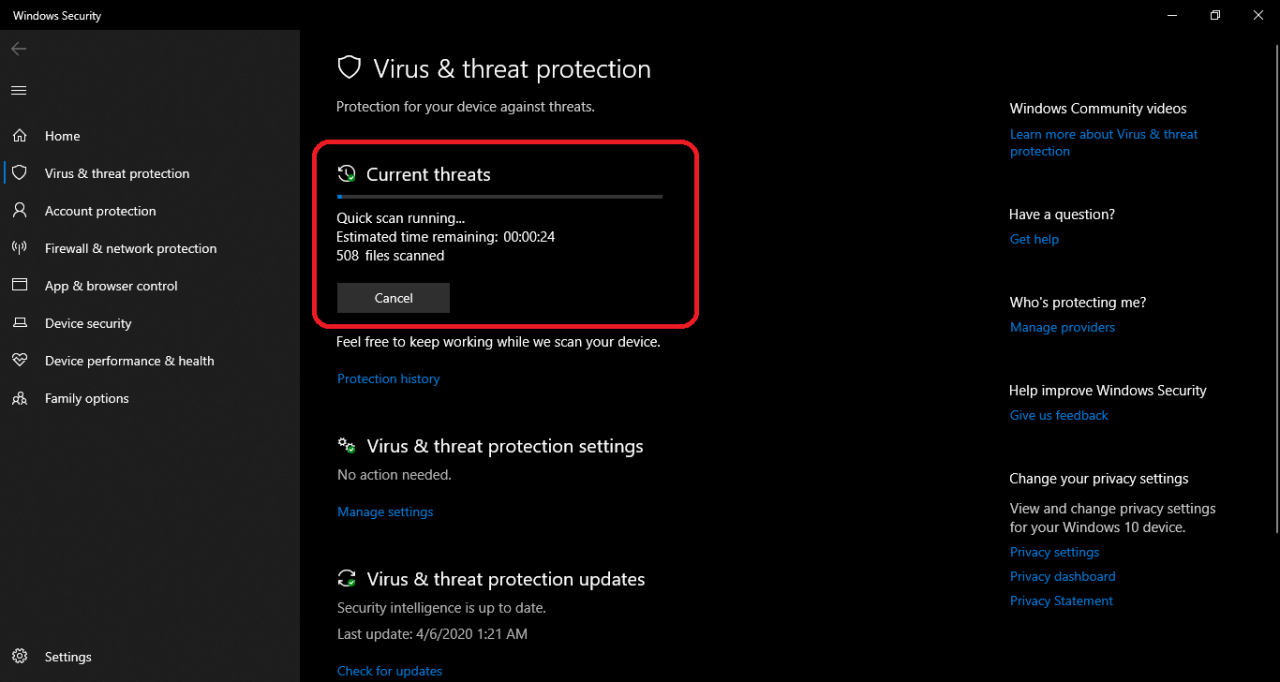
User Interface for Access and Management
The ransomware protection features are integrated into the Windows Security app. This central location provides a consolidated view of security settings, including the ransomware protection component. Navigating to the ransomware protection settings is straightforward. A dedicated section within the Windows Security app is designed to present information clearly and concisely, without unnecessary complexity. Users can quickly access and modify relevant settings.
Interaction with Protection Features
Users interact with the protection features primarily through the Windows Security app. The interface displays the status of real-time protection, allowing users to view and modify protection settings. For example, users can enable or disable the feature, or customize the behavior for different file types or locations. The system offers a straightforward method to check for suspicious activities and react to potential threats.
Ease of Use and Intuitiveness
The design of the ransomware protection features prioritizes simplicity and clarity. The user interface is intuitive, guiding users through the process of configuring and managing the protection. Minimal technical jargon is used, ensuring accessibility for all users. The system’s design emphasizes clear visual cues, such as status indicators and progress bars, to provide a clear understanding of the protection status and any actions in progress.
Simple language is used in pop-up messages and notifications.
Specific Examples of User Interactions
- Enabling or disabling real-time protection is done via a simple toggle switch.
- Setting exclusions for specific files or folders involves a clear path selection process.
- Viewing protection logs and reports displays information in a user-friendly format, without requiring extensive technical expertise.
Security Notifications and Alerts
The system uses clear and concise notifications to inform users about potential threats. Notifications are categorized to distinguish between various types of events, from routine protection actions to potential ransomware activity. These notifications provide essential context and guidance to users, helping them understand and respond to security alerts appropriately.
Potential Threats and Mitigation Strategies
Windows 10’s built-in ransomware protection represents a significant step forward in user security, but no system is impenetrable. Understanding potential vulnerabilities and developing robust countermeasures is crucial for maximizing the protection offered by these tools. This section delves into specific threats that might bypass the built-in defenses and Artikels strategies to mitigate these risks.
Potential Bypasses of Inbuilt Protection
Built-in ransomware protection systems, while effective against many threats, are not foolproof. Sophisticated attackers often employ techniques to evade detection and exploit vulnerabilities. These vulnerabilities may stem from either weaknesses in the protection mechanisms themselves or from exploiting weaknesses in the operating system or applications that the protection system interacts with.
Advanced Ransomware Techniques
Ransomware attacks are constantly evolving, adapting to new security measures. Attackers employ various tactics, including:
- Exploiting Zero-Day Vulnerabilities: These are previously unknown software flaws that attackers can leverage to gain unauthorized access. The rapid pace of software development and deployment means these vulnerabilities are a constant concern.
- Using Polymorphic Malware: This malware changes its code structure frequently to evade signature-based detection systems. Traditional antivirus software often struggles to identify and contain this type of threat.
- Targeting Specific Vulnerabilities in Applications: Ransomware may exploit vulnerabilities within specific applications used by a user or organization. This includes targeting software for financial institutions, healthcare, or other sensitive sectors.
- Supply Chain Attacks: This involves compromising a trusted software vendor or supplier, embedding malicious code into legitimate software updates, and distributing it to a wide range of users.
- Using Social Engineering Techniques: Attackers often use social engineering tactics, tricking users into clicking malicious links or downloading infected files. This can bypass security measures even if the software is properly updated.
Mitigation Strategies
To combat these sophisticated threats, a multi-layered approach is crucial. This includes not only the inbuilt protection but also proactive measures from the user.
| Threat | Description | Countermeasure |
|---|---|---|
| Exploiting Zero-Day Vulnerabilities | Attackers leverage unknown software flaws to gain unauthorized access. | Regularly updating software and operating systems, using security patches as soon as they become available, and employing vulnerability scanning tools. |
| Polymorphic Malware | Malware constantly changes its code to evade signature-based detection. | Using a layered security approach that combines signature-based detection with behavioral analysis, sandboxing, and machine learning-based detection. |
| Targeting Specific Application Vulnerabilities | Exploiting vulnerabilities within specific applications. | Keeping applications updated, using application whitelisting, and implementing strong access controls. |
| Supply Chain Attacks | Compromising a trusted software vendor to distribute malicious code. | Verifying the authenticity of software updates, using secure software development practices, and conducting thorough due diligence on software vendors. |
| Social Engineering Techniques | Tricking users into clicking malicious links or downloading infected files. | Educating users on phishing tactics, providing security awareness training, and implementing multi-factor authentication (MFA). |
Example of Advanced Ransomware Techniques
The Ryuk ransomware, for instance, is known for its sophisticated targeting and ability to evade traditional security measures. It often targets specific vulnerabilities within organizations, often involving supply chain compromises, to gain access to sensitive data and systems. Mitigating such attacks requires a strong combination of robust security measures and awareness training for personnel.
Practical Application and Use Cases
Windows 10’s built-in ransomware protection, a crucial component of its security architecture, offers a layered approach to safeguarding user data. This proactive defense system aims to mitigate the risk of ransomware attacks, a significant threat to individuals and organizations alike. Understanding how this protection functions in real-world scenarios is essential for effectively leveraging its capabilities.The system operates by continuously monitoring for suspicious activity, such as file encryption patterns, and employing various security measures to prevent or contain potential attacks.
This proactive approach is vital for maintaining data integrity and business continuity.
Real-World Scenario Examples
The efficacy of Windows 10’s ransomware protection can be demonstrated through various real-world scenarios. Consider these illustrative examples:
- Home User Scenario: A home user browsing the internet downloads a seemingly harmless document. The document, however, is a disguised ransomware attack. The inbuilt protection system detects the suspicious encryption pattern and isolates the infected file, preventing the ransomware from encrypting other files on the system. The user’s personal documents and data remain intact.
- Small Business Scenario: A small business utilizes a shared network drive for storing critical financial data. A malicious actor launches a targeted ransomware attack on the network, aiming to encrypt sensitive financial information. The Windows 10 ransomware protection identifies the encryption attempt, quarantines the compromised drive, and notifies the administrator. The business is able to quickly restore from backups, preventing substantial financial loss.
- Enterprise Scenario: A large corporation utilizes a cloud-based file storage system for employee collaboration. A sophisticated ransomware attack targets the cloud storage, attempting to encrypt shared files. The protection system, integrated with the cloud storage provider’s security measures, detects the unusual activity, isolates the affected files, and informs the security team. The enterprise avoids widespread data breaches and maintains operational continuity.
Response to Different Attack Types
The ransomware protection mechanism in Windows 10 is designed to address various types of ransomware attacks, leveraging a combination of heuristics and signature-based detection. This multi-faceted approach is essential for combating the evolving nature of ransomware threats.
- Traditional Encryption Ransomware: This type of ransomware typically encrypts files on the system’s hard drive. The Windows 10 protection system detects this encryption pattern, isolates the compromised files, and prevents further spread to other files. The system also alerts the user to the potential threat.
- Ransomware-as-a-Service (RaaS): RaaS allows attackers to utilize pre-built ransomware tools, often employing sophisticated obfuscation techniques. The Windows 10 protection, equipped with advanced threat intelligence, identifies the malicious activity associated with RaaS attacks and takes preventive actions.
- Supply Chain Attacks: Ransomware can infiltrate a system through seemingly legitimate applications or software updates. The Windows 10 protection system can detect unusual activity, such as unauthorized access attempts or changes to critical system files, mitigating the risk of these supply chain attacks.
Specific Use Cases
The Windows 10 ransomware protection demonstrates diverse application in various user contexts, emphasizing its broad applicability.
- Education Institutions: Schools and universities can leverage the protection to safeguard student data and critical educational resources from ransomware attacks. The system alerts the IT department, enabling swift response and minimizing disruption.
- Healthcare Facilities: Protecting patient data is paramount in healthcare. Windows 10 protection assists in preventing ransomware from encrypting sensitive medical records, ensuring patient confidentiality and continuity of care.
- Government Agencies: Government agencies handle sensitive data, making them vulnerable to ransomware attacks. The protection system aids in safeguarding crucial records and preventing disruption of essential services.
Security Best Practices
Leveraging Windows 10’s built-in ransomware protection is a crucial first step, but maximizing its effectiveness requires a multi-faceted approach. This section Artikels essential security best practices for users to bolster their protection beyond the inherent features. These practices not only enhance the security posture but also contribute to a more resilient digital environment.Implementing a robust security strategy involves more than just software; it encompasses user behavior and proactive measures.
Understanding and applying these best practices is key to mitigating risks and maintaining a secure digital ecosystem.
Backup and Recovery Strategies
Regular backups are paramount for mitigating the impact of ransomware attacks. Data loss can be devastating, and a robust backup strategy ensures swift recovery. This proactive approach allows users to restore data quickly and minimize downtime.
Microsoft’s recent disclosure about enhanced ransomware protection in Windows 10 is certainly intriguing. It’s fascinating how these security measures are evolving, and this development could significantly impact the cybersecurity landscape. Interestingly, the Department of Justice’s recent “Safe Harbor” policy for Massachusetts transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) might offer some parallels, potentially impacting how businesses approach data security.
Ultimately, Microsoft’s efforts to bolster Windows 10’s resilience against ransomware attacks are promising, and I’m keen to see how these new features perform in the field.
- Regular Data Backups: Implement a consistent backup schedule, backing up critical data to an external hard drive, cloud storage, or a network share. Test the restoration process periodically to ensure data integrity.
- Redundancy: Consider implementing redundant backup systems. Having multiple backup locations safeguards against failures in a single backup repository. This could involve backing up to the cloud
-and* an external hard drive. - Version Control: Utilize version control systems for critical files. This allows users to revert to previous versions in case of accidental modifications or ransomware attacks.
Strong Password Management
Strong passwords are the first line of defense against unauthorized access. A well-managed password system minimizes the risk of breaches and subsequent data compromises. Implement strong password policies, and utilize password managers to avoid the risk of weak or reused passwords.
- Complex Passwords: Employ a combination of uppercase and lowercase letters, numbers, and symbols for passwords. Avoid using easily guessable words or personal information.
- Unique Passwords: Use unique passwords for each account. Do not reuse passwords across different platforms. Password managers automate this process and provide secure storage for sensitive information.
- Two-Factor Authentication (2FA): Implement 2FA wherever possible. This adds an extra layer of security by requiring a second verification method beyond a password.
Security Awareness Training
User education plays a significant role in a comprehensive security strategy. Empowering users with the knowledge to recognize and avoid phishing attempts and malicious software is essential. Regular security awareness training can mitigate risks associated with social engineering attacks.
- Phishing Awareness: Educate users on how to identify phishing emails, messages, and websites. Train them to report suspicious communications promptly.
- Software Updates: Encourage the regular installation of software updates. Updates often include security patches that address vulnerabilities. Set up automatic updates where possible.
- Suspicious Links: Advise users to exercise caution when clicking on unknown links or downloading attachments from untrusted sources. Verify the source before opening or downloading.
Software and Application Management, Microsoft discloses some details about windows 10 inbuilt ransomware protection
Proactive management of software and applications can significantly reduce the attack surface. This includes keeping software updated and only installing trusted applications. Regularly scanning systems for malware and vulnerabilities can proactively identify and address potential issues.
- Regular Security Scans: Regularly scan systems for malware and vulnerabilities using reputable security software. Schedule these scans as part of your routine maintenance.
- Install Security Software: Implement reputable antivirus and anti-malware software. Ensure that this software is updated regularly.
- Principle of Least Privilege: Grant users only the necessary access rights to perform their job functions. Limit access to sensitive data to authorized personnel.
Closing Summary
In conclusion, Microsoft’s disclosed enhancements to Windows 10’s inbuilt ransomware protection present a significant step towards bolstering system security. While the details provide a strong foundation, understanding the potential limitations and threats is crucial. Users can effectively utilize this new layer of defense by combining it with security best practices, thus achieving a more robust security posture. The future of ransomware protection hinges on continuous innovation, and Microsoft’s approach demonstrates a commitment to addressing this evolving threat.
Essential FAQs
What are the key features of the new ransomware protection?
Microsoft has disclosed key features such as enhanced detection algorithms, proactive prevention measures, and improved user interaction with the protection tools. Specific details are not yet available publicly, but the overall aim is to improve the system’s ability to detect and respond to a wider range of ransomware attacks.
How does this protection compare to other Windows 10 security features?
The new ransomware protection complements existing security measures by focusing specifically on ransomware attacks. It likely integrates with, but operates independently of, features like Windows Defender, offering a layered approach to security.
What are some potential limitations of the protection?
While the disclosed features seem robust, there may be limitations in handling advanced or zero-day ransomware attacks. Future updates and patches will be key to addressing these vulnerabilities as they emerge.
How can users enhance their security posture beyond the inbuilt features?
Users can supplement the inbuilt protection by employing strong passwords, practicing cautious online behavior, and regularly updating their software and security applications. Staying informed about the latest threats and security advisories is essential.




