-
Cloud Computing
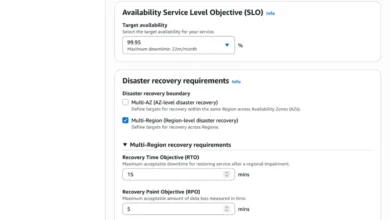
AWS Resilience Hub Unveils Next Generation with Advanced Application Modeling, Dependency Discovery, and AI-Powered Failure Analysis
The next generation of AWS Resilience Hub has been announced, introducing a significantly expanded experience that integrates a new application…
Read More » -
Cloud Computing
AWS Transform Marks One-Year Milestone, Revolutionizing Enterprise Application Modernization with Agentic AI
Exactly one year after its initial launch, AWS Transform has emerged as a pivotal force in the realm of enterprise…
Read More » -
Mobile Application Development
Google Unveils New Android Contact Picker to Strengthen Privacy and User Control in Android 17
Google has officially announced the introduction of a new Android Contact Picker, a significant privacy-focused update set to debut with…
Read More » -
Mobile Application Development
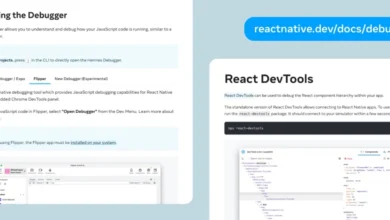
React Native 0.73 Debuts with Enhanced Debugging Tools Android 14 Support and the Launch of Bridgeless Mode
The React Native core team has officially announced the release of version 0.73, marking a significant milestone in the framework’s…
Read More » -
Indonesian National News

Minister of Home Affairs Muhammad Tito Karnavian Oversees Significant Financial Aid Handover for Aceh’s Post-Disaster Recovery Efforts.
In a pivotal demonstration of national solidarity and inter-regional cooperation, Minister of Home Affairs Muhammad Tito Karnavian, acting as the…
Read More » -
Information Technology (Indonesia)

Google to Pay $135 Million in Android Data Privacy Class-Action Settlement Affecting Millions of U.S. Users
Millions of Android users across the United States are poised to receive payments from a landmark $135 million (approximately Rp…
Read More » -
Business & Finance (Indonesia)

Jakarta Composite Index Closes in Red Amidst Escalating Geopolitical Tensions in Strait of Hormuz and Anticipation of Bank Indonesia’s Rate Decision.
The Jakarta Composite Index (IHSG) concluded Monday’s trading session on April 20, 2026, in negative territory, registering a decline of…
Read More » -
Software Development

The Evolving Landscape of AI in Software Development: A Multifaceted Examination
The rapid integration of artificial intelligence into software development is fundamentally reshaping how code is created, verified, and understood. Recent…
Read More » -
Business & Finance (Indonesia)

Banyuwangi Solidifies Status as National Food Basket with Robust First Planting Season Rice Harvest, Projecting Continued Surplus in 2026
Banyuwangi Regency, widely recognized as a pivotal national food basket for Indonesia, has commenced its First Planting Season (MT1) rice…
Read More » -
Software Development

The Shifting Landscape of Software Engineering: From Creation to Supervision in the Age of AI
The rapid integration of Artificial Intelligence into software development workflows is fundamentally altering the role of the professional software engineer,…
Read More »
