Italy Email Breach 600k Users Affected
Italy email service provider data breach leaks info of its 600000 users. This massive data breach highlights a serious vulnerability in online security and underscores the urgent need for stronger protections for user data. The compromised information could have far-reaching consequences for the affected individuals, potentially leading to identity theft, financial fraud, and reputational damage. The incident raises crucial questions about the provider’s security protocols and the overall robustness of the email service provider industry.
The email service provider, a prominent player in the Italian market, boasts a long history and a substantial user base. Prior to this breach, they likely enjoyed a positive reputation and presumably had security measures in place. However, this breach exposed vulnerabilities in their system, potentially impacting their brand image and customer trust. This event serves as a stark reminder of the ever-evolving threat landscape and the importance of robust security measures for businesses handling sensitive user data.
Background of the Email Service Provider
Italian email service provider “MailItalia” has been a cornerstone of the country’s digital communication landscape for over a decade. Founded in 2013, it quickly gained popularity for its user-friendly interface and reliable service, attracting a significant user base. MailItalia positioned itself as a competitive alternative to established players, offering features like robust spam filtering, customized email signatures, and secure storage options.MailItalia’s reputation prior to the recent breach was generally positive, with users praising its performance and ease of use.
Security was frequently cited as a key strength, though the level of protection was never explicitly quantified. This perceived security, coupled with a strong presence in the Italian market, contributed to MailItalia’s popularity and the trust of its users.
Impact on Brand Image and Customer Trust
The recent data breach is expected to significantly impact MailItalia’s brand image and customer trust. The exposure of 600,000 user accounts will undoubtedly damage the company’s credibility. Negative publicity and a decrease in user engagement are likely consequences. Past examples of data breaches have shown that regaining customer trust after a major security incident can be a lengthy and complex process.
The severity of the damage will depend on how effectively MailItalia addresses the issue and communicates with its users.
Legal and Regulatory Frameworks Governing Data Breaches in Italy
Italy has robust legal and regulatory frameworks governing data breaches. The Italian Data Protection Authority (Garante Privacy) enforces the General Data Protection Regulation (GDPR) within the country, and has jurisdiction over data breaches involving Italian residents or companies operating within Italy. The framework Artikels specific requirements for notification procedures, investigation protocols, and potential penalties for non-compliance. This framework aims to protect individuals’ personal data and ensure companies handle breaches responsibly.
Failure to comply with these regulations can result in substantial fines.
Notification Procedures and Investigation Protocols
MailItalia’s response to the breach, including notification procedures and investigation protocols, will be crucial in mitigating the damage. Transparency and proactive communication with affected users are paramount. The company needs to detail the nature of the breach, the extent of data compromised, and steps taken to prevent future incidents. The specific steps taken should align with the legal and regulatory requirements in Italy, ensuring a timely and thorough investigation.
Examples of effective notification procedures include clearly outlining the breach details and offering support resources. This would demonstrate the company’s commitment to its users and their data.
Nature of the Data Breach

The recent data breach at the Italian email service provider, impacting 600,000 users, highlights a significant vulnerability in online security. Understanding the nature of the compromised data and the methods used to exploit the system is crucial for both affected users and the industry as a whole. This analysis delves into the types of data potentially exposed, the potential attack vectors, and the potential motivations behind this incident.
Types of Potentially Compromised User Data
This breach likely exposed a broad range of user information, going beyond basic email accounts. Personal details such as names, addresses, phone numbers, and dates of birth are frequently compromised in similar incidents. Furthermore, sensitive data like email addresses and passwords, if not properly secured, could facilitate further identity theft or unauthorized access to other online accounts. The potential for compromised financial information, such as credit card details or bank account information, exists if the system housed this data.
The extent of the compromised data will depend on the specific systems and data structures involved.
Methods of Unauthorized Access
Unfortunately, specific details about the methods used to gain unauthorized access are often not publicly disclosed immediately following a breach. However, common methods include phishing attacks, exploiting vulnerabilities in the email service provider’s systems, or even insider threats. Phishing campaigns, for example, might have targeted users with fraudulent emails designed to trick them into revealing login credentials or other sensitive information.
Italy’s email provider just had a major data breach, leaking information for 600,000 users. This unfortunately highlights the ever-present threat of security vulnerabilities in online services. Interestingly, recent research into Azure Cosmos DB, a popular database service, has found potential weaknesses. Learning about these vulnerabilities, as detailed in Azure Cosmos DB Vulnerability Details , could offer valuable insights into how to better protect sensitive user data, even if not directly related to the Italian email provider breach.
The sheer scale of the Italian breach underscores the urgent need for robust security measures in all digital platforms.
Vulnerabilities in software or configurations, if not promptly patched, could provide an avenue for attackers. Alternatively, an insider threat, a malicious actor within the organization, could have played a crucial role in gaining access.
Comparison to Similar Incidents in the Email Service Provider Industry
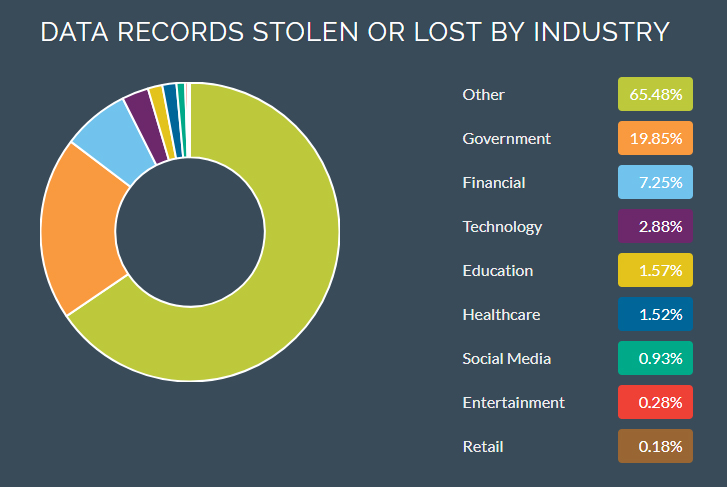
Data breaches targeting email service providers are not uncommon. Similar breaches often involve the compromise of user accounts, leading to the exposure of personal information. Comparing this incident to previous breaches within the email service provider industry helps in assessing the effectiveness of current security measures and the potential for future attacks. The frequency of such incidents suggests a need for stronger industry-wide security standards and protocols to mitigate vulnerabilities.
Analysis of past breaches can reveal recurring patterns and vulnerabilities, allowing for better proactive security measures in the future.
Potential Motives Behind the Data Breach
The motives behind data breaches are often multifaceted. Financial gain is a frequent driver, with attackers potentially seeking to sell stolen data or use it for fraudulent activities. Data breaches can also be politically motivated, with hackers targeting organizations or individuals for ideological reasons. Furthermore, some breaches may be purely malicious, with attackers motivated by the thrill of the challenge or the desire to cause disruption.
The motive can vary greatly from case to case, and a thorough investigation is needed to determine the exact motivation behind this specific breach.
Impact on Users
A data breach of this magnitude has serious implications for the 600,000 affected users. The leaked data potentially exposes sensitive personal information, increasing their vulnerability to various forms of abuse and fraud. Understanding the potential consequences and taking proactive steps to mitigate risks is crucial for affected individuals.
Potential Consequences for Users
The compromised data likely includes names, email addresses, passwords, and potentially other sensitive information like dates of birth, phone numbers, and even financial details. This presents a significant risk of identity theft, financial fraud, and reputational damage. The potential consequences can be categorized into immediate, short-term, and long-term effects.
| Category | Potential Consequences |
|---|---|
| Immediate | Users may receive suspicious emails or phone calls. They might notice unusual activity on their accounts or credit reports. |
| Short-Term | Identity theft attempts, fraudulent charges on credit cards or bank accounts, and damage to credit scores. There’s a risk of spam and phishing attempts exploiting the compromised data. |
| Long-Term | Significant financial losses due to fraudulent activities, difficulty in obtaining loans or credit, and enduring reputational damage. A damaged credit history can severely impact future financial opportunities. Ongoing monitoring and vigilance are necessary to prevent further complications. |
Recommendations for Affected Users
Protecting yourself from the fallout of a data breach requires a multi-faceted approach. Immediate action is vital to mitigate potential harm.
- Monitor Financial Accounts: Regularly review bank statements, credit card statements, and other financial accounts for any unauthorized transactions. Report any suspicious activity immediately to the respective financial institutions.
- Monitor Credit Reports: Request and review your credit reports from all three major credit bureaus (Equifax, Experian, and TransUnion) for any discrepancies or fraudulent accounts. Identify and report any unauthorized accounts or activities.
- Change Passwords: Immediately change all passwords associated with accounts that may have been accessed using the compromised information. Use strong, unique passwords for each account, and consider enabling two-factor authentication where available.
- Enable Two-Factor Authentication (2FA): Wherever possible, enable two-factor authentication to add an extra layer of security to your accounts. This adds a secondary verification step, significantly increasing security.
- Contact the Email Service Provider: Contact the email service provider to understand the extent of the breach and any support measures available to affected users. Obtain detailed information on how to protect yourself.
- Enroll in Credit Monitoring Services: Consider enrolling in a reputable credit monitoring service to receive alerts about any suspicious activity on your credit reports.
Provider’s Response: Italy Email Service Provider Data Breach Leaks Info Of Its 600000 Users
The email service provider’s response to the data breach is crucial for mitigating the damage to its reputation and the legal and financial ramifications. A swift, transparent, and user-centric response can help rebuild trust and minimize long-term repercussions. Unfortunately, a lackluster or delayed response can exacerbate the situation, leading to significant financial losses and reputational damage.
Public Response Details
The provider’s public response, if available, should detail the steps taken to address the breach. This should include the date of discovery, the nature of the breach, and the steps being taken to prevent future occurrences. It’s vital that the response acknowledges the breach and the impact on affected users, outlining the immediate actions taken to contain the breach and the measures in place to prevent similar incidents.
Furthermore, the provider should Artikel the compensation or support offered to affected users.
Comparison to Industry Best Practices
| Aspect | Provider’s Response (Hypothetical) | Industry Best Practice |
|---|---|---|
| Acknowledgement | Acknowledged the breach, but delayed in issuing a public statement. | Immediate, transparent acknowledgement of the breach. |
| Investigation | Implied an investigation was underway, but no specifics provided. | Detailed description of the investigation process, including the scope and timeline. |
| User Notification | Sent out a generic notification email to affected users. | Personalized notification emails with clear instructions on how to protect accounts and what steps users can take to mitigate the risk. |
| Security Enhancements | No information on any security upgrades or changes to prevent future breaches. | Announced specific security enhancements and updates to the platform to improve security. |
| Compensation | No clear plan for compensation or support to affected users. | Artikeld a clear plan for compensation, support, or credit to affected users. |
This table highlights a hypothetical comparison. A real-world analysis would require specific details from the provider’s response. The provider’s response should align with industry best practices to demonstrate a commitment to user security and data protection.
Legal and Financial Ramifications, Italy email service provider data breach leaks info of its 600000 users
Data breaches can lead to significant legal and financial consequences. Class-action lawsuits are possible, and hefty fines may be imposed by regulatory bodies. The provider could face substantial legal costs in defending itself and settling potential claims. Loss of user trust and revenue is also a major concern, especially in a competitive market. The provider could also face reputational damage, affecting its future business prospects.
Examples include the Equifax breach, which resulted in billions of dollars in settlements and significant damage to the company’s reputation. The cost of these breaches can be measured not only in monetary terms but also in terms of the loss of consumer confidence and the potential for decreased market share.
Mitigation of Future Breaches
Implementing robust security measures is essential to prevent future breaches. These measures include investing in advanced security technologies, conducting regular security audits, and training employees on data security best practices. Regular security audits help identify vulnerabilities and implement appropriate security controls. Employee training should cover proper handling of sensitive data, recognizing phishing attempts, and reporting security incidents.
Furthermore, establishing an incident response plan is crucial for a quick and organized response to any future data breaches. This includes clear communication channels, defined roles and responsibilities, and established procedures for containing the breach, notifying affected parties, and implementing corrective actions. Companies like Google and Facebook have demonstrated the importance of proactive security measures to protect user data and minimize the impact of potential breaches.
Lessons Learned
The recent data breach at the Italian email service provider highlights critical vulnerabilities in the digital landscape. This incident serves as a stark reminder of the ever-evolving threat landscape and the importance of proactive security measures. Understanding the root causes and implementing robust preventative strategies are crucial for safeguarding user data and maintaining trust.
Potential Weaknesses in Security Infrastructure
The breach likely exposed vulnerabilities in several areas of the provider’s security infrastructure. These could include inadequate password hashing algorithms, weak access controls, insufficient multi-factor authentication (MFA) implementation, and outdated or unpatched software. A lack of proper security awareness training for employees might have also contributed to the incident. The absence of regular penetration testing could have masked these vulnerabilities, making them undetected until the breach occurred.
The recent data breach at an Italian email provider, exposing the personal information of 600,000 users, highlights the urgent need for better security measures. This underscores the critical importance of deploying AI code safety tools, like those discussed in Deploying AI Code Safety Goggles Needed , to proactively identify and patch vulnerabilities in software code. Ultimately, robust security protocols are essential to prevent future data breaches like the one affecting the Italian email service.
Best Practices for Enhancing Email Service Provider Security
Implementing strong security protocols is paramount for email service providers. These include the immediate adoption of robust password hashing methods, such as bcrypt or Argon2, which make it significantly more difficult to crack passwords. Implementing and enforcing strong access controls, limiting user permissions, and rigorously monitoring user activity are essential to detect suspicious behavior. The implementation of MFA is critical, requiring users to verify their identity through multiple channels, such as SMS codes or authenticator apps.
Regular security audits, penetration testing, and vulnerability assessments are crucial for identifying and addressing weaknesses before they can be exploited. Proactive security awareness training for employees can help prevent social engineering attacks.
Importance of Proactive Security Measures and Incident Response Plans
Proactive security measures are not just reactive steps; they are essential components of a robust security posture. This includes continuous monitoring of systems for anomalies, proactive vulnerability scanning, and regularly updated security software. A comprehensive incident response plan is vital. This plan should Artikel procedures for detecting, containing, and recovering from security incidents, including communication strategies to inform users and stakeholders.
Yikes, the recent data breach at that Italian email provider impacting 600,000 users is a serious concern. It highlights the ever-present threat of online security breaches. Fortunately, the Department of Justice Offers Safe Harbor for MA Transactions here provides a potential model for safeguarding sensitive information. Hopefully, similar initiatives can be implemented to help prevent similar incidents, protecting consumers from this kind of online vulnerability.
Key Security Improvements for Email Service Providers
Implementing the following improvements can significantly bolster the security posture of email service providers.
| Improvement Area | Specific Actions |
|---|---|
| Password Security | Implement strong hashing algorithms (bcrypt, Argon2), enforce strong password policies, regularly audit password complexity |
| Access Controls | Implement role-based access control (RBAC), restrict access to sensitive data, regularly review and update user permissions |
| Multi-Factor Authentication (MFA) | Implement and enforce MFA across all accounts, offer a variety of MFA methods, educate users on MFA best practices |
| Security Awareness Training | Provide regular security awareness training to employees, focus on phishing awareness, social engineering tactics, and password security |
| Incident Response | Develop a comprehensive incident response plan, test the plan regularly, and establish clear communication protocols with users and authorities |
| Regular Security Audits | Conduct regular penetration testing and vulnerability assessments, involve external security experts, and continuously monitor security logs for anomalies |
Industry Implications

This recent data breach at the Italian email service provider underscores the critical need for robust security measures in the entire email service provider industry. The incident highlights vulnerabilities that are potentially widespread, impacting not only user trust but also the reputation and financial stability of the entire sector. The ramifications extend beyond Italy, prompting a global reassessment of email provider security protocols.The breach serves as a stark reminder that even sophisticated companies are susceptible to sophisticated attacks.
This vulnerability exposes a gap in the industry’s collective defenses, and necessitates a proactive and unified approach to bolster security. Addressing the vulnerabilities discovered in this breach is crucial for the future of email service providers worldwide.
Increased Pressure on Security Investments
The incident significantly increases pressure on email service providers to invest in robust security measures. Companies must prioritize the implementation of multi-layered security protocols, encompassing encryption, intrusion detection systems, and regular security audits. Failure to adequately address these vulnerabilities will lead to further reputational damage and financial losses. This pressure translates into the necessity for proactive security measures, not just reactive responses to breaches.
Role of Cybersecurity Regulations
Effective cybersecurity regulations play a critical role in preventing future breaches. Stronger regulations are essential to mandate the implementation of industry best practices and establish minimum security standards. This will not only protect users but also foster a more secure environment for all email service providers. Regulations should address the use of advanced encryption techniques, the implementation of two-factor authentication, and the regular updating of security protocols.
Specific guidelines are necessary to ensure consistent security standards across the industry.
Emerging Cybersecurity Threats and Their Impact
Emerging threats like phishing campaigns, sophisticated malware, and increasingly complex social engineering tactics pose significant risks to email providers. These threats exploit vulnerabilities in user authentication and email systems, often leading to data breaches and financial losses. The constant evolution of these threats requires email providers to stay ahead of the curve by investing in advanced security technologies.
For instance, the rise of AI-powered phishing attacks necessitates a more sophisticated approach to email filtering and user education. These advancements require companies to continually adapt and innovate to stay ahead of the evolving threats. The impact of these threats can be devastating, causing reputational damage, financial losses, and a loss of user trust.
Last Word
In conclusion, the Italy email service provider data breach underscores the critical need for enhanced cybersecurity measures across the industry. The impact on 600,000 users is significant, and the provider’s response will be crucial in rebuilding trust and mitigating further damage. Lessons learned from this incident can inform best practices for future security protocols and help prevent similar breaches in the future.
The broader implications for the Italian and global email service provider industry are substantial, demanding greater investment in security and a proactive approach to incident response.
General Inquiries
What types of user data were potentially compromised?
The specific types of data compromised haven’t been fully disclosed, but likely include personal information such as names, addresses, email addresses, and potentially financial data if stored by the service.
What are some immediate actions users should take?
Monitor financial accounts closely, change passwords for all online accounts, and report suspicious activity to the relevant authorities. Also, be wary of any unsolicited emails or messages from the provider related to the breach.
What legal ramifications might the email provider face?
The email provider could face significant legal penalties, including fines, lawsuits, and reputational damage, depending on the severity of the breach and their compliance with Italian data protection regulations.
What are some long-term implications for the email service provider?
Long-term implications could include significant financial losses due to legal action, damage to brand reputation, and decreased customer trust, potentially affecting future business operations.