Cybersecurity & Protection
-

Experts Uncover Critical "By Design" Weakness in Model Context Protocol, Threatening AI Supply Chain
Cybersecurity researchers have identified a fundamental architectural flaw within the Model Context Protocol (MCP) that could enable remote code execution…
Read More » -

Massive "0ktapus" Phishing Campaign Exploits Multi-Factor Authentication, Compromising Over 130 Companies and 9,931 Accounts
A sophisticated and sprawling phishing campaign, dubbed "0ktapus" by cybersecurity researchers, has successfully ensnared over 130 companies worldwide, leading to…
Read More » -

Beyond Ransomware: Why Business Continuity, Not Just Backup, is Crucial for Survival
Ransomware and sophisticated cyberattacks frequently capture headlines, painting a vivid picture of data loss and operational paralysis. However, the narrative…
Read More » -
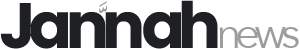
Russian Military Intelligence Exploits Vulnerable Routers for Mass Harvesting of Microsoft Office Authentication Tokens
Hackers associated with Russia’s military intelligence units have been conducting a sophisticated espionage campaign, leveraging well-known vulnerabilities in older Internet…
Read More » -
The AI Demo Illusion: Bridging the Chasm Between Promise and Production Reality
The allure of artificial intelligence has never been more potent, particularly when witnessed in the polished confines of a product…
Read More » -

China-Based APT TA423 Leverages Sophisticated Watering Hole Attacks to Deploy ScanBox Reconnaissance Tool
A China-based advanced persistent threat (APT) group, identified as TA423 and also known as Red Ladon, has intensified its cyber-espionage…
Read More » -
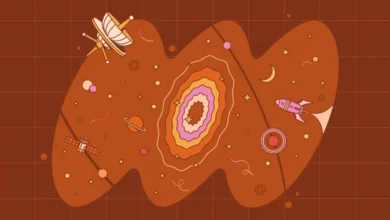
Microsoft Unleashes a Record-Breaking Patch Tuesday, Addressing 167 Security Vulnerabilities Including Actively Exploited Zero-Days
Microsoft unleashed a torrent of software updates today, a massive Patch Tuesday that addressed an unprecedented 167 security vulnerabilities across…
Read More » -

A Deceptive Digital Landscape: Third-Party Compromises and Evolving Attack Vectors Dominate Cybersecurity Concerns in April 2026
April 2026 has underscored a persistent and evolving threat in the cybersecurity landscape: the insidious exploitation of trust. As attackers…
Read More » -

Microsoft Teams Increasingly Abused in Helpdesk Impersonation Attacks
Microsoft is issuing a stern warning to enterprises worldwide: threat actors are escalating their tactics, increasingly leveraging the ubiquitous Microsoft…
Read More » -
Microsoft Issues Record-Breaking Patch Tuesday with 167 Vulnerabilities, Including Actively Exploited Zero-Days
Microsoft unleashed a massive software update on its scheduled Patch Tuesday, addressing a staggering 167 security vulnerabilities across its Windows…
Read More »