Seiko USA Website Defaced, Customer Data Breach Alleged in Ransom Demand
The official website of Seiko USA experienced a significant security breach over the weekend, with malicious actors defacing a portion of the site to issue a ransom demand. The attackers claim to have successfully compromised the company’s Shopify customer database, exfiltrating sensitive user information and threatening to release it publicly unless a ransom payment is made. The incident, first reported by BleepingComputer, highlights the persistent threat of cyberattacks targeting e-commerce platforms and the sensitive data they hold.
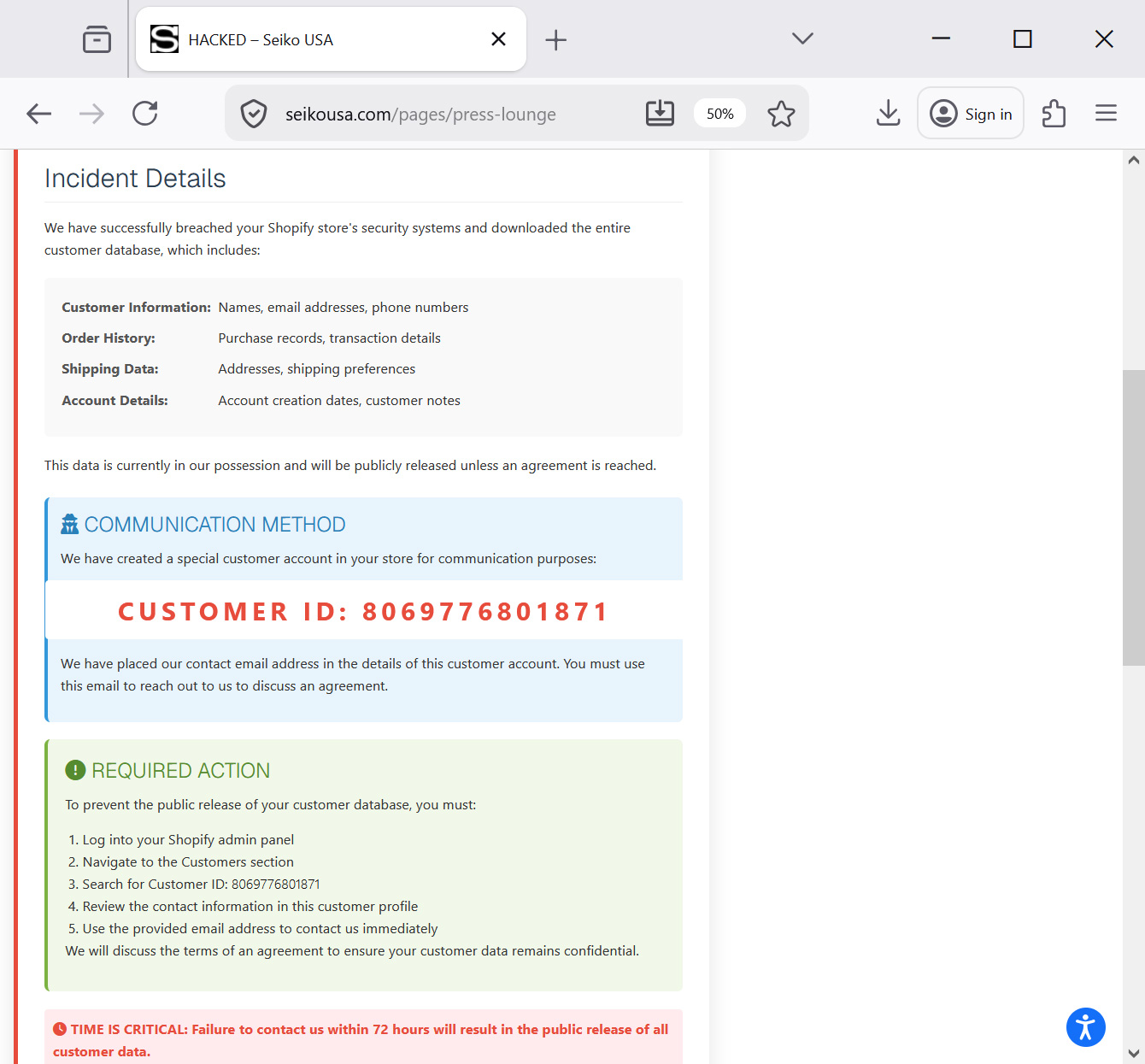
The defacement was discovered in the "Press Lounge" section of the Seiko USA website. Instead of the intended press releases and media kits, visitors were greeted with a stark "HACKED" message. This intrusive display served as a notification of the alleged data breach and a direct ultimatum from the perpetrators. The message explicitly stated that the attackers had gained unauthorized access to the company’s Shopify backend, a popular e-commerce platform used by many businesses to manage online sales and customer data.
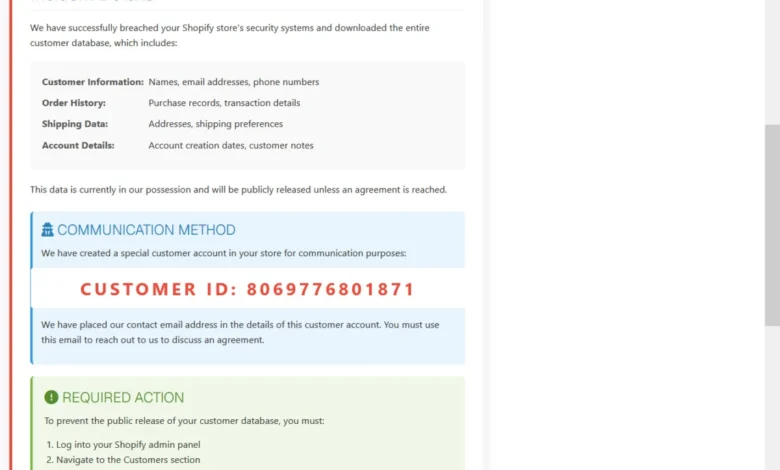
"This is an urgent security notification regarding your Shopify store. Your customer database has been compromised," the defaced webpage declared. It continued with a chilling assertion: "We have successfully breached your Shopify store’s security systems and downloaded the entire customer database." This statement directly implies a deep penetration into Seiko USA’s online retail infrastructure, raising immediate concerns about the privacy and security of its customers.
While the exact scope and nature of the exfiltrated data were not fully detailed in the defaced message, the attackers claimed it contained sensitive customer information. Though a specific list of data points was not explicitly enumerated in the initial reports, typical customer databases compromised in such attacks often include names, email addresses, physical addresses, phone numbers, and potentially payment-related information, although the latter was not explicitly confirmed by the attackers in this instance. The threat actors further emphasized the gravity of their claims by instructing Seiko USA to locate a specific customer account, identified by the ID 8069776801871, within their Shopify admin panel. They asserted that a contact email address had been added to this particular account profile, intended as the sole channel for initiating negotiations.
The ultimatum was time-sensitive, with the attackers warning that Seiko USA had a strict 72-hour window to initiate contact. Failure to do so, they threatened, would result in the public release of the allegedly stolen customer database. This tactic, known as double extortion, involves not only stealing data but also threatening to expose it, thereby increasing pressure on the victimized organization to comply with the ransom demand.
Chronology of the Incident

The incident appears to have unfolded over the weekend, with the defacement becoming visible to visitors sometime before Sunday, October 22nd, 2023. BleepingComputer’s initial report emerged on that date, indicating the defacement was active. By Monday, October 23rd, 2023, the extortion message had been removed from the Seiko USA website, suggesting that the company had taken action to address the immediate threat. However, there has been no official public confirmation or detailed statement from Seiko USA regarding the incident. The timeframe between the discovery of the defacement and its removal indicates a rapid response from the company’s technical and security teams, though the extent of the breach and the validity of the attackers’ claims remain under investigation.
Background Context: E-commerce Security and Ransomware
This incident involving Seiko USA is not an isolated event. The digital landscape is rife with cyber threats, and e-commerce platforms, due to the wealth of sensitive customer data they store, are prime targets for malicious actors. The use of Shopify, while a robust platform, does not exempt businesses from the need for stringent security practices. Shopify itself employs various security measures, but vulnerabilities can still arise from weak passwords, compromised administrator accounts, or third-party app integrations that may have security flaws.
Ransomware attacks, and their variant forms like data extortion, have become increasingly sophisticated and prevalent. Threat actors are constantly evolving their methods to bypass security systems and extract maximum profit. The "double extortion" tactic, where data is both stolen and encrypted, or in this case, threatened to be leaked, has become a common strategy. This approach aims to create a sense of urgency and significant reputational damage, making it harder for organizations to refuse payment.
The value of customer databases to cybercriminals can be immense. This information can be used for various nefarious purposes, including identity theft, phishing campaigns, and further targeted attacks. In some cases, the data itself is sold on dark web marketplaces to other criminal entities. The potential for financial loss, reputational damage, and erosion of customer trust makes such breaches a critical concern for any business.
Supporting Data and Analysis
While specific details about the compromised data in the Seiko USA case are unconfirmed, general trends in data breaches provide context. According to IBM’s 2023 Cost of a Data Breach Report, the global average cost of a data breach reached an all-time high of $4.45 million. This cost includes detection and escalation, lost business, and the aftermath of the breach, such as remediation and reputational repair.

The report also highlighted that organizations that experienced ransomware attacks faced significantly higher costs, averaging $5.06 million, compared to those that did not. The time to identify and contain a data breach also remains a critical factor, with the global average at 204 days in 2023. A faster response, as potentially indicated by Seiko USA’s quick removal of the defacement, can mitigate some of the long-term costs.
The choice of Shopify as the compromised platform is significant. Shopify is used by millions of businesses worldwide, from small startups to large enterprises. Its widespread adoption means that a successful breach of a Shopify store can potentially affect a vast number of customers. Security researchers consistently warn about the importance of securing Shopify accounts with strong, unique passwords, enabling multi-factor authentication (MFA), and carefully vetting any third-party applications installed on the store.
Official Responses and Next Steps
As of the latest reporting, Seiko USA has not issued a public statement confirming the breach or detailing its response. Their immediate action was to remove the extortion message from their website, which is a standard and crucial first step in mitigating the immediate visual impact of the defacement and potentially disrupting the attackers’ communication channel.
However, the absence of a public statement leaves customers and stakeholders in the dark. Best practices in cybersecurity crisis communication dictate transparency and timely updates. Companies that have experienced breaches are often advised to:
- Investigate Thoroughly: Conduct a comprehensive forensic investigation to determine the full extent of the breach, the types of data compromised, and the methods used by the attackers.
- Notify Affected Parties: Inform customers whose data may have been exposed as quickly as possible. This notification should include clear guidance on steps they can take to protect themselves.
- Cooperate with Authorities: Report the incident to relevant law enforcement agencies and regulatory bodies.
- Strengthen Security Measures: Implement immediate and long-term security enhancements to prevent future attacks. This might include security audits, enhanced monitoring, employee training, and reviewing access controls.
BleepingComputer attempted to contact Seiko USA for comment via email, but received no response prior to their removal of the defacement. The lack of direct communication from the company regarding the incident is a point of concern for its customer base.
Broader Impact and Implications
The alleged breach of Seiko USA’s customer database carries significant implications beyond the immediate threat of data leakage.
- Customer Trust: The most immediate impact is on customer trust. Consumers entrust their personal information to businesses with the expectation of its security. A breach can severely damage this trust, leading to customer attrition and a negative brand perception. For a brand like Seiko, known for its heritage and quality, a security incident of this nature can be particularly damaging.
- Reputational Damage: Public knowledge of a data breach can lead to substantial reputational harm. This can affect not only sales but also partnerships, investor confidence, and overall brand equity.
- Regulatory Scrutiny: Depending on the nature of the data compromised and the jurisdictions involved, Seiko USA could face scrutiny from data protection authorities. Regulations like GDPR in Europe and various state-level privacy laws in the U.S. impose strict obligations on companies regarding data protection and breach notification.
- Financial Costs: Beyond the immediate ransom demand (which is often not paid, or if paid, does not guarantee data deletion), the costs associated with a breach can be enormous. These include forensic investigations, legal fees, public relations efforts, potential regulatory fines, and the cost of implementing enhanced security measures.
- Supply Chain Risks: If Seiko USA utilizes third-party vendors or integrates with other services that were also compromised, this could indicate broader vulnerabilities within their digital supply chain.
The fact that the attackers specifically targeted the "Press Lounge" section might be a strategic choice, aiming for immediate visibility and leveraging the news dissemination channels of the company itself. It could also be a less sophisticated approach, simply using a publicly accessible section of the website for their defacement.
The inability of BleepingComputer to immediately identify the threat actor behind the attack suggests that the group may be relatively new, using generic tactics, or employing sophisticated anonymization techniques. Without a public claim of responsibility from known hacking groups, it is difficult to ascertain their motives beyond financial gain through ransom.
The incident serves as a stark reminder for all businesses, especially those operating in the e-commerce space, to prioritize cybersecurity. This includes regular security audits, employee training on phishing and social engineering, robust access controls, prompt patching of vulnerabilities, and having a well-defined incident response plan in place. The digital realm demands constant vigilance, as the threat landscape continues to evolve with alarming speed. Seiko USA’s swift removal of the defacement is a positive sign, but the long-term impact and the company’s comprehensive response will be critical in restoring confidence and ensuring future security.