How to Combat APT Cyber Threats A Comprehensive Guide
How to combat APT cyber threats a comprehensive guide sets the stage for a deep dive into the world of advanced persistent threats (APTs). This guide provides a detailed roadmap for understanding, preventing, and responding to these sophisticated attacks. We’ll explore the tactics, techniques, and procedures (TTPs) employed by APT actors, examining their motivations, attack vectors, and the crucial defensive strategies organizations need to implement.
From the initial introduction to APT threats, to detailed defensive strategies and incident response, this comprehensive guide equips you with the knowledge and tools to protect your organization. We’ll cover everything from understanding the different types of APT attacks to building a robust security posture and the importance of continuous improvement.
Introduction to APT Threats: How To Combat Apt Cyber Threats A Comprehensive Guide
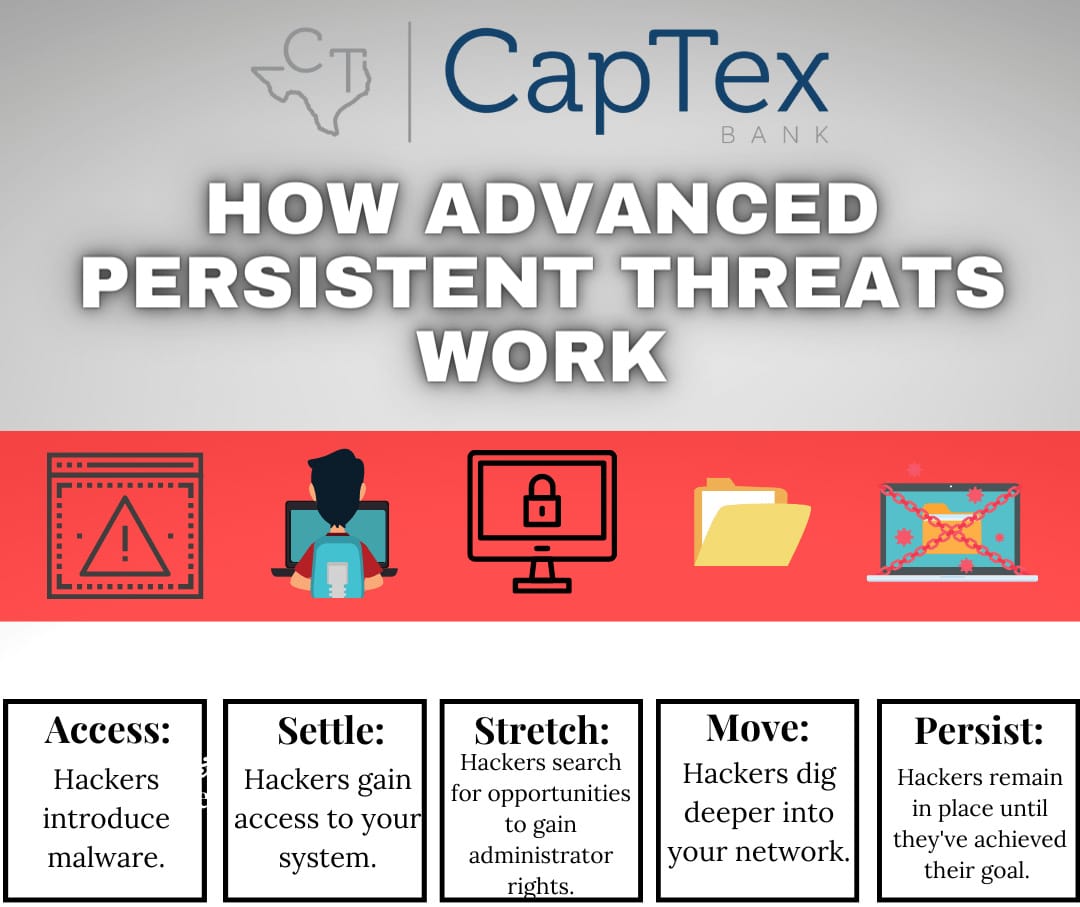
Advanced Persistent Threats (APTs) represent a sophisticated and evolving form of cyberattack. These attacks are characterized by their stealth, persistence, and often, a long-term strategic goal. Unlike typical ransomware or phishing campaigns, APTs are meticulously planned and executed, often targeting specific organizations or individuals with significant value, such as government agencies, corporations, or critical infrastructure.APTs are distinguished from other cyber threats by their sustained and focused nature.
They are not quick bursts of malicious activity, but rather a calculated infiltration and exploitation that can last for months or even years. This extended presence allows attackers to gather extensive intelligence, exfiltrate sensitive data, and maintain access for future operations. The scale of damage from APTs is often considerable, with the potential for substantial financial loss, reputational damage, and even national security implications.
Motivations and Objectives of APT Actors
APT actors are driven by a wide range of motivations. These can include financial gain, political motivations, espionage, sabotage, or ideological objectives. Some groups seek to steal intellectual property or financial assets, while others are driven by a desire to disrupt operations or cause damage. The objectives of APT actors often align with their motivations, aiming to achieve specific outcomes, such as gaining access to sensitive data, manipulating information, or disrupting critical infrastructure.
Examples of High-Profile APT Attacks
Numerous high-profile attacks exemplify the devastating potential of APTs. One notable example is the NotPetya attack, which caused widespread disruption across various industries, including shipping, manufacturing, and healthcare. This attack utilized a sophisticated malware that spread rapidly through compromised systems, resulting in significant financial losses and operational downtime. Similarly, the Stuxnet worm targeted Iranian nuclear facilities, demonstrating the potential for APTs to affect critical infrastructure.
These incidents highlight the need for robust cybersecurity measures and proactive threat intelligence gathering.
Types of APT Attacks
Understanding the various techniques employed by APT actors is crucial for developing effective defenses. These attacks often leverage multiple methods to achieve their objectives. A breakdown of common attack vectors is provided below:
| Attack Type | Description |
|---|---|
| Spear Phishing | Sophisticated phishing attacks targeting specific individuals or organizations. These attacks often involve meticulously researched information to increase the likelihood of success. |
| Supply Chain Attacks | Exploiting vulnerabilities in the supply chain to gain access to target systems. This approach involves compromising a trusted third-party vendor or supplier, which can then provide access to the end-user. |
| Malware Campaigns | Utilizing malicious software to gain unauthorized access to systems and networks. These campaigns are often characterized by advanced techniques and obfuscation to avoid detection. |
| Insider Threats | Exploiting compromised or disgruntled insiders to gain access to sensitive information or systems. These attacks often leverage existing privileges or knowledge of internal systems. |
Understanding APT Attack Vectors
Advanced Persistent Threats (APTs) employ sophisticated and multifaceted attack vectors to achieve their objectives. These attacks are not simple, one-time events but rather prolonged campaigns designed to gain unauthorized access and maintain control over targeted systems for extended periods. Understanding these vectors is crucial for effective defense strategies.APT attacks often leverage a combination of techniques, exploiting vulnerabilities in various systems and employing social engineering tactics to bypass traditional security measures.
This intricate approach necessitates a comprehensive understanding of the attack surface to develop robust countermeasures.
Common Attack Vectors Used by APT Groups
APT groups frequently utilize a range of attack vectors to penetrate their targets. These vectors often include exploiting software vulnerabilities, leveraging phishing campaigns, and compromising legitimate infrastructure components.
- Exploiting Software Vulnerabilities: APTs meticulously identify and exploit known and unknown vulnerabilities in software applications and operating systems. This involves exploiting zero-day vulnerabilities, where attackers leverage vulnerabilities before they are patched by vendors. Sophisticated tools are used to automate the exploitation process, enabling quick and widespread infiltration. Examples include exploits targeting critical infrastructure software, leading to widespread disruptions or data breaches.
- Phishing Campaigns: Social engineering plays a critical role in APT attacks, often employing sophisticated phishing campaigns. These campaigns are meticulously crafted to target specific individuals or organizations, aiming to gain access to sensitive information or compromise systems. Spear phishing, a highly targeted form of phishing, is a common tactic, exploiting the trust built between individuals and organizations to gain access to sensitive data.
- Compromised Infrastructure Components: APTs frequently target legitimate infrastructure components, such as email servers or web servers, to gain a foothold within the network. Compromising these components allows attackers to leverage existing network access for further infiltration and lateral movement.
Evolution of Attack Vectors Over Time
APT attack vectors are constantly evolving, adapting to advancements in security technologies and defensive measures. The initial vectors might have focused on exploiting known vulnerabilities, but the evolution has led to a more sophisticated approach.
- From Known to Unknown Vulnerabilities: Early APT attacks often relied on exploiting known vulnerabilities, but modern APTs increasingly leverage zero-day vulnerabilities. This adaptation requires continuous monitoring of emerging threats and proactive vulnerability management.
- Increased Sophistication in Social Engineering: Sophisticated social engineering techniques are becoming more prevalent, incorporating personalized messages and tailored content to bypass security awareness training. This requires stronger security awareness training programs and enhanced security measures to detect and respond to targeted attacks.
- Leveraging Legitimate Infrastructure: The use of legitimate infrastructure components as attack vectors is becoming more common, making it more difficult to detect malicious activity. This necessitates proactive monitoring and analysis of legitimate traffic for anomalies and suspicious patterns.
Techniques Used to Exploit Vulnerabilities
Attackers employ a variety of techniques to exploit vulnerabilities in different systems. These techniques often involve exploiting vulnerabilities in operating systems, applications, and network protocols.
- Exploiting Operating System Vulnerabilities: Attackers exploit vulnerabilities in operating systems, such as Windows or Linux, to gain unauthorized access. This often involves exploiting buffer overflows, using exploits to gain system privileges, and leveraging vulnerabilities in network services.
- Exploiting Application Vulnerabilities: APTs frequently target vulnerabilities in web applications, databases, and other software applications. This often includes exploiting vulnerabilities in frameworks, libraries, and specific applications.
- Exploiting Network Protocols: Attackers exploit vulnerabilities in network protocols, such as TCP/IP, to gain access to systems or manipulate network traffic. This can involve exploiting vulnerabilities in routing protocols, or man-in-the-middle attacks to intercept communication.
Role of Social Engineering in APT Attacks
Social engineering is a critical component of APT attacks, enabling attackers to bypass technical security controls. Attackers exploit human psychology to manipulate individuals into performing actions that compromise security.
- Exploiting Trust: Attackers exploit the trust built between individuals or organizations to gain access to sensitive information or systems. This includes impersonating trusted individuals or organizations to gain access to data or systems.
- Creating Urgency and Fear: Creating a sense of urgency or fear can manipulate individuals into making rash decisions that compromise security. This includes creating false threats or promises to manipulate individuals into taking actions.
- Leveraging Personal Relationships: Attackers may exploit personal relationships to gain access to sensitive information or systems. This includes targeting individuals who have access to critical data or systems.
Effectiveness of Attack Vectors
This table provides a comparative overview of the effectiveness of different attack vectors. Effectiveness is a complex metric influenced by various factors.
| Attack Vector | Effectiveness | Mitigation Strategies |
|---|---|---|
| Exploiting Software Vulnerabilities | High, especially for zero-day exploits | Proactive vulnerability management, patching, and intrusion detection systems |
| Phishing Campaigns | Moderate to High, depending on sophistication | Security awareness training, email filtering, and multi-factor authentication |
| Compromised Infrastructure Components | High, if attacker gains persistent access | Monitoring network traffic, incident response plans, and segmentation |
Defensive Strategies Against APTS
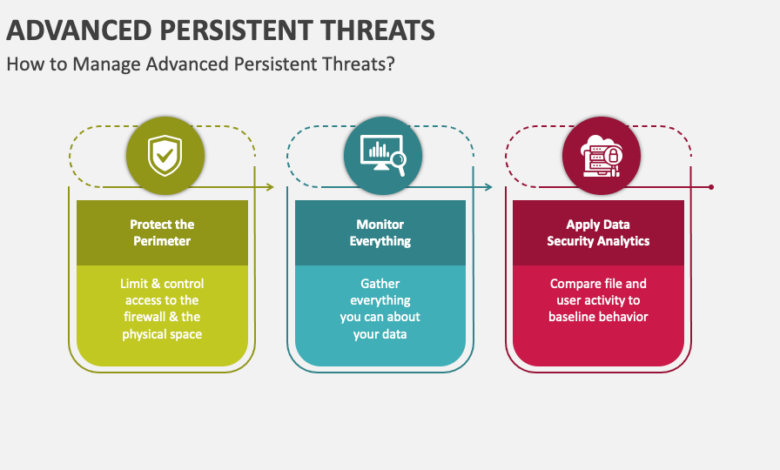
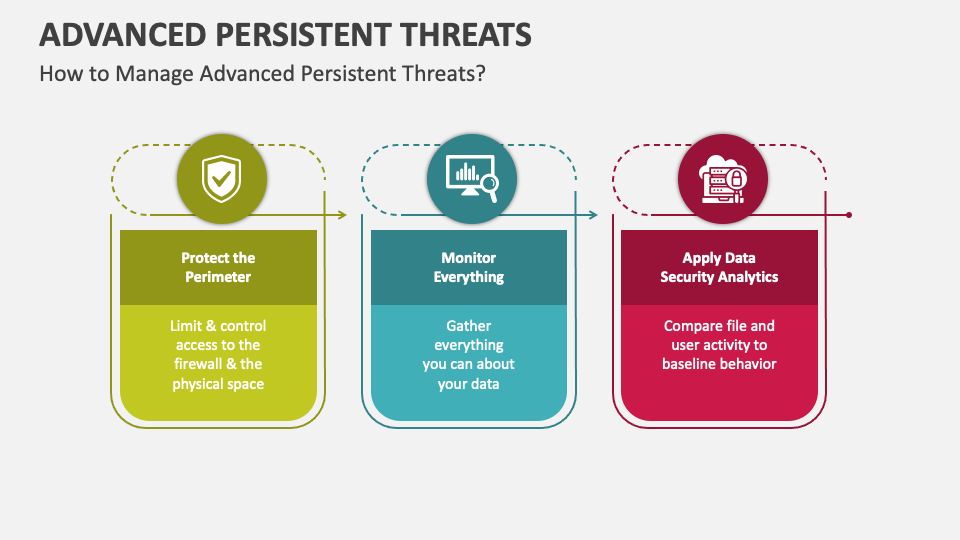
Advanced Persistent Threats (APTs) pose a significant cybersecurity risk to organizations of all sizes. Successfully defending against these sophisticated attacks requires a multi-layered approach encompassing proactive measures, robust detection systems, and a culture of security awareness. This section details key defensive strategies to mitigate the risk of APT attacks.A strong defense against APTs is not just about reactive measures, but also about understanding the adversary’s tactics, techniques, and procedures (TTPs).
By anticipating potential attack vectors and implementing preventative measures, organizations can significantly reduce their vulnerability. Proactive security measures, coupled with rapid detection and response capabilities, are critical in effectively countering these threats.
Preventative Measures to Reduce APT Attack Risk
Proactive security measures are crucial in creating a robust defense against APTs. These strategies aim to reduce the attack surface and enhance the overall security posture. Implementing these measures significantly lowers the probability of a successful attack.
- Strong Access Controls: Implementing strong access controls is paramount. This involves restricting access to sensitive data and systems to only authorized personnel, minimizing the number of users with elevated privileges. Multi-factor authentication (MFA) should be enforced across all critical systems to prevent unauthorized access even if credentials are compromised.
- Vulnerability Management: Regular vulnerability assessments and penetration testing help identify and address security weaknesses before attackers exploit them. Patching systems promptly and configuring systems securely reduces potential entry points for attackers. This is a continuous process, not a one-time fix.
- Network Segmentation: Dividing the network into smaller, isolated segments limits the impact of a breach. If one segment is compromised, the attack is contained within that segment, preventing lateral movement to other critical systems. This isolates sensitive data and prevents the spread of malware.
- Data Loss Prevention (DLP): Implementing DLP systems helps prevent sensitive data from leaving the organization’s control. This includes controlling data exfiltration through email, file transfers, and other communication channels. DLP tools can identify and block unauthorized data transfers.
Proactive Security Measures for APT Defense
Proactive security measures are essential to mitigate the risks associated with APTs. They focus on building a resilient security posture through ongoing monitoring and adaptation.
- Intrusion Detection and Prevention Systems (IDPS): IDPSs monitor network traffic for malicious activity and automatically block or alert on suspicious behavior. These systems can identify anomalies that might indicate an APT attack, enabling rapid response and containment.
- Security Information and Event Management (SIEM): SIEM solutions collect and analyze security logs from various sources. They can correlate events to identify patterns and potential APT activity. This helps in threat detection and response by highlighting unusual or malicious events.
- Endpoint Detection and Response (EDR): EDR solutions monitor endpoints (computers, servers) for malicious activity and provide real-time alerts. They are essential for detecting and responding to attacks that may have already penetrated the network perimeter. EDR systems offer comprehensive visibility into endpoint activity.
- Threat Intelligence: Organizations must stay informed about emerging threats. Using threat intelligence feeds helps in identifying and understanding APT tactics and techniques. This enables proactive measures to counter evolving attack strategies.
Comparing and Contrasting Security Tools
Choosing the right security tools is crucial for effective APT defense. Different tools cater to different aspects of the security infrastructure.
| Tool Category | Description | Strengths | Weaknesses |
|---|---|---|---|
| IDPS | Monitors network traffic for malicious activity. | Fast detection, automated responses. | Can generate false positives, requires expert tuning. |
| SIEM | Collects and analyzes security logs. | Correlates events, identifies patterns. | Requires significant data ingestion and processing capabilities. |
| EDR | Monitors endpoints for malicious activity. | Real-time detection, detailed endpoint visibility. | Requires agent deployment on every endpoint. |
Importance of Security Awareness Training
Security awareness training empowers employees to identify and report suspicious activities. It fosters a culture of security vigilance, making employees active participants in defending against APTs.
- Phishing Simulation: Regularly simulate phishing attacks to test employee awareness and improve their ability to recognize and avoid malicious emails or websites. These simulations are a crucial element in training and should be conducted regularly.
- Security Policies and Procedures: Employees should be trained on the organization’s security policies and procedures, including password management, data handling, and incident reporting. Clear communication of security policies is crucial for effective training.
- Social Engineering Awareness: Train employees to recognize social engineering tactics used by attackers. This includes recognizing phishing attempts, suspicious phone calls, and other methods of manipulating employees into revealing sensitive information. Training should highlight the tactics used by social engineers.
Building a Robust Security Posture
Advanced Persistent Threats (APTs) are sophisticated and targeted attacks, demanding a proactive and layered security approach. A robust security posture isn’t a one-time fix; it’s a continuous process of adaptation and improvement, crucial for withstanding the evolving tactics of APT actors. This proactive strategy goes beyond simply detecting intrusions; it focuses on preventing them from gaining a foothold within the organization’s infrastructure.A well-designed security architecture acts as the bedrock for mitigating APT risks.
It encompasses a comprehensive framework that defines roles, responsibilities, and security controls across all systems and data. This architecture must be dynamic and adaptable, allowing for the swift incorporation of new threats and technologies.
Security Architecture Design
A robust security architecture is a cornerstone of an effective APT defense strategy. It dictates how different components of an organization’s IT infrastructure interact and ensures that security controls are implemented consistently across all systems. This architecture should be designed with a zero-trust model in mind, assuming no implicit trust, and validating every access request. This prevents unauthorized access even if an attacker compromises a single point.
Network Segmentation and Access Controls
Network segmentation is essential for isolating potential attack vectors. By dividing the network into smaller, isolated segments, an attacker’s ability to move laterally across the network is significantly reduced. This compartmentalization limits the impact of a compromise in one area. Access controls, implemented alongside segmentation, dictate who can access specific resources within the network. This granular control further restricts the potential damage caused by an intrusion.
Multi-Factor Authentication (MFA)
Implementing multi-factor authentication (MFA) is a crucial step in strengthening access controls. MFA requires multiple verification steps beyond a simple password, making it considerably harder for attackers to gain unauthorized access. By requiring a combination of factors like a password, a one-time code, or a biometric scan, the risk of unauthorized logins is drastically reduced. This layer of defense can significantly impede attackers seeking to gain initial access to a system.
Incident Response Planning
A well-defined incident response plan is essential for managing and containing APT attacks. This plan Artikels procedures for detecting, analyzing, containing, eradicating, and recovering from security incidents. This proactive planning is crucial for minimizing the impact of an APT attack and for ensuring a swift return to operational normalcy. It details roles, responsibilities, and communication protocols to ensure effective response.
A comprehensive guide to combating advanced persistent threats (APTs) needs a multi-layered approach. Understanding specific vulnerabilities, like those detailed in the Azure Cosmos DB Vulnerability Details , is crucial. Knowing these weaknesses helps prioritize security measures and develop a more robust defense strategy to prevent APT attacks. Ultimately, a layered approach, including vulnerability assessments and proactive security protocols, is key to effectively combat APTs.
Best Practices for Securing Critical Infrastructure
| Security Control | Description | Implementation Considerations ||—|—|—|| Regular Vulnerability Assessments | Proactively identify and address security weaknesses in critical systems. | Schedule regular scans and prioritize remediation of vulnerabilities. || Strong Password Policies | Enforce complex password requirements and regular password changes. | Implement a strong password policy across all user accounts. || Continuous Monitoring | Implement continuous monitoring of network activity and system logs.
| Use intrusion detection and prevention systems (IDPS) and SIEM tools. || Data Loss Prevention (DLP) | Prevent sensitive data from leaving the organization’s control. | Implement DLP solutions to monitor and control data exfiltration attempts. || Employee Training | Educate employees on recognizing and reporting suspicious activities. | Conduct regular security awareness training and phishing simulations.
|
Monitoring and Detection Techniques
Staying ahead of advanced persistent threats (APTs) requires a robust and proactive approach to monitoring and detection. This involves more than just reacting to incidents; it demands a system capable of identifying subtle anomalies and potential threats in real-time. Effective monitoring allows organizations to anticipate and mitigate APT attacks before significant damage occurs.
Security Information and Event Management (SIEM) Systems
SIEM systems are crucial for detecting APT activity. They collect and analyze security logs from various sources, like firewalls, intrusion detection systems, and servers, to identify patterns and anomalies indicative of malicious activity. By correlating events, SIEM systems can uncover the intricate threads of an APT attack that might be missed by individual log analysis. They provide a centralized view of the security posture, allowing security teams to quickly respond to threats.
The ability to identify unusual user behavior, suspicious network traffic, and compromised accounts is paramount.
Intrusion Detection and Prevention Systems (IDS/IPS), How to combat apt cyber threats a comprehensive guide
IDS/IPS systems are essential components of a comprehensive security architecture. IDS systems monitor network traffic for malicious activity, while IPS systems actively block or mitigate detected threats. These systems play a critical role in detecting attacks that might be missed by other security controls. IDS/IPS solutions can detect various attack vectors, including malware, exploits, and reconnaissance activities.
A well-configured IDS/IPS system can provide a significant layer of defense against APT attacks.
Security Monitoring Tools for Real-Time Threat Detection
Real-time threat detection is vital in combating APTs. Implementing security monitoring tools, such as network traffic analysis tools, endpoint detection and response (EDR) solutions, and vulnerability scanners, provides continuous monitoring of systems and networks. These tools can detect malicious activity as it occurs, allowing for quicker responses and reduced damage. Regular updates and configuration tuning are essential to maintain effectiveness.
Sophisticated tools can analyze massive datasets, identify patterns, and pinpoint anomalies.
Threat Intelligence for APT Defense
Threat intelligence plays a pivotal role in anticipating and responding to APT attacks. By leveraging threat intelligence feeds, organizations can gain insights into the tactics, techniques, and procedures (TTPs) used by specific threat actors targeting their industry. This intelligence can be used to proactively adjust security controls and strengthen defenses. Real-world examples show how threat intelligence has been instrumental in preventing attacks before they could materialize.
This is particularly relevant for organizations operating in highly regulated industries.
SIEM and IDS Solutions Comparison
| Solution | Key Features | Pros | Cons |
|---|---|---|---|
| Splunk | Log aggregation, search, visualization, and reporting; strong integration capabilities. | Flexible, powerful, and widely used; strong community support. | Can be complex to implement and manage for smaller organizations. |
| Elasticsearch, Logstash, Kibana (ELK Stack) | Open-source platform for log management and analysis. | Cost-effective, highly scalable, and customizable. | Requires in-house expertise for implementation and management. |
| SolarWinds Security Event Manager | Centralized platform for security information and event management. | Ease of use and intuitive interface. | Limited customization options compared to other solutions. |
| Snort | Open-source intrusion detection system. | Highly customizable, flexible, and adaptable to various environments. | Requires significant expertise for configuration and maintenance. |
| Intrusion Prevention System (IPS) from Fortinet | Active protection against malicious traffic, integrated with firewall and other security products. | Strong prevention capabilities and comprehensive security. | Higher cost compared to other options. |
Incident Response and Recovery
APT attacks demand a swift and meticulous incident response. A well-defined plan is crucial for containing the damage, recovering data, and preventing future breaches. This section delves into the critical steps involved, focusing on practical strategies for mitigating the impact of such sophisticated threats.
Comprehensive Incident Response Plan
A robust incident response plan serves as a roadmap for dealing with security breaches. It Artikels the roles and responsibilities of personnel, defines communication protocols, and details the steps to be taken in various scenarios. This includes the activation of the incident response team, containment procedures, and data recovery strategies. Effective incident response plans are crucial to minimize the impact of an APT attack, including financial losses, reputational damage, and legal repercussions.
Containing and Isolating Compromised Systems
Immediate containment is paramount in an APT attack. Compromised systems must be isolated to prevent further lateral movement and data exfiltration. This involves disconnecting the affected systems from the network, quarantining them, and implementing security measures to prevent unauthorized access. A thorough understanding of the attack vector is essential for effective containment. This involves detailed analysis of network traffic patterns and logs to identify the points of entry and infection.
- Network Segmentation: Isolating compromised systems by segmenting the network is a critical first step. This limits the spread of malware and prevents further exploitation. This approach is especially effective when combined with robust access controls.
- System Isolation: Disconnecting affected systems from the network minimizes the risk of further data exfiltration or malicious activity. This process often involves isolating the affected device from all network communications.
- Security Monitoring: Actively monitoring the network and system logs for unusual activity is essential. This allows for rapid identification of potential threats and helps to understand the scope of the incident. The logs can provide valuable insights into the attacker’s methods and intentions.
Data Recovery and Forensic Analysis
Data recovery and forensic analysis are critical for understanding the extent of the breach and restoring operations. A methodical approach is essential for preserving evidence and reconstructing the attack sequence. This includes creating backups, performing forensic analysis on the compromised systems, and restoring critical data. The recovery process should be carefully documented to facilitate future incident response planning and legal compliance.
Navigating the complex world of APT cyber threats requires a multi-layered approach. A comprehensive guide should cover everything from robust security protocols to employee training, and understanding the nuances of these sophisticated attacks is crucial. Fortunately, resources like the Department of Justice’s recent “Safe Harbor” policy for Massachusetts transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) can provide a crucial layer of protection against financial fraud and data breaches.
Ultimately, a combination of proactive measures and adaptable strategies are essential to combat these sophisticated threats effectively.
- Data Backup and Recovery: Maintaining regular backups is essential for data recovery. A comprehensive backup strategy ensures that critical data can be restored quickly and efficiently. This often involves regularly backing up critical data and systems to offline storage or cloud solutions.
- Forensic Analysis: A forensic investigation helps to understand the attacker’s tactics, techniques, and procedures (TTPs). This analysis can provide critical insights into the attackers’ motivations, goals, and methods. Forensic analysis is essential for gathering evidence and understanding the attack lifecycle.
- Data Restoration: Restoring data from backups is a crucial step in recovery. This process must be carefully planned and executed to ensure the integrity of the restored data. It involves careful comparison of restored data with the original data to identify any discrepancies.
Examples of Successful Incident Response Strategies
Numerous organizations have successfully navigated APT attacks by implementing comprehensive incident response plans. These strategies involved swift containment, rigorous data recovery, and effective communication with stakeholders. Examples include rapid identification and isolation of compromised systems, effective data recovery procedures, and the preservation of evidence for legal proceedings. Success hinges on the organization’s ability to react swiftly and methodically.
Incident Response Process Flowchart
A flowchart illustrating the incident response process can be visualized as a series of interconnected steps. These steps typically include identifying the incident, containing the threat, analyzing the incident, recovering data, and finally, implementing preventative measures.
(Visual representation of a flowchart is not possible here. The flowchart would depict a series of steps, including: 1. Incident Detection, 2. Containment, 3. Analysis, 4. Eradication, 5. Recovery, 6. Post-Incident Review.)
Collaboration and Information Sharing
Fighting advanced persistent threats (APTs) requires a coordinated effort, transcending organizational boundaries. Isolated defenses are often insufficient against the sophisticated tactics and techniques employed by these attackers. Effective collaboration and information sharing are crucial for bolstering defenses and improving overall security posture. Sharing threat intelligence and best practices is essential for collectively understanding and mitigating these evolving threats.The importance of sharing information extends beyond simply identifying attacks.
By understanding the attacker’s motivations, tools, and techniques, organizations can proactively adapt their defenses and prevent future breaches. This proactive approach reduces the likelihood of successful attacks and minimizes the damage caused by those that do occur.
Importance of Collaboration Between Organizations and Security Researchers
Collaboration between organizations and security researchers is vital for combating APTs. Security researchers often uncover vulnerabilities and attack patterns that organizations alone might not identify. Sharing this knowledge enables organizations to quickly patch critical weaknesses and strengthen their defenses. Conversely, organizations provide researchers with real-world attack data and insights into the effectiveness of various attack vectors, enabling them to refine their analysis and develop more effective detection and prevention strategies.
This symbiotic relationship is essential for the constant evolution of cybersecurity defenses.
Role of Information Sharing Platforms in Combating APT Threats
Information sharing platforms facilitate the exchange of threat intelligence between organizations and researchers. These platforms often aggregate data from multiple sources, creating a comprehensive picture of the threat landscape. By enabling the rapid dissemination of threat information, these platforms help organizations to identify and respond to attacks more effectively. This collaborative approach is crucial for reducing the time to detection and response, thereby minimizing the impact of APT attacks.
Importance of Industry-Wide Collaboration in Developing Solutions
Industry-wide collaboration is critical for developing comprehensive solutions to APT threats. A unified approach allows for the development of standardized threat intelligence formats, common security protocols, and improved incident response mechanisms. This collective effort leads to a more resilient and adaptable cybersecurity ecosystem. Sharing best practices, threat analysis methodologies, and security incident reports fosters a stronger, more unified defense against sophisticated attacks.
Examples of Successful Information Sharing Initiatives
Several successful information sharing initiatives have demonstrated the effectiveness of collaborative approaches. One notable example is the collaborative effort between government agencies and private sector organizations in the US to share threat intelligence related to APT attacks. Another example is the use of industry-specific threat intelligence feeds to alert organizations to specific attacks targeting their sector. These initiatives underscore the value of collective action in combating APTs.
Information Sharing Platforms and Their Key Features
| Platform | Key Features | Strengths | Weaknesses |
|---|---|---|---|
| MISP (Malware Information Sharing Platform) | Open-source, flexible, supports various data formats, allows for tagging and linking of information, enabling detailed analysis and correlation. | Highly customizable, extensive community support, facilitates deep analysis of APT attacks. | Requires technical expertise for implementation and management. |
| VirusShare | Focuses on malware analysis and sharing, facilitates rapid identification of malicious software variants and their associated behaviors. | Highly effective in identifying and tracking malware, enabling proactive defense. | Might not provide a holistic view of APT attacks; limited scope compared to other platforms. |
| X-Force Exchange | Provides a centralized platform for sharing threat intelligence, vulnerability reports, and attack data from IBM’s X-Force research team. | High quality, vetted intelligence, integration with other IBM security products. | Limited accessibility for non-IBM clients. |
Continuous Improvement and Adaptation
Staying ahead of advanced persistent threats (APTs) requires a proactive, adaptable security posture. Simply implementing security measures isn’t enough; organizations must continuously refine and improve their defenses to counter the ever-evolving tactics of these sophisticated attackers. This involves understanding emerging threats, regularly updating security protocols, and building a culture of continuous learning within the security team.The landscape of cyber threats is dynamic.
APT actors are constantly innovating their techniques, exploiting new vulnerabilities, and adapting to security measures. A static security approach is doomed to fail. To effectively combat APTs, organizations need to embrace a philosophy of continuous improvement, proactively identifying and addressing emerging threats. This involves a cyclical process of assessment, adaptation, and reinforcement.
Regular Security Protocol Updates
Maintaining a robust security posture demands consistent updates to security protocols and tools. These updates often address newly discovered vulnerabilities, enhance detection capabilities, and improve overall security efficacy. Failing to update security protocols leaves organizations susceptible to known exploits and exposes them to the risk of novel attack vectors. This proactive approach is crucial in mitigating the impact of emerging threats.
Vulnerability Management Programs
A robust vulnerability management program is essential for identifying and mitigating security weaknesses. This program should include automated scanning, regular vulnerability assessments, and a well-defined process for prioritizing and remediating discovered vulnerabilities. By actively addressing vulnerabilities, organizations reduce the attack surface and improve their overall security posture. A comprehensive vulnerability management program is critical for long-term security and reduces the risk of exploitation.
Identifying and Addressing Emerging Threats
Identifying and addressing emerging threats requires continuous monitoring of the threat landscape. This includes staying informed about new attack techniques, vulnerabilities, and tactics employed by APTs. This information can be gleaned from various sources, including threat intelligence feeds, security research publications, and industry forums. By proactively identifying and addressing emerging threats, organizations can strengthen their defenses and reduce the risk of successful attacks.
Periodic Security Audits
Regular security audits are crucial for evaluating the effectiveness of existing security controls and identifying areas for improvement. These audits should cover all aspects of the organization’s security posture, including network security, endpoint protection, data security, and incident response procedures. They provide a systematic approach to evaluating security controls and identifying gaps or vulnerabilities that could be exploited by APTs.
A comprehensive guide to combating APT cyber threats needs to address the evolving nature of these attacks. One crucial aspect is deploying AI-powered tools like those highlighted in Deploying AI Code Safety Goggles Needed , to proactively identify and mitigate vulnerabilities in code. This proactive approach is essential to fortifying defenses against these sophisticated threats.
A checklist for periodic security audits should include the following:
- Network Security Audit: Review firewalls, intrusion detection systems (IDS), and network segmentation strategies to ensure they effectively mitigate known and emerging threats. The audit should verify that access controls are properly configured and monitored.
- Endpoint Security Audit: Evaluate endpoint protection software (antivirus, anti-malware) configurations, update policies, and patch management procedures. Ensure all endpoints are compliant with security standards and updated regularly.
- Data Security Audit: Review data encryption, access controls, and data loss prevention (DLP) policies. Assess the organization’s ability to protect sensitive data and ensure compliance with relevant regulations.
- Incident Response Audit: Evaluate the organization’s incident response plan, including procedures for detection, containment, eradication, recovery, and lessons learned. This should include testing and simulating incidents to ensure preparedness.
A comprehensive security audit provides a detailed assessment of the organization’s current security posture, enabling organizations to identify vulnerabilities and develop strategies to mitigate risks.
Closing Notes
In conclusion, effectively combating APT cyber threats requires a multifaceted approach that combines proactive measures, robust security architectures, and a culture of continuous improvement. This comprehensive guide serves as a valuable resource, equipping you with the knowledge and tools to navigate the evolving threat landscape and safeguard your organization from sophisticated attacks. By understanding the nuances of APT attacks and implementing the strategies Artikeld, you can strengthen your security posture and protect your valuable assets.
Question & Answer Hub
What are the key characteristics that distinguish APTs from other cyber threats?
APTs are characterized by their sophisticated nature, persistence, and targeted approach. They often employ advanced techniques and tools, and they operate for extended periods, aiming to evade detection and achieve their objectives without being discovered.
What are some common attack vectors used by APT groups?
Common attack vectors include spear phishing, exploiting vulnerabilities in software, and supply chain attacks. APT groups often combine these vectors to increase their chances of success.
What is the role of social engineering in APT attacks?
Social engineering plays a significant role in APT attacks, as it aims to manipulate individuals into divulging sensitive information or performing actions that compromise security. This can include phishing emails, impersonation, and other tactics.
What is the importance of threat intelligence in anticipating and responding to APT attacks?
Threat intelligence provides valuable insights into the tactics, techniques, and procedures (TTPs) used by APT groups, enabling organizations to anticipate and respond effectively to these attacks. It’s crucial for proactive security measures.