How to Spoof MAC Address of an Android Phone
How to spoof MAC address of an Android phone? This guide dives deep into the world of MAC address spoofing on Android devices. We’ll explore what a MAC address is, why you might want to change it, and the various methods available. From simple techniques to more complex ones, we’ll cover it all, along with the potential risks and legal implications.
Understanding the intricacies of network communication and the role of MAC addresses is crucial. This article breaks down the process into manageable steps, allowing you to confidently tackle this task. We’ll also examine alternative solutions to network restrictions, providing a well-rounded perspective.
Introduction to MAC Address Spoofing on Android
A MAC address, or Media Access Control address, is a unique identifier assigned to each network interface on a device. Think of it as the device’s unique “social security number” on a network. This address is crucial for communication between devices on a local network. Without a unique MAC address, devices wouldn’t be able to send or receive data correctly.MAC address spoofing involves intentionally changing the MAC address displayed by a device to a different value.
This altered MAC address is not actually tied to the physical hardware of the device. In essence, the device is masquerading as another device on the network, concealing its true identity.
Motivations for MAC Address Spoofing
Users might spoof their MAC address for various reasons, ranging from circumventing network restrictions to maintaining anonymity. Network administrators may implement rules that restrict access based on MAC addresses, and spoofing can bypass these limitations. Furthermore, spoofing can provide a degree of anonymity in online interactions.
Scenarios of MAC Address Spoofing
MAC address spoofing finds applications in various scenarios, such as:
- Bypassing Network Restrictions: A common use case involves users who want to access resources on a network that blocks specific devices. Spoofing allows access by presenting a different MAC address. A prime example would be a user trying to connect to a school or company network from a personal device, but the network blocks devices with non-approved MAC addresses.
- Network Security Testing: Security professionals sometimes use spoofing as a testing technique to evaluate the robustness of network security measures. They can simulate different attack scenarios and assess how the network responds.
- Masking Network Activity: Spoofing can potentially help mask network activity, making it harder to trace the source of specific communications. This could be relevant for users concerned about their online privacy.
Illustrative Examples
The following table demonstrates how MAC address spoofing can be utilized in various contexts:
| MAC Address | Device | Purpose |
|---|---|---|
| 00:1A:2B:3C:4D:5E | Smartphone (User A) | Accessing a restricted Wi-Fi network. |
| 00:1A:2B:3C:4D:5F | Laptop (User B) | Testing network security for a company project. |
| 00:1A:2B:3C:4D:60 | Hacking tool | Masking the source of network attacks. |
Methods for Spoofing MAC Address on Android
MAC address spoofing on Android, while seemingly simple, involves navigating a complex interplay of system permissions and network configurations. Understanding the various methods, their strengths, and weaknesses, is crucial for anyone looking to alter their device’s MAC address. This approach can be used for various purposes, ranging from bypassing network restrictions to enhancing anonymity online. However, it’s essential to use this technique responsibly and ethically, avoiding any malicious activities.
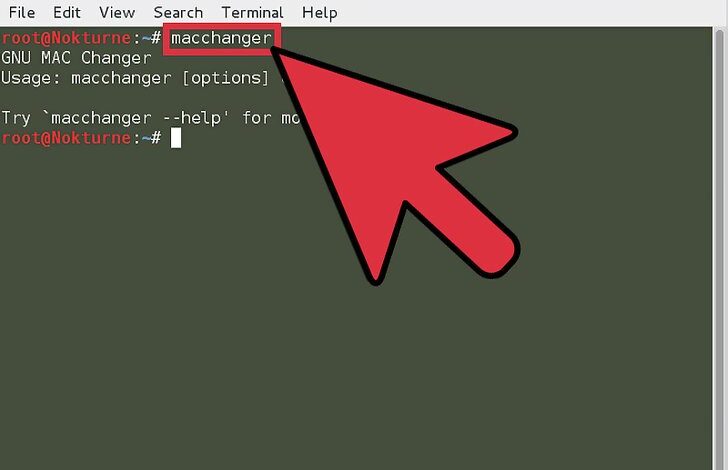
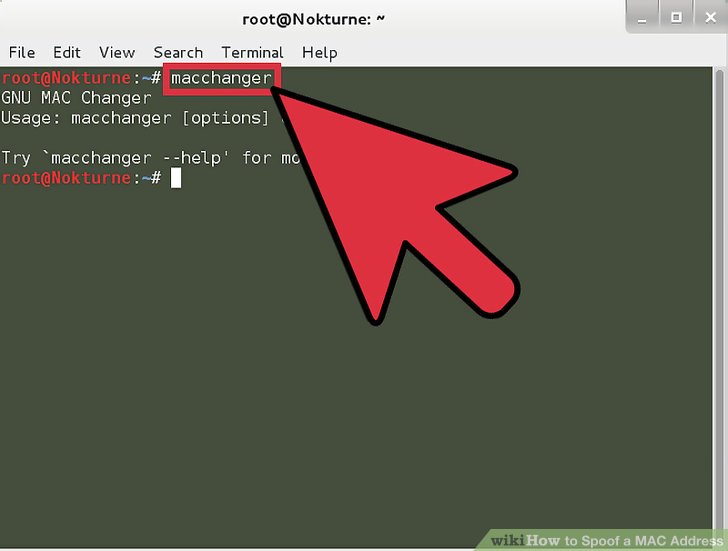
Software-Based MAC Address Spoofing Tools
Several applications are available for Android devices that claim to change the MAC address. These apps typically work by modifying the system files related to network interfaces. This method often involves root access, and the implications of using these apps can vary.
- Root-based applications often offer more comprehensive control over the system, allowing for greater customization and potentially more stable changes. However, gaining root access can void device warranties and potentially introduce security risks if the root application isn’t trustworthy. Some applications might even have malicious intent. Be extremely cautious when choosing a root application.
- Non-root applications often provide a less comprehensive solution, focusing on specific network interfaces or requiring the user to manually configure network settings. Their effectiveness and stability are frequently compromised compared to root-based solutions.
Manual Configuration Methods
Directly manipulating network configurations through the Android system settings is another approach. This method is often less prone to conflicts with other applications and less likely to compromise the device’s stability, but it usually requires technical proficiency with the device’s network settings.
- This method usually involves navigating the device’s settings menu, locating the Wi-Fi or mobile network settings, and manually changing the MAC address in the advanced configuration options (if available). This approach is usually less efficient compared to dedicated applications.
Comparison of Spoofing Methods
The following table summarizes the effectiveness, complexity, and safety of different MAC address spoofing methods on Android.
Ever wanted to change your Android phone’s MAC address? It’s surprisingly straightforward to do, but it’s crucial to understand the potential implications. This is where the need for robust security practices, like those discussed in Deploying AI Code Safety Goggles Needed , becomes paramount. After all, understanding the risks of tampering with your device’s network identity is just as important as learning the technical steps to spoof it.
| Method | Effectiveness | Complexity | Safety |
|---|---|---|---|
| Root-based applications | High | Medium | Low (if using untrusted apps) |
| Non-root applications | Low to Medium | Low | Medium |
| Manual configuration | Low | High | High |
Note: Effectiveness, complexity, and safety are relative and can vary depending on the specific application or method used.
Potential Pitfalls and Limitations
Spoofing a MAC address might not always be successful. Network administrators or security systems might implement measures to detect and block spoofed addresses. Additionally, some network connections might require a valid MAC address for authentication, rendering spoofing attempts ineffective.
- Compatibility issues can arise when using certain applications, especially non-root applications. These applications may not be compatible with all Android versions or network configurations, leading to unpredictable behavior or failure to change the MAC address.
- Network detection mechanisms are becoming more sophisticated, making spoofing less reliable in preventing identification by network administrators.
Practical Steps for Spoofing MAC Address
MAC address spoofing, while seemingly innocuous, can have implications for network security. Understanding the practical steps involved in spoofing a MAC address on an Android device is crucial for both security awareness and troubleshooting. This process, when performed improperly, can lead to network connectivity issues, security vulnerabilities, and potential misuse. However, it’s important to remember that spoofing a MAC address is not inherently malicious.
Sometimes, it’s a necessary troubleshooting step or a requirement for specific network configurations.This section will Artikel the step-by-step procedure for spoofing a MAC address using a third-party application, along with potential errors and troubleshooting tips.
Using a Third-Party App for MAC Address Spoofing
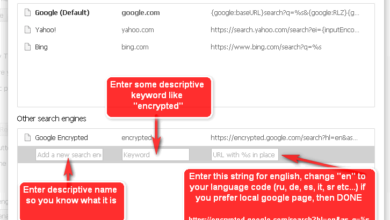
Using a dedicated application is a common approach for spoofing a MAC address on Android. These apps typically offer a user-friendly interface for selecting and changing the MAC address. Before proceeding, ensure the app you select has a reputation for reliability and security.
- Download and Install the App: Download a reputable third-party app designed for MAC address spoofing from a trusted app store. Verify the app’s developer and user reviews to ensure its safety and reliability. Be cautious of apps from unknown sources.
- Grant Necessary Permissions: The app will likely require specific permissions to access network settings. Review the permissions requested and grant them accordingly. This usually includes network access and potentially root access if the app requires it for more advanced MAC address manipulation.
- Locate the Spoofing Function: Once the app is open, navigate to the section dedicated to MAC address manipulation. This usually involves a specific button or option within the app’s interface.
- Select a New MAC Address: The app should provide a mechanism to choose or generate a new MAC address. It might include an option to generate a random MAC address or to manually input a specific one. Manual input is less common but could be required for specific network configurations.
- Confirm the Change: After selecting the new MAC address, confirm the change. The app should display a confirmation message or update the interface to indicate the successful spoofing of the MAC address.
Permissions and Configurations
The necessary permissions and configurations for MAC address spoofing apps can vary. The following table summarizes the typical requirements.
| App Function | Permissions Required | Configuration Details |
|---|---|---|
| Accessing Network Settings | ACCESS_NETWORK_STATE, INTERNET | Required for identifying and interacting with the network interface. |
| Modifying MAC Address | ROOT access (in some cases) | Some apps might require root access to directly modify the system’s network settings. |
| Displaying current MAC Address | ACCESS_WIFI_STATE | Required to display the current MAC address. |
Troubleshooting Common Issues
Several issues can arise during the MAC address spoofing process. Here are some common problems and their potential solutions.
- App Crashes or Errors: If the app crashes or displays error messages, check for updates, ensure the necessary permissions are granted, or uninstall and reinstall the app.
- No Change in MAC Address: If the MAC address doesn’t change after confirming the spoofing action, ensure the app has the required permissions, restart the device, or contact the app developer for assistance.
- Network Connectivity Problems: If network connectivity issues occur after spoofing the MAC address, try restarting the network, resetting the device’s network settings, or reverting the MAC address to its original value.
Legal and Ethical Considerations
MAC address spoofing, while offering potential benefits for network management and security testing, raises significant legal and ethical concerns. Understanding these implications is crucial for responsible use of this technique. Misuse can lead to severe consequences, ranging from fines to legal action. Careful consideration of the potential risks and ethical implications is essential.The legality of MAC address spoofing varies significantly depending on the jurisdiction and the intended use.
Some jurisdictions may permit it under specific circumstances, while others may view it as a violation of network security regulations. It’s essential to consult local laws and regulations before attempting MAC address spoofing.
Legal Implications of MAC Address Spoofing
Understanding the legal ramifications of MAC address spoofing is vital for responsible practice. Different countries and regions have varying legal frameworks regarding network security and unauthorized access. Laws often protect network infrastructure and data, and spoofing could potentially be interpreted as an infringement.
Ever wanted to change your Android phone’s MAC address? It’s surprisingly easy to do, though the specifics vary by phone model. Fortunately, there are plenty of online guides that detail the process. Knowing how to do this can be useful in various situations, like bypassing certain network restrictions, but it’s important to understand that in some contexts, like financial transactions in Massachusetts, such modifications might be viewed differently.
The Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) for certain activities, so it’s always best to check the rules and regulations in your area before making any changes. Ultimately, understanding the legal implications alongside the technical steps is key to responsibly using this feature.
- Misuse for unauthorized access or network intrusion can lead to severe penalties. This includes fines, imprisonment, or civil lawsuits.
- Certain activities, like spoofing to evade network restrictions or security measures, may violate local regulations. This depends on the specific context and the laws of the jurisdiction.
- Spoofing to cause harm, disrupt services, or gain unauthorized access to sensitive data is a serious crime in most jurisdictions. This could be classified as cybercrime, depending on the extent of the harm caused.
Ethical Considerations of MAC Address Spoofing
Ethical considerations should always guide the use of MAC address spoofing. The potential for misuse and the impact on others must be carefully evaluated.
- Unauthorized access to networks or resources is unethical and illegal. Using spoofing for this purpose can violate privacy and security protocols.
- Causing disruption to network services or operations is unethical. Spoofing should not be used to harm or interfere with legitimate network activities.
- Respecting network policies and regulations is crucial. Spoofing should not be used to circumvent established security protocols or network restrictions.
Potential Consequences of Malicious Use
Misuse of MAC address spoofing can result in severe consequences, including legal penalties and reputational damage.
- Penalties for unauthorized access or network intrusion can vary greatly, ranging from substantial fines to imprisonment. The severity of the consequences depends on the specific laws in the relevant jurisdiction and the nature of the offense.
- Reputational damage is another potential consequence. Using spoofing for malicious purposes can damage the reputation of individuals and organizations.
- Financial losses are possible, particularly in business contexts. Breaches caused by spoofing can lead to financial penalties, data recovery costs, and legal fees.
Ethical Use Cases of MAC Address Spoofing
MAC address spoofing can be used ethically in specific situations, such as security testing and network troubleshooting.
- Security testing: Ethical hackers use spoofing to test the security of a network. This involves simulating attacks to identify vulnerabilities. This is often done with the explicit permission of the network owner.
- Network troubleshooting: Network administrators might use spoofing to diagnose network problems. This allows them to identify and fix issues, enhancing network performance and security.
Table of Legal and Ethical Implications
| Use Case | Legal Implications | Ethical Considerations |
|---|---|---|
| Security Testing (with permission) | Generally legal if conducted with proper authorization. | Ethical if conducted with consent and appropriate safeguards. |
| Network Troubleshooting | Generally legal if within authorized network management practices. | Ethical if used for legitimate maintenance and not to circumvent security. |
| Unauthorized Access/Intrusion | Illegal and carries severe penalties. | Unethical and harmful. |
| Evading Network Restrictions | Potentially illegal depending on jurisdiction. | Unethical if done without authorization. |
Security Implications and Precautions
MAC address spoofing, while seemingly innocuous, carries significant security risks. Careless implementation or exploitation by malicious actors can compromise network security and device integrity. Understanding these risks and taking preventative measures is crucial for anyone considering this practice.Spoofing a MAC address can inadvertently expose vulnerabilities, making devices susceptible to various attacks. It’s essential to weigh the potential benefits against the potential for harm before altering your device’s MAC address.
Security Risks Associated with Spoofing
Spoofing a MAC address can be exploited in a number of ways. Malicious actors can use spoofed MAC addresses to gain unauthorized access to networks or launch denial-of-service (DoS) attacks. The spoofed MAC address could be used as a front to conceal malicious activity.
Exploitation by Malicious Actors
Malicious actors can leverage spoofed MAC addresses for various nefarious purposes. These include:
- Unauthorized Network Access: A spoofed MAC address can be used to trick network authentication systems into granting access to a device that shouldn’t have it. This could allow unauthorized users to access sensitive data or resources on the network.
- Denial-of-Service (DoS) Attacks: Spoofing can be used to overwhelm network resources, leading to service disruptions for legitimate users. By flooding the network with fake MAC address requests, attackers can exhaust the network’s capacity.
- Evasion of Security Measures: Spoofing can bypass security protocols designed to identify and block unauthorized devices. This could enable malicious actors to mask their presence on the network and avoid detection.
- Man-in-the-Middle Attacks: Spoofing can be a component of more complex attacks, such as man-in-the-middle attacks, where an attacker intercepts communication between two parties.
Vulnerabilities of Specific Spoofing Methods
Certain methods of MAC address spoofing are inherently more vulnerable than others. For example, methods relying on simple address substitution without proper authentication checks can be easily exploited. Methods that don’t properly account for network security protocols are more susceptible to attacks. A key aspect is that the spoofing technique must be carefully evaluated for potential security gaps.
Mitigating Security Risks
Implementing strong security measures can help minimize the risks associated with MAC address spoofing. Network administrators should implement robust authentication protocols to prevent unauthorized access. Additionally, employing intrusion detection systems can help identify and respond to suspicious activity. Network security is a layered approach, not just one specific measure.
Figuring out how to spoof a MAC address on your Android phone can be tricky, but it’s a valuable skill for various reasons. While not directly related, recent security breaches, like the ones affecting Azure Cosmos DB, highlight the importance of understanding network security. For in-depth details on the Microsoft Azure Cosmos DB vulnerability, check out this resource: Azure Cosmos DB Vulnerability Details.
Ultimately, knowing how to spoof a MAC address is a useful security technique, especially when combined with a strong understanding of your network environment.
Securing the Network and Device
After spoofing, securing the network and the device is paramount. The network should be configured to only allow trusted devices based on strong authentication mechanisms. The device itself should be updated with the latest security patches to mitigate potential vulnerabilities. This step is essential for maintaining a secure network environment.
Alternative Solutions to Network Restrictions
Sometimes, circumventing network restrictions isn’t about changing your device’s identity, but about finding a different path to access the desired content. MAC address spoofing is a direct approach, but it comes with risks. Alternative methods offer different trade-offs, focusing on indirect access and privacy.Network restrictions often stem from specific access controls enforced by administrators or network providers. These restrictions can be bypassed by using intermediary services that route your connection through a different network.
This approach can provide a layer of anonymity and flexibility without modifying your device’s inherent characteristics.
VPN Alternatives
VPNs (Virtual Private Networks) establish an encrypted connection to a remote server. Your traffic is then routed through this server, masking your original IP address and location. This effectively hides your online activity from your local network, allowing you to access content that might otherwise be blocked.
- Advantages: VPNs offer strong encryption, safeguarding your data from prying eyes. They provide a secure tunnel for your internet activity, increasing privacy and security.
- Disadvantages: VPN services can sometimes introduce latency, slowing down your internet speed. Not all VPNs are created equal, and some might have limitations on bandwidth or server availability.
- Example: A user residing in a country with restricted internet access can utilize a VPN server located in a region where the desired content is permitted. This allows the user to circumvent censorship and access blocked websites and services.
Proxy Server Alternatives
Proxy servers act as intermediaries between your device and the internet. They forward your requests to the desired destination, hiding your IP address from the website or service.
- Advantages: Proxy servers can often improve internet speed by caching frequently accessed content, reducing latency. They can also provide a layer of anonymity similar to VPNs.
- Disadvantages: Proxy servers typically don’t offer the same level of security as VPNs, as the encryption may be limited or absent. Proxy servers are also subject to potential downtime or overload.
- Example: A user can utilize a proxy server to access geo-restricted streaming services or bypass content filters at work or school.
Comparison of Spoofing and Alternative Solutions
| Feature | MAC Address Spoofing | VPN | Proxy Server |
|---|---|---|---|
| Mechanism | Changes the MAC address of the device | Establishes an encrypted connection through a remote server | Forwards requests through an intermediary server |
| Security | Low; can be detected and blocked | High; strong encryption | Low to moderate; often lacks encryption |
| Privacy | Limited; only hides the device’s identity on the local network | High; masks your IP address and location | Moderate; hides your IP address, but not always your identity |
| Speed | Usually minimal impact | Potentially slower due to encryption and routing | Potentially faster due to caching; or slower due to server load |
| Legality | Potentially illegal in some jurisdictions | Generally legal, but usage terms may apply | Generally legal, but usage terms may apply |
Potential Limitations of Alternatives
- VPN limitations: Some VPN services may be blocked by specific networks. Choosing a reputable provider is critical to avoid security vulnerabilities or data breaches.
- Proxy server limitations: The level of anonymity and security varies widely among proxy providers. Users need to be cautious about the reliability and security measures implemented by the proxy service.
Illustrative Case Studies
MAC address spoofing, while often associated with malicious activities, can also serve legitimate purposes. Understanding the diverse applications and outcomes is crucial for a comprehensive view. This section delves into real-world scenarios, examining both ethical and legal implications.The examples below highlight how MAC address spoofing can be used for different reasons, ranging from circumventing network restrictions to enhancing security.
The outcomes vary significantly depending on the context and intent behind the action.
Real-World Scenarios of MAC Spoofing
Understanding the practical applications of MAC spoofing requires examining diverse contexts. This includes legal and ethical considerations, technical details, and ultimately, the consequences of such actions.
| Scenario | Ethical Perspective | Legal Perspective | Technical Details | Outcome |
|---|---|---|---|---|
| Circumventing Network Restrictions | Potentially unethical if bypassing legitimate restrictions. Can be ethical if the restriction is deemed unreasonable or discriminatory. | Illegal if violating terms of service or contractual agreements. Legitimate if within the user’s rights and not causing harm. | Modifying the MAC address in the network interface configuration to access a network that would otherwise be blocked. This often involves using specific tools or commands. | Success in accessing the network or failure due to network security measures. |
| Enhancing Network Security (by a Network Administrator) | Highly ethical when used to enhance network security by a network administrator. | Legal when performed by authorized personnel within the scope of their duties. | Using MAC address filtering to prevent unauthorized access to the network. | Increased network security, preventing malicious actors from gaining access. |
| Masking Identity for Privacy | Ethical when used to maintain privacy and anonymity online. | Legal if not violating any laws or regulations regarding anonymity. | Using a spoofed MAC address to mask the original device’s identity on a public network. | Enhanced privacy and anonymity while using a network. |
| Testing Network Security | Ethical when used for authorized security testing and penetration testing. | Legal when performed with proper authorization and within legal boundaries. | Using a spoofed MAC address to test network security measures for vulnerabilities. | Identification of vulnerabilities and potential weaknesses in the network. |
Legitimate Uses of MAC Spoofing, How to spoof mac address of an android phone
There are situations where MAC address spoofing is employed for legitimate purposes, often within the context of network administration or testing.
- Network Security Testing: A network administrator might use MAC spoofing to test the security of their network by simulating unauthorized access attempts. This helps identify potential vulnerabilities and weaknesses before malicious actors exploit them.
- Circumventing Network Restrictions (Legitimate Case): A user might need to connect to a network that blocks specific MAC addresses. Spoofing their MAC address to gain access would be legitimate if the restriction is considered unreasonable or discriminatory.
- Network Administration: Network administrators might use MAC spoofing to troubleshoot network issues or to temporarily switch devices to different network segments. This might involve changing a device’s MAC address to isolate it for diagnostics.
Ethical Considerations in MAC Spoofing
The ethical implications of MAC spoofing hinge on the specific context and the intent behind the action. While using a spoofed MAC address to bypass network restrictions may be perceived as unethical, a network administrator using the same technique to test network security would be considered ethical.
Last Point
In conclusion, spoofing a MAC address on your Android phone can be a useful tool, but it’s crucial to understand the potential risks and ethical considerations. While there are legitimate reasons to change your MAC address, be mindful of the legal and security implications. Always weigh the pros and cons before making any changes to your device’s network settings.
We hope this guide has been informative and helpful in your journey to understanding MAC address spoofing.
FAQs: How To Spoof Mac Address Of An Android Phone
What are the potential risks of spoofing a MAC address?
Spoofing a MAC address can potentially expose your device to security vulnerabilities, making it easier for malicious actors to gain access or disrupt your network. It’s essential to understand the risks before attempting any spoofing techniques.
Are there any legal implications to consider?
The legality of MAC address spoofing varies depending on your location and intended use. Always research the legal implications in your jurisdiction before making any changes to your device.
What are some alternative solutions to network restrictions?
Alternatives to spoofing include using a VPN or proxy server. These methods provide different advantages and disadvantages compared to MAC address spoofing. Researching these alternatives can be a beneficial approach before spoofing.
Can MAC address spoofing be used for ethical purposes?
Yes, MAC address spoofing can be used for ethical purposes, such as security testing or troubleshooting network issues. However, it’s crucial to use it responsibly and within legal boundaries.