How to Use Asset Management Software for Cyber Risk Reduction
How to use your asset management software to reduce cyber risks is crucial in today’s digital landscape. Protecting your valuable assets, from hardware and software to sensitive data, is paramount. This comprehensive guide explores strategies to leverage your asset management software for enhanced cybersecurity, identifying vulnerabilities and implementing robust protection measures.
We’ll delve into practical steps, from identifying and classifying assets to implementing strong access controls, data encryption, and monitoring systems. We’ll also cover crucial elements like regular audits, training programs, and incident response planning, all tailored to bolstering your cybersecurity posture within your asset management systems.
Introduction to Asset Management Software and Cyber Risks
Asset management software is a crucial tool for organizations to track, manage, and monitor their various assets, from physical hardware to intellectual property and sensitive data. This software centralizes information, enabling better control and decision-making across the organization. It’s a cornerstone of operational efficiency and strategic planning, especially in today’s interconnected world. However, this very interconnectedness introduces a significant vulnerability to cyberattacks.Cybersecurity is paramount in asset management.
Failure to adequately protect assets can lead to financial losses, reputational damage, legal ramifications, and operational disruptions. A well-defined cybersecurity strategy integrated with asset management software is critical to mitigating these risks. This approach not only safeguards assets but also helps organizations maintain compliance with regulations and industry best practices.
Types of Cyber Risks in Asset Management
Organizations using asset management systems face a diverse array of cyber threats. These threats range from malicious software (malware) targeting specific assets to broader attacks compromising the entire system. Phishing attempts, ransomware, and insider threats are all potential risks. Data breaches, especially of sensitive information tracked within the asset management system, can have catastrophic consequences. Consequently, robust cybersecurity measures are essential.
Categories of Assets and Potential Cyber Threats
Understanding the different types of assets and their susceptibility to cyber threats is critical for effective risk mitigation. The table below Artikels various asset categories and associated potential cyber risks.
| Asset Category | Potential Cyber Threats |
|---|---|
| Hardware (servers, computers, network devices) | Malware infections, denial-of-service attacks, unauthorized access, physical theft or damage leading to data loss. |
| Software (applications, operating systems) | Exploitation of vulnerabilities in software, malware infections targeting specific applications, unauthorized modifications of software leading to system compromise. |
| Data (customer information, financial records, intellectual property) | Data breaches, ransomware attacks, unauthorized access and exfiltration of sensitive data, insider threats involving data theft or leakage. |
| Intellectual Property (designs, patents, trademarks) | Theft or unauthorized access to intellectual property, sabotage or damage to intellectual property data, potential use of stolen IP for malicious purposes. |
| Contracts and Agreements | Compromise of confidential agreements and contracts leading to financial losses or legal issues, disclosure of sensitive clauses, manipulation of contract terms. |
Implementing Security Measures within Asset Management Software: How To Use Your Asset Management Software To Reduce Cyber Risks

Implementing robust security measures within your asset management software is crucial for mitigating cyber risks. A well-structured security framework, integrated directly into the software, provides a layered defense against threats. This approach ensures that security policies are consistently applied across all assets, reducing vulnerabilities and improving overall security posture.Effective asset management software goes beyond simply tracking assets; it allows for proactive security measures to be built into the very fabric of the system.
This includes defining clear security roles, implementing strong access controls, and automating security updates. By automating these tasks, organizations can significantly reduce the risk of human error and ensure consistent security practices.
Identifying and Classifying Assets
Proper asset identification and classification are foundational to effective security. A clear understanding of what assets exist and their respective sensitivity levels enables targeted security measures. Asset management software should allow for the categorization of assets by type (hardware, software, data), criticality, and sensitivity. This categorization facilitates the implementation of tailored access controls, enabling granular management of access privileges.
This process should incorporate a thorough inventory of all assets, including physical and digital resources, and their associated data. For example, sensitive customer data requires a higher level of protection than internal documentation.
Implementing Access Control Measures
Access control measures are essential for regulating who can access specific assets and what actions they can perform. Implementing granular access control within the asset management software ensures that only authorized personnel have access to specific data or resources. This limits the potential impact of a security breach and safeguards sensitive information.
Strong Password Policies
Robust password policies are paramount to preventing unauthorized access. These policies should mandate complex passwords, frequent password changes, and strong password guidelines. Implementing a password manager within the asset management software can further enhance password security by automating password creation and management. For instance, passwords should incorporate a mix of uppercase and lowercase letters, numbers, and special characters.
Password complexity should be evaluated regularly to meet industry standards and regulatory requirements.
Implementing Multi-Factor Authentication
Implementing multi-factor authentication (MFA) adds an extra layer of security for critical assets. MFA requires users to provide multiple forms of verification, such as a password and a code from a mobile device, to access sensitive data or resources. This approach makes it significantly harder for attackers to gain access, even if they have compromised a user’s password.
The software should support different authentication methods for different asset types. For instance, MFA for accessing sensitive financial data might require a hardware token in addition to a password and a code from a mobile device.
Comparing Access Control Methods
| Access Control Method | Description | Strengths | Weaknesses ||—|—|—|—|| Role-Based Access Control (RBAC) | Grants access based on user roles. | Simple to implement, scalable, and centralized management. | May not be granular enough for highly sensitive assets. || Attribute-Based Access Control (ABAC) | Grants access based on attributes of the user, resource, and environment. | Highly granular, flexible, and adaptable to evolving security needs.
Strengthening your asset management software’s security is crucial, and this involves more than just basic password protection. For example, implementing robust access controls and regularly updating software are key steps. Recent news regarding the Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) highlights the importance of staying ahead of evolving cyber threats.
By staying proactive and leveraging the features of your asset management software, you can significantly mitigate potential risks.
| More complex to implement and maintain than RBAC. || Rule-Based Access Control (RBAC) | Grants access based on predefined rules. | Simple to implement and maintain, particularly for simple scenarios. | Limited flexibility and less adaptability to evolving security needs. |
Regular Software Updates and Patch Management
Regular software updates and patch management are crucial for maintaining the security of the asset management software. Vulnerabilities in the software can be exploited by malicious actors, making it essential to install security patches promptly. Automating the update process within the software minimizes the risk of human error and ensures that the software is always running on the most secure version.
This process should include automated patch deployment, rollback procedures, and regular security audits. Software should have a centralized update system to streamline the patch management process and to ensure consistency across all systems.
Data Security and Protection Strategies
Protecting sensitive data within your asset management software is paramount. A robust security posture not only safeguards your company’s information but also builds trust with clients and partners. Implementing comprehensive data security strategies is crucial for maintaining compliance with industry regulations and avoiding costly breaches. These strategies go beyond basic access controls and encompass a layered approach to encryption, backups, and data loss prevention.
Data Encryption Strategies
Data encryption is a fundamental component of securing sensitive information within your asset management system. By converting readable data into an unreadable format, encryption makes it practically impossible for unauthorized individuals to access and utilize the information. Strong encryption algorithms are essential for safeguarding confidential data, such as financial records, intellectual property, and customer details.
- Implementing strong encryption algorithms: Modern encryption algorithms, such as Advanced Encryption Standard (AES), provide robust security. AES-256, for instance, utilizes 256-bit keys, making it extremely difficult to crack. Choosing appropriate algorithms for different data types is vital, aligning sensitivity levels with the strength of the encryption.
- Full Disk Encryption: Consider encrypting entire hard drives or partitions containing sensitive data. This approach ensures that all data is encrypted, even if the system is compromised. This is especially important for laptops and portable storage devices. This also prevents unauthorized access to data if the device is lost or stolen.
- Database Encryption: Encrypting data within the asset management database ensures that any unauthorized access to the database will not yield readable data. This is crucial for safeguarding sensitive data within the database itself.
Data Backup and Recovery Methods
Regular data backups are vital for disaster recovery and business continuity. Implementing a robust backup and recovery strategy mitigates the risks associated with data loss due to hardware failures, accidental deletion, or malicious attacks. Data loss can have significant financial and operational consequences.
- Regular Backups: Implement a scheduled backup process to regularly copy data to a separate location. This ensures that you have a recent copy of your data available in case of a system failure or data loss. Frequency should be determined by the criticality of the data and the tolerance for data loss.
- Offsite Backup Storage: Store backups in a secure offsite location to protect against physical damage or theft affecting the primary data storage. Cloud storage solutions are a common option for offsite backups.
- Redundancy and Testing: Implement redundancy in your backup strategy to ensure data availability in the event of a backup failure. Regularly test your backup and recovery process to ensure its effectiveness.
Data Loss Prevention (DLP) Tools
Data Loss Prevention (DLP) tools are essential for preventing sensitive data from leaving the organization’s control. These tools monitor data access, identify sensitive information, and prevent its unauthorized transmission or export.
- Data Classification: Classify data based on its sensitivity to determine the appropriate level of protection. This enables targeted protection for sensitive data. This process involves identifying different types of data and categorizing them according to sensitivity.
- Access Controls: Restrict access to sensitive data based on user roles and permissions. This ensures that only authorized personnel can access and modify sensitive information. This helps to control who can access what data and to what extent.
- Monitoring and Alerting: Monitor data transfer and identify potential data breaches. These tools can trigger alerts for suspicious activity or attempts to export sensitive data. This proactive monitoring helps detect security threats and enables quick response.
Data Encryption Algorithm Comparison
Different encryption algorithms offer varying levels of security. A comparison table can aid in selecting the most suitable algorithm for specific data types.
| Algorithm | Key Size (bits) | Security Strength | Performance |
|---|---|---|---|
| AES-128 | 128 | Good | High |
| AES-192 | 192 | Excellent | Moderate |
| AES-256 | 256 | Exceptional | Low |
| RSA | Variable | Good for asymmetric encryption | Moderate |
Configuring and Using Backup and Recovery Solutions
Different backup and recovery solutions have varying configuration options. Thorough understanding of these options is essential for effective data protection.
- Solution Selection: Choose a solution that aligns with your organization’s needs and budget. This involves considering factors like storage capacity, backup frequency, and recovery time objectives.
- Configuration: Configure the backup solution to regularly back up critical data to a secure location. This involves defining backup schedules, selecting storage options, and setting up recovery procedures.
- Testing: Regularly test the backup and recovery process to ensure that data can be restored successfully in the event of a disaster. This verifies the effectiveness of the recovery procedures.
Secure Data Storage Practices
Secure data storage practices encompass the physical and logical security measures to protect data from unauthorized access and damage. This includes physical security controls, such as access control and environmental protection, as well as logical controls, such as encryption and access management.
- Physical Security: Employing physical security measures such as access control systems, environmental controls, and secure storage facilities. This ensures that sensitive data is protected from physical threats such as theft or damage.
- Access Control: Implement strong access control mechanisms to restrict access to sensitive data based on user roles and permissions. This limits the potential impact of unauthorized access.
- Regular Audits: Regularly audit data storage practices to identify vulnerabilities and implement necessary improvements. This proactive approach ensures that the security measures are up-to-date and effective.
Monitoring and Alerting Systems for Cyber Threats
Robust cyber security relies heavily on proactive monitoring and rapid response to threats. This involves setting up systems that detect anomalies and suspicious activities in real-time, enabling swift intervention and minimizing potential damage. By constantly scanning for vulnerabilities and potential breaches, organizations can significantly enhance their overall security posture.Implementing real-time monitoring for potential cyber threats requires a multi-layered approach.
This involves integrating various security tools and technologies, and continuously analyzing data generated by these tools to identify patterns and indicators of compromise (IOCs). The key is to establish automated alerts for suspicious activities, and have clear protocols for incident response.
Real-Time Monitoring for Potential Cyber Threats
Real-time monitoring of asset management data requires a combination of network monitoring, endpoint detection and response (EDR), and security information and event management (SIEM) tools. These tools capture and analyze vast amounts of data, identifying potentially malicious activities as they occur. Implementing a robust logging and auditing system is critical to capturing all activity on the system, making it easier to track suspicious patterns.
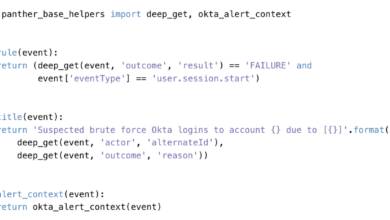
Establishing Automated Alerts for Suspicious Activities
Automated alerts are crucial for timely response to potential cyber threats. These alerts should be configured to trigger on specific events, such as unusual login attempts, unauthorized file access, or suspicious network traffic patterns. The alert system must be designed to filter out false positives, preventing unnecessary disruptions and maintaining operational efficiency. Alerts should be prioritized based on severity and potential impact to ensure that critical issues receive immediate attention.
Identifying Anomalies in Asset Management Data
Identifying anomalies in asset management data is a critical aspect of proactive threat detection. This involves developing statistical models and algorithms to identify deviations from expected behavior. Anomaly detection should be continuously updated and refined based on new data and evolving threat landscapes. Regular review of the detection rules and parameters is essential to ensure effectiveness and accuracy.
Using your asset management software effectively is key to minimizing cyber risks. For example, if you’re managing cloud assets, understanding vulnerabilities like those detailed in the Azure Cosmos DB Vulnerability Details is crucial. Knowing your cloud infrastructure’s weak points allows you to prioritize patching and security measures, ultimately bolstering your overall security posture. This proactive approach is vital in today’s threat landscape.
For example, if a particular server suddenly experiences a spike in disk I/O activity outside of normal operational parameters, this could indicate a potential malware infection and should trigger an alert.
Structured Guide to Identify Anomalies
1. Define Baseline Behavior
Using your asset management software effectively is key to reducing cyber risks. Knowing where all your digital assets are located is a great first step. But, modernizing your security approach also means deploying AI-powered tools, like the ones discussed in Deploying AI Code Safety Goggles Needed , to proactively identify and mitigate vulnerabilities. This proactive approach, coupled with robust asset management, significantly strengthens your overall cybersecurity posture.
Establish normal operational patterns for assets. This includes identifying typical access patterns, resource utilization, and data flow.
2. Develop Statistical Models
Employ statistical methods to model expected behavior. Use data from the baseline to create models and identify deviations from the norm.
3. Implement Anomaly Detection Algorithms
Utilize algorithms like machine learning and AI to identify deviations from the established baseline.
4. Continuous Monitoring and Adjustment
Continuously monitor asset data for anomalies and update the models and algorithms as needed to adapt to changing conditions.
Security Monitoring Tools
| Tool Type | Description | Example |
|---|---|---|
| Network Intrusion Detection/Prevention Systems (IDS/IPS) | Monitor network traffic for malicious activity and block or alert on suspicious patterns. | Snort, Suricata |
| Endpoint Detection and Response (EDR) | Monitor activity on individual devices for malicious software or unauthorized actions. | Microsoft Defender, CrowdStrike Falcon |
| Security Information and Event Management (SIEM) | Centralize security logs from various sources to provide a comprehensive view of security events. | Splunk, QRadar |
| Vulnerability Management Tools | Identify and prioritize vulnerabilities in systems and applications. | Nessus, OpenVAS |
Incident Response Planning
A well-defined incident response plan is essential for handling security breaches effectively. This plan should Artikel procedures for detecting, containing, eradicating, recovering, and learning from security incidents. Clear communication channels and responsibilities must be established in advance to ensure swift and coordinated action during a crisis. It’s crucial to practice the plan regularly to ensure preparedness and identify areas for improvement.
Regularly testing and refining the plan is critical for maximizing effectiveness and minimizing the impact of any security incident.
Training and Awareness Programs
Investing in robust training and awareness programs is crucial for bolstering the cybersecurity posture of your organization. A well-trained workforce is the first line of defense against cyber threats, significantly reducing the risk of data breaches and other security incidents. Effective training programs go beyond simply providing information; they empower users to recognize and respond appropriately to potential threats.Cybersecurity awareness training should be an ongoing, integrated part of your organization’s security strategy, rather than a one-time event.
Consistent reinforcement through regular training sessions ensures that employees retain and apply their knowledge effectively. This proactive approach reduces the likelihood of human error, a common vector for cyberattacks.
Importance of User Training in Cybersecurity Awareness
User training is paramount in fostering a culture of cybersecurity awareness. Employees who understand the risks and threats associated with cyberattacks are less likely to fall victim to phishing scams or other social engineering tactics. This proactive approach to security empowers employees to identify potential threats and report them promptly, which is essential in mitigating the impact of a security incident.
It’s a crucial investment in protecting sensitive data and maintaining the integrity of your organization’s systems.
Creating Effective Training Programs for Asset Management Software Users
Training programs should be tailored to the specific needs and roles of your asset management software users. For example, different levels of access require different levels of training. A user with administrative privileges needs a deeper understanding of security protocols than a user with read-only access. Training modules should be interactive and engaging, incorporating real-world scenarios and examples relevant to their daily tasks.
This approach makes the learning experience more memorable and effective.
Best Practices for Educating Users About Phishing and Social Engineering Tactics
Effective training should focus on recognizing the hallmarks of phishing and social engineering attacks. Users should be taught to scrutinize emails, messages, and websites for suspicious elements, such as poor grammar, urgent requests, and unusual sender addresses. Regularly updating training materials with the latest phishing techniques and examples is essential for maintaining relevance and effectiveness. Emphasize the importance of verifying information independently before acting on requests.
Security Awareness Topics for Asset Management Staff
A comprehensive list of security awareness topics tailored for asset management staff should cover these areas:
- Identifying and reporting suspicious emails and messages.
- Recognizing phishing and social engineering tactics.
- Protecting sensitive data, both online and offline.
- Understanding the importance of strong passwords and password management.
- Recognizing and reporting suspicious website activity.
- Safeguarding physical access to asset management systems and data.
- Understanding and adhering to company policies on data security.
- Procedures for handling lost or stolen devices.
- Recognizing and reporting potential data breaches.
- Understanding the organization’s incident response plan.
These topics equip asset management staff with the knowledge to safeguard company data and systems from cyber threats. Consistent training ensures that these practices are embedded in their daily routines.
Sample Training Module: Recognizing and Reporting Suspicious Activities
This module focuses on recognizing and reporting suspicious activities, a critical aspect of cybersecurity awareness.
- Introduction: This module introduces the importance of recognizing and reporting suspicious activities to protect sensitive information and systems.
- Identifying Phishing Attempts: Review examples of common phishing tactics, including email spoofing, fake websites, and malicious links. Discuss how to spot these attempts by looking for inconsistencies in email addresses, grammar, and urgent requests.
- Recognizing Social Engineering Tactics: Provide examples of social engineering attempts, such as impersonation and pretexting. Explain how these tactics exploit human psychology to gain access to sensitive information. Examples include fake support requests and requests for personal information.
- Reporting Procedures: Detail the process for reporting suspicious activities, including who to contact and the information to provide. Emphasize the importance of promptly reporting any suspicious activity.
- Case Studies: Present real-world case studies illustrating the impact of successful phishing attacks and how they can be avoided. Explain how these incidents led to data breaches or system compromise.
- Interactive Exercises: Include interactive exercises to reinforce learning, such as identifying phishing emails or evaluating social engineering scenarios.
This sample module demonstrates a structured approach to educating users about suspicious activities, crucial for safeguarding against potential threats.
Regular Audits and Assessments
Regular security audits and assessments are crucial for maintaining a strong security posture within your asset management software. They provide a systematic way to identify vulnerabilities, evaluate the effectiveness of existing controls, and ensure ongoing compliance with security standards. Proactive audits allow for timely mitigation of potential threats before they escalate into costly incidents.Thorough assessments not only identify existing weaknesses but also help anticipate future risks, adapting your security strategy to evolving threats.
This proactive approach reduces the likelihood of data breaches and system disruptions, safeguarding your sensitive information and maintaining operational efficiency.
Conducting Regular Security Audits
Security audits are systematic reviews of your asset management software’s security controls. They involve examining policies, procedures, and technical implementations to ensure they align with security best practices. A well-structured audit process typically includes these steps:
- Defining scope and objectives: Clearly Artikel the specific areas and systems to be audited, and establish the goals of the audit. This initial step ensures focus and efficiency.
- Documenting existing security controls: Detail all security policies, procedures, technical measures, and access controls in place. This baseline helps in identifying gaps.
- Evaluating the effectiveness of controls: Assess how effectively current security measures mitigate risks. This step involves reviewing the design, implementation, and operational effectiveness of each control.
- Identifying vulnerabilities and risks: Pinpoint weaknesses and potential threats that could compromise the security of your asset management software. This is crucial for prioritizing remediation efforts.
- Reporting findings and recommendations: Summarize the audit results, including vulnerabilities, risks, and suggested remediation steps. This report serves as a roadmap for improvement.
Assessing the Effectiveness of Security Measures
Assessing the effectiveness of security measures involves quantifying the level of protection they provide. This requires a multifaceted approach:
- Quantitative metrics: Track key performance indicators (KPIs) such as the number of security incidents, successful login attempts, and data breaches. This provides a numerical representation of the effectiveness.
- Qualitative analysis: Evaluate the design and implementation of security measures to assess their potential to prevent threats. This involves expert judgment and review of documentation.
- Benchmarking against industry standards: Compare your security controls and practices with established industry best practices to determine areas for improvement. This helps identify best-in-class solutions.
Examples of Penetration Testing Procedures, How to use your asset management software to reduce cyber risks
Penetration testing simulates real-world attacks to identify vulnerabilities. Common procedures include:
- Network scanning: Identifying open ports and services to discover potential entry points.
- Vulnerability scanning: Automated detection of known software flaws.
- Web application testing: Simulating attacks against web interfaces to find security weaknesses.
- Social engineering: Testing the resilience of personnel to phishing and other social engineering tactics.
Best Practices for Security Vulnerability Assessments
Effective vulnerability assessments involve these best practices:
- Regular scanning: Regularly scanning systems and applications for vulnerabilities to stay ahead of emerging threats. Automated tools and scheduled scans are essential.
- Prioritizing vulnerabilities: Ranking vulnerabilities based on their severity and potential impact to prioritize remediation efforts.
- Utilizing vulnerability management tools: Employing dedicated tools to manage the entire vulnerability lifecycle, from identification to remediation.
- Maintaining up-to-date software: Keeping software patched and updated to address known vulnerabilities.
Maintaining Logs and Monitoring Security Events
Maintaining comprehensive logs and monitoring security events is vital for incident response and proactive threat detection. Effective log management includes:
- Collecting logs from various sources: Gather logs from all relevant systems and applications.
- Analyzing logs for suspicious activity: Monitoring logs for unusual patterns or events that might indicate a security breach.
- Implementing security information and event management (SIEM) solutions: Using SIEM tools to centralize log collection, analysis, and threat detection.
- Setting up alerts for critical events: Configuring alerts to notify security personnel of significant security events.
Case Studies and Best Practices
Implementing robust cybersecurity measures in asset management software requires more than just theoretical knowledge. Real-world examples and best practices demonstrate how organizations have successfully mitigated cyber risks and the lessons learned from past incidents. Analyzing these case studies provides valuable insights into the practical application of security frameworks and standards, ultimately strengthening the overall security posture.
Successful Cybersecurity Implementations
Several organizations have effectively integrated cybersecurity into their asset management processes. For instance, a large manufacturing company implemented multi-factor authentication (MFA) across all asset management software applications, significantly reducing the risk of unauthorized access. Simultaneously, they conducted regular penetration testing to identify and address vulnerabilities proactively. This proactive approach helped prevent potential data breaches and maintain business continuity.
Another example showcases a healthcare provider that leveraged encryption technologies to protect sensitive patient data within their asset management system. By encrypting both in-transit and at-rest data, they adhered to strict industry regulations and ensured patient privacy.
Mitigation of Cyber Risks in Asset Management Processes
Organizations have employed various strategies to mitigate cyber risks within their asset management processes. These include: implementing strong access controls, regularly updating software and hardware, conducting vulnerability assessments, and establishing incident response plans. These proactive measures often lead to a reduced attack surface and improved incident handling capabilities. Furthermore, thorough employee training programs on cybersecurity best practices are crucial.
A strong security culture, built on awareness and vigilance, is essential in preventing security breaches.
Lessons Learned from Past Security Incidents
Examining past security incidents in asset management systems reveals valuable lessons. One common theme is the importance of proactive security measures. Organizations that failed to implement regular vulnerability assessments or update their software quickly often suffered more severe consequences. Another significant lesson is the critical role of employee awareness training. Many incidents stemmed from human error or a lack of understanding about security protocols.
Consequently, organizations now prioritize employee training to build a security-conscious workforce.
Security Frameworks and Standards
Different security frameworks and standards provide guidelines and best practices for implementing cybersecurity in asset management software. These frameworks often offer a structured approach to managing risks and vulnerabilities.
| Framework/Standard | Description | Key Focus Areas |
|---|---|---|
| NIST Cybersecurity Framework | Provides a comprehensive approach to managing cybersecurity risks across different sectors. | Identify, Protect, Detect, Respond, Recover |
| ISO 27001 | An international standard for information security management systems. | Risk assessment, security policies, and controls |
| SOC 2 | A framework for assessing and reporting on the security controls of a company. | Security, availability, processing integrity, confidentiality, and privacy |
Industry Regulations and Compliance
Industry regulations and compliance requirements significantly impact asset management security. For instance, in the healthcare industry, HIPAA regulations mandate the protection of sensitive patient data. Similarly, financial institutions must adhere to strict regulations like PCI DSS to safeguard financial information. These regulations often dictate specific security controls and reporting requirements, ensuring data protection and compliance. Organizations must carefully evaluate relevant industry regulations to establish appropriate security measures and ensure they remain compliant.
Conclusive Thoughts
In conclusion, proactively addressing cyber risks within your asset management software is not just a best practice, but a necessity. By implementing the strategies Artikeld in this guide, you can significantly reduce vulnerabilities, protect your organization’s assets, and maintain a robust cybersecurity posture. Remember, a well-defended asset management system is a critical component of a strong overall security strategy.
Let’s work towards a safer digital future.
FAQ Explained
What are some common cyber threats targeting asset management systems?
Common threats include malware infections targeting specific asset types (e.g., ransomware encrypting critical software), phishing attacks aiming to gain unauthorized access to sensitive data, and insider threats where malicious or negligent employees compromise systems.
How can I choose the right security monitoring tools?
Consider factors like the size and complexity of your asset management system, the types of assets you manage, and your budget. Look for tools with real-time monitoring capabilities, customizable alerts, and the ability to integrate with existing systems. Evaluate vendor reputation and support services.
What is the role of user training in reducing cyber risks?
User training plays a vital role by educating employees about potential threats like phishing scams and social engineering tactics. Well-structured training programs empower employees to recognize and report suspicious activities, reducing the likelihood of successful attacks.
How often should security audits be performed?
Regular security audits, ideally quarterly or biannually, are essential to assess the effectiveness of security measures and identify any weaknesses. The frequency can be adjusted based on the criticality of assets and the specific security posture of the organization.