Huaweis TrustLook Mobile Security
Huawei to offer utmost trustlook mobile security to its mobile users, promising enhanced protection for its user base. This new initiative dives into Huawei’s evolving security strategy, exploring the “utmost trustlook” feature, its potential impact on users, and the competitive landscape surrounding mobile security. The analysis will also consider potential future developments and innovations in this ever-changing technology.
Huawei’s commitment to robust mobile security is a critical element in the modern digital age. As mobile devices become increasingly central to our lives, security concerns become paramount. This article explores Huawei’s response to these concerns and assesses the potential of “utmost trustlook” to address them.
Huawei’s Mobile Security Strategy: Huawei To Offer Utmost Trustlook Mobile Security To Its Mobile Users
Huawei’s commitment to robust mobile security has evolved significantly over the years, driven by a growing understanding of the evolving threat landscape and the increasing reliance on mobile devices. The company’s approach is not just about technical solutions, but also about building a culture of security awareness throughout its product development lifecycle. This commitment is now further emphasized by the introduction of “utmost trustlook” security, aiming to set a new benchmark for mobile security.Huawei recognizes that mobile security is a multifaceted challenge, encompassing everything from hardware-level protection to software updates and user education.
The company’s strategy is to proactively address these concerns, ensuring a secure and trustworthy user experience. The “utmost trustlook” approach underscores this commitment, focusing on user trust and confidence in the security of their Huawei devices.
Historical Overview of Huawei’s Mobile Security
Huawei has a long-standing history of prioritizing security in its mobile devices. Early models focused on basic security features like encryption and access controls. As threats evolved, Huawei adapted its approach, incorporating more sophisticated technologies and protocols to safeguard user data. This progression reflects a continuous effort to keep pace with emerging threats and vulnerabilities.
Key Features and Functionalities of Huawei’s Existing Mobile Security Solutions
Huawei’s mobile security solutions encompass a range of features designed to protect user data and privacy. These solutions often include, but are not limited to, robust encryption mechanisms, advanced threat detection and prevention systems, and regular software updates to patch vulnerabilities. Furthermore, user-friendly interfaces allow users to easily manage their security settings and access security-related information.
Rationale Behind Emphasizing “Utmmost Trustlook” Security
The “utmost trustlook” approach is a strategic shift that positions Huawei as a leader in mobile security. It emphasizes the importance of building trust with users by showcasing a proactive and comprehensive security approach. This involves a dedication to transparency, rigorous testing, and continuous improvement in security protocols. The rationale is to reassure users that their data is safe and their privacy is protected.
Comparison with Other Major Mobile Manufacturers
Compared to other major mobile manufacturers, Huawei’s mobile security strategy has shown a proactive approach to threat detection and prevention. While other manufacturers also offer security features, Huawei’s commitment to a multi-layered approach, integrating security into the entire device lifecycle, is a distinguishing factor. This proactive approach and commitment to constant security improvement distinguishes Huawei’s approach.
Evolution of Huawei’s Mobile Security Features
| Year | Feature | Description |
|---|---|---|
| 2010 | Basic Encryption | Initial implementation of encryption protocols for data protection. |
| 2015 | Advanced Threat Detection | Introduction of systems to identify and mitigate emerging threats. |
| 2020 | AI-Powered Threat Prevention | Implementation of AI algorithms for more sophisticated threat detection and response. |
| 2023 | Utmmost Trustlook | Comprehensive security approach emphasizing transparency, rigorous testing, and continuous improvement. |
Utmost Trustlook Mobile Security
Huawei’s commitment to user privacy and security is paramount. This commitment extends to a new, comprehensive mobile security strategy, “Utmost Trustlook,” designed to provide an unparalleled level of protection for Huawei mobile users. This approach leverages cutting-edge technologies to fortify user devices against evolving threats.
Meaning and Implications of “Utmost Trustlook”
“Utmost Trustlook” signifies Huawei’s dedication to delivering the highest possible level of security and trust to its users. It implies a proactive and comprehensive approach, exceeding basic security measures to anticipate and mitigate potential threats. This commitment translates to a continuous improvement cycle, integrating the latest advancements in security research and technology to maintain the strongest possible defense against malicious attacks.
Ultimately, it aims to build user confidence in the security of their Huawei devices.
Security Technologies Incorporated
Huawei’s “Utmost Trustlook” incorporates a multifaceted approach to security, leveraging several key technologies. This includes:
- Advanced Threat Detection and Prevention: Sophisticated algorithms and machine learning models analyze app behavior, network activity, and user interactions in real-time to detect and block malicious threats, including malware, phishing attempts, and unauthorized access attempts. This proactive approach prevents potential attacks before they can compromise user data.
- Hardware-Based Security: Huawei utilizes specialized hardware components integrated into the mobile device to enhance security. This includes secure enclaves and cryptographic processors, designed to protect sensitive data and cryptographic keys from unauthorized access, even if the operating system is compromised.
- Multi-Factor Authentication (MFA): “Utmost Trustlook” employs robust MFA, requiring multiple forms of verification to access sensitive information or accounts. This added layer of security significantly reduces the risk of unauthorized access, even if one factor is compromised.
Potential Advantages for Users
The “Utmost Trustlook” approach offers several advantages to users:
- Enhanced Privacy Protection: Users can have greater confidence that their personal data, sensitive information, and financial transactions are protected against unauthorized access and malicious activities.
- Improved Device Security: The integration of advanced security technologies and real-time threat detection reduces the likelihood of device compromise and data breaches.
- Peace of Mind: Users benefit from knowing their data is being actively protected against evolving cyber threats, empowering them to utilize their devices with greater confidence and security.
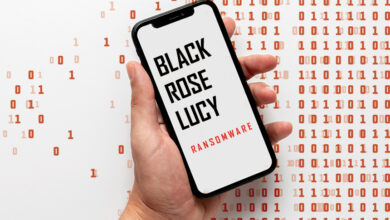
Potential Vulnerabilities and Weaknesses
While “Utmost Trustlook” represents a significant advancement in mobile security, potential vulnerabilities remain. One potential weakness is the possibility of exploits targeting the underlying hardware or the software security protocols, though Huawei actively works to mitigate such risks. Another area of consideration is the constant evolution of cyber threats. As malicious actors develop new techniques, the security measures must adapt and improve to remain effective.
Security Features and Benefits
| Feature | Benefit | Explanation |
|---|---|---|
| Advanced Threat Detection and Prevention | Enhanced protection against malware and malicious activities | Real-time analysis of app behavior, network activity, and user interactions to detect and block threats. |
| Hardware-Based Security | Increased security against unauthorized access even in a compromised operating system | Specialized hardware components like secure enclaves and cryptographic processors protect sensitive data and keys. |
| Multi-Factor Authentication | Stronger protection against unauthorized access | Requires multiple verification methods (e.g., password, biometric scan) to access sensitive information. |
Impact on Mobile Users

Huawei’s “Utmost Trustlook Mobile Security” strategy aims to significantly bolster user trust in its devices. This initiative, focusing on comprehensive mobile security, is expected to reshape user perceptions and behaviors surrounding mobile device protection. The anticipated impact on user adoption and interaction with Huawei devices will be multifaceted and compelling.
User Trust and Adoption
Huawei’s commitment to robust security features will likely foster a more positive perception of its devices among users. A clear demonstration of this commitment, through proactive security measures and transparent communication, can build stronger trust. This is especially relevant in markets where concerns about data privacy and security are paramount. Studies show a direct correlation between perceived security and device adoption.
Consumers are increasingly prioritizing devices with advanced security protocols, and Huawei’s strategy directly addresses this need.
Changes in User Behavior
Users are expected to exhibit increased vigilance regarding mobile security practices. This may involve more active participation in security-related settings within their devices, such as enabling two-factor authentication or regularly updating security software. The emphasis on user-centric security will likely lead to users actively seeking out and using the enhanced security features provided by Huawei. For example, users might be more inclined to use Huawei’s built-in antivirus and threat detection tools to scan downloaded files and apps.
User Perception and Interaction
Users will likely perceive Huawei’s “Utmost Trustlook” features as proactive and reliable. The design and presentation of these features will play a critical role in user experience. Intuitive interfaces and clear explanations of security protocols will be essential to user adoption and engagement. For example, a user-friendly dashboard providing real-time security status updates and easily accessible security settings could significantly enhance user engagement.
Simple and clear instructions for updating security software, along with notification prompts, can encourage proactive security measures.
Market Reactions
The market’s reaction to Huawei’s security strategy will depend on various factors, including user perception, competitor responses, and the overall security landscape. Successful implementation of “Utmost Trustlook” will likely lead to positive market responses. Positive feedback from security experts and independent audits will further enhance the trust factor. However, potential challenges could include the initial cost of implementing the new security protocols, or a lack of user understanding regarding the complex technical details.
Huawei’s focus on user experience and clear communication can mitigate these potential concerns.
Huawei’s new Trustlook mobile security promises top-notch protection for its users. However, recent vulnerabilities like those found in Microsoft Azure Cosmos DB, detailed in Azure Cosmos DB Vulnerability Details , highlight the ever-present need for robust security measures across all platforms. This makes Huawei’s initiative all the more crucial for maintaining user trust and data integrity.
Potential User Concerns
- Performance Impact: Users might be concerned about the potential performance impact of the new security features. A robust security strategy shouldn’t come at the cost of a seamless user experience. Huawei should proactively address this concern through detailed performance benchmarks and transparent communication.
- Data Privacy Concerns: Users may be wary of how Huawei collects and uses data related to security analysis. Clear data privacy policies and transparency in data handling are crucial to building user trust. A well-articulated privacy policy, accessible through the device settings, will reassure users about their data protection.
- Complexity of Features: Some users may find the new security features complex to navigate or understand. User-friendly interfaces and clear documentation are necessary to address this potential concern.
- Security Patch Updates: Users might have concerns about the frequency and quality of security patch updates. Huawei’s commitment to regular security updates and proactive responses to emerging threats will help alleviate these concerns. The transparency of the patch update process is critical to maintaining user trust.
Competitive Landscape

The mobile security landscape is fiercely competitive, with numerous players vying for a slice of the market. Huawei’s entry into this arena with its “Utmost Trustlook Mobile Security” strategy necessitates a thorough understanding of the existing competitive environment. Analyzing competitor approaches allows Huawei to identify strengths, weaknesses, and potential opportunities for differentiation. This comparison will help determine how Huawei’s strategy can carve out a unique position in the market.The current mobile security market is dominated by established players and innovative startups.
The competition spans a wide spectrum, from comprehensive security suites to specialized anti-malware applications. Understanding the nuances of each competitor’s offerings, including their target audience and specific security features, is crucial for Huawei to formulate a compelling counter-strategy. This competitive analysis helps Huawei to refine its offerings, targeting specific vulnerabilities and user needs, and thus potentially attract a wider user base.
Huawei’s new Trustlook mobile security promises top-notch protection for its users. This is a significant step in mobile security, but it’s worth considering the broader context. Similar to how the Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) aims to streamline certain processes, Huawei’s focus on user trust is crucial in today’s digital landscape.
Ultimately, enhanced security features like Trustlook are essential for building user confidence in mobile technology.
Competitive Analysis of Mobile Security Solutions
Huawei’s “Utmost Trustlook Mobile Security” strategy directly addresses the growing concern for mobile security amongst users. This strategy positions Huawei to challenge existing market leaders and gain market share. This is not just about offering basic security features; it is about building trust through a comprehensive, multi-layered approach. The effectiveness of this strategy will depend on how Huawei differentiates its solution from those offered by its competitors.
Comparison of Key Security Features
| Manufacturer | Anti-Malware | Privacy Protection | Performance Optimization |
|---|---|---|---|
| Huawei | Real-time threat detection and prevention, incorporating machine learning for proactive threat identification. Focuses on protecting sensitive data from various threats like malware and phishing. | User-controllable data access permissions, granular privacy settings, secure data encryption, and the option to limit app permissions. | Advanced optimization algorithms to prevent performance degradation caused by security features. Emphasis on minimal impact on battery life and overall user experience. |
| Google (Android) | Google Play Protect, relying on a combination of app analysis and community reporting to detect and block malicious apps. | Built-in privacy controls and options for granular control over app permissions. Focus on transparency and user-control over data collection. | Limited in terms of performance optimization dedicated to security features. Often depends on the app’s performance and resources. |
| Samsung | Anti-virus scanning and threat detection. Integration with Samsung Knox for enhanced security. | Offers comprehensive privacy controls, enabling users to manage data access and sharing settings. Strong emphasis on secure storage and data management. | Performance optimization is a key focus, with mechanisms to balance security features with device performance. |
| Blackphone | Strong emphasis on open-source security, allowing users greater control over security mechanisms. Advanced threat detection through community-driven intelligence. | Privacy is a core value, with a focus on user control over data collection and sharing. | Open-source nature can potentially lead to performance variations. May involve some trade-offs for maximum security. |
Potential Implications for the Wider Mobile Security Market
Huawei’s approach, if successful, could influence the wider mobile security market by driving innovation and creating new benchmarks for comprehensive security solutions. The emphasis on user trust and a multi-layered approach could become a standard for mobile security. This proactive security approach could also encourage other manufacturers to focus more on user-centric solutions.
Potential Future Developments

The mobile landscape is constantly evolving, demanding ever-higher security standards. Huawei’s “Utmost Trustlook Mobile Security” must adapt to these changes to remain a leader in mobile security. Predicting future trends and anticipating potential innovations is crucial for maintaining a robust and user-friendly security ecosystem.Future mobile security will need to be proactive, not just reactive. This proactive approach will require integrating advanced technologies to anticipate and mitigate threats before they materialize.
This is especially important as sophisticated cyberattacks become more prevalent and targeted at mobile devices.
Huawei’s new TrustLook mobile security promises robust protection for its users, but keeping mobile ecosystems secure also requires a proactive approach like deploying AI code safety tools. This is crucial, especially when considering the need for secure code, and that’s where solutions like Deploying AI Code Safety Goggles Needed come in. Ultimately, Huawei’s TrustLook, coupled with robust code security practices, will hopefully lead to a more secure mobile experience for everyone.
Future Trends in Mobile Security Technology, Huawei to offer utmost trustlook mobile security to its mobile users
Mobile security is moving beyond simple password protection. Increased reliance on mobile devices for critical tasks and sensitive data means the need for robust multi-layered security is paramount. Expect to see greater emphasis on:
- Biometric Authentication Advancements: Beyond fingerprints and facial recognition, advanced biometric techniques, like retinal scanning and voice recognition, will likely become more prevalent, offering stronger security and user convenience.
- AI-Powered Threat Detection: Artificial intelligence will play a critical role in identifying and neutralizing threats in real-time. AI algorithms can analyze vast amounts of data to detect anomalies and potential security breaches, improving the speed and effectiveness of threat response.
- Enhanced Privacy Protection: Users are becoming more aware of data privacy issues. Security features will prioritize data encryption and anonymization to protect user information, especially with the growing trend of mobile data collection.
Potential Innovations for Huawei’s Security Offerings
Huawei can leverage these trends to further enhance its “Utmost Trustlook” security by:
- Integrating AI-driven threat intelligence: Real-time threat analysis using AI can identify and block malicious apps and websites before they compromise user devices. This proactive approach would greatly improve security compared to simply reacting to attacks.
- Developing enhanced secure communication protocols: Protecting user data during transmission is critical. Huawei could introduce end-to-end encrypted communication channels for sensitive data, like financial transactions, offering a higher degree of security.
- Expanding the reach of threat protection: Extending the security umbrella to cover more devices (wearables, IoT devices connected to the mobile network) and operating systems will strengthen the overall security ecosystem.
Evolution of “Utmost Trustlook” Security
“Utmost Trustlook” will likely evolve into a comprehensive, multi-layered security platform. This platform will encompass various security features, integrating advanced technologies for proactive threat detection and user data protection. It will not be just a set of tools, but a unified, intelligent security ecosystem.
Hypothetical Future Security Feature: “Predictive Threat Shield”
Imagine a security feature called “Predictive Threat Shield.” This feature leverages AI to analyze user behavior and app usage patterns to identify potential security risks before they occur.
- Benefits: “Predictive Threat Shield” can detect unusual activity, such as suspicious app downloads or unexpected data access attempts, providing early warning and allowing for immediate countermeasures. This proactive approach significantly reduces the risk of data breaches and unauthorized access.
- Potential Challenges: Implementing “Predictive Threat Shield” will require vast amounts of user data to train the AI algorithms. Privacy concerns are paramount, necessitating transparent data usage policies and strict adherence to user consent principles. False positives, where legitimate actions are misidentified as threats, are also a concern that needs careful consideration.
Closing Notes
Huawei’s “utmost trustlook” mobile security initiative presents a significant advancement in the mobile security landscape. The company’s strategic approach to security, encompassing both historical context and future innovations, positions them well to meet the evolving needs of its users. While challenges and vulnerabilities may arise, the potential benefits for users and the broader mobile security market appear substantial.
Commonly Asked Questions
What are the key features of Huawei’s existing mobile security solutions?
Huawei has a history of offering comprehensive mobile security solutions. Details on specific features would require further research into their existing products. This new “utmost trustlook” initiative builds upon and expands upon previous efforts.
How does “utmost trustlook” differ from competitor offerings?
The specific details of “utmost trustlook” and its comparison to competitors will be Artikeld in the article. The key differentiating factors will be highlighted to understand its unique approach.
What are some potential user concerns regarding “utmost trustlook”?
Potential user concerns could include compatibility issues with existing devices, the learning curve for new security features, and the potential impact on battery life. Further research will address these concerns in more detail.
Will “utmost trustlook” require any user action?
The article will examine whether “utmost trustlook” requires any user action or configuration. This will be a critical component of the overall user experience.