Intel Processors Recognizing Ransomware at Hardware Level
Intel processors to recognize ransomware attacks at hardware level sets the stage for a fascinating new approach to cybersecurity. This innovative technology promises to detect malicious activity before it can even encrypt your data, offering a potential game-changer in the fight against ransomware. The discussion will explore how Intel processors can identify and react to suspicious behavior, providing a real-time shield against these sophisticated threats.
We’ll delve into the intricate details, comparing software-based detection to the cutting-edge hardware approach, and exploring the security implications and potential challenges of this transformative technology.
The article will provide a detailed overview of how Intel processors are being designed to recognize the unique patterns and characteristics of ransomware attacks directly at the hardware level. This will involve an examination of the specific features within Intel’s architecture, as well as the mechanisms used to integrate ransomware detection capabilities. Finally, we’ll discuss the implications for future cybersecurity trends and potential areas for further research.
Introduction to Hardware-Level Ransomware Detection
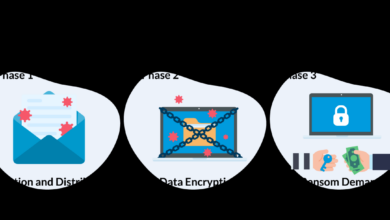
Ransomware is a type of malicious software designed to encrypt a victim’s files and demand payment for their release. It operates by exploiting vulnerabilities in software and often leverages social engineering tactics to gain initial access. This encryption, often irreversible without the decryption key, can severely impact individuals and organizations, leading to significant financial losses and operational disruptions.
Traditional methods of ransomware protection primarily rely on software-based solutions, but hardware-level detection offers a new layer of defense.Hardware-level security offers a powerful means of countering ransomware by detecting malicious activities at the core of the system, before software can even react. By embedding security features directly into the processor architecture, we can achieve greater speed and reduced performance impact compared to software-based methods.
This approach can also hinder the sophistication of ransomware attacks.
Ransomware Attack Methods and Types
Ransomware attacks utilize various methods to compromise systems. These methods include exploiting vulnerabilities in software, phishing emails, malicious websites, and even drive-by downloads. Different types of ransomware target specific vulnerabilities and systems. Crypto-ransomware, for instance, encrypts files, demanding a ransom for decryption. Locker ransomware locks users out of their devices.
Ransomware-as-a-service (RaaS) allows attackers to purchase and use ransomware tools without technical expertise. The targeting strategies vary, from individuals to large organizations, often exploiting vulnerabilities in operating systems or applications.
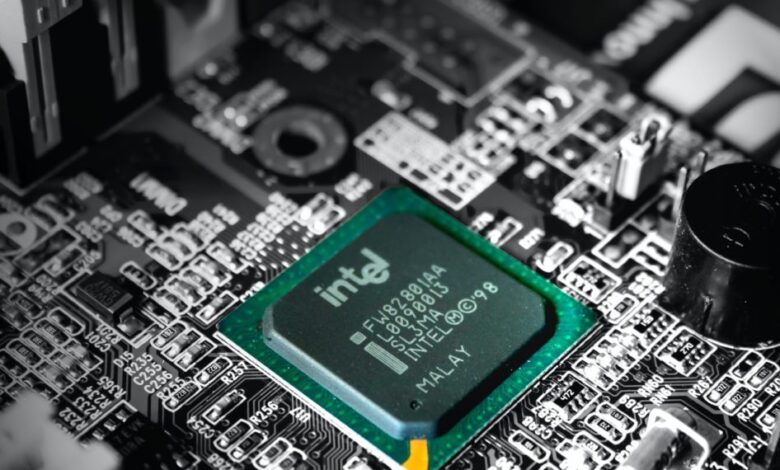
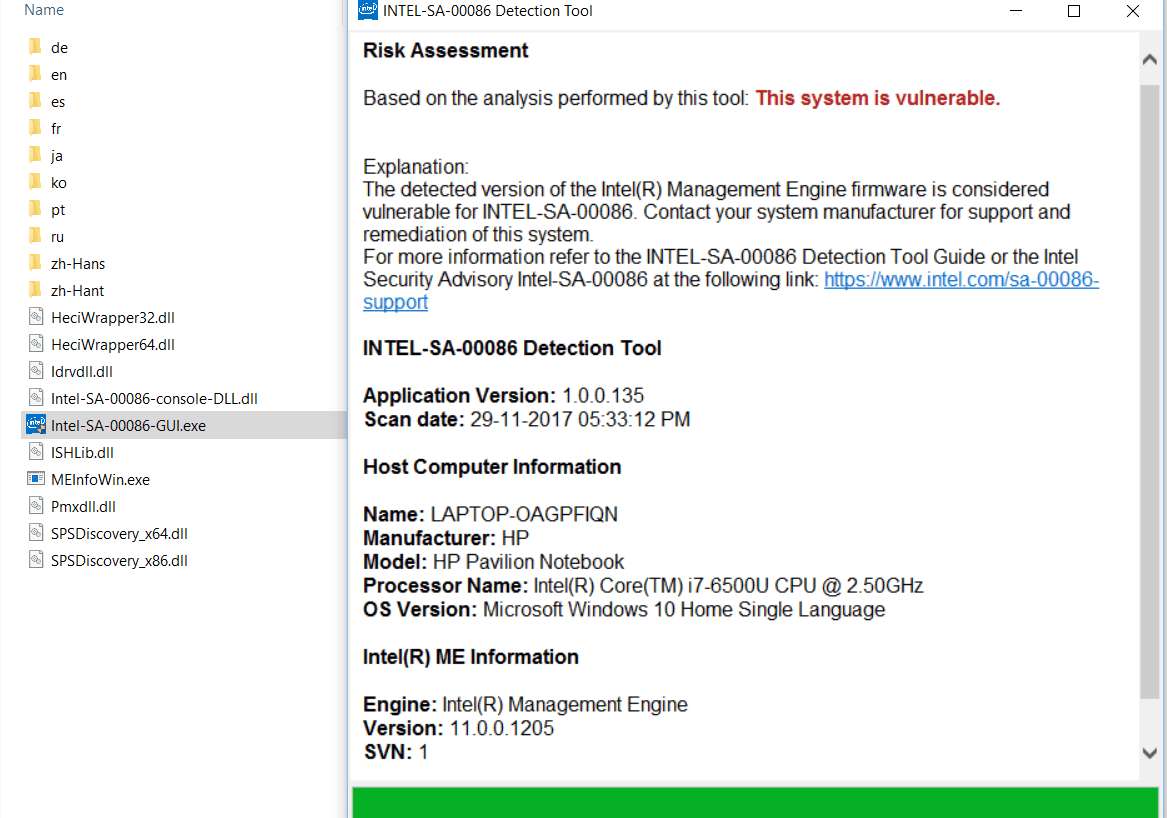
Hardware-Level Security and Intel Processors
Hardware-level security incorporates security features directly into the processor architecture. This approach can detect malicious activities early in the process, often before software has the opportunity to respond. Intel processors, known for their sophisticated architecture, include advanced security features designed to protect against threats like ransomware. These features often include specialized instructions and hardware modules designed to detect and prevent malicious code execution.
The combination of Intel’s architecture and hardware-level security features provides a robust defense against modern threats.
Comparison of Software and Hardware-Based Ransomware Detection, Intel processors to recognize ransomware attacks at hardware level
| Feature | Software-Based Detection | Hardware-Based Detection |
|---|---|---|
| Detection Method | Analysis of system behavior, file integrity monitoring, and heuristic rules. | Direct monitoring of processor instructions and memory access patterns. |
| Speed | Can be slower, depending on the complexity of the attack and the software’s processing capacity. | Faster, as it operates at a lower level, without the overhead of software. |
| Performance Impact | Potentially significant impact on system performance, especially during intensive analysis or scans. | Minimal impact on system performance, as the detection occurs in the background, without extensive processing. |
Intel Processor Features for Ransomware Detection
Intel processors are increasingly incorporating hardware-level security features designed to detect and mitigate ransomware attacks. These advancements allow for real-time threat analysis and early intervention, significantly reducing the damage potential of successful intrusions. The integration of advanced micro-architecture and specific hardware capabilities enables a proactive approach to cybersecurity, bolstering the overall resilience of systems.Leveraging these built-in safeguards offers a crucial advantage in the ever-evolving landscape of cyber threats.
This approach moves beyond relying solely on software-based solutions, enhancing the detection and response mechanisms available to combat ransomware.
Specific Hardware Features for Malicious Activity Recognition
Intel processors utilize a variety of hardware features to detect suspicious activities, including memory access patterns, instruction execution sequences, and system behavior anomalies. These features work in concert to identify patterns often indicative of ransomware.
- Memory Access Monitoring: Intel processors can track memory access patterns in real-time. Ransomware frequently exhibits unusual and voluminous memory allocations, writes, and reads. By monitoring these activities, the processor can identify deviations from typical system behavior, raising an alert when unusual patterns emerge.
- Instruction Execution Analysis: The processor can analyze the instructions being executed. Malicious code often employs specific instruction sequences or techniques to obfuscate its actions or to modify system files. The processor can identify these unique patterns and alert on potential malicious activity.
- System Behavior Monitoring: Hardware can monitor system-wide behavior for anomalies. Ransomware often involves specific actions, like creating a large number of new files, encrypting data, or attempting to disable security measures. The processor can recognize these collective activities and identify a ransomware attack.
Leveraging Features for Real-Time Threat Detection
These hardware features can be leveraged to build real-time threat detection mechanisms. A dedicated hardware unit within the processor can constantly monitor system activity, immediately recognizing suspicious patterns and triggering alerts. This approach provides a critical advantage in preventing the spread of ransomware.
- Dedicated Hardware Unit: A specialized hardware unit, integrated into the processor, continuously observes system operations. This unit acts as a dedicated security sensor, identifying malicious code based on its characteristics, rather than solely relying on software-based signatures.
- Early Detection and Alerting: The hardware unit can alert the operating system to potential threats in real time. This proactive approach enables swift response measures, minimizing the impact of a ransomware attack.
Role of Micro-architecture in Identifying Ransomware Patterns
The micro-architecture of Intel processors plays a critical role in identifying ransomware patterns. Advanced micro-architectures can accelerate the detection process by enabling faster analysis of memory access and instruction sequences.
- Advanced Micro-architecture Enhancements: Modern micro-architectures are designed to recognize complex patterns and unusual behavior. Sophisticated algorithms integrated into the hardware enable faster and more accurate analysis, enabling quicker identification of ransomware.
- Pattern Recognition Capabilities: These micro-architectures can recognize intricate patterns in code execution and memory access that may not be detected by purely software-based systems. This ability is crucial in identifying advanced ransomware.
Detecting Suspicious System Behavior
Hardware-level monitoring allows for the detection of suspicious system behavior indicative of ransomware. This is achieved by analyzing various factors, including file system changes, network activity, and the creation of unusual processes.
- File System Monitoring: Hardware can monitor changes to the file system in real-time, identifying the creation, deletion, or modification of files that align with ransomware activity. This includes identifying patterns of file encryption or file renaming.
- Network Activity Analysis: The processor can monitor network traffic to detect unusual outbound connections, potentially indicative of ransomware attempting to exfiltrate data or communicate with command-and-control servers.
- Process Creation Monitoring: Hardware can track the creation of new processes and their behavior. Ransomware often creates and executes unusual processes, which can be detected by the processor and flagged as potential threats.
Limiting Impact of Successful Attacks
Hardware-level security measures can limit the impact of a successful ransomware attack. By identifying and isolating the compromised components, hardware can prevent the spread of the infection.
- Isolation of Compromised Components: Hardware can isolate compromised parts of the system, preventing the ransomware from spreading further. This can be achieved by isolating processes, files, or network connections.
- Prevention of Data Encryption: In some cases, hardware can prevent the encryption of files or data, preventing the ransomware from achieving its goal.
Mechanisms for Implementing Hardware-Level Ransomware Detection
Hardware-level ransomware detection is a crucial step in bolstering cybersecurity defenses. This approach offers a proactive method to identify malicious activities before they can compromise system integrity. By embedding detection capabilities directly into the processor architecture, we can anticipate and mitigate attacks with greater efficiency and speed. This allows for real-time threat analysis and rapid response mechanisms.
Design Principles of a Hardware Module
A dedicated hardware module for ransomware detection needs to be designed with several key principles in mind. It must be lightweight, minimizing its impact on processor performance. Crucially, the module should be highly specific, focusing on identifying patterns characteristic of ransomware, rather than attempting broad-spectrum threat detection. This allows for faster and more targeted responses. The module must also be resistant to evasion techniques employed by advanced attackers.
Integrating Ransomware Detection Capabilities
The integration of ransomware detection capabilities into Intel processors requires a multi-stage approach. First, a specialized detection unit needs to be designed and integrated into the processor’s microarchitecture. This unit will be responsible for monitoring system activity in real-time. Second, a set of predefined heuristics and signatures specific to ransomware behaviors must be embedded within the detection unit.
Third, a mechanism for communicating detected threats to the operating system and application layers must be established. This allows for appropriate countermeasures to be deployed swiftly.
Techniques for Identifying Ransomware-Related Operations
The hardware module must employ various techniques to identify ransomware-related operations. These methods need to be highly accurate to prevent false positives. Ransomware frequently exhibits specific behavioral patterns, which can be exploited for detection. These patterns are often related to file encryption, network communication, or unusual process activity.
| Technique | Description | Example |
|---|---|---|
| Behavioral Analysis | Monitoring system activity for patterns indicative of ransomware, such as unusual file access, encryption, and network communication. | Detecting rapid and numerous file modifications, or large-scale encryption operations on various file types. |
| Signature-Based Detection | Identifying known ransomware signatures or code patterns in memory or in system calls. | Recognizing specific encryption algorithms or code snippets known to be associated with ransomware families. |
| Heuristic Analysis | Using rules and algorithms to detect suspicious behaviors that do not necessarily match known signatures. | Detecting processes that are attempting to modify critical system files or execute commands in a non-standard manner. |
| Machine Learning | Utilizing machine learning models to analyze system activity and identify anomalies indicative of ransomware. | Training a model to recognize patterns of malicious activity based on vast datasets of ransomware and benign system behaviors. |
System Monitoring and Logging
System monitoring and logging play a vital role in hardware-level ransomware detection. Monitoring crucial system parameters, such as file system activity, network traffic, and process behavior, can highlight suspicious activities. Comprehensive logging allows for detailed analysis of these events, enabling identification of malicious patterns and timely intervention. Logging of such activities is critical to forensic analysis and incident response.
Intel processors are getting smarter, learning to identify ransomware attacks at the hardware level. This proactive approach is crucial in the ever-evolving cybersecurity landscape, especially considering recent developments like the Department of Justice Offers Safe Harbor for MA Transactions here. While these legal protections are helpful, the advanced hardware-level detection in Intel processors offers a truly preventative measure against these malicious attacks, providing a strong layer of defense against ransomware threats.
This information is crucial for understanding the extent of the attack and for developing effective countermeasures in the future.
Security Implications and Challenges
Hardware-level ransomware detection offers a promising new approach to combating this sophisticated threat. However, relying solely on this technology presents several security implications and challenges that must be carefully considered. Implementing effective defenses requires a holistic strategy that combines hardware-level features with robust software solutions and user awareness programs.
Security Implications of Sole Reliance on Hardware
Hardware-level detection, while potentially effective, cannot be the sole solution for ransomware protection. It primarily acts as a proactive measure, identifying suspicious activity and potentially preventing the encryption process. However, sophisticated attackers may develop strategies to circumvent these hardware-based safeguards. This underscores the importance of a layered security approach, including strong software-based protections.
Limitations of Hardware-Level Detection Methods
Hardware-level detection mechanisms have inherent limitations. They are only effective against known attack patterns and may not be able to identify novel or zero-day exploits. The complexity of modern ransomware, including its ability to adapt and evolve, presents a significant challenge for purely hardware-based defenses. Furthermore, false positives can impact system performance.
Challenges of Integrating Hardware with Software
Integrating hardware-level detection with existing software solutions requires careful planning and execution. Compatibility issues and the need for updated software to leverage the new hardware features are key challenges. Maintaining a consistent security posture across the entire system, from hardware to application, becomes critical. Furthermore, a robust security information and event management (SIEM) system will be necessary to correlate hardware events with software logs and user activity.
Impact of False Positives on System Performance
False positives in hardware-level detection can significantly impact system performance. Frequent, unnecessary alerts or blocks can lead to delays, reduced responsiveness, and user frustration. Sophisticated filtering mechanisms are necessary to minimize these disruptions while ensuring effective protection against ransomware. This necessitates a thorough understanding of the hardware and software interactions to accurately interpret and prioritize alerts.
Countermeasures Against Circumventing Hardware Security
Circumventing hardware-level security measures is a constant challenge for attackers. Continuously evolving hardware and software solutions is crucial. Moreover, strong software-based defenses and stringent security policies will be essential to mitigate the risk. Collaboration between hardware manufacturers and software developers is paramount to ensure a proactive and adaptable approach.
Illustrative Case Studies and Examples
Hardware-level ransomware detection is a crucial advancement in cybersecurity. This approach shifts the detection from the software layer to the processor itself, enabling a proactive and potentially preventative approach to attacks. By analyzing suspicious activities at the core of the system, hardware-level detection offers an enhanced security posture against evolving threats like ransomware. This section delves into illustrative case studies and scenarios to highlight the potential of this technology.
Scenario: A Ransomware Attack Detected
Imagine a user’s computer infected with a ransomware strain targeting financial data. The ransomware, after initial infection, begins the process of encrypting files. At this stage, the Intel hardware-level detection system, specifically designed to identify suspicious patterns of file access, recognizes anomalies in the access patterns. This includes unusually high numbers of file read/write operations and encryption algorithms used, exceeding established thresholds.
This anomaly triggers an alert, halting the encryption process before the data is fully compromised. The system isolates the infected process, preventing further encryption and data exfiltration. This scenario demonstrates how hardware-level detection can effectively prevent the encryption of critical data.
Real-World Ransomware Attacks and Hardware Mitigation
Several real-world ransomware attacks, such as the WannaCry and NotPetya outbreaks, highlighted the vulnerability of systems to widespread infections. Hardware-level detection, by analyzing patterns of malicious activity at the processor level, can potentially mitigate such attacks. For instance, if a large number of processes are attempting to encrypt files simultaneously, the hardware can flag this as a potential ransomware attack, allowing for swift intervention.
This proactive approach can significantly reduce the impact of attacks by preventing the widespread encryption and data exfiltration that often accompany these incidents.
Impact of Successful Hardware-Level Detection
Successful hardware-level detection in a real-world ransomware attack translates to significant benefits. Firstly, it prevents the encryption of sensitive data, preserving its integrity and availability. Secondly, it stops the attacker from achieving their primary goal—data extortion. Furthermore, it potentially prevents data exfiltration, preventing the unauthorized transfer of sensitive information. The system’s rapid response can minimize downtime and reduce the financial and reputational damage associated with a ransomware incident.
Preventing Data Encryption
Hardware-level ransomware detection can actively prevent data encryption by recognizing and blocking the encryption processes at a fundamental level. This approach directly intercepts the malicious activities of the ransomware before they can encrypt files. By identifying and halting the encryption routines, the hardware-level detection mechanism safeguards the data integrity. This immediate action avoids the irreversible damage often caused by data encryption.
Intel processors recognizing ransomware attacks at the hardware level is a fascinating development. However, preventing these attacks at the software level is also crucial, and deploying AI Code Safety Goggles Needed here is a vital step. Ultimately, combining these hardware and software approaches will be key to securing systems from ransomware in the future.
Preventing Data Exfiltration
Hardware-level detection systems can be programmed to recognize and block data exfiltration attempts. This involves monitoring network traffic and identifying patterns associated with unauthorized data transfer. For example, if a process attempts to transfer large amounts of encrypted data to a remote server, the hardware can intervene and block the transfer. Such measures protect sensitive information from being transmitted to attackers, thereby mitigating the risk of data leakage.
This capability is especially valuable in preventing data exfiltration that can lead to further exploitation or financial loss.
Future Directions and Research Areas: Intel Processors To Recognize Ransomware Attacks At Hardware Level
Hardware-level ransomware detection is a rapidly evolving field. The ongoing arms race between attackers and defenders necessitates continuous innovation in security strategies. Future research will focus on proactively identifying and mitigating ransomware threats before they can compromise systems. This proactive approach is critical to maintaining the integrity and availability of digital assets in an increasingly interconnected world.
Enhanced Threat Modeling and Signature Detection
Advanced threat modeling techniques are crucial for anticipating novel ransomware attack vectors. Researchers are investigating sophisticated machine learning algorithms to identify subtle anomalies indicative of malicious activity. This involves developing sophisticated signature detection mechanisms that can identify previously unseen ransomware strains, adapting to the dynamic nature of ransomware evolution. The development of these sophisticated signature detection methods will be vital in the future.
Integration with Existing Security Frameworks
Integrating hardware-level ransomware detection with existing security frameworks, such as intrusion detection systems (IDS) and security information and event management (SIEM) systems, is a key area for future development. This synergy will allow for a more comprehensive security posture, enabling early threat identification and improved incident response. The integration will enhance the overall security posture by combining the strengths of both hardware-level and software-level detection methods.
Multi-Factor Authentication and Secure Boot
Future research will investigate the integration of hardware-level ransomware detection with multi-factor authentication (MFA) mechanisms and secure boot processes. This integration will create a layered security approach, providing an additional layer of protection against unauthorized access and malicious code execution. Combining MFA with secure boot will further enhance the robustness of the security system, effectively mitigating the risk of ransomware infiltration.
Adaptive Learning and Dynamic Protection
Hardware-level detection systems should adapt to evolving ransomware tactics. Research into dynamic protection mechanisms that learn from observed patterns of malicious behavior and adapt their detection strategies in real-time is essential. This adaptive learning capability will help stay ahead of the ever-changing ransomware landscape. The systems should be able to learn and adjust to new threats in a dynamic environment.
Intel processors are making strides in recognizing ransomware attacks at the hardware level, a crucial step in cybersecurity. This advancement is especially relevant when considering vulnerabilities like those in Azure Cosmos DB, as detailed in Azure Cosmos DB Vulnerability Details. By proactively identifying threats at the foundational level, these processors can help prevent data breaches, even before software-based defenses kick in, reinforcing their importance in the fight against ransomware.
Collaboration and Standardization
Collaboration between researchers, hardware manufacturers, and security vendors is essential for standardizing hardware-level ransomware detection methods. This will ensure interoperability and ease of deployment across diverse systems and platforms. Standardization will significantly reduce deployment complexity and increase the effectiveness of security measures across a wide range of systems.
Summary
In conclusion, Intel processors to recognize ransomware attacks at hardware level represents a significant advancement in cybersecurity. By integrating detection capabilities directly into the processor, this approach offers the potential to stop ransomware attacks before they can cause significant damage. While challenges remain, such as the need for careful integration with existing software solutions, the potential benefits of this proactive approach are substantial.
This innovative technology has the potential to revolutionize how we combat ransomware, potentially becoming a critical component in future security strategies.
Question Bank
What are the specific hardware features of Intel processors used for ransomware detection?
Intel processors leverage features like advanced security extensions (e.g., SGX) and specialized instructions for system monitoring. These features allow the processors to identify unusual activity patterns indicative of ransomware attacks.
How fast is hardware-level ransomware detection compared to software-based detection?
Hardware-level detection generally offers significantly faster response times, as it operates directly within the processor’s architecture. This speed advantage is crucial for real-time threat mitigation.
What are the potential limitations of relying solely on hardware-level detection?
While effective, hardware-level detection isn’t a complete solution. Sophisticated attackers might develop methods to bypass or exploit limitations in the hardware-based security measures.
How can false positives be minimized in hardware-level detection?
Careful design and tuning of the detection algorithms are crucial to minimize false positives. Robust testing and ongoing updates to the detection mechanisms are essential to ensure accuracy and prevent unnecessary disruptions to system performance.