New Zealand Internet Outage DDoS Attack Impact
Internet in New Zealand disrupted due to a DDoS cyber attack. This crippling blow to New Zealand’s digital infrastructure highlights the vulnerability of modern societies to sophisticated cyberattacks. Businesses, individuals, and government services alike felt the immediate consequences, leading to widespread disruption and raising concerns about the long-term effects on New Zealand’s digital economy. This article delves into the impact, nature, response, and security implications of this significant event, examining the global context and offering insights into the potential lessons learned.
The attack, likely motivated by malicious intent, exploited vulnerabilities in New Zealand’s internet backbone. This caused a significant disruption across various sectors, affecting everything from online banking to essential government services. Understanding the attack’s nature, the response, and the potential security implications is critical for preparing for similar future incidents. The article further analyzes the diverse impacts on different user groups, from residential users to large corporations.
Impact on New Zealand
A recent Distributed Denial of Service (DDoS) attack significantly disrupted internet services across New Zealand. This cyberattack highlighted the vulnerability of critical infrastructure to such attacks and underscored the need for robust cybersecurity measures. The immediate consequences were felt throughout various sectors, impacting businesses, individuals, and government operations.The attack overwhelmed the internet backbone, leading to widespread outages and slowdowns.
The recent DDoS attack disrupting internet access in New Zealand highlights a critical need for robust cybersecurity measures. While the immediate problem is fixing the outage, we also need to consider preventative measures, like deploying AI Code Safety Goggles Needed here to identify and mitigate potential vulnerabilities in the codebase. Ultimately, the attack serves as a harsh reminder that these kinds of disruptions can have real-world consequences, requiring proactive measures to prevent similar events in the future.
This disruption had cascading effects, affecting a wide range of services and activities, demanding swift action from authorities and service providers to restore functionality.
Immediate Consequences
The DDoS attack caused immediate and significant disruption to New Zealand’s internet connectivity. This disruption affected various sectors, impacting businesses, individuals, and government services. Widespread outages and slowdowns severely hampered communication and access to online resources.
Sectors Affected
The attack’s impact extended across several sectors. Businesses relying on online transactions and communication were severely hampered. Individuals found their access to online services, from banking to entertainment, significantly restricted. Government services, crucial for public administration, were also disrupted.
Reported Disruptions
The disruption affected numerous online services. E-commerce platforms, online banking systems, and social media platforms experienced significant outages. This resulted in delays, frustrations, and financial losses for many businesses. Furthermore, online government services, such as online tax filing, were unavailable. Citizens faced challenges accessing critical services, impacting their daily lives.
Potential Long-Term Impacts
The incident serves as a stark reminder of the growing threat of cyberattacks and the need for stronger safeguards. Potential long-term impacts include a loss of confidence in online services, reduced investment in the digital economy, and increased costs associated with security enhancements. Similar incidents in the past have demonstrated that such attacks can have long-lasting effects on the digital economy.
For instance, a previous outage in the region had similar impacts, highlighting the potential for lasting damage.
Social and Economic Consequences
The attack had social and economic consequences for New Zealand citizens. The inability to access online services impacted businesses’ productivity and individuals’ ability to conduct everyday tasks. The disruption to government services created frustration and delays for citizens seeking essential services. Financial losses were experienced by both businesses and individuals, impacting the overall economy.
Impact on Different Internet Users
| Type of User | Impact |
|---|---|
| Residential | Limited access to online services, including banking, entertainment, and communication platforms. Difficulty in conducting everyday tasks like shopping, accessing government services, and connecting with others. |
| Business | Disrupted online transactions, communication, and operations. Significant loss of productivity and potential revenue. Inability to access customer data and manage supply chains. |
| Government | Disruption of critical services, including online tax filing, citizen services, and public information access. Potential for delays in crucial administrative processes and challenges in maintaining public order. |
Nature of the Cyberattack
The recent disruption of internet services in New Zealand highlights the escalating threat of Distributed Denial-of-Service (DDoS) attacks. Understanding the nature of these attacks is crucial to mitigating their impact and strengthening cybersecurity defenses. These attacks can cripple essential services, causing significant economic and social disruption.
Types of DDoS Attacks, Internet in new zealand disrupted due to a ddos cyber attack
DDoS attacks are characterized by overwhelming a target system with a flood of traffic from multiple sources, effectively denying legitimate users access. Various attack vectors can be employed, each with distinct methods and impacts. Understanding these differences is vital for effective response and prevention.
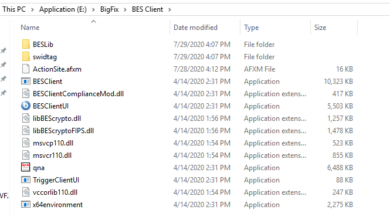
Attack Methods and Techniques
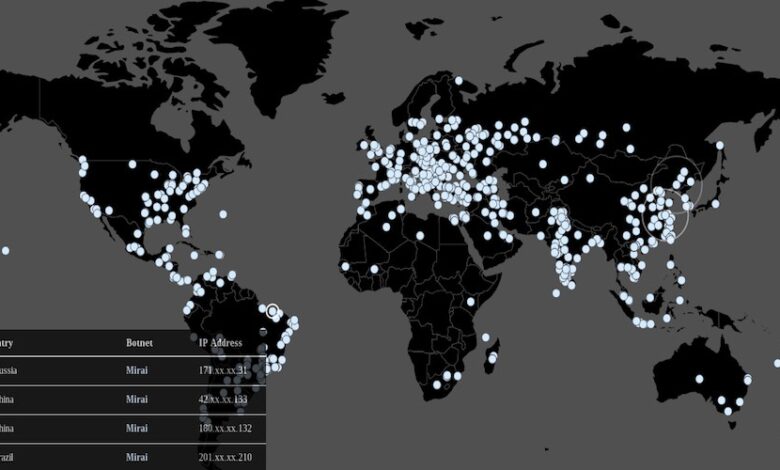
DDoS attacks employ various methods to overwhelm target systems. One common technique involves flooding the target with massive volumes of data packets, consuming available bandwidth and resources. Another strategy targets specific applications or services, exploiting vulnerabilities in the application layer. Critically, attackers often utilize botnets—networks of compromised devices—to amplify the attack’s impact.
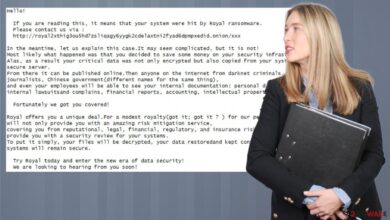
Motivations Behind the Attack
Motivations behind DDoS attacks vary widely. Sometimes, attacks are politically motivated, aiming to disrupt services or systems associated with a particular group or ideology. Other times, they are financially motivated, intended to extort money from the target or to disrupt online commerce. There are also cases where attackers engage in these acts for malicious fun or as a demonstration of their technical prowess.
Scale and Duration of the Attack
The scale and duration of a DDoS attack significantly influence its impact. Large-scale attacks can overwhelm even the most robust infrastructure, leading to prolonged service disruptions. The duration of the attack also plays a crucial role, as a sustained attack can have a more devastating effect on the victim’s operations. Past incidents show that prolonged attacks can cause severe financial losses and reputational damage.
Comparison of DDoS Attack Vectors
| Attack Vector | Description | Impact | Example |
|---|---|---|---|
| Volumetric Attacks | Flood the target with massive amounts of traffic, overwhelming network bandwidth. | Network congestion, service interruption. | UDP floods, ICMP floods. |
| Application Layer Attacks | Exploit vulnerabilities in specific applications or services, often targeting specific resources or functionalities. | Service interruption, denial of access to specific features. | HTTP floods, Slowloris attacks. |
| Protocol Attacks | Exploit weaknesses in network protocols to consume resources, such as server processing power. | Service exhaustion, server overload. | SYN floods, fragmented packet attacks. |
The table above highlights the differences in DDoS attack vectors, their impact, and common examples. Different attack types target various vulnerabilities and have distinct consequences.
Examples of Similar Attacks in the Past
Numerous high-profile DDoS attacks have occurred in recent years, disrupting services and causing substantial damage. The Mirai botnet attacks, for instance, are notable for their scale and widespread impact, targeting various organizations and services. These examples underscore the evolving nature of DDoS attacks and the need for proactive defense strategies. Similarly, the Dyn DNS attack in 2016 disrupted numerous websites and services, highlighting the vulnerability of critical infrastructure to these types of attacks.
Response and Recovery

The widespread disruption of New Zealand’s internet infrastructure due to a DDoS attack highlighted the critical need for robust response mechanisms. Swift and effective action by internet service providers, government agencies, and technical experts proved crucial in mitigating the impact and restoring essential services. The experience offers valuable lessons for future preparedness and the development of more resilient digital ecosystems.
Initial Response from ISPs
New Zealand’s internet service providers (ISPs) responded swiftly to the escalating attack, immediately implementing traffic management strategies. This involved a combination of techniques to filter malicious traffic and prioritize legitimate user requests. Their initial response was critical in preventing a complete collapse of internet services. ISPs worked collaboratively, sharing information and coordinating their efforts to lessen the impact on users.
Mitigation and Restoration Steps
The mitigation process involved several key steps. Firstly, the identification and characterization of the attack’s nature were paramount. This allowed for the implementation of targeted countermeasures. Secondly, implementing traffic filtering and redirection techniques was vital to isolate and divert malicious traffic. This often involved working with international partners to help route traffic around the attack source.
Finally, restoring service involved a phased approach. Essential services were prioritized, and the restoration process was managed carefully to avoid overwhelming the network.
Effectiveness of Response Strategies
The effectiveness of the response strategies employed was demonstrated by the relatively quick restoration of internet services. While some outages persisted, the speed and efficiency of the mitigation process limited the overall duration of the disruption. Real-time monitoring and analysis played a crucial role in adapting the response strategies in real time, allowing for quicker adjustments as the attack evolved.
This adaptability proved critical in limiting the damage.
Role of Government Agencies
Government agencies, particularly those responsible for cybersecurity and emergency management, played a critical role in coordinating the response. They acted as a central point of communication and information dissemination. Their role extended to coordinating with ISPs, providing resources, and ensuring the safety of critical infrastructure. This collaboration was vital in ensuring a cohesive and effective response.
Potential Lessons Learned
The incident highlighted the importance of proactive cybersecurity measures and the need for robust emergency response plans. Collaboration between ISPs, government agencies, and technical experts is essential for future preparedness. The incident also underscored the need for ongoing investment in advanced threat detection and mitigation capabilities. Real-time threat intelligence sharing between stakeholders will be critical in the future.
Developing a national cybersecurity strategy is critical to ensure a unified and coordinated approach to future threats.
Timeline of Attack, Response, and Recovery
| Phase | Description | Approximate Time |
|---|---|---|
| Attack Initiation | Attack launched against New Zealand’s internet infrastructure. | Early Morning |
| ISP Response | Initial response by ISPs to mitigate the attack. | Within Hours |
| Government Coordination | Government agencies begin coordinating with ISPs. | Within 24 Hours |
| Mitigation and Filtering | Implementation of traffic filtering and redirection techniques. | 24-48 Hours |
| Phased Restoration | Phased restoration of services, prioritizing essential services. | 2-3 Days |
| Full Recovery | Full restoration of internet services. | 3-5 Days |
Security Implications
The recent distributed denial-of-service (DDoS) attack highlighting New Zealand’s internet vulnerabilities underscores the urgent need for robust cybersecurity measures. This incident serves as a stark reminder that even seemingly robust infrastructure can be susceptible to sophisticated attacks. A deeper understanding of these vulnerabilities, along with a comparative analysis of global security practices, is critical to bolstering New Zealand’s digital resilience.The attack exposed critical weaknesses in the current infrastructure, prompting a need for a proactive and multifaceted approach to cybersecurity.
The swift response and recovery efforts are commendable, but the focus should now shift to strengthening the preventative measures to avoid future incidents.
Vulnerability of New Zealand’s Internet Infrastructure
New Zealand’s internet infrastructure, while generally considered stable, faces vulnerabilities similar to other developed nations. A reliance on interconnected systems, where a single point of failure can cascade into widespread disruption, makes the country susceptible to sophisticated attacks. The interconnected nature of the modern digital world makes isolation impossible; therefore, resilience is a more crucial goal.
New Zealand’s internet went down recently due to a massive DDoS attack, highlighting the vulnerability of online services. Thankfully, while the digital chaos unfolded, the Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) is a positive development, showing a proactive approach to protecting digital transactions. Hopefully, these kinds of protections can help safeguard online systems from similar disruptions in the future.
Comparison of Security Measures with Other Countries
Comparing New Zealand’s cybersecurity measures with those of other developed nations reveals a mixed picture. While New Zealand has implemented various security protocols, some countries demonstrate more comprehensive strategies, particularly in areas like proactive threat intelligence gathering and advanced threat detection. The absence of a universally accepted standard for cybersecurity creates challenges in comparative analysis. For example, the US has a more robust national cybersecurity strategy and more substantial investment in threat intelligence gathering, while the UK prioritizes collaboration and information sharing amongst government and private sectors.
This highlights the need for a tailored approach for New Zealand, adapting successful strategies from other countries while leveraging its unique context.
Potential Weaknesses in Existing Cybersecurity Infrastructure
Potential weaknesses in New Zealand’s existing cybersecurity infrastructure include a lack of centralized threat intelligence sharing and insufficient resources dedicated to proactive threat hunting. The fragmented nature of cybersecurity responsibilities across various government agencies and private sectors can hinder effective collaboration and information sharing. Limited funding for advanced threat detection tools and the skills gap in cybersecurity professionals further compound the issue.
This can be compared to the situation in other countries, where strong collaboration between government and industry sectors allows for more effective and proactive responses.
Importance of Proactive Cybersecurity Measures
Proactive cybersecurity measures are crucial to preventing future disruptions. A reactive approach, while important, is insufficient. The focus should be on identifying and mitigating potential vulnerabilities before they are exploited. This proactive approach includes continuous monitoring of network traffic, regularly updating software and hardware, and implementing strong security protocols for all users and devices.
Recommendations for Improving New Zealand’s Internet Security
- Establish a national cybersecurity strategy that Artikels clear roles and responsibilities for all stakeholders, including government agencies, private sectors, and educational institutions.
- Increase funding for cybersecurity research and development, focusing on developing innovative tools and techniques to detect and mitigate advanced threats.
- Enhance collaboration and information sharing among government agencies, private sectors, and international partners to improve threat intelligence gathering and response capabilities.
- Develop a comprehensive cybersecurity education program to address the skills gap in cybersecurity professionals.
- Implement industry-wide best practices for cybersecurity, including regular security assessments, incident response plans, and robust access controls.
Cybersecurity Best Practices for Organizations
Implementing robust cybersecurity practices is essential for organizations of all sizes. A proactive approach reduces the risk of breaches and ensures business continuity.
| Best Practice | Description |
|---|---|
| Regular Security Assessments | Identifying vulnerabilities and weaknesses through regular security audits and penetration testing. |
| Incident Response Plan | Developing and regularly testing a plan for handling security incidents, including containment, eradication, and recovery. |
| Strong Access Controls | Implementing strong authentication methods and access controls to limit unauthorized access to sensitive data. |
| Data Backup and Recovery | Creating and regularly testing backup and recovery procedures to ensure business continuity in case of data loss or system failure. |
| Security Awareness Training | Providing regular security awareness training to employees to educate them about threats and best practices for avoiding security breaches. |
Global Context: Internet In New Zealand Disrupted Due To A Ddos Cyber Attack
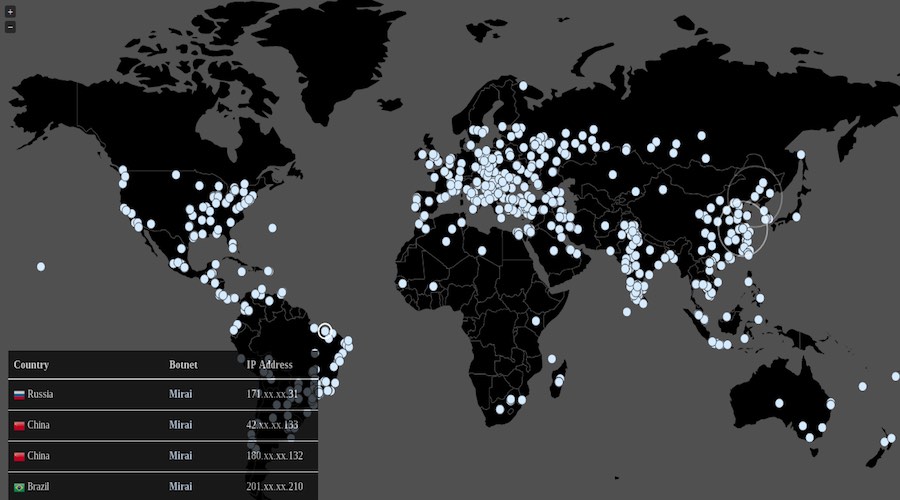
The recent DDoS attack targeting New Zealand’s internet infrastructure highlights a disturbing trend in the global cyber landscape. This isn’t an isolated incident; similar disruptions have occurred in other countries, demonstrating the pervasive threat of such attacks and the need for robust global responses. Understanding the broader context of these events is crucial to developing effective strategies for prevention and mitigation.
Comparison to Similar Disruptions Elsewhere
Numerous countries have experienced significant internet disruptions due to DDoS attacks in recent years. For example, major outages in the United States, Europe, and Asia have demonstrated the vulnerability of critical internet infrastructure to coordinated attacks. Analyzing these events reveals commonalities in attack vectors and targets, suggesting a growing sophistication and frequency of these attacks. The scale and impact of these attacks vary, depending on the specific targets and the resources of the attackers.
However, the underlying motivations and tactics often overlap.
Increasing Frequency of DDoS Attacks Globally
The frequency of DDoS attacks has been steadily rising, driven by a combination of factors. The accessibility of DDoS tools and services, often offered through the dark web, has made launching such attacks easier and more affordable for malicious actors. The rise of botnets, networks of compromised computers controlled remotely, provides attackers with a vast pool of resources to overwhelm targeted systems.
Furthermore, the increasing reliance on online services and critical infrastructure makes these systems more vulnerable. The attack vectors are becoming more sophisticated and the target scope more widespread, leading to significant disruption.
Evolving Nature of Cyber Threats
Cyber threats are constantly evolving, adapting to new vulnerabilities and technologies. The complexity of modern internet infrastructure, with its interconnected systems and diverse protocols, creates numerous points of potential attack. The rise of ransomware, phishing, and other forms of malicious software adds to the evolving threat landscape. The sophistication of attackers is also increasing, making it more difficult to detect and prevent attacks.
The attackers are using more advanced tools and techniques, making them more difficult to identify and stop.
Role of International Cooperation in Addressing Such Attacks
International cooperation is essential to effectively combat DDoS attacks. Sharing information about attack patterns, developing common security standards, and collaborating on law enforcement efforts are critical steps. This collaborative approach allows countries to learn from each other’s experiences and develop more effective strategies to mitigate these threats. International organizations like the United Nations and Interpol play a vital role in fostering this cooperation.
By pooling resources and expertise, countries can create a more robust defense against cyberattacks.
“International collaboration is paramount in the fight against DDoS attacks. Sharing information and resources across borders is essential to develop comprehensive strategies for prevention and response.”
Global Perspective on the Attack
The New Zealand incident underscores the interconnected nature of the global internet and the need for international collaboration in addressing cyber threats. The impact extends beyond national borders, highlighting the shared vulnerability of critical infrastructure and the need for collective action. Understanding the global context of such attacks is crucial for developing effective preventative measures and promoting cybersecurity awareness.
Illustrative Examples
The internet outage in New Zealand, caused by a Distributed Denial-of-Service (DDoS) attack, highlighted the vulnerabilities of modern digital infrastructure and the interconnectedness of our lives. The disruption wasn’t just an abstract concept; it had tangible consequences for businesses, individuals, and the overall economy. This section provides concrete examples of the attack’s impact.
Impact on Specific Businesses
The widespread disruption affected numerous businesses, from small startups to large corporations. A local e-commerce company, “KiwiCrafts,” experienced a significant drop in sales. Their online store was inaccessible for over 12 hours, resulting in lost orders and a substantial hit to their daily revenue. The inability to process transactions directly impacted their cash flow and threatened their short-term financial stability.
Similarly, a major online banking platform experienced a surge in support calls as customers struggled with account access and transactions.
Challenges Faced by Different Internet Users
The DDoS attack presented unique challenges for various types of internet users. Students relying on online learning resources for their education faced delays in accessing vital study materials. This disruption directly affected their ability to complete assignments and participate in online classes. Similarly, remote workers were hampered in their productivity as online communication tools and collaborative platforms became unavailable.
Examples of Affected Online Services
Numerous online services were affected by the attack. The outage impacted video conferencing platforms, effectively halting remote meetings and collaborations. This directly impacted businesses operating across multiple locations and impacted their productivity. Social media platforms experienced disruptions, impacting real-time communication and information sharing.
Economic Costs of the Disruption
Estimating the precise economic costs is challenging, but the impact was substantial. Businesses lost revenue due to lost sales and reduced productivity. The disruption in online services impacted various sectors, causing indirect economic losses. The loss of productivity across various sectors, from retail to education, amounted to a significant economic cost, which can be further illustrated with examples from similar past events.
Financial institutions also faced costs related to handling the increased customer support calls and the potential for fraudulent activities.
New Zealand’s internet went down due to a massive DDoS attack, highlighting vulnerabilities in online infrastructure. This incident brings to mind the recent security concerns surrounding Azure Cosmos DB, which has experienced a concerning vulnerability. Understanding the intricacies of such attacks, like the one affecting New Zealand, is crucial for developing robust defenses, and learning from details like those available in the Azure Cosmos DB Vulnerability Details can help us build better systems.
The disruption underscores the ever-present threat of these attacks, especially as online reliance continues to grow.
Illustrative Timeline of the Attack
A visual timeline of the attack can be presented as a simple table, demonstrating the escalation of the disruption.
| Time | Event | Impact |
|---|---|---|
| 10:00 AM | Attack Begins | Initial slowdown in internet speeds |
| 10:30 AM | Internet speeds drastically decrease | Significant impact on online services |
| 11:00 AM | Major websites and services become inaccessible | Businesses experience major disruption |
| 12:00 PM | Peak of the attack | Maximum disruption to internet access |
| 1:00 PM | Initial recovery efforts | Partial restoration of services |
| 2:00 PM | Full restoration of internet services | Return to normal online operations |
Outcome Summary
In conclusion, the recent DDoS attack on New Zealand’s internet infrastructure serves as a stark reminder of the growing threat of cyberattacks in the digital age. The swift response and recovery efforts, along with the lessons learned, are crucial for strengthening New Zealand’s cybersecurity posture. The attack’s impact underscores the importance of proactive measures, international cooperation, and continuous adaptation to evolving cyber threats.
Moving forward, New Zealand must prioritize robust cybersecurity strategies to safeguard its digital ecosystem and ensure the resilience of its critical infrastructure.
Answers to Common Questions
What types of services were affected by the outage?
The outage affected various services, including online banking, e-commerce platforms, government websites, and essential communication systems. The specific services impacted varied depending on the severity and duration of the disruption in different areas.
How long did the outage last?
The duration of the outage varied depending on the specific services and locations affected. Detailed timelines are available in the report.
What steps were taken to mitigate the attack?
New Zealand’s internet service providers and relevant government agencies implemented various mitigation strategies, including traffic filtering and network rerouting. The effectiveness of these measures is detailed in the article.
What were the economic costs of the attack?
Quantifying the precise economic costs of the attack is challenging, but the disruption undoubtedly resulted in significant financial losses for businesses and individuals. The article explores the economic ramifications further.