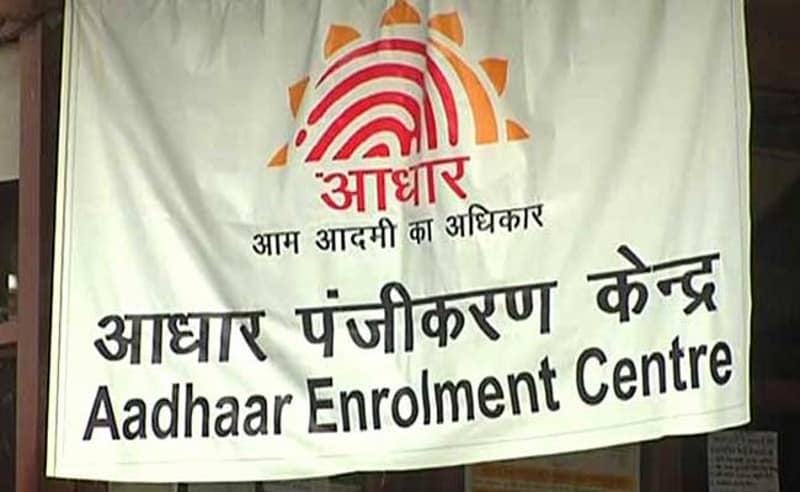
IOC Indane Leak 6.7M Aadhaar Details Exposed
Ioc indane leaks aadhaar details of 6 7 million indian citizens – IOC Indane leaks Aadhaar details of 6.7 million Indian citizens, raising serious concerns about data security. This massive breach highlights the vulnerability of personal information in the digital age, potentially impacting millions of lives. The leak exposes sensitive Aadhaar data, prompting questions about the strength of India’s data protection measures and the potential consequences for affected individuals.
The leak underscores the urgent need for robust cybersecurity protocols and enhanced data protection measures within the Aadhaar system. This incident compels a deeper look into the potential ramifications for affected individuals, the Indian government, and the overall security of India’s digital infrastructure. Further investigation is crucial to understand the extent of the damage and implement effective measures to prevent similar incidents in the future.
Background of the Leak

The recent leak of Aadhaar data, reportedly impacting millions of Indian citizens, underscores a recurring vulnerability in the digital infrastructure of a rapidly developing nation. This incident, though claimed to have been addressed, highlights the critical need for robust security measures and transparent data handling practices. The incident serves as a stark reminder of the potential consequences of data breaches in a society increasingly reliant on digital identity systems.The Aadhaar program, a biometric-based identification system, has become a cornerstone of India’s digital governance.
However, its widespread use also brings with it the risk of misuse and unauthorized access to personal information. Past incidents of data breaches and compromises, both in the Aadhaar system and other digital platforms, have highlighted the potential for large-scale breaches and the consequent impact on individuals and the nation as a whole.
Historical Overview of Data Breaches Related to Aadhaar
Multiple instances of alleged data breaches involving Aadhaar have occurred over the years. These incidents, though sometimes contested, have raised concerns about the security of the system and the protection of sensitive personal data. The nature of these breaches varies, from reported vulnerabilities to suspected unauthorized access. Each incident has prompted scrutiny of the safeguards in place to prevent such intrusions.
Potential Impact on Indian Citizens
Data breaches involving Aadhaar details can have far-reaching consequences for individuals. Loss of financial control, identity theft, and potential fraud are significant concerns. The potential for misuse of biometric data is particularly alarming, given its unique and potentially irreversible nature. For instance, unauthorized access to biometric data could lead to the creation of fraudulent identities, potentially enabling criminal activity.
Implications for National Security and Privacy
The national security implications of Aadhaar data breaches are substantial. Compromised personal data can be used to target individuals for various forms of fraud or malicious activities. The potential for foreign actors to exploit such breaches to gain intelligence or disrupt societal functions also exists. The breach poses a significant threat to individual privacy and national security.
The integrity of the national identity system is compromised when sensitive data is exposed.
Data Breaches in India: A Summary
Data breaches are not unique to Aadhaar. Many entities across sectors are vulnerable. This table provides a concise overview of various data breaches in India, highlighting affected entities and their impact on citizens.
| Type of Breach | Affected Entity | Impact on Citizens | Example |
|---|---|---|---|
| Unauthorized Access | Government Databases | Identity theft, financial fraud | Aadhaar data breach |
| Phishing Attacks | Financial Institutions | Financial losses, account compromises | Bank account hacking |
| Malware Infections | Personal Devices | Data loss, privacy violations | Ransomware attacks |
| Insider Threats | Corporate Networks | Confidential data exposure, operational disruptions | Employee misconduct |
Impact Assessment
The recent leak of Aadhaar details impacting millions of Indian citizens necessitates a thorough examination of the potential repercussions. This leakage, exposing sensitive personal information, raises significant concerns across various facets of life, demanding a comprehensive understanding of its far-reaching consequences.
Financial Ramifications
The unauthorized access to financial details, linked to Aadhaar, poses substantial financial risks. Compromised accounts, fraudulent transactions, and unauthorized access to credit lines or loans are direct threats. Individuals could face significant financial losses due to unauthorized deductions, credit card fraud, or even the freezing of accounts. For instance, a compromised bank account could lead to the loss of savings or even the inability to access essential services requiring financial transactions.
Social Consequences, Ioc indane leaks aadhaar details of 6 7 million indian citizens
The leakage of personal data can trigger significant social consequences. Discrimination based on perceived socioeconomic status or community affiliation is a serious concern. Harassment and targeted attacks based on the leaked information are also probable. Victims could face social stigma, impacting their opportunities and interactions within their communities. This could manifest in subtle forms of discrimination, such as denied employment or housing opportunities, or more extreme forms, like targeted abuse.
Legal Repercussions and Remedies
Legal repercussions for such data breaches are substantial. Affected individuals may have recourse through civil or criminal lawsuits, depending on the nature and extent of the damage. Remedies may include compensation for financial losses, emotional distress, and potential punitive damages for negligence or malicious intent. The legal framework in India pertaining to data protection and privacy violations should be reviewed and strengthened in the wake of such incidents.
Moreover, a strong regulatory framework with clear guidelines and accountability mechanisms is essential to deter future breaches.
Comparison of Data Leak Impacts Across Demographics
| Demographic | Financial Impact | Social Impact | Legal Remedies |
|---|---|---|---|
| Low-income individuals | Loss of limited savings, difficulty accessing essential services, potential for predatory lending | Increased vulnerability to discrimination, social stigma, and harassment | Limited access to legal recourse due to financial constraints, possible difficulty proving damages |
| High-income individuals | Significant financial losses, potential for identity theft and fraud, substantial legal costs for redressal | Less vulnerable to direct social discrimination, but potential reputational damage | Access to better legal resources, greater potential for successful legal action |
| Rural population | Limited access to financial institutions and digital services, higher risk of fraudulent activities in rural markets | Greater vulnerability to social ostracism and harassment due to community ties | Lower awareness of legal options and access to legal support |
| Urban population | Potential for significant financial losses through online transactions, increased risk of cybercrime | Exposure to social stigma in densely populated areas, increased risk of targeted harassment | Better access to legal aid and support networks, greater awareness of legal remedies |
Data Analysis of Leak
The recent Aadhaar data leak impacting millions of Indian citizens underscores a critical vulnerability in the nation’s digital infrastructure. Understanding the methods used, the exploited vulnerabilities, and the potential motivations behind this breach is crucial for future preventative measures. This analysis delves into the intricate details of the incident, highlighting potential implications and offering comparative insights into similar data breaches.
Likely Methods of the Leak
Several methods could have facilitated the unauthorized access to Aadhaar data. Sophisticated phishing campaigns, targeting both individuals and organizations with access to the database, are a significant concern. Alternatively, vulnerabilities in the database’s internal systems or access controls could have allowed unauthorized access. Exploiting weak or compromised credentials, or exploiting zero-day vulnerabilities, is also a possibility.
Potential Vulnerabilities Exploited
Identifying the specific vulnerabilities exploited in this incident requires thorough investigation. However, known vulnerabilities in similar systems, such as SQL injection flaws, weak password policies, and insufficient access controls, are potential targets. Furthermore, insider threats, where authorized personnel with malicious intent compromise the system, are also a concern. Poorly configured firewalls and a lack of multi-factor authentication could have left the system susceptible.
Possible Motivations Behind the Leak
The motivations behind the leak are multifaceted and could range from financial gain to political manipulation or even espionage. Criminals could leverage the leaked data for identity theft, fraudulent transactions, or extortion. Similarly, political adversaries or foreign intelligence agencies might seek to exploit the data for intelligence gathering or sabotage. Moreover, the leak could have been a deliberate act by individuals or groups seeking to damage the reputation of the government or its institutions.
The recent IOC Indane leak exposing Aadhaar details of 6.7 million Indian citizens highlights a critical vulnerability in data handling. Protecting sensitive data like this is paramount, and requires a proactive approach. This underscores the need for robust security measures, like the ones discussed in Deploying AI Code Safety Goggles Needed – a crucial step towards preventing similar breaches in the future.
Ultimately, the incident serves as a harsh reminder of the ongoing importance of secure coding practices to prevent sensitive data from falling into the wrong hands.
Comparison of Data Breach Methodologies
| Methodology | Description | Vulnerabilities Exploited | Motivations |
|---|---|---|---|
| Phishing | Tricking individuals into revealing sensitive information, often through deceptive emails or websites. | Social engineering, weak passwords, lack of security awareness. | Financial gain, espionage, political manipulation. |
| SQL Injection | Exploiting vulnerabilities in database queries to gain unauthorized access. | Weaknesses in database security, lack of input validation. | Data theft, financial gain, disruption. |
| Insider Threat | Unauthorized access by individuals with legitimate access to the system. | Poor access controls, insufficient oversight, lack of employee training. | Financial gain, sabotage, political motivations. |
| Zero-Day Exploits | Exploiting previously unknown vulnerabilities in software or hardware. | Lack of timely security updates, inadequate vulnerability assessments. | Data theft, financial gain, espionage. |
The table above provides a basic comparison of data breach methodologies. Each method presents unique challenges and requires specific countermeasures for prevention and mitigation.
Implications for Aadhaar System

The recent Aadhaar data leak underscores critical vulnerabilities within the system, demanding immediate attention to bolster its security posture. This breach, affecting millions of citizens, raises serious concerns about the integrity of personal data and the potential for misuse. Strengthening the Aadhaar framework is not just about preventing future leaks; it’s about safeguarding the fundamental right to privacy for every Indian citizen.The leak highlights a critical gap in the current security protocols surrounding the Aadhaar system.
While the system’s utility in streamlining various government services is undeniable, its security infrastructure needs urgent reinforcement to withstand sophisticated attacks. Addressing this breach isn’t just about technical fixes; it’s about a fundamental shift in approach, incorporating robust security measures and citizen awareness.
Enhanced Security Measures
Strengthening the Aadhaar system requires a multifaceted approach. This includes implementing multi-layered authentication protocols, incorporating biometric verification at multiple stages, and introducing encryption techniques for data storage and transmission. Rigorous security audits and penetration testing should become routine to identify and patch vulnerabilities proactively.
Potential Policy Changes
To prevent future leaks, policy changes are essential. This includes stricter regulations regarding data handling, storage, and access, coupled with clear penalties for violations. Mandating regular security assessments of the system and its associated infrastructure, along with strict adherence to international data privacy standards, is crucial. The policy should also incorporate provisions for independent audits and oversight to ensure transparency and accountability.
Role of Regulatory Bodies
Regulatory bodies play a vital role in overseeing and enforcing data protection standards within the Aadhaar system. The establishment of an independent regulatory body dedicated to Aadhaar data security and privacy would be instrumental in ensuring compliance and swift response to breaches. This body should have the authority to conduct investigations, impose penalties, and issue guidelines to improve the system’s overall security posture.
Reinforcing System Security and Integrity
Reinforcing the system’s security and integrity requires a comprehensive strategy involving several key steps. This includes:
- Improved data encryption and transmission protocols: Implementing end-to-end encryption for all data transfers is critical. This will make data unintelligible to unauthorized parties, even if intercepted.
- Strengthening access controls: Restricting access to sensitive data based on the “need-to-know” principle will minimize the potential for misuse. Implementing robust access controls for all personnel involved in handling Aadhaar data is crucial.
- Regular security audits and penetration testing: Proactive identification of vulnerabilities is essential. Regular security audits and penetration testing will identify potential weak points and ensure the system’s defenses are up-to-date.
- Enhanced awareness campaigns: Educating citizens about data privacy and the importance of safeguarding their Aadhaar information is critical. Clear communication regarding the implications of a data breach and how to protect their information is essential.
These measures will create a more secure and resilient Aadhaar system, ensuring the continued trust of the Indian citizens.
Citizen Responses and Actions
The recent Aadhaar data leak has understandably caused significant concern among Indian citizens. This section Artikels crucial steps individuals can take to mitigate the risks and protect themselves from potential fraud and identity theft. Understanding your rights and responsibilities in the face of such a breach is paramount.Protecting your personal data in the digital age is crucial. This includes being vigilant about the information you share online and offline, and understanding the potential consequences of a data breach.
Immediate Actions for Affected Individuals
A proactive approach to safeguarding your personal information is essential. Reviewing your financial accounts and credit reports frequently, for instance, is vital. Monitoring your accounts for suspicious activity and promptly reporting any irregularities is a necessary precaution.
- Review Your Financial Accounts: Regularly check your bank statements, credit card statements, and loan documents for any unauthorized transactions. Look for discrepancies in account balances or unusual activity. Examples include unexpected charges, suspicious transfers, or new accounts opened in your name. Compare your account statements with recent online transactions and records to catch any anomalies.
- Monitor Your Credit Report: Request and review your credit report from all major credit bureaus. Be alert for any new accounts or inquiries that you don’t recognize. This proactive measure is essential to catch potential fraudulent activities early.
- Change Passwords and Security Questions: Immediately change passwords for all online accounts that use the leaked Aadhaar details. This includes banking, e-commerce, and social media accounts. Consider creating unique and complex passwords to further enhance security. Also, update your security questions and answers to strengthen the security measures of your accounts. This step is vital in preventing unauthorized access.
The recent IOC Indane leak exposing Aadhaar details of 6.7 million Indian citizens is deeply concerning. Security breaches like this highlight the critical need for robust data protection measures. This issue echoes the vulnerabilities in systems like Azure Cosmos DB, which recently faced a critical vulnerability that could have compromised sensitive data. Understanding these weaknesses, like those detailed in Azure Cosmos DB Vulnerability Details , is vital to prevent future data breaches, and ultimately, to protect the personal information of millions.
The IOC Indane leak serves as a stark reminder of the ongoing struggle to safeguard sensitive citizen data.
- Report Suspicious Activity: If you notice any suspicious activity on your accounts, report it immediately to the relevant financial institutions or authorities. This includes reporting to your bank, credit card company, and other financial service providers.
Resources Available to Affected Citizens
Several resources can assist individuals in navigating the aftermath of the data breach. Government agencies, financial institutions, and non-profit organizations can provide valuable support.
- National Helpline: A dedicated helpline established by the government can offer guidance and support to affected citizens. These services often include reporting mechanisms for fraud and identity theft.
- Financial Institutions: Your bank or other financial institutions have dedicated channels for reporting fraudulent activities. They can provide assistance and guidance on securing your accounts.
- Consumer Protection Agencies: National and state consumer protection agencies can offer guidance on consumer rights and procedures for reporting fraud. They can provide information on relevant laws and regulations, helping affected citizens.
- Cybersecurity Organizations: Organizations dedicated to cybersecurity often provide resources and tips for protecting personal data. These resources can offer valuable insights into preventative measures against potential threats.
Reporting Breaches and Seeking Assistance
Understanding the process of reporting a data breach is crucial. Knowing the correct channels and procedures can help in seeking timely assistance.
- Contact Relevant Authorities: Reach out to the appropriate authorities, such as the authorities managing the Aadhaar system, to report the data breach. This step is critical for the authorities to understand the scope of the issue and take necessary actions.
- Seek Legal Advice: Consult with legal professionals for guidance on your rights and options in cases of identity theft or fraud. Legal counsel can provide essential support during such challenging times.
- Follow Instructions from Authorities: Follow any instructions provided by the authorities regarding account security or other necessary steps. Adhering to these guidelines is crucial in mitigating the impact of the data breach.
Data Security Measures
Implementing strong data security practices can help prevent future breaches. These measures are critical to protect personal data and maintain confidentiality.
| Step | Action | Description | Potential Risk Mitigation |
|---|---|---|---|
| Strong Passwords | Use unique and complex passwords | Create passwords that are difficult to guess and use different passwords for different accounts. | Reduces the risk of unauthorized access to accounts. |
| Two-Factor Authentication | Enable 2FA wherever possible | Enable two-factor authentication (2FA) for all online accounts that support it. | Adds an extra layer of security to prevent unauthorized access even if a password is compromised. |
| Regular Software Updates | Keep software updated | Ensure all software, including operating systems and applications, are updated to the latest versions. | Patches vulnerabilities that could be exploited by hackers. |
| Be Cautious of Phishing | Avoid suspicious links and emails | Be wary of suspicious emails or links, and avoid clicking on them. | Reduces the risk of falling victim to phishing scams that may compromise personal data. |
Illustrative Case Studies
The Aadhaar data breach highlights a critical vulnerability in personal data management. Understanding how similar breaches have unfolded globally, and how other nations have responded, provides valuable insights into the potential repercussions and lessons learned. This section will examine global precedents, focusing on the approaches taken to mitigate similar risks and the impact on public trust.Examining comparable data breaches in other countries offers a crucial framework for understanding the potential consequences of this incident and how to improve data protection measures.
Lessons learned from these events can help India formulate effective responses and preventative strategies.
Global Data Breach Examples
Understanding past data breaches provides valuable context for assessing the implications of the Aadhaar leak. Several notable breaches worldwide underscore the vulnerability of personal data systems and the importance of robust security protocols.
- The 2017 Equifax data breach exposed the personal information of over 147 million Americans, illustrating the widespread damage that can result from a major security lapse. This incident highlighted the critical need for robust security measures and transparent communication with affected individuals.
- The 2018 Cambridge Analytica scandal, involving the unauthorized collection and use of Facebook user data, exposed the risks associated with data sharing and the potential for misuse of personal information for political purposes. It underscored the importance of data privacy regulations and ethical data handling practices.
- The 2021 Colonial Pipeline ransomware attack showcased the vulnerabilities of critical infrastructure to cyberattacks. While not strictly a data breach in the same way as Aadhaar, the attack demonstrated the potential for disruption and economic damage stemming from such breaches. The attack highlighted the need for robust cybersecurity defenses across all sectors.
Comparative Analysis of Responses
Analyzing how different countries have responded to similar data breaches offers valuable insights into effective strategies for mitigating the impact and preventing future occurrences.
| Country | Type of Breach | Response Measures | Impact on Public Trust |
|---|---|---|---|
| United States (Equifax) | Credit reporting agency data breach | Class-action lawsuits, regulatory investigations, and improved security measures | Significant decline in public trust in the affected institution; spurred legislative changes. |
| United Kingdom (various breaches) | Varied, including government and private sector breaches | Increased regulatory oversight, improved cybersecurity standards, and public awareness campaigns | Erosion of public trust, but varying levels depending on the specifics of the breach and the response. |
| Canada (various breaches) | Varied, including government and private sector breaches | Focus on enhanced data protection regulations, cybersecurity awareness, and incident response protocols | Mixed public response, with varying levels of impact depending on the specific breach and the effectiveness of the response. |
| India (hypothetical similar breach) | Aadhaar data leak | (Potential response) Investigation, data recovery efforts, security audits, compensation mechanisms, and strengthened privacy laws. | (Potential impact) Significant decline in public trust in the Aadhaar system, potentially impacting government initiatives and citizen participation. |
Prevention Strategies
The Aadhaar data leak underscores the critical need for robust preventative measures against future breaches. A proactive approach is essential to safeguarding sensitive citizen information and maintaining public trust in the Aadhaar system. Implementing effective security protocols and employing cutting-edge technology are paramount to mitigating risks and ensuring the long-term integrity of the system.
Strengthening Cybersecurity Protocols
Robust cybersecurity protocols are fundamental to preventing future data breaches. These protocols encompass a multi-layered approach that includes technical safeguards, administrative controls, and physical security measures. Implementing strong authentication mechanisms, regular security audits, and incident response plans are crucial elements of a comprehensive strategy. Regular vulnerability assessments and penetration testing can identify potential weaknesses in the system before they are exploited.
Role of Technology in Mitigating Future Incidents
Advanced technologies play a critical role in bolstering the security of the Aadhaar system. Multi-factor authentication, encryption techniques, and blockchain technology can significantly enhance the security posture of the system. These technologies can make it far more challenging for unauthorized access to sensitive data. For example, biometric authentication methods, coupled with strong passwords, can significantly deter unauthorized access.
The recent IOC Indane gas leak exposing Aadhaar details of 6.7 million Indian citizens is a serious breach of privacy. This highlights the critical need for robust data security measures in India’s infrastructure. Interestingly, a parallel issue is emerging with the Department of Justice’s recent announcement offering a safe harbor for MA transactions Department of Justice Offers Safe Harbor for MA Transactions.
While seemingly unrelated, both issues underscore the vulnerability of personal information in a digital world and the importance of vigilance in protecting sensitive data.
Regular software updates and patching vulnerabilities are also critical.
Recommendations for Preventing Future Incidents
Implementing a comprehensive set of recommendations is vital to prevent future incidents of this nature. These recommendations span various aspects of the Aadhaar system, from data handling practices to system architecture.
- Improved Data Encryption and Access Control: Implementing end-to-end encryption for all Aadhaar-related data, coupled with granular access controls based on the “need-to-know” principle, can effectively limit unauthorized access. This involves segregating data based on sensitivity and limiting access to only those individuals requiring it.
- Enhanced Authentication Procedures: Implementing robust multi-factor authentication (MFA) systems, combining passwords with biometric verification or one-time passwords, can drastically reduce the risk of unauthorized access. Using strong, unique passwords and employing frequent password changes can also enhance security.
- Regular Security Audits and Penetration Testing: Conducting regular security audits and penetration testing can identify potential vulnerabilities in the system. This proactive approach allows for the prompt resolution of weaknesses before they can be exploited. Results from these tests can be used to strengthen security protocols.
- Proactive Incident Response Plan: Developing and implementing a comprehensive incident response plan, outlining procedures for handling data breaches, is critical. This plan should include steps for containment, notification, and recovery. Training personnel on incident response protocols is also essential.
- Employee Training and Awareness: Educating employees about cybersecurity best practices and the importance of data protection is crucial. This involves raising awareness about phishing scams, social engineering tactics, and other threats. Regular training programs can reinforce security awareness.
Information Visualization
This section delves into visualizing the scale and impact of the Aadhaar leak, highlighting the geographical spread of affected citizens and the types of compromised data. We’ll also explore the typical stages of a data breach using a flowchart, offering a clearer understanding of the vulnerabilities involved.Visual representations are crucial in understanding the gravity and scope of the Aadhaar leak.
By presenting data in a digestible format, we can better grasp the potential consequences for affected individuals and the broader implications for India’s digital identity system.
Scale of the Leak
Visualizing the scale of the leak is essential to grasp its magnitude. A bar graph, for instance, could effectively show the number of Aadhaar numbers compromised, potentially contrasting it with the total number of Aadhaar holders in India. This comparison visually highlights the severity of the data breach, facilitating comprehension of the potential impact. The graph’s horizontal axis could represent the number of compromised accounts, while the vertical axis represents the corresponding percentage.
Geographical Distribution
A choropleth map can effectively illustrate the geographical distribution of affected citizens. This map would shade different states or regions based on the proportion of affected individuals. Areas with a higher concentration of affected citizens would be depicted with darker shades, providing a clear picture of the regional impact.
Types of Compromised Data
A pie chart can visually represent the types of data compromised. The chart’s slices would represent the various data points leaked, such as name, date of birth, address, and other personal identifiers. This visualization provides a clear breakdown of the sensitive information exposed, allowing a better understanding of the breach’s scope.
Data Breach Flowchart
A flowchart can effectively depict the typical steps involved in a data breach. The flowchart could start with the initial vulnerability, like a weak password or a compromised server. Subsequent steps, such as unauthorized access, data exfiltration, and eventual leak, would be depicted with connecting arrows, showcasing the progression of the breach. The visual representation can be further enhanced with icons or symbols to represent each stage, making it more intuitive.
The diagram could highlight potential entry points for attackers and measures that could prevent such incidents.
Final Review: Ioc Indane Leaks Aadhaar Details Of 6 7 Million Indian Citizens
The IOC Indane Aadhaar leak serves as a stark reminder of the importance of data security in the digital era. Millions of Indian citizens are potentially affected, highlighting the urgent need for improved cybersecurity measures and a stronger focus on data protection. The implications extend beyond financial loss and potential fraud, impacting national security and individual privacy. Moving forward, it’s imperative that the government and affected parties work together to address the aftermath and prevent similar breaches in the future.
General Inquiries
What is the potential impact of financial ramifications for affected individuals?
The leak of Aadhaar details could lead to fraudulent transactions, unauthorized access to accounts, and identity theft, resulting in significant financial losses for affected individuals. This could range from small amounts to substantial sums, potentially crippling individuals financially.
What steps should individuals take to protect themselves from potential fraud and identity theft?
Monitor financial accounts regularly, report any suspicious activity promptly, and consider credit monitoring services. Be cautious about sharing personal information online and use strong passwords. Regularly update software and security protocols to minimize vulnerabilities.
How can I report a breach and seek assistance?
Contact the relevant authorities, such as the Indian government’s data protection agency, and file a formal complaint. Consider consulting with legal professionals to understand the available legal remedies and potential recourse.
What are the likely methods used for the leak?
Determining the precise methods is crucial. Potential avenues could range from compromised internal systems to external hacking. Further investigation is required to pinpoint the exact methods and prevent similar attacks in the future.