ISIS Shifts to Cyberattacks After Loss
Isil will shift its focus to cyber attacks after battlefield loss – ISIS will shift its focus to cyber attacks after battlefield loss, signaling a potential new era in terrorist tactics. This shift raises serious concerns about the evolving threat landscape, and how terrorist groups adapt to battlefield setbacks. Understanding the motivations, methods, and potential consequences of this shift is crucial for national and international security.
The recent territorial losses suffered by ISIS have likely prompted this strategic recalibration. Their past battlefield prowess, combined with the increasing sophistication of cyber warfare techniques, suggests a dangerous new chapter in their operations. This adaptation demands a multifaceted response, requiring a comprehensive understanding of their capabilities and motivations.
Background on ISIS/ISIL
The rise and fall of ISIS/ISIL, a self-proclaimed caliphate, has been a defining chapter in modern conflict. Its brutal tactics and territorial ambitions have had a profound impact on the geopolitical landscape of the Middle East and beyond. Understanding its history, motivations, and strategies is crucial to comprehending the ongoing threat and potential for future resurgence.The group’s evolution from a small insurgent group to a formidable force, controlling vast territories and imposing a harsh interpretation of Islamic law, is a complex process rooted in regional instability and grievances.
This evolution reflects the interplay of various factors, from the Iraq War’s aftermath to the Syrian civil war, which provided fertile ground for extremist ideologies to take root.
History of ISIS/ISIL
ISIS, initially known as the Islamic State of Iraq and the Levant (ISIL), emerged from the ashes of al-Qaeda in Iraq. Its early stages were marked by brutal attacks against Iraqi security forces and civilians. The group rapidly gained strength by exploiting sectarian divisions and the power vacuum created by the Iraq War. The Syrian civil war further bolstered its ranks, providing a sanctuary and access to resources.
Key milestones include the declaration of a self-proclaimed caliphate in 2014, which marked the peak of its territorial control.
Territorial Gains and Losses
ISIS’s territorial expansion was dramatic. The group seized control of large swathes of territory in Iraq and Syria, establishing a self-declared caliphate. This included significant cities and infrastructure. However, this expansion was not without its challenges. The group faced significant opposition from various coalitions, including US-led forces and local militias.
The combination of military offensives and internal dissent has steadily chipped away at ISIS’s territory, leading to significant losses and setbacks.
Organizational Structure and Leadership
ISIS operated under a hierarchical structure, with a central leadership that coordinated operations across various provinces. The leadership, often composed of former military officers and ideologues, controlled resources and implemented strategies. The group’s structure has undergone significant shifts due to battlefield losses and leadership changes. The group’s internal conflicts and disputes have also weakened its capacity to operate effectively.
Motivations and Goals
ISIS’s motivations were multifaceted, drawing from a mix of religious extremism, political opportunism, and a desire for territorial control. The group sought to establish a global Islamic caliphate, governed by its interpretation of Islamic law, aiming to impose a strict religious order. The group used the ideology to attract recruits and maintain control.
Financial Resources and Support Networks
ISIS generated revenue through various means, including extortion, oil sales, and looting. The group also benefited from external support networks, both financial and logistical. These networks, often complex and decentralized, provided crucial resources to sustain its operations.
Previous Tactics and Strategies on the Battlefield
ISIS utilized a combination of conventional and unconventional tactics. The group employed guerrilla warfare, ambushes, and suicide bombings, leveraging its understanding of local terrain and exploiting vulnerabilities in enemy defenses. ISIS also employed propaganda to recruit new members and maintain control.
Recent Battlefield Losses
Recent military operations have severely degraded ISIS’s capacity to control territory. The group’s losses have been significant, resulting in the loss of key cities and infrastructure. The loss of key leaders and fighters, coupled with the tightening of international and regional pressure, has diminished the group’s ability to operate effectively.
ISIS’s battlefield setbacks might push them towards cyberattacks. This shift in tactics could potentially exploit vulnerabilities in critical infrastructure, like those detailed in the Azure Cosmos DB Vulnerability Details. This means we need to be extra vigilant in safeguarding our digital systems, especially as ISIS looks for new avenues to exert influence and cause damage.
Motivations for Shifting to Cyberattacks
The territorial losses suffered by ISIS/ISIL on the battlefield have likely prompted a strategic reassessment, pushing the group to explore alternative avenues for maintaining influence and achieving its objectives. This shift towards cyberattacks reflects a calculated adaptation to the changing geopolitical landscape and a recognition of the limitations imposed by conventional warfare. The group’s motivations for this change are multifaceted and complex, stemming from a combination of tactical, strategic, and ideological factors.The perceived advantages of cyberattacks over traditional warfare are significant.
Cyber operations are often less costly and require fewer resources than conventional military actions. They can be conducted remotely, minimizing direct risks to the group’s fighters and enabling operations from various locations. Furthermore, cyberattacks can inflict significant damage without the need for a large-scale physical presence, allowing for a greater degree of operational flexibility and anonymity.
Potential Assessment of Strengths and Weaknesses
ISIS/ISIL likely assesses its current strengths and weaknesses in the context of its diminished battlefield presence. The group may view its diminished conventional military capacity as a vulnerability, motivating a shift to areas where it can exert influence without direct confrontation. However, the group also recognizes the potential for cyberattacks to inflict economic damage, and the recruitment and radicalization of new members through online platforms.
This calculated shift to cyberspace might represent an attempt to adapt to new realities, to maintain their operational capacity, and to continue the struggle through new means.
ISIS’s potential shift to cyberattacks after losing ground on the battlefield is a serious concern. This shift in tactics, however, might be somewhat mitigated by recent developments like the Department of Justice Offers Safe Harbor for MA Transactions Department of Justice Offers Safe Harbor for MA Transactions , which could potentially make some cyber activities harder to pursue.
Ultimately, the threat of ISIS engaging in cyber warfare remains a worry, despite this positive development.
Potential for Recruitment and Radicalization
ISIS/ISIL understands the power of online platforms in recruitment and radicalization. The group may leverage online forums, social media, and encrypted messaging applications to reach new audiences, disseminate propaganda, and attract recruits. The group’s past success in utilizing online platforms to radicalize individuals and inspire attacks provides a template for future efforts. The rise of decentralized online communities could potentially allow ISIS/ISIL to bypass traditional security measures and reach previously untapped pools of potential supporters.
This allows for greater reach and adaptability.
Comparison of Past and Potential Future Cyber Activities
ISIS/ISIL’s past cyber activities have largely focused on propaganda dissemination and online recruitment. However, their potential future cyber activities may encompass a broader range of operations, including cyber espionage, cyberattacks on critical infrastructure, and the disruption of financial systems. The group may attempt to leverage their existing network of supporters and sympathizers to coordinate these activities.
ISIS’s battlefield setbacks are likely to push them towards cyberattacks. This shift necessitates a proactive approach to cybersecurity, like deploying AI Code Safety Goggles Needed here to prevent vulnerabilities in our digital infrastructure. After all, a determined foe will always look for new avenues of attack, and the digital realm is a prime target for groups like ISIS.
Motivations for Economic Damage
ISIS/ISIL may be motivated to use cyberattacks to inflict economic damage on their adversaries. The group may target financial institutions, critical infrastructure, or government agencies. Cyberattacks on such targets could inflict significant economic disruption, and undermine public confidence. The successful targeting of financial institutions during the 2010s, for example, demonstrated the potential for cyberattacks to have far-reaching consequences.
This motivation reflects a shift towards more calculated and targeted approaches.
Methods and Capabilities of Cyberattacks
The shift to cyberattacks by ISIS/ISIL, following battlefield setbacks, necessitates an understanding of their potential methods and capabilities. This analysis examines the types of attacks they might employ, the targets they are likely to select, and the level of sophistication they might achieve. It also explores the vulnerabilities inherent in their cyber operations, highlighting the potential for disrupting their activities.The digital realm offers ISIS/ISIL a new avenue for achieving their objectives, potentially circumventing the limitations of traditional military tactics.
This shift to cyberwarfare poses a significant threat, demanding careful consideration of the potential consequences.
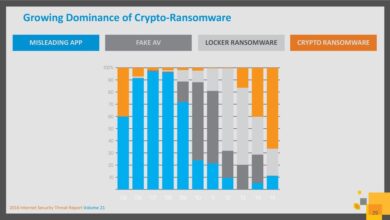
Potential Cyberattack Methods
ISIS/ISIL might employ a range of cyberattack methods to achieve their goals, from simple denial-of-service attacks to more complex infiltration attempts. The nature of these attacks will likely depend on their access to skilled personnel and resources.
- Denial-of-Service (DoS) Attacks: These attacks overwhelm a target system with traffic, effectively shutting it down. DoS attacks are relatively simple to execute and can cause significant disruptions, especially to websites or online services. For example, the distributed denial-of-service (DDoS) attack against Dyn in 2016, which caused widespread internet outages, illustrates the potential impact of this type of attack.
ISIS/ISIL could target critical infrastructure or government websites, aiming to disrupt operations and sow chaos.
- Malware Distribution: ISIS/ISIL could spread malicious software designed to steal data, disrupt operations, or sabotage systems. This could involve phishing campaigns to target individuals or organizations with access to critical infrastructure or financial systems. The use of ransomware, which encrypts data and demands payment for its release, could also be a potential tactic. The NotPetya ransomware attack of 2017 serves as a stark reminder of the potential for widespread disruption.
- Social Engineering and Propaganda: ISIS/ISIL could leverage social media platforms to spread propaganda and misinformation. This includes creating fake news articles, manipulating online discussions, or attempting to recruit new members. Their ability to exploit existing online vulnerabilities and recruit individuals with technical expertise would further amplify this threat.
Potential Targets
The potential targets for ISIS/ISIL’s cyberattacks extend beyond simple online platforms. They could target critical infrastructure, financial systems, and even political processes.
- Critical Infrastructure: Systems controlling utilities, transportation, or communication networks could be targeted. Disruptions to these networks could have severe consequences, leading to widespread damage and disruption. For instance, attacks on water treatment facilities or power grids could cause significant public health and safety issues.
- Financial Systems: ISIS/ISIL might target financial institutions or online payment systems to disrupt economic activity or generate funds. They could attempt to steal funds or manipulate financial markets to destabilize economies.
- Government Websites and Services: Disrupting government services or websites could cause confusion and potentially undermine public trust. This could involve defacing websites, stealing sensitive data, or disrupting essential online services.
Potential for Disruption and Damage
Cyberattacks can cause widespread disruption and damage, ranging from minor inconveniences to catastrophic failures. The potential impact depends on the target, the method of attack, and the level of sophistication involved.
- Disruptions to Essential Services: Attacks on critical infrastructure, such as power grids or water treatment facilities, could lead to significant disruptions in essential services, affecting public health and safety.
- Economic Damage: Attacks on financial systems or online payment platforms could cause significant economic damage, disrupting trade and potentially causing financial instability.
- Erosion of Trust: Disruptions to government websites or services could undermine public trust in institutions and potentially lead to social unrest.
Capabilities and Weaknesses
ISIS/ISIL’s capabilities in cyberattacks are likely to be evolving, but remain limited. While they could potentially recruit skilled individuals or acquire tools and techniques, their lack of a dedicated cyber warfare unit could pose significant vulnerabilities.
- Limited Technical Expertise: ISIS/ISIL may lack the technical expertise to execute sophisticated cyberattacks. Their ability to recruit or acquire skilled individuals would significantly affect their potential effectiveness.
- Dependence on External Resources: Their dependence on external resources and individuals for technical expertise could be a weakness. This dependence could make their operations more vulnerable to disruption or detection.
- Lack of Resources: Compared to state-sponsored actors, ISIS/ISIL likely has limited resources to invest in developing and maintaining sophisticated cyber capabilities.
Impact and Consequences of Cyberattacks

The shift by ISIS/ISIL towards cyberattacks, following battlefield losses, presents a significant threat to global security. This new tactic allows the organization to maintain operational capacity and exert influence without the limitations of physical space and resources. The consequences of these attacks can ripple through numerous sectors, impacting individuals, businesses, and governments in unprecedented ways.The potential ramifications of ISIS/ISIL’s cyber capabilities are far-reaching.
From disrupting critical infrastructure to undermining financial systems, the effects of such attacks can be devastating and long-lasting. Understanding these potential impacts is crucial for formulating effective countermeasures and mitigating the risks associated with this evolving threat landscape.
Potential Impact on Global Security and Stability
Cyberattacks, especially those orchestrated by terrorist organizations, can destabilize international relations and trigger broader conflicts. The targeting of critical infrastructure, like power grids or water systems, can cause widespread panic and disruption, potentially escalating into regional or even international disputes. The potential for misattribution and escalation makes the threat of cyberattacks particularly concerning. The Syrian civil war, for example, has demonstrated how cyberattacks can amplify existing tensions and create new avenues for conflict.
Potential Impact on Individuals, Businesses, and Governments
Individuals, businesses, and governments alike face significant vulnerabilities in the face of sophisticated cyberattacks. Personal data breaches can lead to identity theft and financial losses, while attacks on businesses can cripple operations and cause substantial economic damage. Government services, including essential functions like healthcare and emergency response, can be disrupted, leading to a loss of public trust and impacting citizens’ safety.
The 2017 NotPetya attack, a ransomware attack that affected businesses and government agencies worldwide, exemplifies the devastating potential of such attacks.
Impact on International Relations and Cooperation
The increasing reliance on interconnected digital systems necessitates a strong international framework for cybersecurity cooperation. Differences in national priorities and approaches to cybersecurity can hinder the development of unified responses to global cyber threats. Successful cooperation, however, is vital to prevent and mitigate the impact of attacks orchestrated by groups like ISIS/ISIL. The collaborative efforts to combat international crime are a model that can be adapted for cybersecurity.
Impact on ISIS/ISIL’s Public Image
The success or failure of ISIS/ISIL’s cyberattacks will have a direct impact on their public image and perceived strength. Successful attacks could bolster their image as a sophisticated and formidable adversary, potentially attracting new recruits or supporters. Conversely, unsuccessful or poorly executed attacks could erode their reputation and diminish their influence. The organization’s previous successes in attracting global attention through violence and media manipulation provide a cautionary example.
Potential Targets and Impact Scenarios
| Target | Potential Impact | Mitigation Strategies |
|---|---|---|
| Critical Infrastructure | Disruption of essential services, economic damage, potential loss of life | Enhanced security measures, redundancy planning, robust emergency response protocols |
| Financial Systems | Fraud, theft, economic instability, disruption of international trade | Strengthened security protocols, increased vigilance, international cooperation on financial transactions |
| Government Services | Disruption of operations, loss of public trust, potential for societal unrest | Robust cybersecurity defenses, contingency plans, transparent communication with the public |
Potential Responses from Affected Nations, Isil will shift its focus to cyber attacks after battlefield loss
Affected nations will likely respond to cyberattacks with a combination of defensive and offensive measures. This includes enhancing cybersecurity infrastructure, bolstering intelligence gathering capabilities, and potentially developing offensive cyber capabilities for deterrence and retaliation. The response will also likely involve international cooperation and information sharing to enhance collective security. The Stuxnet incident, a suspected US-Israeli operation against Iranian nuclear facilities, highlights the potential for offensive cyber capabilities in responding to threats.
Comparison with Other Terrorist Groups: Isil Will Shift Its Focus To Cyber Attacks After Battlefield Loss
Assessing ISIS/ISIL’s potential shift to cyberattacks requires a comparative analysis with other terrorist groups. Understanding similarities and differences in their strategies and capabilities provides crucial insights into potential future actions. This comparison reveals patterns of behavior and technological adoption within the broader terrorist landscape. The motivations, methods, and targets of these groups offer a framework for predicting ISIS/ISIL’s likely cyber activities.Examining the cyber activities of other terrorist groups reveals potential similarities and differences with ISIS/ISIL.
This analysis helps anticipate future actions by the group, based on observed patterns in the broader terrorist landscape. This comparison is critical for developing effective countermeasures.
Cyber Expertise
The cyber capabilities of terrorist groups vary significantly. Some groups demonstrate a nascent understanding of digital tools, while others exhibit more advanced techniques. This disparity highlights the varying levels of technological sophistication among different groups.
- Al-Qaeda, for instance, initially had limited cyber capabilities, primarily focusing on propaganda dissemination. However, over time, their activities have expanded to include online recruitment and fundraising, demonstrating an evolving understanding of digital platforms.
- Other groups, like the Taliban, have shown a more recent, albeit still limited, interest in cyber activities, primarily utilizing social media for propaganda and recruitment.
Target Selection
Terrorist groups frequently target infrastructure, government agencies, and financial institutions, reflecting their objectives to disrupt critical services and generate fear. Their choices of targets reflect a desire to maximize impact and demonstrate power.
- The selection of targets by ISIS/ISIL in the past has primarily focused on physical infrastructure and civilian populations. The transition to cyberattacks suggests a potential shift towards targeting critical digital infrastructure.
- A comparison with other groups reveals that cyberattacks may target financial institutions, government websites, and media outlets to disrupt communication and create chaos.
Operational Structure
The internal organizational structures of terrorist groups vary. Some operate as centralized entities, while others have more decentralized structures. This organizational complexity impacts their cyber capabilities.
- ISIS/ISIL’s hierarchical structure could facilitate the development and execution of sophisticated cyber operations if specialized cells or individuals are assigned to these tasks.
- Other groups may rely on more decentralized structures, potentially leading to less coordinated and effective cyberattacks.
Comparative Analysis Table
| Feature | ISIS/ISIL | Other Groups |
|---|---|---|
| Cyber Expertise | Developing, likely acquiring external expertise | Varied; from limited to developing capabilities. |
| Target Selection | Potentially critical digital infrastructure; financial, governmental, media | Infrastructure, financial institutions, government agencies. |
| Operational Structure | Hierarchical, potentially adaptable to cyber cells | Varied, centralized or decentralized. |
Potential Countermeasures and Strategies

Countering ISIS/ISIL’s evolving cyber capabilities requires a multifaceted approach that goes beyond reactive measures. A proactive strategy must be implemented, encompassing international cooperation, robust cybersecurity infrastructure, and a commitment to continuous improvement. This approach will not only protect critical infrastructure but also deter future attacks.Effective countermeasures are crucial to mitigate the potential damage and disruption caused by terrorist groups utilizing cyberattacks.
This involves developing and deploying strategies that can disrupt, detect, and ultimately neutralize these attacks. Understanding the motivations and tactics of ISIS/ISIL is essential to designing effective countermeasures.
National Strategy for Defending Against Cyberattacks
A comprehensive national strategy requires a coordinated effort between various governmental agencies, private sector entities, and international partners. Such a strategy should be regularly reviewed and updated to address emerging threats and adapt to changing tactics.
- Intelligence Gathering and Sharing: Enhanced intelligence gathering, including open-source intelligence (OSINT) analysis, is critical to identifying potential threats and vulnerabilities. International cooperation and intelligence sharing platforms are vital to understanding ISIS/ISIL’s cyber operations and anticipate their future actions. The exchange of threat intelligence, best practices, and technical expertise between nations will be key to strengthening collective defense.
- Cybersecurity Awareness and Training: Widespread cybersecurity awareness and training programs are essential to educate individuals and organizations on identifying and responding to potential cyber threats. This training should cover recognizing phishing attempts, social engineering tactics, and other methods employed by terrorist groups. The training should also include practical exercises to enhance skills in responding to cyberattacks. Organizations, including government agencies and critical infrastructure providers, should prioritize continuous training for employees to remain vigilant against evolving threats.
- Strengthening Cybersecurity Infrastructure: A robust cybersecurity infrastructure is a cornerstone of any effective defense strategy. This involves upgrading existing systems, implementing advanced security protocols, and investing in cutting-edge technologies. Protecting sensitive data, critical infrastructure, and communication channels is crucial to deterring attacks and minimizing potential damage. Regular security assessments and vulnerability scanning are essential to proactively identify weaknesses.
- Technological Advancements in Thwarting Cyberattacks: Leveraging advancements in artificial intelligence (AI), machine learning (ML), and big data analytics can significantly enhance the ability to detect and respond to cyberattacks. AI-powered tools can analyze massive datasets to identify patterns and anomalies indicative of malicious activity, enabling faster response times. Advanced threat detection systems can provide early warning of potential threats and support proactive measures to mitigate potential damage.
- Proactive Measures and Continuous Monitoring: Proactive measures, such as penetration testing and red teaming exercises, are vital to identifying and addressing vulnerabilities before they are exploited. Continuous monitoring of online activity for suspicious patterns can help detect and respond to emerging threats. This proactive approach is crucial to anticipating and preventing future attacks, reducing the potential for widespread damage and disruption.
International Cooperation and Intelligence Sharing
Effective countermeasures rely heavily on international cooperation. Sharing information, best practices, and resources is crucial to understanding and addressing the evolving cyber threats posed by ISIS/ISIL. This collaborative approach strengthens the collective defense against terrorism.
- Joint Task Forces: Establishing joint task forces between nations to share intelligence, resources, and expertise is a valuable method. Such collaborative efforts can enable rapid responses to cyberattacks and improve coordination in countering terrorist groups’ cyber activities.
- Information Sharing Platforms: Developing and utilizing dedicated platforms for information sharing among intelligence agencies and cybersecurity experts is crucial. This allows for the rapid dissemination of crucial information about emerging threats and enables timely responses.
- Cybersecurity Agreements: Strengthening international cybersecurity agreements and protocols can create a unified front against cyberterrorism. These agreements can establish clear guidelines for cooperation and information sharing, facilitating the coordination of efforts against ISIS/ISIL’s cyber activities.
Outcome Summary
In conclusion, ISIS’s potential shift to cyberattacks presents a complex and multifaceted threat. Their motivations, methods, and potential targets necessitate a comprehensive understanding and proactive response. International cooperation, technological advancements, and robust cybersecurity measures are vital to mitigate the risks posed by this evolving threat. The future of global security may hinge on our ability to effectively counter this shift in tactics.
Frequently Asked Questions
What are some specific examples of cyberattacks ISIS might employ?
ISIS could launch denial-of-service attacks to disrupt critical infrastructure, spread disinformation campaigns to sow chaos, or engage in financial fraud to generate revenue. They might also target government websites to disrupt operations and erode public trust.
How does this shift compare to other terrorist groups’ cyber activities?
While other groups have dabbled in cyberattacks, ISIS’s recent battlefield losses and stated motivations suggest a more serious and potentially sustained cyber campaign. Analyzing their capabilities and comparing them to those of other groups can offer insights into potential future actions.
What are some potential responses from affected nations?
Affected nations might strengthen their cybersecurity infrastructure, enhance intelligence sharing, and invest in advanced cybersecurity measures. International cooperation and coordination will be crucial in combating this emerging threat.
What is the role of technological advancements in thwarting future cyberattacks?
Advancements in artificial intelligence and machine learning can play a significant role in detecting and preventing attacks. Continuous monitoring, analysis, and development of defensive measures are essential.