LockBit Lies Never Pay the Ransom
LockBit lies prove another reason to never pay the ransom. This post dives deep into the deceptive tactics of the LockBit ransomware group, highlighting why paying the ransom is often a disastrous decision. We’ll explore the group’s misleading claims, the potential consequences of succumbing to their demands, and ultimately, why choosing not to pay is the safer and more effective approach.
LockBit ransomware operates by encrypting victim’s data and demanding payment in exchange for decryption keys. Their modus operandi often involves sophisticated intrusion techniques, targeting various data types and demanding substantial ransoms. This post examines the specifics of their methods, highlighting the inconsistencies between their promises and their actual performance.
Understanding LockBit Ransomware Tactics
LockBit ransomware, a notorious threat actor, has consistently demonstrated sophisticated tactics and a relentless pursuit of financial gain. Understanding their methods is crucial for organizations to proactively mitigate the risk of an attack. This analysis delves into the intricacies of LockBit’s operations, revealing their modus operandi and the stages involved in a typical attack.LockBit employs a combination of technical prowess and calculated strategies to maximize its impact.
Their targeting strategies are often tailored to specific industries or vulnerabilities, and their operations are frequently refined based on observed patterns and successful attacks. The focus here is on deciphering their tactics, enabling informed security strategies.
LockBit’s Modus Operandi
LockBit’s modus operandi involves a multi-staged approach, starting with infiltration and culminating in a ransom demand. They utilize a variety of techniques to gain initial access, often exploiting vulnerabilities in software or through social engineering.
Data Encryption Methods
LockBit employs robust encryption algorithms to render victim data inaccessible. Commonly used encryption methods include AES-256, ensuring high levels of data security for the perpetrators. The encrypted data is then held hostage, demanding a ransom for its release.
Distribution Strategies
LockBit leverages various methods to distribute its malware, targeting vulnerable systems. These include phishing campaigns, exploiting software vulnerabilities, and leveraging compromised systems to spread laterally. The choice of distribution strategy is often adjusted based on the target’s vulnerabilities.
Stages of a LockBit Attack
A typical LockBit attack proceeds through distinct phases. Initial intrusion is followed by lateral movement across the network. Once within the network, the malware encrypts sensitive data. Subsequently, a ransom demand is issued.
Data Targeted by LockBit
LockBit targets a wide range of data types, prioritizing sensitive information like customer data, financial records, and intellectual property. This data is often highly valuable to the victim organization, making it a prime target for extortion.
LockBit’s Ransom Demands
LockBit demands varying ransom amounts, depending on the size and value of the victim organization. Payment methods are often cryptocurrencies like Bitcoin, designed to maintain anonymity and facilitate illicit transactions. The precise amount is not always publicly disclosed, but there are reported instances of high ransom demands.
Comparison of LockBit Tactics with Other Ransomware Groups
| Characteristic | LockBit | Other Ransomware Groups (e.g., REvil, Conti) |
|---|---|---|
| Data Encryption | AES-256 | Various, often including RSA |
| Distribution Methods | Phishing, exploits, lateral movement | Phishing, exploits, spam |
| Ransom Demands | Cryptocurrencies | Cryptocurrencies, potentially other payment methods |
| Targeting | Specific industries, vulnerabilities | Broader targeting |
The Reasons Behind Non-Payment

Deciding whether to pay a ransomware demand is a critical juncture for victims. The choice is often fraught with difficult trade-offs, and the decision to refuse payment is not taken lightly. This section delves into the motivations behind victims’ refusal to pay, exploring the potential consequences of payment, and outlining the support systems available.Refusal to pay a ransom is often driven by a multitude of factors.
The financial burden of the demand can be crippling, especially for small businesses and organizations with limited resources. The fear of future attacks is another significant deterrent. Furthermore, victims may be concerned about the legal and ethical implications of paying, potentially opening themselves up to further scrutiny and legal challenges.
LockBit’s lies are just another nail in the coffin for paying ransoms. The Department of Justice’s recent initiative, Department of Justice Offers Safe Harbor for MA Transactions , further underscores the risks. Knowing that law enforcement is actively working to protect victims and that paying these criminals won’t get you your data back only strengthens the case for never giving in to these cyber extortionists.
Critical Factors Influencing Non-Payment Decisions, Lockbit lies prove another reason to never pay the ransom
Several critical factors influence the decision to not pay ransomware demands. These include the potential for irreparable data loss if the decryption key is flawed or unavailable, as well as the high risk of re-infection or further extortion attempts. The significant financial and reputational costs associated with paying can also be overwhelming. Finally, many victims recognize that paying does not guarantee data recovery or protect them from future attacks.
Potential Consequences of Paying LockBit
Paying the LockBit ransom often leads to negative repercussions. A critical consequence is the encouragement of future attacks. LockBit, and other ransomware groups, may view payment as a validation of their methods and a signal that victims are willing to pay. This can lead to more frequent and sophisticated attacks in the future.Furthermore, paying the ransom does not guarantee the return of data.
There is no guarantee that the decryption key provided is functional or even legitimate. The risk of data breaches and further financial losses remains significant. The compromised systems may have vulnerabilities exploited by other cybercriminals, leading to further data breaches. This risk is especially pronounced when victims rely on the same systems for other sensitive data.
There is also the risk of facing further extortion attempts by the same or other criminal groups.
Legal and Ethical Considerations
Paying a ransom has significant legal and ethical implications. From a legal standpoint, there is concern about the funds being used for illegal activities. This can lead to legal trouble for the victim. From an ethical perspective, paying a ransom can be seen as condoning criminal activity and supporting future attacks. The financial cost may be deemed disproportionate compared to the potential benefit of data recovery.
LockBit’s lies are just another reason to never pay the ransom. Recent revelations about the group’s tactics highlight the unreliability of these cybercriminals. For example, the details about the Microsoft Azure Cosmos DB vulnerability, as highlighted in Azure Cosmos DB Vulnerability Details , further demonstrate the dangers of trusting their promises. Ultimately, paying these criminals only fuels their malicious activities and doesn’t guarantee data recovery, so the lesson remains clear: never pay the ransom.
Effectiveness of Non-Payment Strategies
Non-payment strategies, when supported by robust cybersecurity measures, can be more effective in deterring future attacks than paying. Organizations that prioritize security measures and data backups are less likely to become victims of ransomware attacks in the first place. When victims choose not to pay, it sends a message that criminal activity will not be tolerated or rewarded.
LockBit’s lies are just another nail in the coffin for ransomware payments. It’s clear these criminals can’t be trusted. To better protect yourself, implementing robust security measures, like deploying AI Code Safety Goggles Needed here , is crucial. Ultimately, ignoring the deceptive tactics of LockBit and prioritizing proactive security is the best course of action.
Support Systems and Resources for Victims
There are support systems and resources available to victims who choose not to pay. Cybersecurity firms and law enforcement agencies can provide guidance and support during negotiations. Data recovery services and specialists can assist with data restoration from backups. The sharing of information and best practices among victims can help strengthen the collective resilience against future attacks.
Potential Risks and Rewards of Paying or Not Paying LockBit Ransom
| Option | Potential Risks | Potential Rewards |
|---|---|---|
| Pay LockBit Ransom | Encourages future attacks, no guarantee of data recovery, potential for further extortion, legal and ethical implications, exposure to other cyber threats | Potential for data recovery, avoiding further disruption to operations |
| Do Not Pay LockBit Ransom | Potential for data loss, disruption of operations, reputational damage, financial losses | Sets a precedent against future attacks, protects against further extortion, maintains ethical and legal compliance, potentially lessens future attacks |
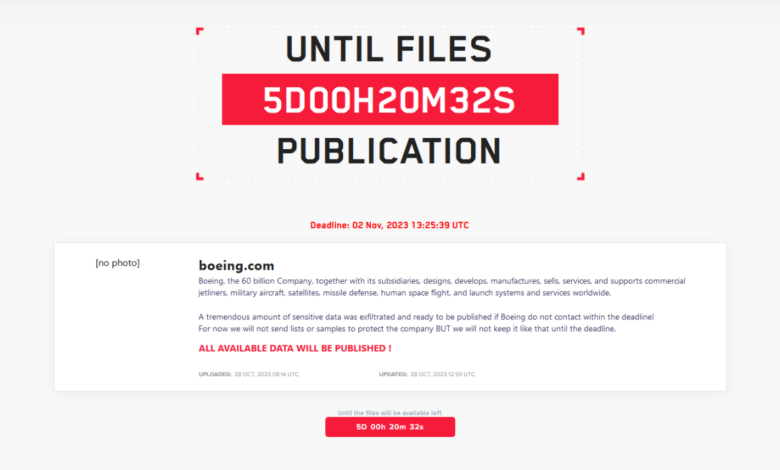
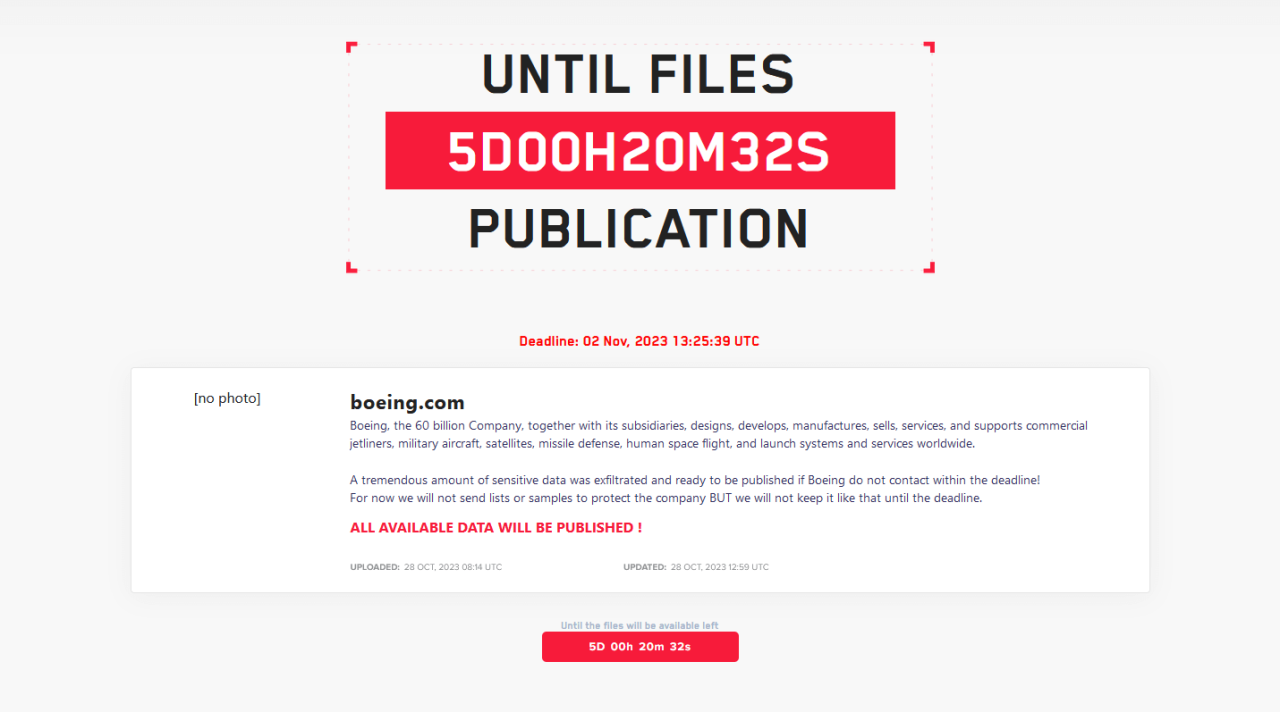
The Reliability of LockBit’s Claims
LockBit ransomware, notorious for its aggressive tactics, often promises data recovery after payment. However, this promise is frequently broken, leaving victims with lost data and significant financial losses. This section delves into the unreliability of LockBit’s claims, examining their track record of failed data restorations and the reasons behind these failures.LockBit’s promises of data recovery after ransom payment are often nothing more than empty assurances.
Victims frequently report that their data remains encrypted, or that the decryption keys provided are faulty or incomplete. This lack of reliability stems from a multitude of factors, including the complex nature of the encryption techniques employed, the often-compromised integrity of the decryption keys, and the inherent unpredictability of the criminal actors behind LockBit.
LockBit’s Failure to Deliver on Promises
The trustworthiness of LockBit’s claims regarding data recovery is significantly undermined by the substantial number of documented cases where victims did not receive their data back after payment. These cases, often reported on cybersecurity forums and in news articles, paint a consistent picture of a ransomware operation that prioritizes profit over integrity.
- Numerous reports detail instances where victims paid the ransom but were unable to decrypt their data. The lack of a reliable process for data recovery often leaves victims with encrypted files and no recourse.
- Some victims reported receiving incomplete or corrupted decryption keys, further exacerbating the problem and leaving them with irretrievable data.
- The complexity of LockBit’s encryption methods often makes the decryption process unreliable. Even with a supposedly valid key, the decryption process may fail, leaving the victim with no data and the ransom money lost.
Reasons Behind LockBit’s Non-Fulfillment
Several factors contribute to LockBit’s frequent failure to deliver on its data recovery promises. The inherent nature of ransomware operations, the technical complexities involved, and the lack of ethical considerations are all crucial elements.
- Technical Complexity: The encryption methods employed by LockBit are frequently sophisticated, and the decryption process can be challenging, even for skilled professionals. Errors in the decryption process, either intentional or accidental, can lead to data loss even if the victim has a seemingly valid key.
- Criminal Intent: The actors behind LockBit are primarily motivated by financial gain. They have little incentive to ensure the successful recovery of data. Their primary goal is to extort money, and fulfilling their promises is often a secondary concern.
- Lack of Trustworthiness: The nature of LockBit’s operation is inherently untrustworthy. The lack of a secure or verified channel for decryption further compounds the issue, making the entire process highly risky for victims.
Typical Patterns in LockBit’s Data Recovery Process
LockBit typically follows a predictable pattern when it comes to data recovery. Victims often experience a series of delays and excuses, and the process is seldom straightforward.
- Initial Promise: LockBit often promises the recovery of data in exchange for the ransom. However, this promise is rarely met with the expected efficiency.
- Delayed Response: Victims often experience significant delays in receiving decryption tools or assistance. This tactic can be used to increase pressure on the victim and to make them more likely to pay.
- Technical Issues: Technical problems with the decryption process or the keys themselves are frequently cited as reasons for the failure to recover data.
Promises vs. Reality: Data Recovery After Payment
This table illustrates the stark difference between LockBit’s promises and the reality of data recovery.
| LockBit’s Promise | Reality |
|---|---|
| Data will be recovered after payment. | Data is often not recovered, or decryption keys are faulty. |
| Decryption keys are reliable and complete. | Decryption keys are often incomplete, corrupted, or unusable. |
| Data recovery process is straightforward. | Data recovery is often delayed, complicated, and unreliable. |
Examples of LockBit Victims’ Experiences
LockBit ransomware attacks have left a trail of devastation, crippling businesses and individuals alike. The tactics employed by the group, coupled with the often-misleading promises surrounding payment, create a complex and stressful situation for victims. Understanding the diverse experiences of those affected is crucial in recognizing the futility of paying the ransom and the resilience of those who choose not to.The experiences detailed below represent just a small fraction of the countless victims impacted by LockBit.
Each case, though unique, underscores the significant negative consequences of succumbing to the extortion tactics and the surprising positive outcomes that can arise from resisting.
LockBit Victim Experiences: Payment
The allure of quickly recovering data often leads victims to consider paying the ransom. However, this decision frequently comes with significant negative repercussions. One victim, a small manufacturing company, paid the ransom demanded by LockBit. The attackers delivered a decryption key, but the files remained corrupted, and critical business data was unrecoverable. The company faced not only the financial burden of the ransom but also the substantial costs associated with restoring their systems and processes, a prolonged and complex recovery.
This experience highlights the unreliable nature of LockBit’s claims and the often-unfulfilled promises of data recovery.
LockBit Victim Experiences: Non-Payment
Choosing not to pay the ransom can be daunting, but it often leads to surprisingly positive outcomes. A graphic design firm, faced with a LockBit attack, chose to prioritize their long-term stability and security over immediate data recovery. They immediately contacted cybersecurity professionals and worked diligently to restore their systems from backups. This approach allowed the company to avoid the financial and operational damage associated with paying the ransom.
The firm’s decision not only saved significant financial resources but also reinforced their commitment to robust data protection strategies.
Key Lessons Learned
The experiences of these victims underscore the importance of not paying the ransom. The high failure rate of decryption keys and the significant cost of recovery often outweigh the perceived benefits. Furthermore, paying the ransom directly funds the criminal enterprise, encouraging further malicious activities. Instead of succumbing to extortion, victims should prioritize data backup, robust security measures, and expert cybersecurity assistance.
Comparison Table: Paid vs. Unpaid
| Characteristic | Paid Ransom | Did Not Pay Ransom |
|---|---|---|
| Decryption Key Success | Frequently unsuccessful or incomplete | Possible recovery through alternative means |
| Financial Impact | Ransom cost + recovery expenses | Recovery costs significantly reduced |
| Operational Impact | Prolonged business disruption | Faster recovery and return to operations |
| Security Implications | Reinforces criminal activity | Reinforces security protocols |
Emotional Toll
The psychological impact of a LockBit attack is often overlooked. Victims face significant anxiety, stress, and frustration as they grapple with the loss of data, the disruption of business operations, and the fear of further attacks. The pressure to pay the ransom adds another layer of emotional distress. The stories of victims illustrate the significant emotional toll that these attacks can inflict, underscoring the importance of empathy and support during these challenging times.
Long-Term Implications of LockBit Lies
LockBit’s pattern of deception, consistently promising data recovery while often failing to deliver, casts a long shadow on the cybersecurity landscape. The group’s actions have profound and multifaceted consequences, impacting not only individual victims but also the entire ecosystem of ransomware and data recovery services. This section delves into the lasting effects of LockBit’s fraudulent tactics.
Broader Implications on the Cybersecurity Landscape
LockBit’s lies erode trust in the entire ransomware market. The group’s actions create a climate of uncertainty for victims, who are left questioning the legitimacy of any data recovery promises. This lack of trust can dissuade organizations from investing in robust security measures, as they may perceive the risks as insurmountable and the cost of recovery as equally high.
The long-term consequence is a potential weakening of overall cybersecurity defenses.
Impact on Victims’ Trust in Data Recovery Services
LockBit’s actions have significantly damaged the reputation of data recovery services. Victims who have paid the ransom and received incomplete or corrupted data have lost faith in the ability of these services to retrieve their information. This diminished trust translates to a potential decrease in the demand for data recovery services, impacting their profitability and the market’s overall viability.
Furthermore, legitimate data recovery companies are unfairly associated with LockBit’s fraudulent operations.
Financial Losses and Reputational Damage
The financial losses associated with LockBit attacks are substantial, encompassing not just the ransom payments but also the cost of downtime, lost productivity, and the expense of restoring systems. Moreover, the reputational damage inflicted on victims can be devastating. Public disclosure of a ransomware attack can lead to a loss of customer confidence, impacting the organization’s brand and market share.
For example, a hospital facing a LockBit attack might lose patients due to public perception of compromised security.
Impact on the Ransomware Ecosystem
LockBit’s tactics have implications for the wider ransomware ecosystem. Their deceptive practices potentially incentivize other ransomware groups to adopt similar strategies. This encourages a culture of mistrust and makes it difficult for victims to discern legitimate recovery options from fraudulent ones. The constant need to verify the trustworthiness of these groups can place a burden on both victims and law enforcement.
Lessons Learned from LockBit’s Deceptive Practices
LockBit’s actions highlight the crucial importance of independent verification of any data recovery claims. Organizations should prioritize comprehensive security measures and robust incident response plans to minimize the impact of ransomware attacks. It’s essential to understand that paying the ransom is not a guarantee of data recovery, and often leads to further complications. The need for proactive security strategies and alternative recovery solutions is emphasized.
Long-Term Consequences: Victims vs. Ransomware Group
| Aspect | Victims | LockBit Group |
|---|---|---|
| Financial Impact | Significant financial losses (ransom, downtime, recovery costs) and potential loss of customers/reputation. | Short-term financial gains, but long-term reputational damage and potential for law enforcement intervention. |
| Operational Impact | Significant operational disruption and loss of productivity. | Potentially increased operational challenges due to legal ramifications and heightened security measures. |
| Reputational Impact | Severe damage to brand and reputation. | Damage to reputation, decreased legitimacy and credibility. |
| Trust in Data Recovery | Erosion of trust in data recovery services and potential decreased demand. | Decreased credibility and decreased willingness to engage in legitimate recovery practices. |
| Security Practices | Potential for increased investment in security measures and enhanced risk awareness. | Potential for increased countermeasures and law enforcement scrutiny. |
Wrap-Up
In conclusion, the LockBit ransomware group consistently fails to deliver on their promises of data recovery after payment. Choosing not to pay is a crucial step in protecting your data and assets. This post has Artikeld the group’s tactics, the reasons behind non-payment, and the long-term implications of their deceptive practices. Remember, never pay the ransom, and always prioritize robust cybersecurity measures to prevent such attacks.
Essential FAQs: Lockbit Lies Prove Another Reason To Never Pay The Ransom
What are the typical data types targeted by LockBit?
LockBit often targets sensitive data like financial records, customer information, intellectual property, and operational databases. They are known for targeting a wide range of organizations, from small businesses to large corporations.
What are the legal and ethical considerations surrounding ransom payments?
Paying a ransom may be illegal in certain jurisdictions, and ethically questionable. It can be considered a form of financial support for criminal activities, and potentially lead to further attacks in the future.
What support systems are available for victims who choose not to pay?
Many cybersecurity firms and organizations offer support and resources to victims of ransomware attacks, regardless of whether they paid the ransom. These resources often include forensic analysis, incident response services, and recovery strategies.