LA County Data Breach Impacts 200,000
Los angeles county suffers data breach impacting 200000 individuals – Los Angeles County suffers data breach impacting 200,000 individuals. This significant security incident raises serious concerns about the protection of personal information in the digital age. The potential ramifications for affected individuals and the county government are substantial, encompassing financial, reputational, and legal repercussions. Understanding the nature of the breach, the steps taken to address it, and preventive measures to avoid future incidents is crucial for both affected residents and the broader community.
The breach likely involved sensitive data, potentially including financial information, personal identifiers, and possibly even medical records. This highlights the importance of robust cybersecurity measures for public institutions and the need for transparent communication with affected citizens. The impact of this data breach extends beyond individual harm to the very fabric of public trust and confidence in the county’s ability to protect its citizens’ information.
Impact Assessment

A data breach affecting 200,000 individuals in Los Angeles County carries significant ramifications, impacting not only the county’s reputation but also the financial and personal well-being of the affected citizens. The swift and effective response to contain the breach is crucial, but the long-term effects require careful consideration and proactive measures. Addressing the fallout requires a multi-faceted approach that includes impact assessment, victim support, and preventative measures.The scale of the breach necessitates a comprehensive understanding of the potential damage to both the county and its residents.
Understanding the nature of the compromised data and the potential for misuse is essential to developing appropriate mitigation strategies. A thorough impact assessment allows for targeted responses, safeguarding the affected individuals and upholding the county’s integrity.
Potential Ramifications for Individuals, Los angeles county suffers data breach impacting 200000 individuals
The potential consequences of a data breach for individuals are substantial and varied. Compromised personal information can lead to identity theft, fraudulent activity, and unwarranted financial losses. Moreover, sensitive data like medical records can expose individuals to discrimination, denial of services, and privacy violations.
Financial Repercussions
Financial losses are a significant concern in data breaches. Unauthorized access to financial accounts can result in significant monetary losses for individuals. This can include fraudulent charges, unauthorized withdrawals, and the need for extensive credit monitoring and identity restoration services. Examples of real-world scenarios include cases where victims have faced thousands of dollars in fraudulent charges after their account details were compromised.
Reputational Damage
The public perception of Los Angeles County government could be significantly tarnished by a data breach. A loss of public trust can lead to reduced public confidence in the county’s ability to protect sensitive information. This reputational damage can negatively impact the county’s ability to attract investments and maintain its positive image.
Legal Repercussions
Data breaches often trigger legal ramifications, both for the affected individuals and the county government. Individuals may file lawsuits against the county, demanding compensation for damages incurred due to the breach. Furthermore, the county could face regulatory penalties and fines for non-compliance with data protection regulations. These legal repercussions can be substantial and require careful management to minimize potential liability.
Data Classification Framework
To effectively assess the severity of the breach, a framework for classifying the compromised data is essential. This framework can be structured as follows:
| Data Type | Description | Severity Level |
|---|---|---|
| Financial Data | Bank account details, credit card information, and transaction records. | High |
| Personal Data | Names, addresses, phone numbers, and social security numbers. | Medium |
| Medical Data | Health records, diagnoses, and treatment plans. | High |
| Government IDs | Driver’s licenses, state IDs, and other government issued documents. | High |
Victim Support Services and Resources
Providing support to victims of a data breach is critical. The county should offer comprehensive resources to help individuals navigate the aftermath of the breach. These resources could include:
- Identity theft protection services: These services can help individuals monitor their credit reports, detect fraudulent activity, and restore their identities. Companies like Experian and Equifax offer such services.
- Credit monitoring services: These services alert individuals to any changes in their credit reports and help them take action against fraudulent activity.
- Legal assistance: Legal resources can help victims understand their rights and options, and guide them through the legal process.
- Financial counseling: Financial counselors can assist individuals in managing their finances and recovering from financial losses.
- Mental health support: The emotional toll of a data breach can be significant, and mental health services can provide support and resources for victims.
Data Breach Characteristics
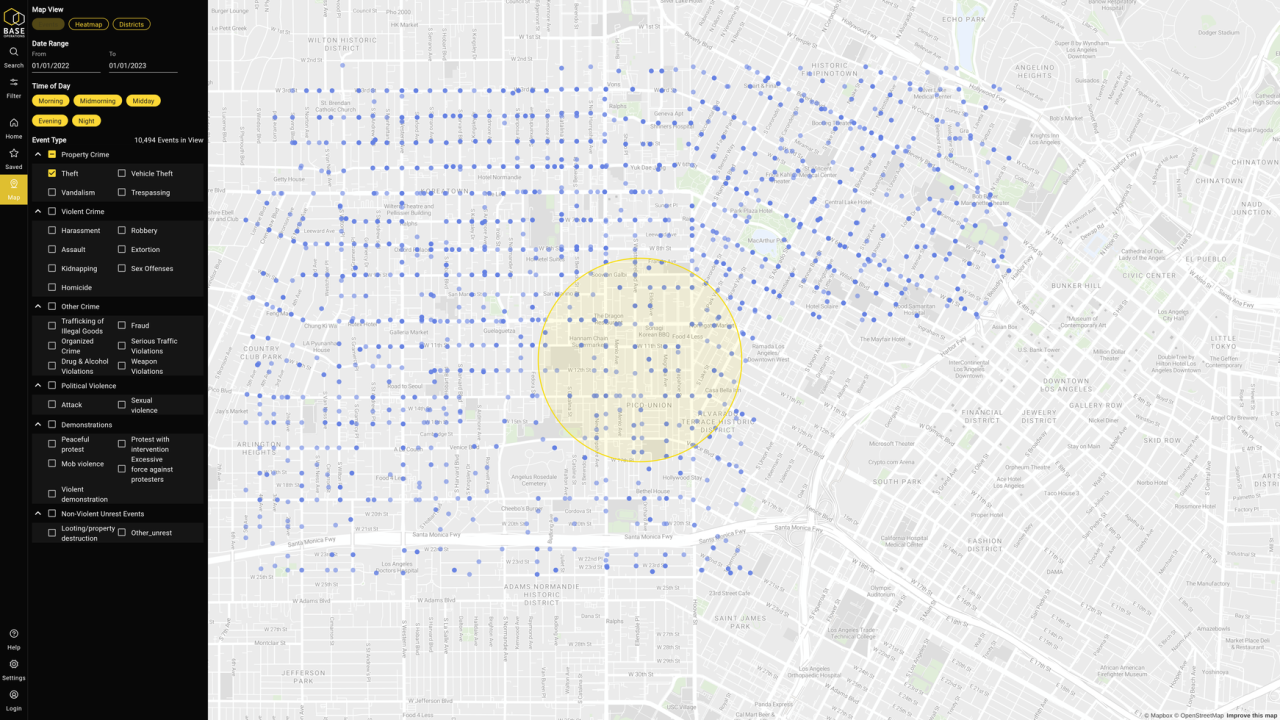
A recent data breach impacting 200,000 individuals in Los Angeles County highlights the pervasive threat of cyberattacks on public institutions. Understanding the characteristics of such breaches is crucial for both prevention and response. This analysis delves into potential causes, different types of breaches, potential warning signs, and the types of data compromised, along with their consequences.The vulnerability of large datasets, especially those held by government agencies, is a significant concern.
Robust security measures are essential to mitigate risks and protect sensitive information from unauthorized access.
Potential Causes of the Breach
Several factors can contribute to data breaches, ranging from simple human error to sophisticated attacks. System vulnerabilities, inadequate security protocols, and insufficient employee training are all potential culprits. A lack of robust multi-factor authentication, outdated software, and inadequate network security are often identified as contributing factors.
Types of Data Breaches
Data breaches manifest in various forms, each with its own characteristics and risks. Phishing attacks, where malicious actors attempt to trick individuals into revealing sensitive information, are prevalent. Malware infections, which can compromise systems and steal data, are another common method. Insider threats, where malicious or negligent employees gain access to sensitive information, can also be a significant source of breaches.
Comparison of Data Breach Types
Different types of breaches vary in their complexity and impact. Phishing attacks, while often seemingly simple, can be highly effective if targeted properly. Malware attacks can lead to widespread data theft and system disruption, as seen in numerous cases across industries. Insider threats can be particularly damaging, as the perpetrator often has authorized access, making detection challenging.
Indicators of a Potential Breach
Certain indicators might precede a data breach. Unusual activity on network systems, such as unusual login attempts or data transfers, can be warning signs. A sudden spike in support tickets related to system issues or security incidents could also suggest a potential breach. The absence of routine security audits or the failure to patch known vulnerabilities could also create a window of opportunity for attackers.
Potential Data Compromised and Consequences
- Social Security Numbers (SSNs): Unauthorized access to SSNs can lead to identity theft, fraudulent applications for credit and loans, and potentially, the misuse of personal funds. Real-world examples demonstrate the devastating consequences of stolen SSNs.
- Addresses: Compromised addresses can facilitate the targeting of individuals for scams, phishing attacks, and even physical threats. This can disrupt personal life and create a climate of fear and anxiety.
- Financial Information: Exposure of bank account details, credit card numbers, or other financial data can lead to significant financial losses, fraudulent transactions, and damage to creditworthiness. Financial institutions often have robust measures in place to mitigate these risks, but the potential consequences can be substantial.
Data Breach Impact Assessment
A detailed impact assessment should consider the potential financial and reputational damage of a breach. This often includes calculating the costs of remediation, legal fees, and reputational damage. This involves calculating potential loss from credit card fraud, identity theft, and related issues.
Investigation and Response
A data breach, like the one impacting Los Angeles County, demands a swift and thorough investigation and response. Effective handling of such incidents requires meticulous attention to detail, transparent communication, and a well-defined plan. This phase involves uncovering the extent of the breach, identifying the root cause, and implementing measures to mitigate future risks. A well-structured approach minimizes damage and safeguards sensitive information.
Determining the Scope of the Breach
Understanding the full extent of a data breach is crucial. This involves identifying the specific data compromised, the number of affected individuals, and the potential channels through which the data may have been accessed or transmitted. The initial steps often include reviewing logs, examining network traffic, and analyzing security systems to pinpoint the exact point of intrusion.
Identifying the Source of the Breach
Pinpointing the source of a data breach is essential for preventing similar incidents. This involves tracing the unauthorized access path, analyzing security protocols, and evaluating the roles and responsibilities of individuals involved. Often, the source is determined by examining the methods used to gain unauthorized access, such as weak passwords, vulnerabilities in software, or social engineering tactics.
Identifying Compromised Data
Determining the specific data compromised is critical for effective remediation. This process entails cataloging the types of information affected, assessing its sensitivity, and determining its potential impact on individuals and organizations. For example, identifying whether financial data, personal information, or intellectual property was compromised will influence the remediation efforts.
Best Practices for Incident Response
A well-defined incident response plan is critical to managing a data breach effectively. This includes clear communication strategies, notification procedures, and legal considerations. These steps must be meticulously planned to ensure minimal damage and legal compliance.
Communication Strategies
Effective communication with stakeholders is vital during a data breach. This includes notifying affected individuals, regulatory bodies, and the public. Transparency and promptness are key. For example, in the Los Angeles County case, clear communication to the affected individuals, including the type of data compromised, steps taken to secure the data, and future preventative measures, is essential.
Notification Procedures
Notification procedures must be meticulously followed to comply with legal requirements and inform affected parties. This involves determining the appropriate channels for notification, such as email, mail, or a dedicated website, and providing clear and concise information. Examples include explaining the nature of the breach, the steps taken to address it, and the steps individuals can take to protect themselves.
Legal Considerations
Legal considerations must be carefully evaluated during a data breach response. This includes understanding applicable laws and regulations, consulting with legal counsel, and documenting all actions taken. For instance, in a case like the Los Angeles County breach, the investigation and response must adhere to relevant data privacy laws and regulations.
Components of a Comprehensive Data Breach Response Plan
A comprehensive plan should address various aspects of the breach response, including prevention, detection, containment, eradication, recovery, and lessons learned. Each of these phases requires specific steps and procedures to ensure a smooth and effective response.
Assessing the Potential Impact of the Data Breach
Assessing the impact on various stakeholders is vital for planning effective mitigation strategies. This includes analyzing the financial losses, reputational damage, legal liabilities, and operational disruptions. For example, a data breach affecting a healthcare provider may result in patient distrust and potential legal action.
Preventive Measures
The recent data breach at Los Angeles County underscores the critical need for robust cybersecurity measures. Proactive steps are essential to mitigate the risk of future incidents and safeguard sensitive data. A comprehensive approach encompassing enhanced security protocols, employee training, and adherence to best practices is paramount. This proactive strategy will build resilience against evolving cyber threats.Effective prevention strategies require a multifaceted approach.
Organizations must prioritize security protocols, employee awareness, and the implementation of best practices. The goal is not just to react to breaches but to create a culture of security that minimizes the likelihood of incidents.
Enhanced Security Protocols
Robust security protocols are the cornerstone of any effective cybersecurity strategy. These protocols should be tailored to the specific needs and vulnerabilities of the organization. Regular security audits and penetration testing are crucial for identifying and addressing weaknesses before attackers exploit them. Implementing a layered security approach, incorporating multiple security controls, enhances protection against various threats. This approach ensures that even if one layer is compromised, other layers provide a robust defense.
The recent LA County data breach affecting 200,000 individuals highlights a critical need for better security measures. This kind of incident underscores the urgent need to deploy AI-powered tools like those discussed in “Deploying AI Code Safety Goggles Needed” Deploying AI Code Safety Goggles Needed. Ultimately, robust security protocols are essential to prevent future breaches and protect sensitive information.
Employee Training
Employee training is a critical component of a strong cybersecurity posture. Employees are often the weakest link in the security chain. Comprehensive training programs should equip employees with the knowledge and skills necessary to identify and report suspicious activities. Regular phishing simulations and security awareness training are essential to reinforce good practices and enhance vigilance. These training programs should be tailored to the specific roles and responsibilities of employees to ensure relevance and effectiveness.
The LA County data breach impacting 200,000 individuals is a serious concern, highlighting the vulnerability of our digital infrastructure. It’s worth noting that recent reports of a vulnerability in Microsoft Azure Cosmos DB, as detailed in Azure Cosmos DB Vulnerability Details , could potentially be a contributing factor to this kind of incident. This emphasizes the critical need for robust security measures across the board to protect sensitive data from breaches.
Examples include training on recognizing malicious emails, social engineering tactics, and safe password practices.
Cybersecurity Best Practices
Adhering to cybersecurity best practices is essential to preventing data breaches. A robust cybersecurity program should include regular security assessments, vulnerability scanning, and penetration testing to proactively identify and address security gaps. Regular updates and patching of software are crucial to mitigate known vulnerabilities. The implementation of strong access controls and least privilege principles restricts access to sensitive data only to authorized personnel.
Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) adds an extra layer of security to user accounts. MFA requires users to provide more than one form of verification, such as a password and a code from a mobile device. This significantly reduces the risk of unauthorized access. By requiring multiple verification steps, MFA makes it substantially more difficult for attackers to gain access to accounts even if they have obtained passwords.
Implementations should be tailored to the specific needs of the organization.
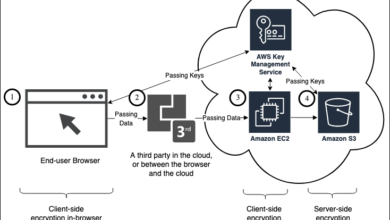
Encryption Protocols
Encryption protocols are vital for protecting sensitive data in transit and at rest. Data encryption converts readable data into an unreadable format, making it indecipherable to unauthorized individuals. Implementing encryption protocols on databases, storage devices, and communication channels is crucial for data protection. This includes end-to-end encryption for sensitive data transmission.
Security Measures Effectiveness
| Security Measure | Effectiveness | Explanation |
|---|---|---|
| Strong Passwords | High | Strong passwords are difficult for attackers to guess or crack. |
| Multi-Factor Authentication (MFA) | High | MFA adds an extra layer of security, making it harder for attackers to access accounts. |
| Regular Security Audits | Medium | Audits help identify vulnerabilities, but their effectiveness depends on the thoroughness of the process. |
| Employee Training | Medium-High | Training equips employees to recognize threats and avoid falling victim to social engineering tactics. |
| Data Encryption | High | Encrypted data is unreadable to unauthorized individuals, providing strong protection. |
Public Awareness and Education

The recent data breach impacting Los Angeles County underscores the critical need for public awareness and education on data security. A proactive approach to educating residents about potential risks and empowering them with protective measures is essential to mitigate future incidents and build a more resilient digital community. Understanding the breach and its implications can help individuals make informed decisions about their personal information.Effective public awareness campaigns can foster a culture of vigilance and empower residents to protect themselves from similar incidents.
The recent data breach in Los Angeles County, affecting nearly 200,000 individuals, highlights the urgent need for robust data security measures. Meanwhile, the Department of Justice’s recent announcement regarding a “Safe Harbor” policy for Massachusetts transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) offers a glimmer of hope for improved protections. However, these positive developments still don’t fully address the serious implications of the LA County breach and the broader issue of protecting personal information.
By providing accessible and understandable information, residents can become active participants in safeguarding their personal data. This proactive approach is vital in preventing further breaches and promoting a culture of data security.
Importance of Public Education
Public education plays a crucial role in reducing the vulnerability of individuals to data breaches. By equipping residents with knowledge and practical skills, we can empower them to recognize and avoid potential threats. A comprehensive education program should emphasize the importance of strong passwords, safe online practices, and the recognition of phishing attempts. This knowledge empowers residents to take proactive steps to protect their information, ultimately reducing the impact of future breaches.
Developing an Education Strategy
A robust education strategy should address various aspects of data security. It should incorporate clear and concise information, presented in easily understandable formats. This could include targeted social media campaigns, workshops in community centers, and partnerships with schools and local organizations. Engaging presentations, interactive workshops, and readily available online resources can significantly enhance the effectiveness of the program.
This comprehensive approach ensures that all segments of the community are reached, regardless of their level of digital literacy.
Identifying Suspicious Activity
Recognizing suspicious activity is crucial in preventing data breaches. Educating the public on common indicators of phishing attempts, such as emails or text messages with unusual requests for personal information, is paramount. Providing examples of such scams can be extremely helpful. For example, a seemingly legitimate email from a bank requesting account details should raise immediate suspicion.
Individuals should be encouraged to verify requests directly with the institution involved before taking any action. By recognizing these red flags, residents can safeguard their personal information and prevent fraud.
Resources for Personal Information Protection
A comprehensive list of resources can provide residents with the tools to protect their personal information. This should include information about creating strong passwords, using multi-factor authentication, recognizing phishing scams, and managing privacy settings on various platforms. A dedicated website or online portal, with easily accessible resources, can facilitate access to this information. It should also include contact information for reporting suspicious activities.
Furthermore, clear and simple explanations of the importance of each resource should be included.
- Strong Passwords: Use a combination of uppercase and lowercase letters, numbers, and symbols. Avoid using easily guessed passwords, such as birthdays or names. Consider using a password manager to store and generate strong passwords securely.
- Multi-Factor Authentication (MFA): Enable MFA wherever possible to add an extra layer of security to your accounts. This involves using multiple verification methods, such as a code sent to your phone or email, to confirm your identity.
- Phishing Awareness: Be cautious of emails or messages requesting personal information. Verify requests directly with the institution involved before taking any action. Never click on suspicious links or attachments.
- Privacy Settings: Review and adjust privacy settings on social media and online accounts to limit the amount of personal information shared publicly.
Methods for Raising Public Awareness
Public awareness campaigns can be designed to reach diverse audiences effectively. Consider using a mix of digital and traditional methods, such as social media posts, community events, and partnerships with local news outlets. Creating engaging videos, infographics, and interactive quizzes can help educate residents about data security in an engaging way. Collaborating with community leaders and influencers can amplify the message and increase its reach.
Impact on Services
The Los Angeles County data breach, impacting over 200,000 individuals, carries significant implications for the smooth operation of vital services. Beyond the immediate concern of compromised personal data, the breach has the potential to disrupt public trust, hinder essential operations, and even jeopardize public safety. Understanding the cascading effects of such a breach is crucial to mitigating the long-term consequences.
Potential Disruptions to Services and Operations
The data breach can lead to a multitude of operational disruptions across various county departments. Services reliant on digital systems, from scheduling appointments to processing payments, could be significantly affected. Delays in service delivery, system outages, and increased workload for support staff are all potential outcomes. Furthermore, the sheer volume of inquiries and support requests could overwhelm existing resources, leading to longer response times and frustration among citizens.
Effects on Public Trust and Confidence in Government Institutions
A data breach, especially one affecting a significant portion of the population, can severely damage public trust in government institutions. Citizens may lose confidence in the county’s ability to protect their personal information, leading to decreased participation in online services and a reluctance to engage with county agencies. This erosion of trust can have lasting consequences, potentially impacting future elections, policy decisions, and the overall relationship between the government and its constituents.
The County’s reputation for efficiency and responsiveness will be under scrutiny, demanding proactive steps to rebuild trust.
Impact on Essential Services
The breach’s impact extends to crucial services like healthcare, finance, and social security. In healthcare, compromised patient records could lead to identity theft, fraud, and the potential for medical errors. In the financial sector, unauthorized access to financial records could result in significant financial losses for residents. Social security services, if compromised, could lead to issues with benefits disbursement and identity theft, impacting the lives of countless residents.
Implications for Public Safety and Emergency Response Systems
The breach could also affect public safety and emergency response systems. Compromised data related to emergency personnel, criminal records, or other sensitive information could compromise the integrity of public safety operations. For example, compromised records of emergency personnel could affect response times or potentially leak sensitive information regarding locations of critical personnel. Further, the disruption to essential services like communications and information systems could impact the efficiency of emergency response.
Maintaining public safety during and after a breach is paramount.
Legal and Regulatory Implications
Data breaches, particularly those affecting public entities like Los Angeles County, trigger a complex web of legal and regulatory responsibilities. Understanding these implications is crucial for effective response and prevention. This section delves into the specific legal frameworks, county government obligations, potential liabilities, and penalties associated with the recent breach.
Applicable Legal Frameworks
Several federal and state laws govern data breaches in the US, impacting how Los Angeles County must handle this incident. These include regulations designed to protect individuals’ personal information and hold organizations accountable for its security. California, in particular, has stringent regulations regarding data privacy.
Responsibilities of Los Angeles County Government
Los Angeles County, as a public entity, has a responsibility to safeguard the personal data of its citizens. This involves proactive measures to prevent breaches and a robust response plan when they occur. The county must demonstrate compliance with relevant regulations, including timely notification of affected individuals and investigation into the breach’s cause.
Potential Legal Liabilities and Penalties
Failure to adequately respond to a data breach can expose Los Angeles County to significant legal liabilities. These may include civil lawsuits from affected individuals alleging damages, and potentially regulatory penalties from governing bodies for non-compliance. Examples of potential penalties include fines and reputational damage, which can severely impact public trust.
Table of Relevant Regulations and Laws
| Regulation/Law | Description | Potential Impact on County |
|---|---|---|
| California Consumer Privacy Act (CCPA) | Protects California residents’ personal information. | County must comply with notification requirements, potentially facing fines for non-compliance. |
| Health Insurance Portability and Accountability Act (HIPAA) | Protects health information. | If the breach involves protected health information (PHI), stringent HIPAA requirements must be followed. |
| Federal Trade Commission (FTC) guidelines | General guidelines for data security. | Non-compliance with these guidelines could lead to investigation and potential enforcement actions. |
| California Privacy Rights Act (CPRA) | Enhances CCPA’s protections for consumers’ data. | County must comply with CPRA provisions, potentially facing penalties for non-compliance. |
| State and Local Government Data Breach Laws | Laws applicable to specific state or local jurisdictions. | Specific requirements may vary depending on the type of information compromised and the applicable jurisdiction. |
The table above highlights some key regulations and laws. The specific applicability and the extent of the impact depend on the nature of the compromised data and the extent of non-compliance.
Closure: Los Angeles County Suffers Data Breach Impacting 200000 Individuals
In conclusion, the Los Angeles County data breach underscores the critical need for enhanced data security protocols and robust incident response plans. The potential impact on individuals and the county’s operations is substantial, demanding a comprehensive approach to investigation, remediation, and prevention. Ultimately, the breach serves as a valuable learning opportunity for the county and other institutions to prioritize data protection and build public trust.
We must learn from this unfortunate event to ensure similar breaches are less likely to occur in the future.
Popular Questions
What types of data were potentially compromised?
The specific data compromised hasn’t been publicly released. However, the Artikel suggests potentially sensitive information like Social Security numbers, addresses, financial details, and potentially medical information.
What steps is the county taking to notify affected individuals?
The Artikel doesn’t specify the exact notification procedures. However, a comprehensive response plan would include notifying affected individuals as soon as possible.
What preventative measures can individuals take to protect themselves?
Individuals can strengthen their own security practices by using strong passwords, enabling multi-factor authentication where available, and regularly reviewing their accounts for suspicious activity.
How does this breach impact public trust in government institutions?
Breaches like this can significantly erode public trust in government institutions. Transparency and swift action to address the breach are crucial in rebuilding trust.