Telkomsel Unveils Enhanced RoaMAX Haji 2026 Package, Bolstering Digital Connectivity for Indonesian Pilgrims
Jakarta, Indonesia – Telkomsel, Indonesia’s leading digital telecommunications company, has announced a comprehensive suite of digital connectivity services designed to ensure seamless communication for Indonesian pilgrims undertaking the Hajj pilgrimage in the 1447 Hijriah season. Central to this offering is the new RoaMAX Haji 2026 package, providing an expansive data quota of up to 42GB and leveraging 5G network support across Saudi Arabia, signifying a major leap in pilgrim connectivity. This initiative underscores Telkomsel’s commitment to facilitating a more connected, secure, and serene pilgrimage experience for hundreds of thousands of Indonesian citizens traveling to the Holy Land.
The Imperative of Connectivity in Modern Hajj
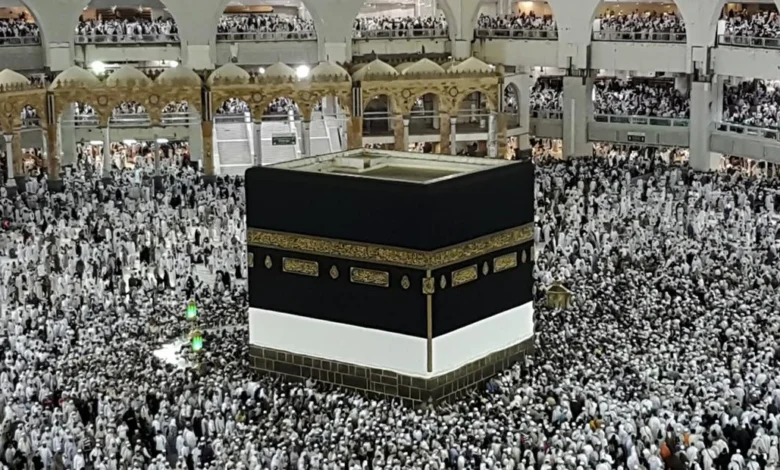
The annual Hajj pilgrimage to Mecca and Medina is one of the five pillars of Islam, drawing millions of Muslims from around the globe, including the largest contingent from Indonesia. For Indonesian pilgrims, who often embark on a journey spanning several weeks, maintaining contact with family, accessing critical information, and managing personal needs through digital platforms has become increasingly vital. The Hajj is not merely a spiritual journey but also a logistical marvel, requiring robust infrastructure and reliable communication channels to ensure the safety and well-being of pilgrims. In recent years, the integration of technology, from e-visas and digital guidance apps to emergency communication tools, has transformed the Hajj experience, making dependable connectivity an indispensable component.
Historically, pilgrims faced significant challenges in staying connected, often relying on expensive international roaming, acquiring local SIM cards with language barriers, or using public Wi-Fi with varying reliability. These hurdles could lead to feelings of isolation, anxiety for families back home, and potential delays in accessing urgent assistance. Recognizing these critical needs, telecommunication providers like Telkomsel have continuously evolved their services, moving from basic voice and SMS packages to sophisticated data-rich offerings that cater to the modern pilgrim’s demands for constant digital engagement.
Unpacking the RoaMAX Haji 2026 Offering
The RoaMAX Haji 2026 package is meticulously crafted to address the multifaceted communication requirements of pilgrims. With a substantial data allowance of up to 42GB, it is designed to support extensive usage, from frequent video calls with family to navigating unfamiliar territories using maps, accessing religious guidance applications, and staying updated with news and emergency alerts. The package boasts an impressive validity period of up to 60 days, covering the entire duration of the pilgrimage, from pre-departure preparations to the return journey.
Danang Andrianto, VP Halo Product Marketing and Engagement Service at Telkomsel, emphasized the strategic importance of this offering. "Through RoaMAX Haji 2026, we are delivering a larger quota, reliable roaming network access through collaboration with STC, Mobily, and Zain, and high-speed 5G access so that pilgrims can communicate comfortably and focus on their worship with peace of mind," Danang stated on Monday, April 20, 2026. This statement highlights the core philosophy behind the package: enabling spiritual focus by removing communication worries.
Beyond the primary data quota for use in Saudi Arabia, the RoaMAX Haji 2026 package also includes a 2GB domestic quota, specifically allocated for use during the departure process within Indonesia. This thoughtful inclusion ensures that pilgrims can stay connected with loved ones right up until their flight, managing last-minute arrangements or goodbyes without worrying about their main international quota. Furthermore, an additional 1GB quota is provided for use in 13 key transit countries, including Qatar, United Arab Emirates, Turkey, and Singapore. This feature is particularly valuable given the often long and multi-leg journeys undertaken by Indonesian pilgrims, ensuring uninterrupted connectivity even during layovers.
Technological Advancements for Superior Experience
The RoaMAX Haji 2026 package is not just about quantity but also quality. It offers access to 5G networks in Saudi Arabia, providing speeds of up to 100 Mbps, subject to network availability. The integration of 5G technology marks a significant upgrade, promising ultra-fast downloads, smoother streaming, and more responsive online experiences, which are crucial for high-bandwidth activities like video calls or accessing large digital files. This leap in speed ensures that pilgrims can utilize modern applications and services without frustration.
Moreover, the package supports Voice over LTE (VoLTE), a technology that delivers crystal-clear call quality and faster call connection times. This enhancement is particularly beneficial in crowded environments where traditional voice calls might struggle. Clear communication is paramount for coordination within pilgrim groups, contacting support services, or simply speaking with family without distortion.
Adding further value, Telkomsel has integrated free access to Qara’a, an AI-based Al-Qur’an learning application. This innovative feature leverages artificial intelligence to assist pilgrims in their spiritual studies, offering personalized guidance and tools for reciting and understanding the Holy Quran. Such an inclusion aligns perfectly with the spiritual essence of the Hajj, providing a valuable resource for pilgrims to deepen their faith while in the Holy Land.
Flexible Package Options and Robust Customer Support
Understanding that pilgrims have varying needs and budgets, Telkomsel offers a range of package choices under the RoaMAX Haji umbrella. These include:
- Internet RoaMAX Haji: Starting from Rp500,000, this package focuses primarily on data connectivity.
- Combo RoaMAX Haji: Priced from Rp610,000, this comprehensive option bundles data with talk time and SMS services, catering to those who prefer a more traditional communication mix.
- Talkmania: A specialized package designed specifically for voice calls, offering focused solutions for pilgrims who prioritize verbal communication.
These tiered options ensure that every pilgrim can find a package that best suits their individual communication preferences and financial considerations.
Beyond the packages themselves, Telkomsel has established an extensive support infrastructure to ensure pilgrims receive assistance whenever needed. In Saudi Arabia, the company has set up GraPARI outlets in Mecca and dedicated service posts in both Mecca and Medina. These physical touchpoints provide direct customer service, technical assistance, and information to pilgrims on the ground, addressing issues promptly and effectively.
Domestically, Telkomsel has deployed 17 Hajj service posts across various embarkation points in Indonesia, including major hubs like Banda Aceh, Jakarta, Surabaya, and Makassar. These pre-departure support centers assist pilgrims with activating their roaming services, understanding package details, and resolving any connectivity concerns before they even leave the country, ensuring a smooth start to their journey.
To complement the physical presence, Telkomsel also offers 24-hour, toll-free customer support through multiple digital channels. Pilgrims can access assistance via the roaming call center, through the virtual assistant Veronika, or by utilizing the dedicated "Haji Corner" feature within the MyTelkomsel application. This multi-channel approach guarantees that help is always accessible, regardless of time zone or location.
Strategic Collaborations and Broader Implications
The success of Telkomsel’s RoaMAX Haji 2026 package is heavily reliant on strategic international collaborations. The partnership with major Saudi Arabian telecommunication providers – STC, Mobily, and Zain – is crucial. These collaborations ensure extensive network coverage, reliable service quality, and seamless roaming experiences across the Kingdom. By leveraging the robust infrastructure of these local operators, Telkomsel can guarantee that its pilgrims receive the best possible connectivity, even in remote or heavily populated areas during peak Hajj rituals.
This initiative by Telkomsel carries significant implications beyond merely providing internet access. It reflects a deeper understanding of the pilgrim’s journey, addressing not just connectivity but also peace of mind, safety, and spiritual enrichment. For the Indonesian government, particularly the Ministry of Religious Affairs, such private sector initiatives are invaluable in supporting the welfare of its citizens abroad. Reliable communication services contribute directly to pilgrim safety by enabling quick access to emergency services, facilitating group coordination, and allowing families to monitor their loved ones’ well-being.
From an industry perspective, Telkomsel’s enhanced offering sets a high benchmark for telecommunication services in religious tourism. It showcases the potential of advanced technology, such as 5G and AI, to improve traditional experiences. This commitment also reinforces Telkomsel’s position as a market leader, demonstrating its corporate social responsibility and dedication to serving its vast customer base, even when they are thousands of miles away. The investment in robust roaming infrastructure and customer support solidifies its brand loyalty and reputation.
Historical Context and Evolution of Hajj Connectivity
The evolution of Hajj connectivity services has mirrored the broader advancements in telecommunications. Decades ago, pilgrims relied on international phone booths or postal services to communicate. The advent of mobile phones brought pre-paid international calling cards and basic roaming. Over the last decade, with the proliferation of smartphones and data-hungry applications, the demand shifted dramatically towards affordable and high-capacity data roaming.
Telkomsel has been at the forefront of this evolution, consistently upgrading its Hajj packages. Earlier iterations might have offered limited data or focused primarily on voice. The progression to large data quotas, 5G support, and value-added services like AI-based religious apps reflects a continuous commitment to innovation and understanding the evolving needs of its customers. This journey highlights a shift from simply providing a connection to offering a comprehensive digital ecosystem that supports every aspect of the pilgrim’s journey.
Future Outlook: Towards a Fully Digital Pilgrimage
The launch of RoaMAX Haji 2026 is a strong indicator of the future trajectory of Hajj services. As digital literacy increases and technology becomes more pervasive, pilgrims will likely demand even more integrated and personalized digital solutions. This could include enhanced virtual reality or augmented reality experiences for pre-pilgrimage preparation, more sophisticated AI assistants for real-time translation or religious guidance, and seamless integration with smart wearables for health monitoring and emergency alerts.
Telkomsel’s commitment to 5G technology and AI integration positions it well to capitalize on these future trends. The company’s proactive approach in anticipating pilgrim needs and leveraging cutting-edge technology will likely continue to shape the landscape of digital services for religious tourism, ensuring that the spiritual journey remains unburdened by communication anxieties in an increasingly interconnected world. The RoaMAX Haji 2026 package is not just a service; it’s a testament to how technology can profoundly enhance one of humanity’s most sacred journeys.