Memory Card and USB Drive Prices Soar by an Average of 123% Amidst Surging AI Data Center Demand, Sparking Market Uncertainty
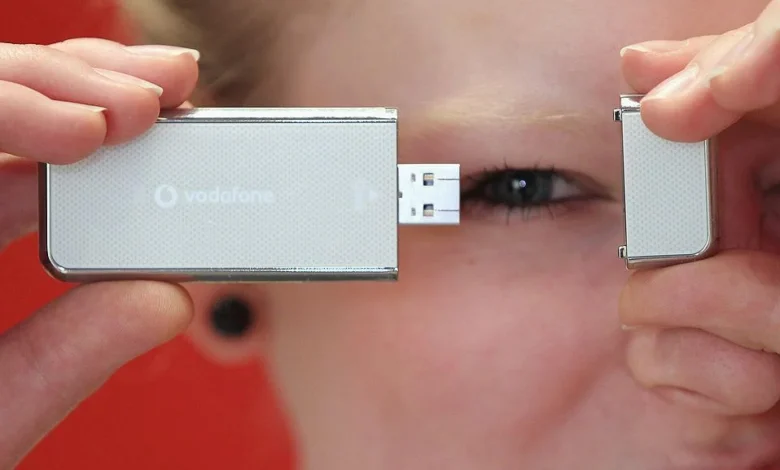
Jakarta, April 20, 2026 – A significant and alarming trend has emerged in the global memory market, with prices for ubiquitous consumer storage devices such as memory cards and USB flash drives witnessing unprecedented surges. According to recent findings by Tom’s Hardware, referencing an investigation by PCWorld, the average price increase for these essential components has reached a staggering 123 percent year-on-year. This dramatic escalation is not merely an isolated incident but a widespread phenomenon, with no examples of price stability or decline found across numerous product samples. In fact, some specific products have seen even more extreme hikes, such as the Lexar Blue microSDXC UHS-I 256GB card, which reportedly skyrocketed by an astonishing 261 percent compared to the previous year. This market upheaval is directly attributed to an insatiable demand for high-quality NAND flash memory from the burgeoning artificial intelligence (AI) data center sector, diverting critical production capacity and leaving consumer-grade products in short supply.
The Underlying Mechanics: NAND Flash Memory and Its Dual Role
At the core of this price crisis lies NAND flash memory, a non-volatile storage technology indispensable for a vast array of electronic devices. From high-performance Solid State Drives (SSDs) that power modern computers to the tiny memory cards in smartphones and digital cameras, and the portable convenience of USB flash drives, NAND is the silent workhorse. The fundamental issue stems from the shared manufacturing infrastructure for these diverse applications. Memory cards and USB drives, while seemingly distinct from enterprise-grade SSDs, are produced using NAND chips derived from the very same silicon wafers and production lines. The distinction often lies in the quality grading of these chips; higher-performing, more durable, and more reliable NAND blocks are typically reserved for demanding applications like enterprise SSDs, while lower-tier, yet still perfectly functional, chips are allocated for consumer-grade memory cards and flash drives.
Historically, the NAND flash market has been characterized by cyclical patterns of oversupply and undersupply, leading to fluctuating prices. Manufacturers like Samsung, SK Hynix, Micron, Kioxia/Western Digital, and YMTC invest billions in fabricating advanced NAND chips, constantly striving for higher density, faster speeds, and lower cost per bit. However, the current surge is not merely a typical market cycle; it’s an unprecedented disruption driven by a new, immensely powerful demand force.
The AI Revolution: A Game-Changer for NAND Demand
The advent and rapid expansion of artificial intelligence, particularly large language models (LLMs) and deep learning applications, have fundamentally altered the landscape of data center infrastructure. Training these sophisticated AI models requires colossal datasets and immense computational power, which in turn necessitates vast quantities of high-performance, high-endurance storage. AI data centers are willing to pay a substantial premium for top-tier NAND chips due to their critical requirements:
- Speed: AI workloads involve continuous reading and writing of massive datasets, demanding the fastest possible data transfer rates.
- Endurance: The intense and repetitive write cycles inherent in AI model training quickly wear out lower-grade NAND. High-endurance chips are crucial to ensure operational longevity and prevent costly data loss or system downtime.
- Reliability: Data integrity is paramount in AI applications; even minor errors can compromise model accuracy or training progress.
This confluence of factors has positioned AI data centers as the undisputed priority customers for NAND manufacturers. With significant capital and strategic imperatives at stake, AI companies are placing massive, long-term orders and are demonstrating a willingness to absorb higher costs, effectively outbidding other sectors for the available premium NAND supply. Manufacturers, logically, have re-optimized their production lines and resource allocation to cater to these high-margin, high-volume enterprise orders, shifting focus away from lower-profit consumer products.
A Chronology of Rising Costs and Market Shifts
The impact of AI’s burgeoning demand on the NAND market began to materialize noticeably in late 2023 and early 2024. Prior to this, the memory market, particularly for NAND, had experienced a period of oversupply, leading to price declines. However, as AI investments surged, particularly following the mainstream success of generative AI applications, demand for high-bandwidth memory (HBM) and enterprise NAND began to escalate sharply.
- Q4 2023: Early indicators emerged as enterprise SSD prices began to firm up, a precursor to broader market shifts. Manufacturers started signaling a strategic pivot towards higher-value products.
- Q1 2024: Industry analysts like TrendForce reported significant increases in contract prices for enterprise SSDs and NAND wafers, forecasting continued upward trends. The first signs of constrained supply for lower-grade NAND began to appear.
- Mid-2024: Spot market prices for NAND components started their upward trajectory, reflecting tightening supply. Retailers began adjusting prices for memory cards and USB drives, though initially at a slower pace.
- Late 2024 – Early 2025: The full force of the supply diversion became apparent. As production capacities were increasingly dedicated to enterprise and AI-specific NAND, the availability of chips for consumer-grade products dwindled significantly. This period saw more pronounced retail price increases.
- Early 2026 (Current Situation): The Tom’s Hardware/PCWorld investigation, released around April 2026, solidifies these observations, detailing the average 123% price surge and extreme individual cases. The market has reached a critical point where the scarcity of lower-grade NAND is fundamentally reshaping product availability and pricing for the average consumer.
One stark illustration of this market shift is the recent release by SanDisk. Earlier this month, the company launched a 2TB SD card priced at an astonishing USD 2,000 (approximately Rp 32 million), even after a USD 500 discount. While a 2TB SD card represents cutting-edge capacity, its premium pricing reflects not only its technological advancement but also the underlying cost structure and market dynamics favoring high-margin, high-capacity storage solutions over affordability for mass consumer segments. This move highlights how some major brands are now compelled to focus their efforts on premium product lines, where the economics of higher-priced NAND can be absorbed, rather than competing in the increasingly constrained and less profitable budget segments.
Supporting Data and Market Analysis
Market intelligence firms have been closely tracking these trends. TrendForce, a leading research provider for the memory industry, has consistently highlighted the robust demand for high-density, high-performance NAND from the AI and server sectors. Their reports indicate that NAND flash bit shipments for AI servers are projected to grow exponentially, placing immense pressure on the overall supply. While manufacturers are investing in new fabrication plants and technologies, the lead time for bringing new capacity online is typically 18-24 months, meaning current demand far outstrips immediate supply expansion capabilities.
Furthermore, the shift towards advanced NAND architectures like QLC (Quad-Level Cell) and PLC (Penta-Level Cell) aims to increase storage density and reduce cost per bit. However, these technologies, while promising for future cost efficiencies, still require significant R&D and manufacturing optimization. In the short term, the primary focus remains on fulfilling the immediate and lucrative AI demand using established, high-quality TLC (Triple-Level Cell) NAND, which is often preferred for its balance of performance and endurance. This strategic prioritization directly impacts the availability of less premium TLC or older generation MLC (Multi-Level Cell) NAND typically used in consumer products.
Implications for Consumers, Businesses, and the Broader Economy
The soaring cost of memory cards and USB drives carries significant implications across various sectors:
- For Consumers: Everyday users, photographers, videographers, and mobile device owners will bear the brunt of these price increases. The cost of expanding storage on cameras, drones, smartphones, or simply having a portable backup solution has become substantially higher. This could deter casual users from purchasing additional storage or force them to opt for lower capacities, impacting their digital lifestyles.
- For Small Businesses and Creative Professionals: Industries reliant on high-volume data capture, such as independent film production, event photography, or data archiving for small businesses, face increased operational costs. The ability to quickly and affordably transfer and store large files is crucial for these professionals, and the current market makes this more challenging.
- For Manufacturers of Consumer Electronics: Companies producing digital cameras, action cameras, drones, and other devices that rely on external flash storage will either have to absorb higher component costs, pass them on to consumers through increased product prices, or consider bundling devices with smaller-capacity storage to manage costs. This could potentially slow down innovation in certain consumer segments that have historically benefited from cheap, abundant flash storage.
- Broader Economic Impact: The rising cost of essential digital components contributes to inflationary pressures within the electronics sector. It also underscores a broader trend where the immense capital flowing into AI is creating ripple effects throughout the technology supply chain, prioritizing enterprise and specialized applications over mainstream consumer affordability.
Statements and Analyst Outlook: When Will Normalcy Return?
While no specific official statements from individual NAND manufacturers regarding consumer product pricing were part of the original report, it can be logically inferred that their focus remains on strategic alignment with high-growth sectors. Manufacturers would likely issue general statements emphasizing their commitment to optimizing production efficiencies, meeting global demand, and investing in next-generation technologies. Their public discourse would likely highlight the overall growth of the memory market driven by emerging technologies, indirectly justifying their prioritization of enterprise clients.
The critical question for consumers and the broader market remains: when will this supply crisis abate, and prices return to more sustainable levels? Opinions among industry analysts are divided:
- The Pessimistic View (2027 or Beyond): Some analysts, citing the immense and sustained investment in AI infrastructure, believe that the current demand-supply imbalance for high-quality NAND will persist for a considerable period, potentially extending until 2027 or even later. They argue that the sheer scale of AI build-outs, coupled with the long lead times required to bring new NAND fabrication facilities online and ramp up production, means that supply will struggle to catch up with demand for several years. This outlook suggests that consumers should brace for a prolonged period of elevated memory prices.
- The Optimistic View (Sooner Correction): Conversely, other experts point to recent market corrections in other memory segments, such as DDR5 RAM, as a potential harbinger of what could happen in the NAND market. DDR5, after an initial period of high prices and limited availability driven by new technology adoption and manufacturing challenges, has recently seen price stabilization and even some declines as production matured and supply chains adjusted. This perspective suggests that while AI demand is powerful, the market’s inherent cyclical nature and manufacturers’ eventual ability to increase capacity could lead to a sooner-than-expected price correction for NAND, possibly by late 2026 or early 2027. However, it’s crucial to acknowledge that the AI-driven demand for NAND might be a more fundamentally disruptive force than the typical technology transition seen with DRAM. The sheer volume and specialized nature of NAND required for AI could mean that the correction takes longer or is less pronounced for certain grades of NAND.
Conclusion: A New Era for Digital Storage
The dramatic surge in memory card and USB drive prices marks a significant turning point in the digital storage landscape. Fueled by the insatiable appetite of AI data centers for high-quality NAND flash memory, manufacturers have strategically reoriented their production, leaving consumer-grade products in short supply and driving up costs. While the long-term outlook remains uncertain, with predictions ranging from a sustained crisis until 2027 to a potential earlier correction mirroring DDR5 RAM, the immediate reality for consumers is one of significantly higher prices for essential digital storage. This situation underscores the profound and far-reaching economic implications of the AI revolution, demonstrating how a technological advancement in one sector can profoundly reshape market dynamics and consumer accessibility across the entire digital ecosystem. The coming months will be critical in determining whether the market can adapt to this new paradigm or if affordable flash storage for the masses becomes a relic of a bygone era.