Security
-
Cybersecurity & Protection
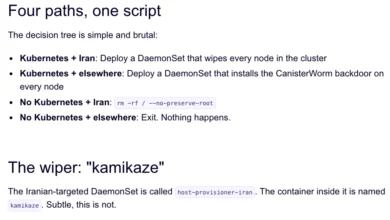
TeamPCP Targets Iran with Data-Wiping Worm, Exploits Cloud Vulnerabilities
A financially motivated cybercrime syndicate known as TeamPCP has escalated its operations by unleashing a sophisticated data-wiping worm that targets…
Read More » -
Cybersecurity & Protection

ZionSiphon Malware Targets Israeli Water Systems, Raising Critical Infrastructure Security Concerns
Cybersecurity researchers have identified a new and sophisticated piece of malware, codenamed ZionSiphon, which exhibits a clear and deliberate focus…
Read More » -
Cybersecurity & Protection

LockBit Dominates Summer Ransomware Landscape Amidst Conti Offshoot Resurgence
Ransomware attacks have surged this summer, with the LockBit group emerging as the most prolific threat actor, relentlessly targeting organizations…
Read More » -
Mobile Application Development
Google Play Announces Major Privacy and Security Updates Including New Contact and Location Features and Official Account Transfer Tools
Google has unveiled a comprehensive suite of policy updates and developer tools designed to fortify user privacy and streamline the…
Read More » -
Software Development

Navigating the Evolving Landscape of Technology, Security, and Human Values
The technological sphere continues its rapid evolution, marked by significant developments in artificial intelligence, cybersecurity, and the fundamental principles guiding…
Read More » -
Cybersecurity & Protection

The Face Behind the Ransomware: Daniil Maksimovich Shchukin Identified as Leader of GandCrab and REvil
The shadowy figure operating under the moniker "UNKN," or "UNKNOWN," who helmed some of the most disruptive ransomware operations in…
Read More » -
Cybersecurity & Protection

Experts Uncover Critical "By Design" Weakness in Model Context Protocol, Threatening AI Supply Chain
Cybersecurity researchers have identified a fundamental architectural flaw within the Model Context Protocol (MCP) that could enable remote code execution…
Read More » -
Cybersecurity & Protection

Massive "0ktapus" Phishing Campaign Exploits Multi-Factor Authentication, Compromising Over 130 Companies and 9,931 Accounts
A sophisticated and sprawling phishing campaign, dubbed "0ktapus" by cybersecurity researchers, has successfully ensnared over 130 companies worldwide, leading to…
Read More » -
Cybersecurity & Protection

Beyond Ransomware: Why Business Continuity, Not Just Backup, is Crucial for Survival
Ransomware and sophisticated cyberattacks frequently capture headlines, painting a vivid picture of data loss and operational paralysis. However, the narrative…
Read More »

