Tens of Thousands of Hikvision Cameras Remain Unpatched Against Critical 11-Month-Old Vulnerability, Exposing Organizations Worldwide

A significant cybersecurity threat continues to loom over numerous organizations globally, as an alarming number of Hikvision surveillance cameras remain vulnerable to a critical command injection flaw that has been publicly known for nearly a year. New research indicates that over 80,000 of these devices are still susceptible to exploitation, leaving a vast attack surface open for malicious actors. This persistent vulnerability, tracked as CVE-2021-36260, carries a severe CVSS score of 9.8 out of 10, underscoring its critical nature and the potential for widespread compromise.
Hikvision, formally known as Hangzhou Hikvision Digital Technology, is a prominent Chinese state-owned manufacturer of video surveillance equipment. Its products are deployed in over 100 countries, including significant installations within the United States. This widespread adoption, coupled with the unpatched vulnerability, raises serious concerns about the security posture of critical infrastructure, businesses, and public spaces reliant on Hikvision’s extensive camera network. The U.S. Federal Communications Commission (FCC) previously identified Hikvision as an "unacceptable risk to U.S. national security" in 2019, adding another layer of geopolitical and security apprehension to the current situation.
The command injection flaw, first disclosed to the public last Fall, allows attackers to execute arbitrary commands on the affected Hikvision devices. This capability can lead to a complete takeover of the camera, enabling attackers to surveil sensitive areas, manipulate footage, or use the compromised device as a pivot point to access other systems within a network. The fact that more than 80,000 devices remain unpatched, despite the severity of the vulnerability and the passage of almost a year, suggests a critical gap in patch management practices across a significant portion of Hikvision’s user base.
A Persistent Threat: Timeline and Discovery
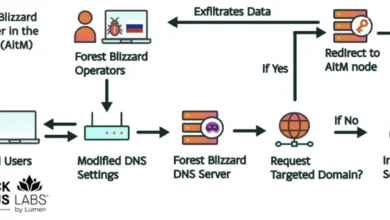
The vulnerability, officially designated as CVE-2021-36260, was initially brought to light in the latter half of 2021. Security researchers and vendors began issuing warnings and recommendations for patching soon after its public disclosure. However, the recent research highlights a disturbing lack of remediation efforts. The researchers have also uncovered evidence of active exploitation attempts, noting "multiple instances of hackers looking to collaborate on exploiting Hikvision cameras using the command injection vulnerability." These discussions and collaborations have been observed on Russian dark web forums, where leaked credentials for compromised Hikvision devices are also reportedly being offered for sale.
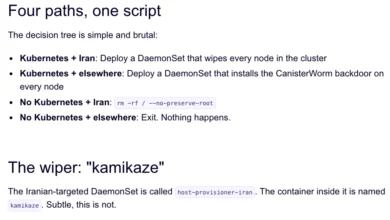
The implications of such a widespread, unpatched vulnerability are multifaceted. The full extent of damage already inflicted is difficult to ascertain, as compromised devices may be used for clandestine surveillance or as part of larger botnets without immediate detection. The authors of the report have speculated that state-sponsored threat groups, including Chinese entities such as MISSION2025/APT41, APT10 and their affiliates, as well as unknown Russian threat actor groups, could leverage these vulnerabilities. Their motives could range from intelligence gathering to geopolitical disruption, given the nature of surveillance equipment.
The IoT Security Conundrum: Beyond Simple Negligence
While the prolonged lack of patching might initially suggest user negligence, the issue of securing Internet of Things (IoT) devices, particularly surveillance cameras, is often more complex. David Maynor, senior director of threat intelligence at Cybrary, points to systemic issues within Hikvision’s product design and the broader IoT ecosystem. "Their product contains easy to exploit systemic vulnerabilities or worse, uses default credentials," Maynor stated, highlighting a fundamental weakness in the devices themselves. He further elaborated on the challenges of remediation and verification: "There is no good way to perform forensics or verify that an attacker has been excised. Furthermore, we have not observed any change in Hikvision’s posture to signal an increase in security within their development cycle." This suggests that even with awareness, organizations might face significant hurdles in securing these devices.
Paul Bischoff, a privacy advocate with Comparitech, echoed these sentiments, emphasizing the inherent difficulties in patching IoT devices compared to more conventional computing systems. "IoT devices like cameras aren’t always as easy or straightforward to secure as an app on your phone," Bischoff explained in a statement. "Updates are not automatic; users need to manually download and install them, and many users might never get the message." He further noted the lack of user feedback mechanisms on IoT devices: "Furthermore, IoT devices might not give users any indication that they’re unsecured or out of date. Whereas your phone will alert you when an update is available and likely install it automatically the next time you reboot, IoT devices do not offer such conveniences." This disparity in user experience and update mechanisms creates a fertile ground for vulnerabilities to persist unnoticed.
The Role of Default Credentials and Discovery Tools
A significant compounding factor, as identified by Bischoff, is the widespread use of default credentials. Hikvision cameras, like many other IoT devices, often ship with a limited set of predetermined default passwords. Many users, either due to a lack of awareness or convenience, fail to change these passwords from the factory settings. This practice creates an easily exploitable entry point for attackers.
Cybercriminals actively scan the internet for vulnerable devices using specialized search engines like Shodan and Censys. These platforms allow threat actors to discover devices with open ports and identifiable vulnerabilities, including those running unpatched software or using default login credentials. The combination of weak default security, the complexity of manual patching for IoT devices, and a lack of user awareness creates a perfect storm, leaving tens of thousands of organizations unknowingly exposed.
Broader Implications and the Path Forward
The persistent vulnerability in Hikvision cameras has far-reaching implications. For businesses, a compromised camera system can lead to intellectual property theft, industrial espionage, or disruptions to operations. For government entities and critical infrastructure, the risk is amplified, potentially impacting national security and public safety. The ability of threat actors to gain persistent access to surveillance networks can facilitate reconnaissance for more significant attacks, compromise sensitive data, or even be used for targeted disinformation campaigns.
The lack of timely patching also reflects a broader challenge within the cybersecurity landscape concerning the lifecycle management of IoT devices. Manufacturers have a responsibility to provide secure products and accessible update mechanisms, while users and organizations must prioritize security updates and robust password management practices.
Hikvision, as a major global supplier, faces pressure to not only provide effective patches but also to improve the inherent security of its future product lines and to better support its existing customer base in the update process. The ongoing threat posed by CVE-2021-36260 serves as a stark reminder of the critical need for vigilance, proactive security measures, and a collaborative approach between manufacturers, users, and cybersecurity researchers to mitigate the risks associated with the ever-expanding world of connected devices. Until these issues are comprehensively addressed, the threat of exploitation will continue to loom large over the thousands of organizations reliant on Hikvision’s surveillance technology.