authentication
-
Cloud Computing

Traditional authentication is incapable of securing AI agents, the company says, as it announces Access Intelligence.
The rapid proliferation of sophisticated, increasingly autonomous AI agents in enterprise development, projected to surge by 2026, presents a formidable…
Read More » -
Software Development
Public Integration Without Authentication Exposes Critical Control Failure
A recent high-profile incident, where the threat actor group ShinyHunters claimed a breach of Rockstar Games’ environment, has illuminated a…
Read More » -
Cybersecurity & Protection

Massive "0ktapus" Phishing Campaign Exploits Multi-Factor Authentication, Compromising Over 130 Companies and 9,931 Accounts
A sophisticated and sprawling phishing campaign, dubbed "0ktapus" by cybersecurity researchers, has successfully ensnared over 130 companies worldwide, leading to…
Read More » -
Cybersecurity & Protection
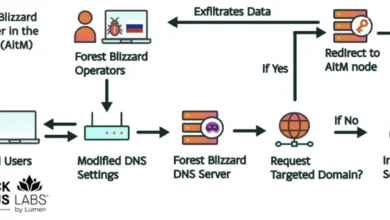
Russian Military Intelligence Exploits Vulnerable Routers for Mass Harvesting of Microsoft Office Authentication Tokens
Hackers associated with Russia’s military intelligence units have been conducting a sophisticated espionage campaign, leveraging well-known vulnerabilities in older Internet…
Read More »
