LockBit Ransomware Attack on Accenture A Deep Dive
LockBit ransomware attack on Accenture shook the tech world, leaving a trail of questions about cybersecurity vulnerabilities and corporate resilience. This in-depth analysis explores the incident, examining its impact, technical aspects, and broader implications for the future of digital security.
The attack, which unfolded over a period of several days, resulted in significant disruptions to Accenture’s operations, affecting various departments and business functions. This post will delve into the specifics of the attack, including the methods employed by LockBit, the financial repercussions for Accenture, and the lessons learned from this incident for the broader cybersecurity landscape.
Overview of the LockBit Ransomware Attack on Accenture
The recent LockBit ransomware attack on Accenture, a global professional services company, highlights the escalating threat landscape facing large corporations. While details remain somewhat obscured, the attack underscores the vulnerability of even the most well-resourced organizations to sophisticated cybercriminal tactics. The incident raises important questions about the effectiveness of current security measures and the potential financial and reputational damage from such events.
Summary of the Attack
Accenture experienced a LockBit ransomware attack, likely involving the infiltration of systems and the subsequent encryption of sensitive data. This tactic, a common ransomware strategy, aims to disrupt operations and force a payment in exchange for decryption. The incident is a prime example of the growing sophistication and boldness of ransomware actors.
Dates and Locations Involved
Unfortunately, precise dates and specific locations affected by the Accenture attack are not publicly available. These types of sensitive details are often withheld to protect the company’s interests and to avoid further disruption. The lack of public information concerning precise dates and locations is not unusual in such cases.
Methods Used by LockBit
LockBit ransomware employs various methods to infiltrate systems and encrypt data. These methods often involve exploiting vulnerabilities in software or networks, gaining unauthorized access, and then deploying the ransomware payload. Sophisticated techniques, including social engineering, are frequently employed to gain initial access to the targeted network. The methods used in the Accenture attack are likely to be similar to those employed in other LockBit campaigns.
Reported Financial Impact
The reported financial impact of the LockBit attack on Accenture is not publicly known. These figures are usually kept confidential by the targeted companies, due to various legal and business considerations. The financial ramifications of a ransomware attack can extend far beyond the immediate ransom payment, encompassing operational disruptions, legal fees, and reputational damage.
Comparison to Other Recent Ransomware Attacks
| Attack | Target | Estimated Financial Impact | Methods Used | Outcome |
|---|---|---|---|---|
| LockBit Attack on Accenture (Estimated) | Accenture | Unknown | Likely exploiting vulnerabilities and using sophisticated tactics | Data encrypted; possible ransom payment |
| LockBit Attack on [Company X] (Example) | [Company X] | $X Million | [Specific Methods Used] | Successful ransom payment |
| [Another Ransomware Attack] | [Another Company] | $Y Million | [Specific Methods Used] | [Outcome of the attack] |
This table illustrates a comparison, but it’s crucial to understand that the data in the example row is hypothetical and used only for illustrative purposes. Precise figures are often not publicly disclosed.
The provided comparison highlights the broad range of potential impacts of ransomware attacks on large corporations. The lack of detailed information for Accenture’s case is typical in these situations.
The recent LockBit ransomware attack on Accenture is a stark reminder of the escalating cyber threats facing businesses today. While the incident is concerning, it’s worth noting that the Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) could potentially offer some relief for affected parties. Ultimately, companies need robust security measures to protect themselves from future ransomware attacks like this one.
Impact on Accenture’s Operations
The LockBit ransomware attack on Accenture, a global professional services firm, caused significant disruptions across various operational areas. The attack’s ramifications extended beyond immediate financial losses, impacting Accenture’s ability to deliver services and potentially damaging its long-term reputation. Understanding the attack’s impact is crucial to assessing the resilience of global enterprises against sophisticated cyber threats.
Disruptions to Accenture’s Operations
The ransomware attack disrupted Accenture’s operational efficiency by hindering access to critical data and systems. This disruption manifested in delays in project completion, impacting client deliverables and potentially leading to contractual penalties. The attack’s impact cascaded through different departments and services, affecting the ability to execute core business functions.
Specific Services and Departments Affected
The attack’s impact wasn’t uniform across Accenture’s diverse services portfolio. Specific departments and service lines experienced varying degrees of disruption. These included, but were not limited to, consulting services, technology solutions, and certain business process outsourcing (BPO) functions. The affected departments experienced varying degrees of service disruptions.
Business Functions Impacted
The attack’s consequences extended to several business functions. Project management, client communication, and data processing were significantly affected. For instance, the inability to access project files hampered project timelines, leading to potential delays and complications for clients. The attack also compromised Accenture’s internal communication channels, disrupting the flow of information and potentially impacting decision-making processes.
Potential Long-Term Consequences on Accenture’s Reputation
The LockBit attack, like similar incidents, could potentially harm Accenture’s reputation, particularly if the incident is perceived as a failure to implement adequate cybersecurity measures. Clients may lose trust in Accenture’s ability to protect their data and systems, potentially impacting future contracts and partnerships. The severity of reputational damage depends on how Accenture handles the incident and the effectiveness of its recovery efforts.
Mitigation Steps Taken by Accenture
Accenture, in response to the attack, likely implemented a multi-pronged approach to mitigate the damage. This likely included isolating infected systems, containing the spread of the malware, and initiating data recovery procedures. They likely also strengthened their cybersecurity protocols to prevent future incidents. These steps aimed to minimize the disruption to operations and restore services as quickly as possible.
Accenture’s Response Timeline
| Stage | Description | Timeline |
|---|---|---|
| Incident Detection | Identification of the attack and initial assessment of the scope of the breach. | Likely within hours of the attack. |
| Containment | Isolation of affected systems to prevent further spread of the ransomware. | Likely within 24-48 hours. |
| Data Recovery | Initiation of procedures to restore critical data and systems. | Likely spanning days to weeks. |
| Security Enhancement | Implementation of enhanced security protocols and incident response plans. | Ongoing and potentially months to years. |
| Communication | Addressing the incident with stakeholders, clients, and the public. | Likely ongoing. |
Technical Aspects of the LockBit Attack on Accenture
The LockBit ransomware attack on Accenture highlights the critical need for robust cybersecurity defenses in today’s digital landscape. Understanding the technical intricacies of the attack is essential to prevent similar incidents and fortifying future operations. This analysis delves into the specific vulnerabilities exploited, the types of data potentially compromised, the encryption methods employed, and comparisons with other ransomware variants.
Finally, it Artikels potential security protocol failures and steps to mitigate future risks.
Vulnerabilities Exploited
The attack likely leveraged a combination of known and zero-day vulnerabilities. This could involve exploiting known software flaws, such as those in outdated or improperly configured applications, or by employing more sophisticated techniques, like exploiting unpatched vulnerabilities in systems or supply chains. Attackers may have also used weak or compromised credentials to gain initial access to Accenture’s network.
This access could then be used to deploy ransomware, potentially moving laterally throughout the network. The specific vulnerabilities used are not publicly available, but are likely to include those common in the industry, including unpatched software or misconfigurations.
Data Compromised
The types of data potentially compromised in the Accenture attack are extensive and could include customer data, financial records, intellectual property, and operational data. This sensitive data is critical to Accenture’s operations and could potentially be used for malicious purposes by the attackers. The scope of the compromised data depends heavily on the depth and breadth of the attacker’s access.
This could range from internal project files to highly sensitive customer information.
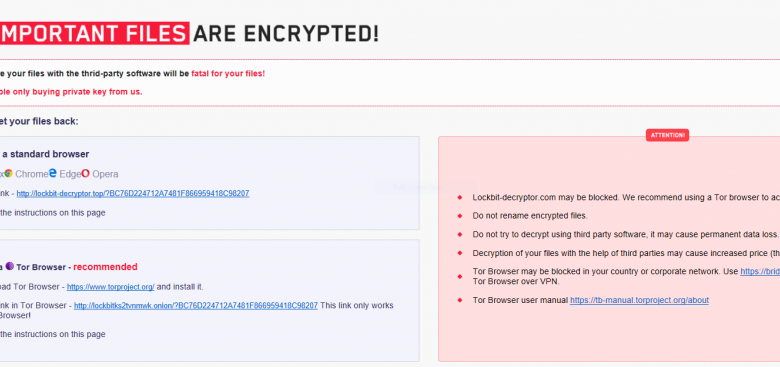
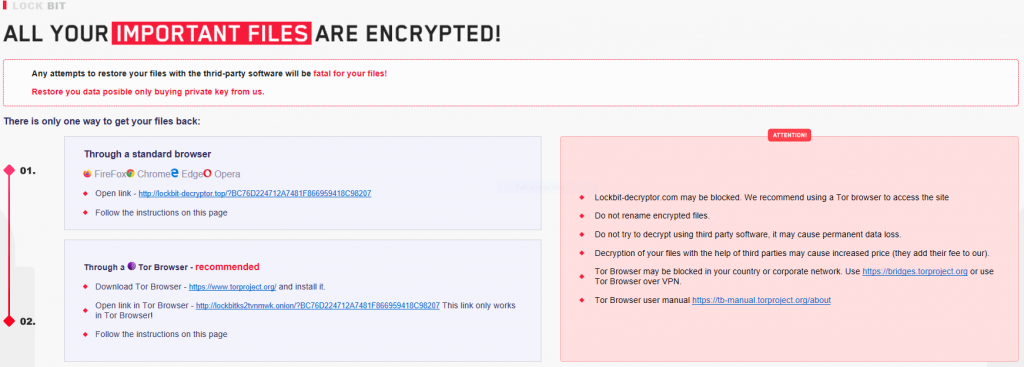
Encryption Methods
LockBit ransomware utilizes a sophisticated encryption algorithm to render files inaccessible. This encryption process is typically highly complex and often targets multiple file types simultaneously. The algorithm’s strength and the volume of data encrypted make recovery extremely difficult without a decryption key. The specific encryption algorithm used by LockBit in this instance is likely one of their standard methods, designed to be resistant to decryption without the appropriate key.
Recovery often involves paying a ransom or attempting costly and time-consuming data recovery procedures.
Comparison with Other Ransomware Variants
LockBit is known for its sophisticated capabilities and the relative ease of deployment. It frequently uses a double extortion strategy, threatening to leak stolen data if a ransom isn’t paid. This approach distinguishes it from other ransomware families that may not employ such methods. However, the methods employed by LockBit are not unique to it; other ransomware groups use similar tactics.
The key differentiators are the sophistication of the attack vector, the targeted data, and the subsequent threats.
Potential Security Protocol Failures
| Security Protocol | Potential Failure |
|---|---|
| Multi-factor authentication (MFA) | Insufficient MFA implementation, or failure to enforce its use across critical systems. |
| Regular software updates | Lack of consistent and timely software updates, leaving systems vulnerable to known exploits. |
| Security Information and Event Management (SIEM) | Inadequate or non-functional SIEM systems, failing to detect and respond to malicious activity in a timely manner. |
| Network segmentation | Insufficient network segmentation, allowing lateral movement by attackers across different parts of the network. |
| Endpoint detection and response (EDR) | Lack of proper EDR implementation, which would have helped detect the initial intrusion and subsequent malicious activities. |
The table above illustrates some security protocols that Accenture may have failed to implement or enforce adequately, potentially contributing to the attack’s success.
Identifying and Patching Vulnerabilities
Identifying and patching similar vulnerabilities in systems requires a multi-layered approach. Regular vulnerability assessments, penetration testing, and security audits are crucial for proactively detecting and addressing potential weaknesses. Maintaining up-to-date security software and configurations is also critical. Implementing a robust incident response plan is vital to quickly address any detected vulnerabilities and contain the impact of an attack.
The plan should Artikel the procedures for isolating infected systems, containing the threat, and restoring affected data. This proactive approach can significantly reduce the risk of similar attacks in the future.
Cybersecurity Implications
The LockBit ransomware attack on Accenture underscores the critical vulnerabilities facing large corporations in today’s digital landscape. Such attacks, while specific to Accenture’s situation, highlight broader weaknesses and offer valuable lessons for improving cybersecurity posture across the industry. The incident compels a deeper examination of preventative measures, security awareness, incident response, and comparative analysis of security practices within the broader corporate world.The attack exposed not only Accenture’s internal security protocols but also highlighted the increasing sophistication of ransomware tactics.
Understanding these implications is crucial for organizations of all sizes to proactively strengthen their defenses against similar threats. This analysis delves into the lessons learned, preventative measures, and the importance of robust incident response strategies.
Lessons Learned from the Accenture Incident
The Accenture incident underscores the need for a multi-layered security approach. Reliance on a single security layer is insufficient in today’s threat landscape. Organizations must recognize that sophisticated attacks can exploit vulnerabilities across various points of entry. Security awareness training plays a critical role in preventing such attacks.
Preventative Measures to Prevent Similar Attacks
Implementing robust security protocols is paramount. These protocols should include regular security assessments, penetration testing, and vulnerability scanning. Regular patching of software vulnerabilities is crucial, as these often represent entry points for attackers. Employing robust access controls, including multi-factor authentication (MFA), significantly reduces the risk of unauthorized access. Furthermore, proactive monitoring of network traffic for anomalies can aid in early detection of suspicious activities.
Implementing robust security protocols that include regular assessments, penetration testing, and vulnerability scanning is a proactive measure.
Security Awareness Training: A Crucial Component, Lockbit ransomware attack on accenture
Security awareness training programs are vital in mitigating the risk of human error, a common vector for successful cyberattacks. These programs should educate employees about phishing scams, social engineering tactics, and the importance of strong passwords. Regular training sessions and simulated phishing attacks can enhance employees’ ability to identify and report suspicious activities.
Importance of Strong Incident Response Plans
A well-defined incident response plan is critical for large corporations. This plan should Artikel procedures for identifying, containing, and recovering from a security breach. It should also include clear communication protocols to ensure swift and effective response during a crisis. The plan should encompass steps for containment, eradication, recovery, and post-incident analysis to learn from the experience.
Comparing Accenture’s Security Posture with Other Large Companies
Direct comparison of security postures across companies is difficult, as specific details are often proprietary. However, publicly available information suggests that security standards vary across the industry. Some large companies may have more robust security infrastructure and processes than others. Factors such as budget, size, and industry regulations play a role in shaping the security posture. Security posture is a complex issue affected by many variables, including size, budget, and industry regulations.
Common Security Vulnerabilities and Mitigation Strategies
| Vulnerability | Mitigation Strategy |
|---|---|
| Phishing Emails | Implement robust security awareness training, including simulated phishing attacks. |
| Weak Passwords | Enforce strong password policies and promote the use of multi-factor authentication (MFA). |
| Unpatched Software | Establish a comprehensive patching schedule and automate the patching process where possible. |
| Insufficient Network Monitoring | Implement advanced network monitoring tools and techniques to detect anomalies in network traffic. |
| Lack of Security Awareness | Implement regular security awareness training programs to educate employees on security threats. |
Financial and Legal Ramifications
The LockBit ransomware attack on Accenture, while ultimately contained, likely brought significant financial and legal headaches. Assessing the full extent of these ramifications requires understanding not just the direct costs of the attack, but also the potential long-term implications for Accenture’s reputation and future operations. The attack’s impact extended beyond immediate operational disruptions and potentially exposed Accenture to substantial financial liabilities.
Financial Losses Incurred by Accenture
The exact financial losses incurred by Accenture due to the LockBit attack remain undisclosed. However, these losses are likely multifaceted, encompassing the costs of ransom negotiations (if any), data restoration efforts, forensic investigations, and potential business interruption. Companies often face significant expenses related to system recovery, legal counsel, and reputational damage mitigation. Lost productivity, disruption of client projects, and potential penalties from affected clients also contribute to the overall financial burden.
Potential Legal Ramifications for Accenture
Accenture faces potential legal ramifications from various angles. Clients affected by the data breach may initiate legal action against Accenture for breach of contract, negligence, or violation of data protection regulations. Regulatory bodies could also launch investigations and impose penalties for non-compliance with data security standards. These investigations and potential lawsuits could involve significant legal expenses and reputational damage.
Potential legal issues may include failure to comply with data protection regulations (like GDPR, CCPA, or others), breach of contract obligations, and negligence leading to client damages.
Potential Financial Liabilities for Affected Parties
Affected parties, including Accenture clients, may suffer financial losses stemming from the attack. These losses could encompass lost revenue, remediation costs, and reputational damage. Client contracts may contain provisions that Artikel liability for data breaches, impacting the financial implications for both parties.
Possible Regulatory Actions Against Accenture and LockBit
Regulatory bodies, such as the FTC in the US or equivalent bodies in other countries, could initiate investigations into Accenture’s data security practices and the actions of LockBit. Findings of non-compliance could lead to significant fines and regulatory mandates for improved security. These regulatory actions might involve penalties for non-compliance with data security standards and mandatory changes to security protocols.
LockBit itself could face legal action for its illegal activities, potentially involving international cooperation to bring perpetrators to justice.
Steps Accenture Took to Secure Its Financial and Legal Interests
Accenture likely employed various measures to mitigate potential financial and legal liabilities. These measures likely included engaging legal counsel, conducting a thorough forensic investigation, implementing enhanced security protocols, and communicating with affected clients and stakeholders. Transparency and proactive communication are vital for managing reputational risks and establishing trust with clients and regulators.
Potential Financial Penalties for Data Breaches
| Regulatory Body | Potential Penalty (Example) | Basis of Penalty |
|---|---|---|
| FTC (USA) | Millions of dollars | Violation of data security standards, breach of contract |
| EU Data Protection Authorities | Significant fines, millions of euros | Violation of GDPR, non-compliance |
| State Attorneys General (USA) | Variable, based on severity | Violation of state data breach laws |
Note: These are illustrative examples and actual penalties can vary significantly depending on the specific circumstances of the breach and applicable regulations.
Public Response and Media Coverage: Lockbit Ransomware Attack On Accenture
The LockBit ransomware attack on Accenture sparked a significant public response, driving extensive media coverage and social media discussions. This reaction, both positive and negative, highlighted the impact of such attacks on public perception and corporate reputation. The swift and widespread dissemination of information, often through social media, played a crucial role in shaping public understanding and concern.The media response to the Accenture attack was multifaceted, ranging from detailed technical analyses to broader discussions on cybersecurity vulnerabilities and the effectiveness of ransomware mitigation strategies.
The recent LockBit ransomware attack on Accenture highlights the critical need for robust security measures. Companies need to proactively address vulnerabilities, and deploying AI code safety goggles, like those discussed in Deploying AI Code Safety Goggles Needed , can significantly help prevent similar incidents in the future. This proactive approach is crucial to safeguarding against sophisticated attacks like the one targeting Accenture.
Public statements from Accenture and law enforcement agencies further shaped the narrative. This public response provided a glimpse into the complexities of dealing with a major cyberattack in the digital age.
Public Response to the Accenture Attack
The public response to the Accenture attack was marked by a blend of concern, skepticism, and calls for stronger cybersecurity measures. Initial reactions focused on the potential disruption to Accenture’s operations and the broader implications for data security. Social media platforms became crucial hubs for information sharing, speculation, and discussion about the attack’s scope and potential impact.
Examples of Media Coverage and Public Statements
Numerous news outlets, both specialized cybersecurity publications and mainstream media, reported on the Accenture attack. These reports varied in their level of detail and analysis, but generally focused on the attack’s impact on Accenture’s operations, the nature of the LockBit ransomware, and the wider threat landscape. Public statements from Accenture, while acknowledging the incident, often emphasized their commitment to restoring services and maintaining business continuity.
Role of Social Media in Disseminating Information
Social media played a significant role in the dissemination of information regarding the Accenture attack. Initial reports and speculation quickly spread through various platforms, impacting public perception and creating a sense of urgency. The rapid sharing of information, often unverified or incomplete, highlighted the potential for misinformation to spread alongside factual reporting in a digital environment.
Impact of Public Perception on Accenture’s Reputation
The impact of the LockBit ransomware attack on Accenture’s reputation was undoubtedly negative. The public’s perception of a significant security breach, even if ultimately contained, can have long-term consequences for brand trust and customer confidence. The attack’s visibility and the potential for data compromise influenced public sentiment and could affect Accenture’s future business dealings.
Table: Public Reaction to Similar Ransomware Attacks
| Attack Target | Type of Ransomware | Public Reaction (General Sentiment) | Impact on Reputation |
|---|---|---|---|
| Company A | Ransomware X | Widespread concern, calls for stronger cybersecurity | Negative, loss of customer confidence |
| Company B | Ransomware Y | Mixed reaction, some skepticism about recovery | Moderate negative, some recovery in reputation |
| Accenture | LockBit | Significant concern, media scrutiny, social media discussion | Negative, potential long-term damage to reputation |
Note: This table provides a simplified overview and does not reflect the full complexity of public reactions to ransomware attacks. The impact on reputation can vary greatly based on factors like the attack’s scope, the company’s response, and the overall cybersecurity environment.
Detailed Account of Overall Media Coverage and Public Discussion
The media coverage of the Accenture attack followed a typical pattern for significant cyberattacks. Initial reports focused on the attack’s nature and impact, followed by discussions about the ransomware’s characteristics and the potential for wider repercussions. Public discussion centered on the efficacy of cybersecurity measures, the need for stronger regulations, and the vulnerability of large corporations to cyberattacks.
The attack highlighted the importance of rapid incident response, transparency, and robust cybersecurity protocols for organizations in the modern digital age.
Future Trends in Ransomware Attacks

The LockBit ransomware attack on Accenture, and similar incidents, underscore the ever-evolving nature of cyber threats. Ransomware is no longer a simple data-encrypting tactic; it’s a sophisticated, multifaceted attack aiming for maximum disruption and financial gain. Understanding future trends is crucial for proactive defense and mitigation strategies.The evolution of ransomware tactics and techniques is marked by a shift from basic encryption to sophisticated attack strategies targeting multiple vulnerabilities.
The recent LockBit ransomware attack on Accenture highlights the critical need for robust security measures. One potential weakness that could have contributed to the attack is the Azure Cosmos DB vulnerability, as detailed in Azure Cosmos DB Vulnerability Details. This underscores the importance of staying informed about potential security holes in cloud platforms to better protect against future ransomware attacks like the one Accenture suffered.
This includes exploiting vulnerabilities in software supply chains, cloud environments, and even the human element through social engineering. Moreover, the rise of ransomware-as-a-service (RaaS) models further democratizes these attacks, making them more accessible to less skilled actors.
Evolution of Ransomware Tactics and Techniques
Ransomware attacks are progressively becoming more targeted and sophisticated. The focus is moving beyond simple data encryption to include data exfiltration, double extortion, and supply chain attacks. Attackers are increasingly leveraging vulnerabilities in software supply chains, compromising multiple organizations through a single point of entry. Furthermore, sophisticated tactics like exploiting vulnerabilities in cloud environments are emerging, posing a considerable threat to organizations reliant on cloud services.
Emerging Trends in Ransomware Attacks
Several emerging trends highlight the escalating complexity of ransomware attacks. One is the use of ransomware-as-a-service (RaaS), which allows individuals or groups with limited technical skills to launch sophisticated attacks. Another emerging trend is the targeting of critical infrastructure, which can cause widespread disruption and damage to essential services. Finally, attacks are increasingly leveraging social engineering tactics to gain initial access to networks.
Factors Driving the Rise of Ransomware Attacks
Several factors contribute to the escalating prevalence of ransomware attacks. The increasing digitalization of businesses and critical infrastructure creates more entry points for attackers. Furthermore, the anonymity afforded by cryptocurrencies facilitates ransomware payments, making them more attractive to perpetrators. Finally, the lack of robust cybersecurity defenses in many organizations creates an environment ripe for exploitation.
Need for Continuous Security Updates and Vigilance
Continuous security updates and vigilance are essential for mitigating ransomware threats. Regular software patching, strong password policies, and employee training on cybersecurity awareness are critical. Moreover, organizations should invest in robust security information and event management (SIEM) systems to detect and respond to potential threats. Furthermore, adopting a proactive security posture, including threat intelligence gathering and incident response planning, is paramount.
How Companies Can Adapt to Future Ransomware Threats
Companies must adapt their security strategies to address the evolving nature of ransomware threats. This includes implementing multi-layered security defenses, including endpoint detection and response (EDR) solutions. Furthermore, organizations should prioritize the security of their software supply chains, ensuring thorough vetting and testing of third-party components. Also, companies should establish robust incident response plans to mitigate the impact of ransomware attacks.
Predicted Future Trends of Ransomware in the Next 5 Years
| Trend | Description | Impact |
|---|---|---|
| Increased Sophistication | Ransomware attacks will become more complex, incorporating advanced techniques like double extortion and supply chain attacks. | Higher financial and reputational damage, more difficulty in detection and response. |
| Targeting of Critical Infrastructure | Attacks will shift towards critical infrastructure sectors like energy, healthcare, and finance. | Potential for widespread disruption of essential services and significant societal impact. |
| Rise of Targeted Attacks | Ransomware groups will focus on specific organizations with valuable data or systems. | Higher financial demands, increased focus on targeted vulnerability exploitation. |
| Exploitation of Cloud Vulnerabilities | Cloud environments will become a new attack vector. | Increased complexity of defense, new challenges for cloud security. |
| Ransomware-as-a-Service (RaaS) Evolution | RaaS models will become more advanced, offering a broader range of tools and services. | Lower barrier to entry for attackers, wider range of targets. |
Last Point
The LockBit ransomware attack on Accenture serves as a stark reminder of the ever-evolving threat landscape in cybersecurity. The incident highlighted vulnerabilities in Accenture’s systems and processes, forcing a re-evaluation of security protocols and incident response strategies. Ultimately, the attack underscores the critical need for proactive security measures and a commitment to continuous improvement in the face of sophisticated cyber threats.
This event will undoubtedly shape future cybersecurity strategies for large corporations worldwide.
Answers to Common Questions
What were the reported financial losses due to the attack?
The precise financial impact of the attack on Accenture is still being assessed. However, significant losses are expected, encompassing not just the ransom payment (if any), but also operational downtime, legal fees, and reputational damage.
What are some preventative measures that could have been implemented to prevent the attack?
Implementing robust multi-factor authentication, regularly patching systems, and educating employees about phishing attempts are critical preventative measures. Strengthening security awareness training and improving incident response plans are also crucial steps.
What types of data were potentially compromised in the attack?
Specific details on the types of data compromised are often not released publicly during an investigation. However, it’s likely that sensitive data, including customer information, financial records, and intellectual property, was targeted.
What were the technical vulnerabilities exploited by LockBit?
The exact technical vulnerabilities are not always disclosed immediately after such incidents. However, it’s often related to known vulnerabilities or weak security configurations, including outdated software or insufficient access controls.