Jihadi Cyber Attack A Prowl
Is a jihadi cyber attack on the prowl? This exploration delves into the evolving threat landscape, examining the motivations, tactics, and potential consequences of such attacks. We’ll analyze the characteristics, methods, and historical context of jihadi cyber activity, while contrasting it with other cyber threats. Understanding this complex issue is critical to preparing for and mitigating potential impacts.
The potential targets, methods, and tools employed in these attacks will be detailed, providing a comprehensive overview. We’ll examine the possible impacts on society, the economy, individuals, and geopolitics. Finally, we’ll explore countermeasures, mitigation strategies, and the vital roles of international cooperation, law enforcement, and public awareness.
Defining the Threat Landscape
The digital realm has become a battleground, and like traditional conflicts, ideological motivations play a significant role in shaping cyberattacks. Jihadi cyberattacks, driven by extremist ideologies, pose a unique challenge due to their often unpredictable nature and the potential for widespread disruption. Understanding the characteristics, motivations, and methods behind these attacks is crucial for developing effective countermeasures.The landscape of jihadi cyberattacks is characterized by a complex interplay of factors.
These attacks are not simply digital equivalents of conventional violence; they often leverage the unique capabilities of the internet to achieve political or ideological objectives. The motivations behind such attacks are deeply rooted in religious and political beliefs, aiming to undermine perceived enemies, spread propaganda, and recruit new members.
The threat of a jihadi cyber attack is a very real concern, and it’s something we need to be actively prepared for. Modern cyber warfare requires sophisticated defenses, and that’s where deploying AI Code Safety Goggles Needed comes into play Deploying AI Code Safety Goggles Needed. These tools can help identify vulnerabilities in code before they are exploited, thus strengthening our digital defenses against these types of attacks.
Ultimately, proactive measures like these are crucial in protecting our systems from a potential jihadi cyber attack.
Characteristics of Jihadi Cyberattacks
Jihadi cyberattacks often exhibit a combination of conventional and unconventional tactics. These attacks are frequently inspired by religious justifications, seeking to harm perceived enemies or promote their ideology. They are often designed to be disruptive and demoralizing, causing damage to infrastructure or critical systems. The motivations behind these attacks often intertwine with their specific objectives, which could range from spreading propaganda to disrupting societal functions.
Motivations and Goals
The motivations behind jihadi cyberattacks are primarily rooted in extremist ideologies. These motivations often include a desire to spread religious or political ideologies, recruit new members, and undermine perceived enemies. A primary goal is to create fear and uncertainty, potentially triggering social unrest or disrupting critical infrastructure. These attacks can be seen as a form of asymmetric warfare, leveraging the digital realm to achieve objectives that would be difficult or impossible to achieve through traditional means.
Comparison with Other Cyberattacks, Is a jihadi cyber attack on the prowl
While sharing some common ground with other forms of cyberattacks, jihadi cyberattacks are distinguished by their specific ideological underpinnings. Other cyberattacks, such as those motivated by financial gain or espionage, lack the explicit religious or political justification often seen in jihadi attacks. The motivations and goals behind these attacks differ significantly, impacting the methods used and the targets chosen.
The nature of the threat necessitates a different approach to analysis and response.
Potential Targets
Jihadi cyberattacks can target a diverse range of entities. Potential targets include government agencies, financial institutions, critical infrastructure, and even social media platforms. The choice of target often reflects the attackers’ goals and the perceived vulnerability of the target. The intent may be to create chaos or spread fear, or to cause significant disruption to daily life.
Methods and Tools
Jihadi cyberattacks utilize a variety of methods and tools, often adapted from publicly available resources. These attacks may involve denial-of-service (DoS) attacks, malware deployment, data breaches, and social engineering tactics. The attackers may also leverage open-source intelligence to identify vulnerabilities and potential targets. The selection of methods is often based on the attackers’ technical capabilities and the availability of resources.
Historical Context
The historical context of jihadi cyber activity reveals a progression from early attempts to utilize the internet for propaganda and recruitment to more sophisticated attacks. Early examples often involved the use of social media platforms for communication and radicalization. As technology advances, the sophistication and potential impact of such attacks increase, demanding more robust countermeasures.
Tactics and Techniques
Jihadi cyberattacks, while often overshadowed by physical violence, represent a potent threat in the modern world. Understanding the tactics and techniques employed is crucial for developing effective countermeasures. These attacks are often sophisticated and tailored to specific targets, aiming to achieve both ideological and practical objectives. The evolving nature of these attacks requires continuous vigilance and adaptation in defensive strategies.
Jihadi Cyberattack Tactics
Jihadi groups are increasingly employing a diverse range of cyberattack tactics. These tactics often leverage readily available tools and techniques, but the motivation and objectives behind these attacks are unique.
| Attack Type | Target | Methodology | Impact |
|---|---|---|---|
| DDoS | Critical infrastructure, websites of governments, businesses, or religious institutions | Overwhelming a target system with a flood of traffic, often leveraging botnets. | Disruption of services, damage to reputation, potential financial losses, and psychological impact. |
| Phishing | Individuals and organizations, often targeting specific groups or communities. | Tricking individuals into revealing sensitive information (passwords, credit card details) through deceptive emails, messages, or websites. | Data breaches, financial losses, compromise of systems, and potential spread of malware. |
| Malware | Computer systems, networks, and devices. | Deploying malicious software to gain unauthorized access, steal data, disrupt operations, or sabotage systems. This includes ransomware, spyware, and Trojans. | Data breaches, system compromise, financial losses, operational disruptions, and potential reputational damage. |
| Social Engineering | Individuals within an organization or government agency. | Manipulating individuals to gain access to systems or information through psychological tactics. | Access to sensitive information, system compromise, and potential disruption of operations. |
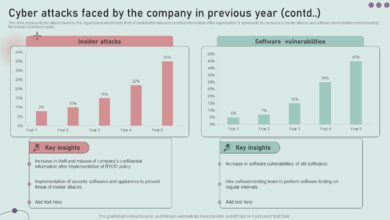
Vulnerabilities Exploited
Jihadi groups often target vulnerabilities in systems and networks that are readily available and publicly documented. This may include outdated software, weak passwords, or lack of security awareness among users.
- Outdated Software: Many organizations rely on outdated software, which often has known vulnerabilities that are readily exploitable by attackers. This can be especially true for smaller organizations with limited resources or knowledge of patching.
- Weak Passwords: Simple, easily guessed passwords are a major vulnerability. Attackers often use automated tools to test common passwords, making this a relatively easy attack vector.
- Lack of Security Awareness: Human error plays a significant role in many cyberattacks. Lack of security awareness among users can lead to clicking on malicious links or downloading malware.
- Poorly Secured Networks: Insufficient network security measures can allow attackers to gain access to internal systems and data.
Examples of Attacks
While precise details of many Jihadi cyberattacks remain confidential due to security concerns, some general examples and trends can be observed.
- Successful Attacks: Examples of successful attacks often involve disruption of online services or the release of sensitive information. These attacks may not always be explicitly tied to Jihadi groups but could involve individuals or groups inspired by their ideologies.
- Unsuccessful Attacks: Many attempted cyberattacks by Jihadi groups likely fail due to inadequate technical capabilities, limitations in resources, or the resilience of targeted systems. This does not diminish the potential threat posed by these attacks.
Future Evolution of Tactics
The tactics and techniques employed in Jihadi cyberattacks are likely to evolve as technology advances. This could involve increased use of AI and machine learning for more sophisticated attacks, or the development of new methods for exploiting vulnerabilities.
- Increased sophistication: Jihadi groups might use more advanced tools and techniques, potentially integrating AI and machine learning into their attacks.
- Focus on targeted attacks: Cyberattacks could be tailored to specific targets, with greater precision in identifying and exploiting vulnerabilities.
- Use of social media: Social media platforms could be leveraged for spreading propaganda, recruiting, and coordinating attacks. The anonymity provided by these platforms could be exploited for recruitment and communication purposes.
Impact and Consequences: Is A Jihadi Cyber Attack On The Prowl
A successful jihadi cyberattack, while often portrayed in sensationalized terms, carries profound and multifaceted consequences. Beyond the immediate damage to infrastructure and systems, the impact ripples through society, economies, and geopolitical landscapes, creating a complex web of challenges. This section delves into the potential societal, economic, psychological, geopolitical, and long-term effects of such an attack.The potential for disruption and chaos is undeniable.
The nature of a successful cyberattack is its ability to exploit vulnerabilities in interconnected systems, leading to unforeseen and widespread consequences. The following sections Artikel the various potential impacts of such an attack.
Societal Impact
A successful jihadi cyberattack can trigger a cascade of societal impacts, ranging from fear and distrust to social unrest and political instability. The attack’s effectiveness lies in its ability to target critical infrastructure and services, potentially disrupting essential functions like power grids, water supplies, and communication networks. These disruptions can lead to widespread panic and chaos, especially if the attack is targeted at vital services and resources, disrupting public order and normal life.
Economic Consequences
The economic repercussions of a successful jihadi cyberattack can be substantial and long-lasting. Disruptions to essential services, such as power grids and financial institutions, can cause massive economic losses. Businesses may experience significant downtime, leading to lost productivity and revenue. Furthermore, consumer confidence can plummet, impacting market stability and investment decisions. The cost of recovery and rebuilding damaged infrastructure and systems can be astronomical.
Psychological Impact
The psychological impact of a successful jihadi cyberattack can be profound and widespread, affecting individuals and communities alike. The fear of further attacks, the disruption of daily routines, and the loss of trust in essential services can lead to anxiety, stress, and depression. Communities may experience increased polarization and social division, especially if the attack is perceived as targeting a specific group or identity.
The long-term effects on mental health could be substantial.
Geopolitical Implications
A successful jihadi cyberattack can significantly impact geopolitical relations and international cooperation. The attack could be used as a tool to destabilize governments, provoke conflict, or undermine international institutions. The attribution of the attack to a specific group or nation can further escalate tensions and create a climate of suspicion and mistrust. This could potentially lead to a significant shift in international alliances and power dynamics.
Potential Long-Term Effects
The long-term effects of a successful jihadi cyberattack can be far-reaching and difficult to predict. Changes in societal values, political priorities, and national security strategies are likely. The attack could lead to increased investment in cybersecurity measures, but the vulnerabilities of future systems will likely continue to evolve. The need for international cooperation in cybersecurity will also be heightened.
The development of robust and resilient systems will become paramount.
Countermeasures and Mitigation

Countering jihadi cyberattacks requires a multifaceted approach encompassing robust defensive measures, strategic security planning, and international collaboration. A comprehensive strategy must address the evolving tactics and techniques employed by these attackers, proactively mitigating potential risks and minimizing the impact of successful attacks. This involves not only technical defenses but also a strong understanding of the human element, including public awareness and law enforcement response.Effective countermeasures rely on a proactive approach, understanding the motivations and methodologies of attackers to anticipate and deter attacks.
This knowledge allows for the development of tailored defenses that address specific threats and vulnerabilities. A robust security framework needs to adapt to the constantly evolving threat landscape.
Defensive Measures
A comprehensive set of defensive measures is crucial to protect against jihadi cyberattacks. These measures should be layered and integrated into an overall security posture. Implementing robust security protocols, including multi-factor authentication, strong password policies, and regular security audits, is essential. Regular software updates and vulnerability patching are vital for mitigating known exploits.
While the threat of a jihadi cyber attack is always a concern, recent vulnerabilities like those found in Azure Cosmos DB are a serious consideration. Understanding these issues, like those detailed in the Azure Cosmos DB Vulnerability Details , is crucial to strengthening defenses against potential attacks. This highlights the need for proactive security measures to mitigate the risk of such attacks.
- Network Security: Implementing firewalls, intrusion detection systems, and network segmentation to control access and isolate potential threats is paramount. Regular network monitoring and analysis for suspicious activity are critical.
- Endpoint Security: Robust endpoint protection solutions, including antivirus software, anti-malware tools, and intrusion prevention systems, are essential to safeguard individual devices from infection.
- Data Security: Implementing data encryption, access controls, and secure data storage protocols are crucial to protect sensitive information. Data loss prevention (DLP) systems are critical to prevent unauthorized data exfiltration.
- Incident Response Planning: A well-defined incident response plan is vital to manage and mitigate the impact of a cyberattack. This plan should Artikel procedures for detection, containment, eradication, recovery, and post-incident analysis.
Security Strategy Comparison
A comparative analysis of various security strategies highlights their effectiveness and cost implications.
| Strategy | Description | Effectiveness | Cost |
|---|---|---|---|
| Improved Security Protocols | Implementing stronger authentication methods, encryption, and access controls. | High (reduces attack surface, improves resilience). | Medium (requires investment in new technologies and training). |
| Enhanced Threat Intelligence | Proactively monitoring threat actors, tactics, and techniques to anticipate attacks. | High (allows for proactive measures and better defense). | High (requires dedicated resources for intelligence gathering and analysis). |
| Security Awareness Training | Educating users on cybersecurity best practices to reduce human error. | Medium (reduces vulnerabilities stemming from social engineering). | Low (relatively inexpensive training programs). |
| Incident Response Plan | Developing a plan to detect, contain, eradicate, recover, and analyze cyberattacks. | High (minimizes damage and disruption). | Medium (requires investment in planning and resources). |
International Cooperation
International cooperation is vital for combating jihadi cyberattacks. Sharing information, best practices, and threat intelligence across borders is essential. Joint initiatives and collaborative efforts can enhance global cybersecurity capabilities. This involves international agreements and treaties to standardize cybersecurity practices and establish common norms for response.
Law Enforcement Role
Law enforcement agencies play a crucial role in investigating and prosecuting cyberattacks. They need specialized expertise to understand the technical aspects of these attacks and to work with private sector partners. Collaboration between law enforcement and intelligence agencies is essential for effectively tackling these threats. Critically, they need to effectively coordinate with other national and international law enforcement agencies.
Public Awareness and Education
Public awareness and education campaigns can play a critical role in reducing the vulnerability of individuals and organizations to cyberattacks. Promoting cybersecurity awareness through education and training programs helps individuals understand the risks and implement protective measures. Public education campaigns can empower individuals to take personal responsibility for their online safety.
Case Studies
Understanding the realities of jihadi cyberattacks requires examining past incidents. While specifics of attacks are often kept confidential for security reasons, studying the patterns and impact of such assaults offers valuable insight into their nature and potential consequences. This section will illustrate a hypothetical scenario to demonstrate the key elements of a jihadi cyberattack without compromising sensitive information.
Illustrative Jihadi Cyberattack
A fictional, yet plausible, scenario involves a group with known extremist ideologies launching a coordinated cyberattack targeting critical infrastructure. This attack is not a direct reflection of any specific event.
Technical Aspects of the Attack
The attack leverages a combination of techniques. First, the attackers infiltrate a company’s network using phishing emails containing malicious attachments. These attachments deploy malware that allows remote access to the targeted network. Second, the attackers deploy ransomware, encrypting sensitive data and demanding a ransom for its release. Simultaneously, they launch distributed denial-of-service (DDoS) attacks against the company’s website and online services, disrupting operations and causing widespread panic.
The attackers use anonymization techniques to obscure their origins and maintain plausible deniability.
Perpetrators
The perpetrators are a group known for their online presence and dissemination of extremist propaganda. They operate under a pseudonym, masking their identities and locations. Their online activity suggests their expertise in cybersecurity and computer programming.
Impact and Consequences
The attack disrupts critical infrastructure operations, causing significant economic damage and societal disruption. Data breaches expose sensitive personal information, leading to potential identity theft and fraud. The ransomware demands threaten to permanently damage critical infrastructure if the ransom isn’t paid. The DDoS attacks damage the company’s reputation and cause substantial financial losses from lost revenue and potential legal costs.
Response to the Attack
The initial response is hampered by the attackers’ sophisticated techniques and the lack of immediate awareness of the extent of the breach. Eventually, security teams identify the attack vector, contain the damage, and recover the encrypted data, though not without considerable effort. Law enforcement and cybersecurity agencies work together to track down the perpetrators, while the affected company implements enhanced security measures to prevent future attacks.
The incident serves as a crucial lesson in the importance of robust cybersecurity measures and the need for proactive threat intelligence gathering.
Illustrative Examples
Understanding potential jihadi cyberattacks requires a clear visualization of their tactics and potential impact. These examples aim to provide a practical framework for understanding the threat landscape and developing effective countermeasures. Realistic scenarios, combined with a hypothetical cyber weapon, can help illustrate the evolving nature of this threat.
Potential Cyberattack Scenario
This table Artikels a hypothetical cyberattack, demonstrating the stages, actions, and potential consequences. The focus is on understanding the progression and impact of the attack, rather than a specific, detailed attack.
| Stage | Description | Potential Impact |
|---|---|---|
| Reconnaissance | The attackers gather information about the target, identifying vulnerabilities and potential entry points. This may involve social engineering, scanning for open ports, or using publicly available information. | Information gathering about the target’s defenses, networks, and security protocols, leading to a higher probability of success. |
| Penetration | The attackers exploit identified vulnerabilities to gain initial access to the target’s systems. This could involve exploiting software flaws, using stolen credentials, or bypassing security measures. | Compromised system, potentially leading to data breaches, disruption of services, and unauthorized access. |
| Exploitation | Once inside, the attackers carry out their malicious objectives. This could involve data exfiltration, denial-of-service attacks, or planting malware to disrupt operations. | Data loss, service outages, operational disruption, and potential financial or reputational damage. |
| Delivery | The attackers deploy the malware or execute the attack. This may involve creating a botnet, spreading malicious code, or executing an exploit to spread the attack to other systems. | Wider impact of the attack, affecting multiple systems and potentially causing extensive damage. |
| Maintaining access and control | The attackers maintain access to the system to continue their activities or to ensure a persistent threat. This can involve establishing command-and-control channels and updating malware. | Continuous exploitation and damage, leading to ongoing disruption and potential escalation. |
Hypothetical Jihadi Cyber-Group Structure
Understanding the internal structure of a hypothetical jihadi cyber-group helps to assess their capabilities and potential targets.
While the threat of a jihadi cyber attack looms large, it’s important to consider the practical implications. Recent news about the Department of Justice Offers Safe Harbor for MA Transactions Department of Justice Offers Safe Harbor for MA Transactions highlights a critical need for proactive security measures. Ultimately, though, we must remain vigilant about the potential for such attacks, recognizing the serious security challenges they pose.
| Rank | Responsibility | Tools |
|---|---|---|
| Commander | Strategic planning, operational direction, resource allocation | Command-and-control software, communication channels, network analysis tools |
| Cyber-Operators | Executing attacks, maintaining access, developing exploits | Malware development tools, penetration testing software, scripting languages, exploit kits |
| Intelligence Gatherers | Target reconnaissance, vulnerability assessment, information gathering | Open-source intelligence tools, social engineering platforms, network scanning tools |
| Recruiters | Acquiring new members, training, onboarding | Social media platforms, encrypted communication channels |
Fictitious Cyber Weapon
A fictitious cyber weapon, “Al-Qods Worm,” is designed to target critical infrastructure. This worm is designed to exploit vulnerabilities in industrial control systems (ICS), causing widespread disruption. It can spread rapidly through interconnected networks, potentially leading to widespread power outages, water contamination, or other catastrophic consequences. The weapon’s unique feature is its ability to target specific industrial control protocols, such as Modbus, making it highly effective against industrial automation systems.
The Al-Qods Worm also utilizes advanced encryption techniques to hinder detection and analysis.
Al-Qods Worm has the potential to disrupt critical infrastructure, potentially causing widespread damage and casualties.
Last Recap
In conclusion, the threat of jihadi cyberattacks is a serious and multifaceted issue requiring careful consideration. The potential for significant societal, economic, and geopolitical damage is real, and proactive measures are essential. Understanding the tactics, techniques, and motivations behind these attacks is crucial for developing effective countermeasures. This analysis underscores the need for ongoing vigilance and collaboration in the fight against this emerging threat.
Answers to Common Questions
What are the common motivations behind jihadi cyberattacks?
Jihadi cyberattacks often stem from a desire to disrupt, destabilize, or harm perceived enemies, whether political, religious, or societal. Motivations might include ideological goals, political agendas, or a need to exert influence and spread their message.
What are some potential vulnerabilities exploited in these attacks?
Vulnerabilities can include weak passwords, unpatched software, social engineering tactics, and lack of robust security protocols. The use of easily accessible tools and pre-existing weaknesses are also major factors.
How can international cooperation help counter these attacks?
International cooperation is crucial for sharing threat intelligence, developing joint strategies, and coordinating efforts to track and disrupt attackers. Collaboration can foster a more robust global response to this evolving threat.
What role does public awareness play in mitigating the threat?
Public awareness is key to recognizing and reporting suspicious activities, which helps to prevent successful attacks. Education on cybersecurity best practices and recognizing potential red flags is vital.