Iranian Hackers Target Western Data
Iranian hackers to launch data destroying malware on western countries. This escalating cyber threat poses a significant risk to critical infrastructure and financial systems across the West. We’ll explore the potential methods, targets, and impacts of these attacks, alongside defensive strategies and international implications. Get ready to delve into the world of state-sponsored cyber warfare and the potential for devastating consequences.
This analysis will examine the historical context of Iranian cyber capabilities, outlining past attacks and highlighting potential motivations. We’ll also investigate the specific techniques employed for data destruction, including malware types and data exfiltration methods. Understanding these tactics is crucial for comprehending the scale of the potential threat.
Background on Iranian Cyber Capabilities

Iranian cyber capabilities have evolved significantly over the past two decades, transitioning from rudimentary attacks to sophisticated operations capable of targeting critical infrastructure and sensitive data. This evolution reflects a combination of factors, including access to advanced technologies, dedicated resources, and a growing pool of skilled personnel. The motivations behind these activities are multifaceted, often tied to geopolitical tensions and perceived threats from Western nations.The Iranian government’s involvement in cyber activities is a complex issue with various layers.
Understanding the background of these activities is essential to assessing the potential risks and consequences. The historical context of Iranian cyber operations provides valuable insights into their tactics, techniques, and procedures.
Historical Overview of Iranian Cyber Activities
Iranian cyber activities have spanned various targets, including financial institutions, government agencies, and critical infrastructure. Early operations often involved simple denial-of-service attacks and data breaches, but over time, they have progressed to more complex and sophisticated tactics. Notable incidents, while sometimes difficult to definitively attribute, point to a growing capability and strategic intent. The evolution of these activities highlights the need for constant vigilance and adaptation in cybersecurity measures.
Tactics, Techniques, and Procedures (TTPs)
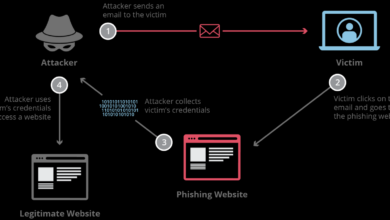
Iranian actors have demonstrated a proficiency in a range of cyberattack methods. Their arsenal includes malware development, phishing campaigns, and social engineering techniques. These attacks often target vulnerabilities in software and networks to gain unauthorized access. The sophisticated development and deployment of their malware have become a significant concern for Western cybersecurity professionals.
Resources and Infrastructure
Iranian cyber actors likely have access to various resources and infrastructure to support their operations. This includes dedicated servers, advanced computing capabilities, and potentially government-sponsored research and development initiatives. The extent of their resources and the specifics of their infrastructure remain largely opaque, making precise assessment challenging.
Cyberattacks Targeting Western Countries
Numerous reported incidents suggest Iranian actors have targeted Western countries. These attacks have ranged from espionage operations to attempts to disrupt critical infrastructure. The motivations behind these actions are likely varied, including political retribution, economic disruption, and intelligence gathering. However, specific examples and details of attacks are often limited due to the nature of such operations.
Motivations Behind Iranian Cyberattacks
The motivations behind Iranian cyberattacks against Western countries are complex and multifaceted. These range from retaliatory measures for perceived Western actions in the Middle East to efforts to gain intelligence and disrupt the West’s technological superiority. Economic motivations also play a significant role, with cyberattacks sometimes aimed at disrupting Western financial interests.
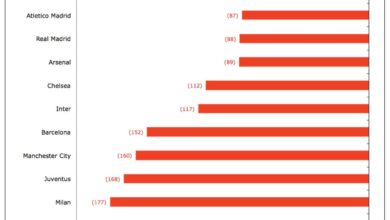
Comparison of Iranian Cyber Capabilities
| Feature | Iran | Other Nation-State Actors (e.g., Russia, China) |
|---|---|---|
| Malware Development | Demonstrating increasing sophistication, particularly in targeting specific vulnerabilities. | Known for diverse malware types and advanced capabilities, including zero-day exploits. |
| Infrastructure | Potentially leveraging a mix of government-sponsored resources and private sector capabilities. | Often employing extensive state-sponsored infrastructure and resources. |
| Intelligence Gathering | Focusing on acquiring sensitive information related to Western technology and military operations. | Primarily focused on intelligence gathering, but motivations and targets vary. |
| Targeting | Targeting critical infrastructure, financial institutions, and government agencies. | Targeting critical infrastructure, financial institutions, and government agencies, often with greater scale and complexity. |
This table offers a comparative overview of the capabilities of Iranian cyber actors relative to other nation-state actors. Note that precise quantitative comparisons are difficult due to the clandestine nature of these activities. The information presented in the table provides a high-level overview.
Methods of Data Destruction
Iranian cyber actors possess a range of sophisticated capabilities, including the development and deployment of malware designed for data destruction. Understanding the methods employed by these actors is crucial for bolstering defenses against such attacks. This analysis explores the various techniques used for data destruction, examining the vulnerabilities in western digital infrastructure and providing examples of real-world attacks.Data destruction is a primary objective for many state-sponsored cyberattacks.
The motivation ranges from crippling critical infrastructure to erasing evidence of malicious activity. The methods used are often complex, employing multiple layers of obfuscation and evasion techniques.
Common Malware Types Used for Data Destruction
Data destruction malware often employs a variety of malicious code types. These are not always easily distinguishable from other types of malware, requiring advanced analysis techniques. Common types include ransomware, wiper malware, and rootkits. Ransomware encrypts data, demanding payment for its release, but wiper malware is designed to irreversibly delete data, while rootkits provide covert access for malicious activities.
Techniques for Encrypting, Deleting, or Corrupting Data
Data destruction techniques vary in their complexity and sophistication. Some techniques focus on encrypting data, making it inaccessible without a decryption key. Others directly delete data from storage devices or corrupt files, rendering them unusable.
- Encryption: Encryption techniques involve transforming data into an unreadable format. Advanced encryption algorithms, like AES-256, can be employed to make data recovery extremely difficult. This is a common tactic in ransomware attacks, where victim’s data is encrypted until a ransom is paid.
- Data Deletion: Direct deletion of data is a more straightforward method. This often involves overwriting data sectors multiple times with random patterns. Sophisticated malware may utilize specialized techniques to bypass standard data recovery procedures. The effectiveness depends on the quality of the overwriting and the potential for forensic recovery.
- Data Corruption: Corrupting data involves altering file structures or metadata, making the data unusable or inaccessible. This can involve manipulating file headers, altering checksums, or introducing inconsistencies in file structures. This technique might be less devastating than direct deletion but can still cripple systems and disrupt operations.
Comparison of Data Exfiltration and Destruction
Data exfiltration focuses on extracting data from a target system, often for intelligence gathering or financial gain. Data destruction, on the other hand, aims to render the data unusable or unrecoverable. While both can cripple operations, data destruction is more focused on the irreversible loss of information. Methods for exfiltration often overlap with those used for data destruction, particularly in the use of covert channels and tools to bypass security measures.
Vulnerabilities in Western Digital Infrastructure
Western digital infrastructure often relies on outdated systems and configurations, which can create vulnerabilities. These vulnerabilities may include unpatched software, weak passwords, inadequate security protocols, and a lack of comprehensive security awareness training. The complexity and interconnectedness of modern infrastructure create potential entry points for cyberattacks.
Real-World Data Destruction Attacks and Impacts
Numerous attacks have demonstrated the potential for data destruction. In some cases, attackers have targeted critical infrastructure, disrupting services and causing significant financial losses. For example, attacks targeting financial institutions can result in substantial financial losses and reputational damage. Attacks on healthcare organizations can have catastrophic implications, compromising patient records and disrupting medical operations.
Malware Types and Destructive Capabilities
| Malware Type | Destructive Capability | Example |
|---|---|---|
| Ransomware | Encrypts data, demanding payment for decryption. | WannaCry, Maze |
| Wiper Malware | Irreversibly deletes data. | NotPetya, Industroyer |
| Rootkit | Provides covert access for malicious activities. | Various targeted attacks |
Targets and Potential Impacts: Iranian Hackers To Launch Data Destroying Malware On Western Countries
The potential for Iranian-backed cyberattacks targeting Western nations is a serious concern, particularly given the increasing sophistication of their capabilities and the demonstrated willingness to inflict significant damage. The choice of targets reflects a calculated strategy to maximize disruption and impact, with a clear understanding of vulnerabilities across various sectors. This analysis will explore the likely targets, the potential repercussions, and the intricate web of cascading failures that could emerge from such attacks.
Likely Targets within Western Countries
Western nations boast intricate interconnected systems, making them vulnerable to cascading failures if critical infrastructure is compromised. This interconnectedness is a double-edged sword, allowing for rapid response and efficient operation, but also amplifying the impact of any disruption. Financial institutions, government agencies, and energy providers are prime targets due to their central roles in the economic and social fabric of Western societies.
Attacks targeting these sectors can have devastating consequences.
Potential Economic Repercussions
Disruptions to critical infrastructure, such as power grids or water treatment facilities, could cripple entire regions. The economic fallout from such widespread disruptions would be substantial. Financial institutions are also attractive targets, as attacks could trigger widespread panic and destabilize financial markets. The 2017 NotPetya attack, which impacted global supply chains, serves as a stark reminder of the potential for widespread economic damage.
A similar attack could lead to massive supply chain disruptions, impacting manufacturing, transportation, and retail. The potential for data breaches and the subsequent release of sensitive information can cause further economic harm.
Potential Social Repercussions
Disruptions to essential services, like healthcare or transportation, would have significant social repercussions. Loss of access to essential resources could lead to widespread panic and social unrest. The potential for widespread social disruption is real, especially in the face of misinformation and panic that could spread rapidly in a crisis situation. Consider the psychological impact of widespread outages, impacting public trust in institutions and potentially leading to societal instability.
Potential Political Repercussions
Cyberattacks can significantly impact the political landscape. Disruptions to government agencies and sensitive information breaches could erode public trust and potentially undermine the legitimacy of elected officials. Such attacks could also be used to manipulate public opinion or to sow discord between different groups within a society. The potential for cyberattacks to influence elections or to interfere with democratic processes is a growing concern.
Cascading Failures and Supply Chains
The interconnected nature of modern economies makes them susceptible to cascading failures. A cyberattack on one sector can quickly ripple through related industries. For instance, an attack on a financial institution could trigger a wider financial crisis. Attacks on energy providers could lead to disruptions in transportation and manufacturing. The reliance on global supply chains makes them particularly vulnerable to disruptions.
A targeted attack on a key component of a global supply chain could cripple multiple industries simultaneously.
Data Breaches and Release of Sensitive Information
Breaches of government and corporate databases could expose sensitive personal information, leading to identity theft, financial fraud, and reputational damage. Release of classified government documents could have serious national security implications. Companies could suffer significant financial losses if sensitive customer data is exposed. The release of trade secrets could damage a company’s competitive position.
Potential Targets and Vulnerabilities
| Target | Potential Vulnerabilities |
|---|---|
| Critical Infrastructure (Power Grids) | Outdated systems, lack of security protocols, remote access vulnerabilities. |
| Financial Institutions | Phishing campaigns, malware targeting financial transactions, weak authentication protocols. |
| Government Agencies | Compromised personnel, weak password policies, outdated software. |
| Healthcare Providers | Vulnerable medical devices, lack of security training for staff, inadequate data encryption. |
| Transportation Networks | Remote access points to control systems, outdated software, lack of security patches. |
Defense Mechanisms and Mitigation Strategies
The escalating threat of data-destruction malware, particularly from state-sponsored actors like Iranian hackers, necessitates robust defense mechanisms. Proactive security measures, coupled with well-defined incident response plans, are crucial in mitigating the potential damage. International cooperation plays a vital role in sharing threat intelligence and best practices to counter these sophisticated attacks.Effective defense against sophisticated cyberattacks requires a multi-layered approach encompassing technological solutions, procedural safeguards, and international collaboration.
This involves a comprehensive strategy to protect systems and data from various attack vectors, including those designed for data destruction.
Existing Cybersecurity Measures
Existing cybersecurity measures encompass a wide range of technologies and protocols. Firewalls, intrusion detection systems (IDS), and antivirus software are fundamental components of any robust defense system. Regular security audits, vulnerability assessments, and penetration testing are critical for identifying and patching potential weaknesses in systems. These measures help detect and mitigate vulnerabilities before they are exploited by malicious actors.
Defensive Strategies
Defensive strategies include implementing intrusion detection systems (IDS) that monitor network traffic for suspicious patterns. IDS alerts security personnel to potential intrusions, allowing for timely intervention. Robust data backup and recovery plans are essential to ensure business continuity in the event of a successful attack. Regular backups, stored securely offsite, can restore critical data and systems. Regular security awareness training for personnel is also critical to prevent social engineering attacks.
Importance of Proactive Security Measures
Proactive security measures are essential for preventing cyberattacks. These measures include implementing strong access controls, regularly updating software and operating systems, and employing multi-factor authentication. Regular security audits, vulnerability assessments, and penetration testing are critical for identifying potential weaknesses and improving security posture.
Word is that Iranian hackers are planning to unleash data-destroying malware on Western countries. This is a serious threat, and it highlights the urgent need for better cybersecurity measures. Protecting sensitive data requires proactive strategies, like deploying AI code safety goggles to catch malicious code before it’s released into the wild, as discussed in Deploying AI Code Safety Goggles Needed.
Ultimately, these sophisticated attacks underscore the importance of continuous vigilance and robust defense mechanisms to counter these threats.
Incident Response Planning
Comprehensive incident response planning is vital for managing cyberattacks effectively. This includes establishing clear roles and responsibilities, developing procedures for containment, eradication, and recovery, and establishing communication channels for rapid response. Incident response plans should also Artikel procedures for reporting and coordinating with law enforcement and relevant agencies.
Role of International Cooperation, Iranian hackers to launch data destroying malware on western countries
International cooperation is crucial in countering sophisticated cyberattacks. Sharing threat intelligence, best practices, and information about emerging attack vectors among nations can significantly enhance global cybersecurity. Collaboration fosters a more coordinated and effective response to cyber threats. Joint training exercises and information exchanges between cybersecurity agencies can strengthen mutual support and coordination.
Creating Secure Systems
Creating secure systems that resist malware requires a multi-faceted approach. Employing strong encryption protocols, implementing least privilege access controls, and regularly patching vulnerabilities are fundamental to a robust defense. Regular security assessments and penetration testing are crucial to identify potential weaknesses in systems. Regular updates and maintenance of security software are also critical for staying ahead of emerging threats.
Preventive Measures
- Strong Password Policies: Implementing strong password policies that require complex passwords, regular changes, and multi-factor authentication is essential to protect against unauthorized access.
- Regular Software Updates: Keeping software and operating systems updated with the latest security patches mitigates known vulnerabilities and improves overall security.
- Network Segmentation: Segmenting networks isolates sensitive data and systems, limiting the impact of a breach to a smaller portion of the network.
- Data Encryption: Encrypting sensitive data both in transit and at rest protects data from unauthorized access and theft.
- Regular Security Awareness Training: Training personnel on phishing, social engineering, and other common attack vectors can significantly reduce the risk of successful attacks.
- Robust Backup and Recovery Plans: Implementing comprehensive backup and recovery plans ensures data and system restoration in the event of an attack or other disruption.
Illustrative Scenarios of Data Destruction
Iranian cyber actors, possessing advanced capabilities, pose a significant threat to Western critical infrastructure. Their potential for data destruction, leveraging sophisticated malware, necessitates a comprehensive understanding of potential scenarios and mitigation strategies. This section details a possible attack scenario, examining the stages of an operation, the damage caused, and potential countermeasures.
Scenario: Targeting a Western Country’s Power Grid
“A coordinated cyberattack targeting a Western country’s power grid, designed to disrupt critical infrastructure and cause widespread damage, represents a grave threat.”
The scenario involves Iranian hackers targeting the Supervisory Control and Data Acquisition (SCADA) system of a major power grid.
Initial Reconnaissance and Targeting
The initial phase involves extensive reconnaissance, meticulously mapping the power grid’s network topology, identifying vulnerabilities, and establishing access points. This stage often leverages publicly available information, social engineering, and exploiting known software flaws within the grid’s systems. Attackers may use spear-phishing emails to gain initial access, or exploit vulnerabilities in older, less-secure systems.
Malware Deployment and Propagation
Following reconnaissance, sophisticated malware is deployed. This malware is designed to disrupt communication channels, corrupt data, and disable critical functions within the SCADA system. The malware could be tailored to specifically target programmable logic controllers (PLCs), essential for grid operation. The propagation of the malware through the grid’s network is crucial to maximize disruption.
Data Destruction and Disruption
The malware proceeds to systematically destroy critical data, rendering the power grid dysfunctional. This includes corrupting or deleting control system configuration files, manipulating operational parameters, and ultimately leading to widespread power outages. The attackers might use ransomware techniques to further disrupt operations, demanding payment for the restoration of service. The attack may also aim to cripple backup systems to maximize the disruption’s duration and impact.
Examples of Similar Attacks
Past attacks on critical infrastructure, such as the 2015 Ukraine power grid attack, illustrate the potential consequences. The disruption of essential services and the significant economic losses underscore the gravity of such attacks.
Potential Long-Term Effects
The long-term effects of such an attack on a Western country’s power grid could be devastating. Widespread power outages could lead to significant economic losses, impacting industrial production, transportation, and essential services. The cascading effect of the disruption could affect other sectors, potentially leading to social unrest and political instability.
Mitigation Strategies
To mitigate the damage, the targeted country should implement robust cybersecurity measures, including:
- Proactive Vulnerability Management: Regular security audits and penetration testing of critical infrastructure systems are essential to identify and address vulnerabilities before they can be exploited.
- Advanced Threat Protection: Implementing advanced threat detection and response systems to identify and block malicious activity is crucial to thwarting sophisticated attacks.
- Incident Response Planning: Developing a comprehensive incident response plan that Artikels the procedures to follow during a cyberattack is critical to minimize damage and facilitate a swift recovery.
- Robust Backup and Recovery Procedures: Maintaining robust backup and recovery systems is essential to restore critical systems and data quickly after an attack.
International Relations and Cyber Warfare
The potential for Iranian cyberattacks against Western nations raises complex issues within the broader geopolitical landscape. These actions are not isolated incidents but are deeply intertwined with regional tensions, historical rivalries, and the evolving dynamics of international power. Understanding the motivations and strategies of state-sponsored actors is crucial to predicting and mitigating the potential consequences.
Geopolitical Context of Iranian Cyberattacks
The Middle East is a region characterized by complex geopolitical relationships. Tensions between Iran and various Western nations often manifest in various forms, including cyber warfare. These conflicts are frequently rooted in differing interpretations of regional influence and security concerns. The potential for escalation through cyberattacks must be considered within this context, recognizing that such actions can have far-reaching implications beyond the immediate target.
Motivations and Tactics of Nation-State Actors
Different nation-state actors in cyber warfare employ diverse motivations and tactics. Iran, for example, may prioritize disrupting infrastructure or disseminating disinformation to undermine Western interests. Other actors, such as Russia or North Korea, might focus on financial gain or political leverage. Understanding these motivations and the tactics employed allows for a more nuanced assessment of the potential consequences of a cyberattack.
International Law and Norms in Cyber Activities
International law regarding cyber warfare is still developing. There is no universally recognized legal framework to address state-sponsored cyberattacks. The absence of clear norms and enforcement mechanisms creates an environment where such actions can potentially be viewed as acceptable tactics in the context of political and geopolitical rivalries.
Iranian hackers are reportedly planning to unleash devastating data-destroying malware on Western countries. This poses a serious threat to critical infrastructure and sensitive data, and the need for robust cybersecurity measures is paramount. Fortunately, the Department of Justice Offers Safe Harbor for MA Transactions Department of Justice Offers Safe Harbor for MA Transactions might offer some level of protection, though its effectiveness in countering these sophisticated attacks remains to be seen.
The upcoming cyberattacks from Iranian hackers still remain a major concern, demanding immediate attention and proactive defense strategies.
Potential Responses by the International Community
The international community’s response to a significant cyberattack from Iran would likely involve a multi-faceted approach. This may include sanctions, diplomatic pressure, and potential collaborations with allies to counter the attack and deter future actions. Past responses to similar cyber incidents provide some insight into potential strategies, but each situation is unique.
Reports of Iranian hackers planning to unleash data-destroying malware on Western countries are concerning. This potential attack highlights the critical need for robust cybersecurity measures. Luckily, Microsoft’s Azure Cosmos DB has recently been flagged for vulnerabilities. Understanding these vulnerabilities, as detailed in Azure Cosmos DB Vulnerability Details , is crucial in mitigating the risk of these attacks.
While the Iranian hacking group’s actions remain a serious threat, proactively addressing security weaknesses like the Azure Cosmos DB vulnerability can help protect against such potential attacks.
Effects of One Nation-State’s Actions on Others
Actions by one nation-state can significantly affect others. A cyberattack by Iran could provoke retaliatory measures from Western nations, potentially escalating the conflict and impacting global stability. This ripple effect highlights the interconnectedness of the international system and the potential for unintended consequences.
End of Discussion

In conclusion, the potential for Iranian-led cyberattacks against Western countries is a serious concern. The potential for widespread data destruction and disruption of critical systems necessitates proactive security measures and international cooperation. By understanding the tactics, targets, and potential impacts, we can better prepare for and mitigate the risks associated with these escalating cyber threats.
FAQ Section
What are the primary motivations behind these attacks?
Motivations could include retaliatory actions for perceived Western policies, gaining intelligence, or disrupting economic stability.
What types of critical infrastructure are most vulnerable?
Financial institutions, energy grids, transportation systems, and government agencies are potential targets due to their interconnected nature and the potential for widespread disruption.
What role does international cooperation play in countering these threats?
International cooperation is crucial in sharing threat intelligence, developing common defense strategies, and holding perpetrators accountable.
How effective are current cybersecurity measures in preventing these attacks?
Current measures vary in effectiveness, and a proactive, multi-layered approach is essential. Strengthening defenses and fostering international cooperation is vital.