Embracing Advanced Frameworks for Vulnerability Management
Embracing advanced frameworks for effective vulnerability management sets the stage for a robust and proactive security approach. This involves more than just basic scans; it delves into integrating cutting-edge methodologies like DevSecOps and Agile to identify and mitigate vulnerabilities throughout the software development lifecycle. We’ll explore the key frameworks, discuss automation and AI, and Artikel best practices for building a comprehensive vulnerability management program.
From defining vulnerability management frameworks and their core principles to exploring the practical implementation of automation and AI in vulnerability identification and remediation, this exploration is designed to provide a practical guide for organizations seeking to bolster their security posture. We’ll examine the benefits of integrating advanced frameworks into existing processes, along with case studies of successful implementations.
Defining Vulnerability Management Frameworks
Vulnerability management is crucial for maintaining the security posture of any organization. Effective frameworks provide a structured approach to identify, assess, and mitigate vulnerabilities. These frameworks establish standardized procedures, best practices, and guidelines, ultimately improving the overall security posture.A vulnerability management framework acts as a blueprint for organizations to manage vulnerabilities effectively. It defines the steps, procedures, and standards for identifying, assessing, prioritizing, and remediating vulnerabilities across various systems and applications.
It facilitates a proactive approach to security, reducing the risk of exploitation and ensuring compliance with industry standards and regulations.
Vulnerability Management Frameworks: A Comprehensive Overview
Vulnerability management frameworks provide a structured approach to managing vulnerabilities within an organization. They Artikel the principles, methodologies, and processes involved in identifying, assessing, and mitigating vulnerabilities, promoting a proactive security posture.
Core Principles and Methodologies
Different frameworks, such as NIST and OWASP, employ various principles and methodologies. NIST, for instance, focuses on a risk-based approach, emphasizing the prioritization of vulnerabilities based on their potential impact and likelihood of exploitation. OWASP, on the other hand, emphasizes the identification and mitigation of vulnerabilities in web applications, utilizing a standardized set of testing methodologies.
Components of a Vulnerability Management Lifecycle
A typical vulnerability management lifecycle comprises several key stages:
- Identification: This stage involves discovering and cataloging vulnerabilities across systems and applications. Tools and techniques like vulnerability scanners, penetration testing, and security information and event management (SIEM) systems play a vital role in this process. Comprehensive identification efforts help organizations understand their security weaknesses.
- Assessment: Once vulnerabilities are identified, they must be assessed to determine their severity and potential impact. Factors like the likelihood of exploitation, potential damage, and business impact are considered in this assessment. The outcome of this step allows for prioritized remediation.
- Prioritization: Vulnerabilities are ranked based on their risk, considering factors like the potential impact on business operations and the likelihood of exploitation. This stage ensures that resources are allocated effectively to address the most critical vulnerabilities first.
- Remediation: This stage involves implementing the necessary steps to mitigate or eliminate identified vulnerabilities. This can include patching software, configuring systems securely, or implementing security controls. Thorough remediation plans are essential to prevent future vulnerabilities.
- Verification: This step validates that the remediation efforts have been successful and the vulnerabilities have been addressed. This stage is crucial for ensuring that the security posture has been strengthened and that no lingering vulnerabilities remain.
Comparison of Vulnerability Management Frameworks
The following table provides a comparative analysis of different vulnerability management frameworks, highlighting their core principles, key components, and target audience.
| Framework | Core Principles | Key Components | Target Audience |
|---|---|---|---|
| NIST | Risk-based approach, standardized processes, and compliance. | Vulnerability scanning, risk assessment, and remediation. | Organizations of all sizes, aiming for compliance and improved security posture. |
| OWASP | Open-source community-driven approach, web application security. | Testing methodologies, vulnerability identification, and secure coding practices. | Organizations developing or deploying web applications. |
| ISO 27001 | Information security management system (ISMS), risk management. | Policies, procedures, controls, and audits. | Organizations seeking a comprehensive information security management system. |
Advanced Frameworks in Action: Embracing Advanced Frameworks For Effective Vulnerability Management

Embracing advanced frameworks like DevSecOps and Agile methodologies isn’t just a trend; it’s a crucial shift in how organizations approach vulnerability management. These frameworks, when effectively integrated, dramatically improve security posture by embedding security considerations throughout the entire software development lifecycle. This proactive approach, contrasted with traditional, reactive methods, significantly reduces the risk of vulnerabilities entering production environments.The key to success lies in understanding how these advanced frameworks can be implemented within existing vulnerability management processes.
This involves automating repetitive tasks, leveraging machine learning to identify patterns and predict future threats, and building a culture of security awareness across the entire organization. Ultimately, this transformation leads to a more efficient, proactive, and secure environment.
Integrating DevSecOps into Vulnerability Management
DevSecOps, a combination of development, security, and operations, fundamentally alters the way vulnerability management is performed. Instead of treating security as a separate, after-the-fact process, DevSecOps integrates security into every stage of the software development lifecycle (SDLC). This continuous integration and continuous delivery (CI/CD) approach allows for early detection and remediation of vulnerabilities.Organizations can implement DevSecOps principles by incorporating security tools and processes into their CI/CD pipelines.
This includes automated vulnerability scanning, static application security testing (SAST), and dynamic application security testing (DAST) performed throughout the development process. This proactive approach significantly reduces the time and cost associated with finding and fixing vulnerabilities later in the lifecycle. Tools that integrate security scanning into the pipeline can automatically identify and flag vulnerabilities, triggering alerts and prompting immediate remediation.
Benefits of Automation and Machine Learning
Automation and machine learning are powerful enablers of effective vulnerability management. Automation streamlines repetitive tasks, like scanning and reporting, freeing up security teams to focus on higher-level tasks. Machine learning algorithms can analyze vast amounts of data to identify patterns and anomalies indicative of vulnerabilities. This predictive capability allows for proactive threat detection and prioritization of remediation efforts.By automating vulnerability scanning, organizations can dramatically increase the frequency of scans, leading to faster identification of emerging threats.
Embracing advanced frameworks is key for robust vulnerability management, and understanding specific vulnerabilities like those in Azure Cosmos DB is crucial. For example, checking out the Azure Cosmos DB Vulnerability Details helps illustrate how these frameworks can pinpoint and mitigate potential issues. Ultimately, a proactive approach using these frameworks ensures a more secure environment.
Machine learning models can learn from historical data to identify subtle patterns and anomalies that might be missed by traditional methods. This predictive approach can be particularly useful in identifying zero-day exploits and emerging threats.
Successful Implementations of Advanced Frameworks
Numerous organizations have successfully integrated advanced frameworks into their vulnerability management processes. For example, companies adopting DevSecOps have observed a significant reduction in the number of vulnerabilities reaching production environments. These reductions are directly attributable to the proactive nature of the DevSecOps methodology, where vulnerabilities are identified and addressed much earlier in the SDLC.Furthermore, the use of automated tools and machine learning techniques in these implementations has demonstrated considerable efficiency gains.
This improved efficiency translates to faster identification, reduced remediation times, and a lower overall cost of vulnerability management.
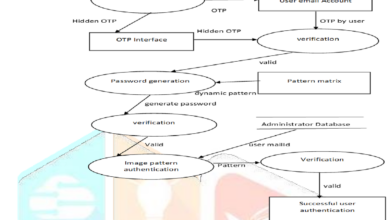
Process Flow Diagram: DevSecOps Integration
A DevSecOps-integrated vulnerability management lifecycle involves several key stages. The diagram below illustrates this integration, emphasizing the continuous nature of the process:
[Diagram of DevSecOps Integration Process Flow]
// A simple textual representation of the process flow
// Start -> Code Commit -> CI/CD Pipeline -> Vulnerability Scan -> Automated Remediation -> Feedback Loop -> Security Review -> Production Deployment -> Monitoring
This continuous process, incorporating vulnerability scanning throughout the pipeline, significantly reduces the likelihood of vulnerabilities reaching production and ensures ongoing monitoring.
Embracing Automation and AI
Modern vulnerability management demands a shift towards automation and AI-powered solutions. Manual processes are often slow, prone to errors, and struggle to keep pace with the ever-evolving threat landscape. Automating tasks and leveraging AI’s analytical capabilities are crucial for effective and efficient vulnerability management.
Automation significantly streamlines the entire process, from scanning for vulnerabilities to applying patches, resulting in faster identification and remediation. AI’s predictive capabilities further enhance the process by prioritizing vulnerabilities based on their potential impact and likelihood of exploitation. This proactive approach minimizes risks and maximizes resource allocation.
Automation Tools for Vulnerability Scanning and Patching
Automation tools are essential for enhancing vulnerability scanning and patching procedures. These tools can perform repetitive tasks, such as scanning networks and systems for vulnerabilities, significantly reducing the time and resources required. By automating these steps, organizations can allocate more resources to higher-priority tasks and gain a better understanding of their security posture.
- Automated vulnerability scanning tools like Nessus, OpenVAS, and QualysGuard can quickly identify weaknesses in applications, networks, and operating systems. These tools use predefined rules and patterns to detect known vulnerabilities, freeing up security personnel to focus on more complex issues.
- Automated patching tools, such as those integrated with vulnerability management platforms, allow for efficient application of security updates to affected systems. These tools can prioritize patches based on criticality, reducing the risk of downtime and security breaches.
AI-Powered Vulnerability Prioritization and Threat Prediction
AI algorithms can analyze vast amounts of data to prioritize vulnerabilities based on their severity and potential impact. These algorithms can consider factors such as the exploitability of a vulnerability, the number of affected systems, and the potential damage that could result from an attack. Prioritization based on these factors enables security teams to focus on the most critical issues first.
Furthermore, AI can predict future threats by analyzing historical data, current events, and emerging trends. This proactive approach allows security teams to anticipate potential vulnerabilities and implement preventative measures before an attack occurs. For example, if an increase in a specific type of malware is detected, AI can flag potential vulnerabilities in systems that could be targeted by this new threat.
Automated Vulnerability Scanning Tools
The table below provides an overview of various automated vulnerability scanning tools, highlighting their key features, supported platforms, and advantages.
Embracing advanced frameworks for vulnerability management is crucial. Modern applications demand robust security, and a key part of that is proactive identification of potential flaws. This often necessitates deploying AI-powered tools like those discussed in Deploying AI Code Safety Goggles Needed , which can automatically scan code for vulnerabilities. Ultimately, integrating these advanced frameworks ensures more comprehensive and efficient vulnerability management practices.
| Tool Name | Key Features | Supported Platforms | Advantages |
|---|---|---|---|
| Nessus | Comprehensive vulnerability scanning, detailed reporting, customizable scans | Windows, Linux, macOS, various network devices | Widely used, robust features, excellent reporting capabilities |
| OpenVAS | Open-source vulnerability scanner, extensive database of vulnerabilities | Windows, Linux, macOS | Cost-effective, actively maintained, large community support |
| QualysGuard | Cloud-based vulnerability management platform, integrates with other security tools | Wide range of platforms and applications | Scalable, centralized management, comprehensive security posture analysis |
Building a Robust Vulnerability Management Program

A robust vulnerability management program is not just a set of tools; it’s a strategic initiative that protects an organization’s digital assets. It demands a proactive approach, encompassing everything from initial identification to final remediation. This involves a comprehensive understanding of vulnerabilities, the processes to mitigate them, and the ongoing monitoring to ensure their effectiveness. Effective vulnerability management fosters a culture of security awareness and empowers organizations to adapt to an ever-evolving threat landscape.
Building a robust program goes beyond simply scanning for vulnerabilities; it’s about establishing a well-defined process that integrates security into the daily operations of the organization. This requires careful planning, clear communication, and consistent monitoring of results. The program must adapt to the changing technological landscape and the emerging threats that organizations face.
Establishing Clear Communication Channels and Reporting Mechanisms
Effective communication is paramount in a vulnerability management program. This includes establishing clear channels for reporting vulnerabilities, both internally and externally. A well-defined escalation path ensures timely responses to critical issues. Regular communication with stakeholders, including IT teams, business units, and executive leadership, keeps everyone informed about the status of vulnerabilities and the remediation efforts.
A critical component of this is a robust reporting mechanism. Reports should provide a clear and concise overview of vulnerabilities, their severity, and the status of remediation efforts. Regular reporting helps track progress, identify trends, and demonstrate the value of the vulnerability management program to stakeholders. The reports should be easily accessible and understandable, allowing for effective monitoring and decision-making.
Defining Metrics and Key Performance Indicators (KPIs)
Tracking the effectiveness of a vulnerability management program is crucial. Key performance indicators (KPIs) provide quantifiable measures to assess the program’s performance. These metrics should be aligned with organizational goals and provide insights into the program’s impact on security posture.
Examples of relevant KPIs include:
- Number of vulnerabilities identified per week/month: This metric tracks the frequency of vulnerability discovery. A consistent increase could indicate a need for improved scanning techniques or more frequent assessments. Similarly, a steady decrease suggests a successful program.
- Vulnerability remediation time: This measures the average time taken to remediate identified vulnerabilities. A longer remediation time could point to process bottlenecks or resource constraints. A shorter remediation time indicates an efficient process.
- Percentage of critical vulnerabilities addressed: This metric focuses on the most severe vulnerabilities. A high percentage indicates a strong focus on critical risks.
- Number of security incidents prevented: This metric reflects the real-world impact of the vulnerability management program. A high number of prevented incidents demonstrates the effectiveness of the program in reducing potential threats.
Key Elements of a Successful Vulnerability Management Policy
A robust vulnerability management policy is essential for consistent and effective execution. This policy should be clearly documented, communicated, and enforced.
- Comprehensive vulnerability scanning procedures: This involves using a variety of scanning tools and techniques to identify a wide range of vulnerabilities. These procedures must cover all relevant systems and applications.
- Automated patching and remediation processes: Automation streamlines the patching process, significantly reducing manual effort and improving response times.
- Regular vulnerability assessments and reviews: This ensures the program is adapting to new threats and vulnerabilities. Regular reviews allow for adjustments to the process and policies.
- Clear roles and responsibilities: Defining roles and responsibilities ensures accountability and efficient workflow.
- Security awareness training: Educating employees on potential vulnerabilities and security best practices is a critical component of a successful vulnerability management program.
- Incident response plan: A well-defined incident response plan ensures a coordinated response to security incidents, including those related to vulnerabilities.
Overcoming Challenges and Best Practices
Embracing advanced vulnerability management frameworks offers significant benefits, but organizations often face hurdles during implementation. Understanding these challenges and developing effective strategies for overcoming them is crucial for a successful transition. This section details potential obstacles, actionable solutions, and best practices for integrating advanced frameworks into existing security infrastructure.
Staying ahead of cyber threats demands embracing advanced frameworks for effective vulnerability management. The recent Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) highlights the evolving landscape of legal considerations. Ultimately, a robust approach to vulnerability management, like employing cutting-edge tools and strategies, is crucial to ensuring data security and compliance in this complex digital environment.
Successfully implementing advanced frameworks requires careful consideration of existing processes, tools, and personnel. A proactive approach to addressing potential issues, coupled with a robust plan for integration, is key to achieving optimal results. This includes careful planning and communication to ensure a smooth transition and mitigate any disruptions.
Potential Challenges
Organizations transitioning to advanced frameworks often encounter several challenges. Resistance to change from personnel accustomed to existing methods, inadequate resources (financial, human, or technological), and a lack of skilled personnel capable of utilizing the new tools are common obstacles. Furthermore, integrating new frameworks with existing security infrastructure can be complex, requiring significant effort to ensure compatibility and seamless data flow.
Data silos and inconsistent data formats between different systems can also complicate the process.
Strategies for Overcoming Challenges
Addressing these challenges requires a multifaceted approach. Comprehensive training programs for staff are crucial to ensure personnel are equipped to use new tools and frameworks effectively. Clear communication and stakeholder buy-in are essential for fostering acceptance and support. Allocating sufficient resources and establishing a dedicated team can help manage the complexities of integration. Furthermore, careful planning and thorough documentation are crucial to ensure that the transition is well-managed.
Establishing clear communication channels and regular feedback loops can help mitigate issues and ensure successful integration.
Best Practices for Integration
Integrating advanced frameworks into existing security infrastructure requires a structured approach. Thorough assessments of current processes and tools are necessary to identify areas for improvement and potential conflicts. Careful planning and phased implementation, starting with pilot programs, can help minimize disruptions and allow for iterative refinement. Implementing strong data governance policies, ensuring data consistency and standardization, and establishing clear data flow protocols are critical for success.
Prioritizing security audits and penetration testing throughout the implementation process helps ensure the framework is working as intended.
Case Studies
Several organizations have successfully integrated advanced vulnerability management frameworks into their operations. One example involves a financial institution that experienced a significant reduction in vulnerability exposure after implementing a new, automated vulnerability scanning and patching system. This led to a considerable reduction in security incidents and improved overall security posture. Another example demonstrates how a healthcare organization successfully streamlined its vulnerability management process by integrating various tools into a centralized platform, resulting in improved efficiency and reduced operational costs.
These cases highlight the potential benefits of adopting advanced frameworks and the importance of careful planning and execution.
Illustrative Scenarios
Successfully managing vulnerabilities hinges on a proactive and adaptive approach. Ignoring emerging threats and outdated frameworks can lead to significant security breaches. This section illustrates the crucial difference between effective vulnerability management strategies and those that fall short. We will examine both successful implementations and failures, highlighting the importance of advanced frameworks in preventing and mitigating security risks.
Scenario 1: A Company Embracing Advanced Frameworks
A mid-sized software company, “SecureTech,” proactively integrates advanced vulnerability management frameworks into its development lifecycle. They leverage a platform that automatically scans code for potential vulnerabilities during development, continuously monitors production environments for emerging threats, and employs machine learning algorithms to predict and prioritize potential attacks. When a critical vulnerability is identified, the system triggers automated remediation steps, like patching or implementing workarounds.
This proactive approach minimizes the risk of exploitation, enabling rapid response and minimizing downtime.
Scenario 2: A Company Failing to Embrace Advanced Frameworks
“VulnerableCorp,” a similar-sized company, relies on outdated manual vulnerability scanning and patching procedures. Their security team lacks the resources and expertise to effectively analyze complex vulnerabilities. A zero-day exploit targets a previously unknown vulnerability in their widely used software library. The lack of automated detection and response results in a significant data breach, impacting customer trust and potentially leading to substantial financial losses.
Comparing Vulnerability Management Approaches
| Feature | SecureTech (Advanced Frameworks) | VulnerableCorp (Outdated Approach) |
|---|---|---|
| Vulnerability Detection | Automated, continuous, across the entire software lifecycle | Manual, sporadic, limited to post-release |
| Vulnerability Prioritization | Automated based on severity and likelihood of exploitation | Manual, subjective, often delayed |
| Response Time | Rapid automated remediation, minimized downtime | Delayed manual patching, potential for extended exposure |
| Security Posture | Proactive, constantly improving | Reactive, vulnerable to exploitation |
| Cost of Breach | Potentially lower due to minimized exposure | Potentially higher due to prolonged vulnerability exposure |
Demonstrating the Importance of Advanced Frameworks
The contrasting scenarios highlight the crucial role of advanced vulnerability management frameworks. SecureTech’s proactive and automated approach minimizes risks and ensures a strong security posture. VulnerableCorp’s failure to adapt to modern threats resulted in a significant security breach, emphasizing the need for continuous improvement and adoption of innovative solutions. Advanced frameworks are not just about identifying vulnerabilities but also about automating the process of remediation, ensuring rapid response and minimizing the impact of security incidents.
The effectiveness of vulnerability management is directly correlated with the adoption of advanced frameworks.
Future Trends and Predictions
The landscape of vulnerability management is constantly evolving, driven by advancements in technology and the ever-increasing sophistication of cyber threats. Understanding these trends is crucial for organizations to proactively adapt and build robust security postures. Predicting the future, while inherently uncertain, allows for strategic planning and investment in the right technologies and processes.
Emerging Technologies’ Influence, Embracing advanced frameworks for effective vulnerability management
The integration of emerging technologies like artificial intelligence (AI), machine learning (ML), and the Internet of Things (IoT) is profoundly impacting vulnerability management. These technologies are transforming vulnerability detection and response, leading to greater automation and improved efficiency.
AI-Powered Vulnerability Detection and Response
AI and ML algorithms are being increasingly deployed to analyze vast datasets of security events and identify vulnerabilities more quickly and accurately. These algorithms can identify patterns and anomalies that might be missed by traditional methods. For example, AI-powered systems can learn from historical vulnerability data to predict potential future threats and proactively address them. This approach enhances the speed and accuracy of threat detection and response.
Automation of Vulnerability Management Tasks
Automation is another critical trend in vulnerability management. Automated tools and processes can streamline tasks such as vulnerability scanning, patching, and reporting. This automation not only reduces the workload on security teams but also allows them to focus on more strategic initiatives. Automation can significantly improve efficiency and reduce the human error that can introduce vulnerabilities.
IoT Security Considerations
The proliferation of IoT devices introduces new challenges and opportunities for vulnerability management. Vulnerabilities in these devices can potentially expose entire networks to attacks. The need for specialized tools and techniques to identify and manage vulnerabilities specific to IoT devices is becoming increasingly important. Organizations need to adapt their strategies to account for the unique security requirements of this expanding ecosystem.
The Rise of Cloud Security Considerations
The increasing reliance on cloud services brings new security considerations for vulnerability management. The distributed nature of cloud environments and the shared responsibility model necessitate new approaches to identifying and mitigating vulnerabilities. The security of cloud environments demands specialized frameworks and tools that can analyze and manage vulnerabilities in the cloud infrastructure and applications. Security tools and strategies need to be adapted to the cloud context.
Potential Future Challenges
While advancements offer exciting possibilities, several challenges are anticipated. One significant hurdle is the evolving nature of cyber threats. The rapid development of new attack vectors requires continuous adaptation and improvement of vulnerability management strategies. Another key challenge is maintaining the accuracy and effectiveness of vulnerability detection tools in the face of increasingly sophisticated evasion techniques. Furthermore, ensuring compliance with evolving regulatory requirements and standards presents a persistent challenge.
The ever-increasing complexity of security landscapes poses a continuous challenge to security teams.
Outcome Summary
In conclusion, embracing advanced frameworks for effective vulnerability management is crucial in today’s complex threat landscape. By integrating automation, AI, and robust methodologies like DevSecOps, organizations can proactively identify and remediate vulnerabilities, significantly reducing the risk of breaches and improving overall security posture. The future of vulnerability management lies in embracing these advancements and adapting to emerging technologies, ensuring that security measures stay ahead of the evolving threat landscape.
Answers to Common Questions
What are some common challenges organizations face when implementing advanced vulnerability management frameworks?
Implementing advanced frameworks can be challenging due to the need for significant cultural shifts, integration with existing systems, and training for personnel. Resistance to change, inadequate resources, and lack of skilled personnel can also hinder progress. Successfully navigating these obstacles requires a well-defined plan, clear communication, and a commitment to ongoing improvement.
How can organizations effectively prioritize vulnerabilities for remediation?
Prioritization depends on several factors, including the severity of the vulnerability, its potential impact, and the likelihood of exploitation. Utilizing risk assessment tools and incorporating AI-powered analysis can significantly improve prioritization efforts, ensuring that resources are allocated to the most critical vulnerabilities.
What are some key performance indicators (KPIs) for measuring the effectiveness of a vulnerability management program?
Effective KPIs might include the number of vulnerabilities identified and remediated, the time taken to remediate vulnerabilities, the reduction in security incidents, and the overall improvement in the organization’s security posture. Tracking these metrics over time provides valuable insights into the program’s effectiveness and areas needing improvement.
How can organizations ensure that their vulnerability management program remains up-to-date with the latest threats and technologies?
Staying current requires continuous monitoring of emerging threats and technologies. This involves subscribing to security advisories, participating in industry forums, and training personnel on new vulnerabilities and remediation techniques. Regular updates to the vulnerability management program are critical to maintaining an effective defense against the evolving threat landscape.