-
Cybersecurity

Is It the Solution to Filling Cybersecurity Workforce Gap 2?
Is it the solution to filling cybersecurity workforce gap 2? This exploration delves into a crucial question facing organizations today.…
Read More » -
Cybersecurity

Iranian Hackers Target Western Data
Iranian hackers to launch data destroying malware on western countries. This escalating cyber threat poses a significant risk to critical…
Read More » -
Cybersecurity

Iranian Hackers Target Australian Universities
Iran hackers cyber attack australian universities – Iranian hackers cyber attack australian universities, a disturbing trend in the digital landscape,…
Read More » -
Security

iPhone Vulnerability Contactless Payment Fraud
iPhone vulnerability allows hackers to fraudulently make contactless payments, exposing a serious security flaw that could lead to significant financial…
Read More » -
Technology

IoT Worm Threatens City Smart Lights
An IoT worm could hack all smart lights in a city, potentially crippling vital infrastructure. This poses a significant threat…
Read More » -
Technology

Criminals Spy on You Connected Home Devices
Internet connected household electronics are helping criminals spy on you. From smart thermostats to security cameras, our homes are increasingly…
Read More » -
Technology

Intels Broadcom Grab Blocking Qualcomm Merger
Intel to acquire Broadcom to prevent its merger with Qualcomm. This high-stakes move in the semiconductor industry is creating ripples…
Read More » -
Business Insurance

Insurance Companies Now Cover Ransomware Cyber Attacks
Insurance companies are now covering ransomware cyber attacks, signaling a significant shift in how businesses approach digital security risks. This…
Read More » -
Cybersecurity

Insider Threats Detect, Remediate, Prevent Attacks – Live Webinar
Insider threats detect remediate prevent insider attacks live webinar. This webinar dives deep into the insidious world of insider threats,…
Read More » -
Cybersecurity
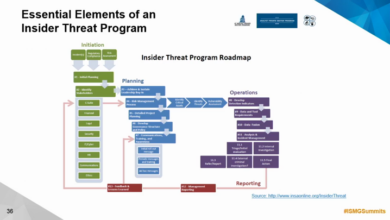
Insider Threat Detection What You Need to Know
Insider threat detection what you need to know sets the stage for understanding a critical security issue in today’s digital…
Read More »
Privacy Overview
This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Strictly Necessary Cookies
Strictly Necessary Cookie should be enabled at all times so that we can save your preferences for cookie settings.
If you disable this cookie, we will not be able to save your preferences. This means that every time you visit this website you will need to enable or disable cookies again.
