-
Cybersecurity

Insider Risk Unconventional Thoughts & Lessons Learned
Insider risk unconventional thoughts and lessons learned – Insider risk: unconventional thoughts and lessons learned. This exploration delves into the…
Read More » -
Industrial Automation

Industrial Open Automation Software Vulnerabilities Unveiled
Industrial open automation software filled with vulnerabilities – Industrial open automation software, filled with vulnerabilities, poses a significant threat to…
Read More » -
Cybersecurity

Imperva Cloud Firewall Hack Data Exposed
Imperva announces that data of its cloud firewall was exposed to hackers, sparking immediate concern about the security of sensitive…
Read More » -
Software Development
If Youre Only as Strong as Your Allies, Should You Trust Third-Party Code?
If youre only as strong as your allies should you trust third party code – If you’re only as strong…
Read More » -
Technology

IBM Acquires Spanugo Cloud Security Boost
IBM acquires Spanugo cloud security startup, marking a significant move in the rapidly evolving cloud security landscape. This acquisition promises…
Read More » -
Technology

Huawei Equipment Dutch Mobile Eavesdropping Fears
Huawei equipment eavesdropping on Dutch mobile users raises serious security concerns. This investigation delves into the historical context of Huawei’s…
Read More » -
Technology

Zero Trust CIO & CTO Advantage in Corporate Environments
How zero trust helps CIOs and CTOs in corporate environments is a critical issue. Zero trust security is rapidly reshaping…
Read More » -
Cybersecurity
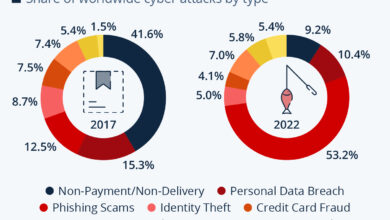
How to Make 5 Million a Day in Cybercrime A Risky Proposition
How to make 5 million a day in cybercrime? This is a tempting question, but the reality is far more…
Read More » -
Cybersecurity
How to Defend Against Zero-Click Attacks
How to defend against zero click attacks – How to defend against zero-click attacks is crucial in today’s threat landscape.…
Read More »
Privacy Overview
This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Strictly Necessary Cookies
Strictly Necessary Cookie should be enabled at all times so that we can save your preferences for cookie settings.
If you disable this cookie, we will not be able to save your preferences. This means that every time you visit this website you will need to enable or disable cookies again.

