-
Healthcare
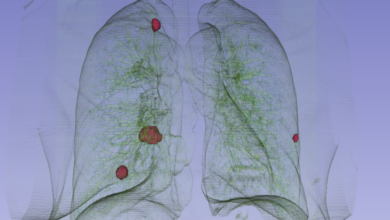
AI Lung Cancer Detection 10 Years Earlier
Lung cancer detection possible 10 years prior with AI, opening up a new era in preventative healthcare. This groundbreaking technology…
Read More » -
Technology

Logicalis Intelligent Security for Global Safety
Logicalis enhances global security services with the launch of intelligent security, offering a groundbreaking approach to safeguarding critical infrastructure and…
Read More » -
Cybersecurity
Intel Zombieload Hacker Target
Intel Zombieload vulnerability might expose sensitive data like passwords to hackers. This sophisticated attack leverages a previously unknown flaw in…
Read More » -
Business Management

Insufficient Mobile Security Business Enterprises at Risk
Insufficient mobile security business enterprises at risk face significant vulnerabilities in today’s digital landscape. From financial losses and reputational damage…
Read More » -
Cybersecurity

Insider Threat and Mitigation Best Practices
Insider threat and mitigation best practices are crucial for organizations to protect sensitive data and systems. Understanding the different types…
Read More » -
Technology

IBM and Cisco Unite for Cloud Security
IBM and Cisco announce a partnership to tackle threats related to cloud security, promising a robust defense against the ever-evolving…
Read More » -
Cybersecurity
IAST, RASP, and Runtime Instrumentation Securing Apps
Iast rasp and runtime instrumentation – IAST, RASP, and runtime instrumentation are crucial for securing applications. This exploration delves into…
Read More » -
Work From Home

Hybrid Working Tips for Success
Hybrid working and tips to make it a success is becoming increasingly popular, and for good reason. It offers a…
Read More » -
Healthcare Technology

Care Analytics Partner Webinar CloudPassage Security & Compliance 2
Care analytics partner webinar cloudpassage security and compliance 2 – Care Analytics Partner Webinar: CloudPassage Security and Compliance 2 dives…
Read More » -
Cybersecurity

How to Survive a Ransomware Attack A Comprehensive Guide
How to survive a ransomware attack is a critical question for businesses and individuals alike. This guide dives deep into…
Read More »
Privacy Overview
This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Strictly Necessary Cookies
Strictly Necessary Cookie should be enabled at all times so that we can save your preferences for cookie settings.
If you disable this cookie, we will not be able to save your preferences. This means that every time you visit this website you will need to enable or disable cookies again.
