-
Cybersecurity Analysis

Cybersecurity Half Full or Half Empty?
Is the cybersecurity industrys glass half full or half empty – Is the cybersecurity industry’s glass half full or half…
Read More » -
International Relations

Is Banning Chinese Products Working?
Is banning Chinese products in the name of national security working for countries? This complex issue dives deep into the…
Read More » -
Cybersecurity

IP Cameras IoTs Cyber Attack Hotspots
IP cameras among IoT devices are most vulnerable to cyber attacks. The Internet of Things (IoT) is rapidly changing our…
Read More » -
Business & Finance

Internet of Things Inc Acquires AI-Driven Weather Telematics Inc
Internet of things inc acquires ai driven weather telematics inc – Internet of Things Inc acquires AI-driven weather telematics inc,…
Read More » -
Politics

Huawei to Take Up Espionage Case with Biden
Huawei to take up its espionage case with Joe Biden, a move that promises to be a major escalation in…
Read More » -
Technology

Huawei Acquires Hexatier Cloud Security Boost
Huawei to acquire israel based cloud security firm hexatier – Huawei to acquire Israel-based cloud security firm Hexatier, signaling a…
Read More » -
Cybersecurity
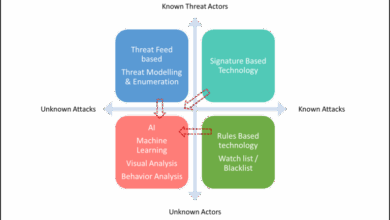
Connecting Dots Complex Threat Landscape
How to connect all the dots in a complex threat landscape is crucial for modern security. This exploration delves into…
Read More » -
Network Security

How Security Service Edge Revolutionizes Network Security
How security service edge is revolutionizing network security by fundamentally shifting the way we approach network security. It’s moving beyond…
Read More » -
Cybersecurity

Multi-Vector Security Defeating Evasive Malware
How multi vector security solutions neutralize evasive malware is a crucial topic in today’s digital landscape. Malware constantly evolves, finding…
Read More »
Privacy Overview
This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Strictly Necessary Cookies
Strictly Necessary Cookie should be enabled at all times so that we can save your preferences for cookie settings.
If you disable this cookie, we will not be able to save your preferences. This means that every time you visit this website you will need to enable or disable cookies again.