-
Technology
Google Admits Its Virtual Assistants Indulge in Eavesdropping
Google admits its virtual assistants indulge in eavesdropping. This bombshell revelation has sent shockwaves through the tech world, raising serious…
Read More » -
Cloud Security

Google Acquired Cloud Companies One Security Umbrella
Google acquired cloud companies now come under one security umbrella, a massive undertaking with significant implications for both Google and…
Read More » -
Online Security
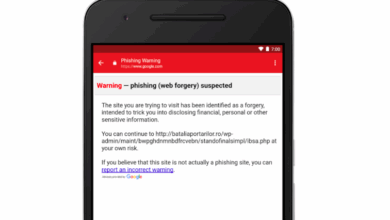
Gmail Users Vulnerable to Phishing Cyber Attacks
Gmail users vulnerable to the following phishing cyber attacks: It’s a scary thought, isn’t it? We all rely on Gmail…
Read More » -
Technology
Glass Class The Searchable Log of All Conversation and Knowledge
Glass class the searchable log of all conversation and knowledge – Glass Class: The Searchable Log of All Conversation and…
Read More » -
Technology

GitHub Refuses Microsofts $2 Billion Acquisition
Github refuses microsofts 2 billion acquisition deal – GitHub refuses Microsoft’s 2 billion dollar acquisition deal – a headline that…
Read More » -
Data Privacy

GDPR Compliance Checklist 9 Step Guide
Gdpr compliance checklist 9 step guide – GDPR Compliance Checklist: 9 Step Guide – navigating the complexities of GDPR can…
Read More » -
Cybersecurity
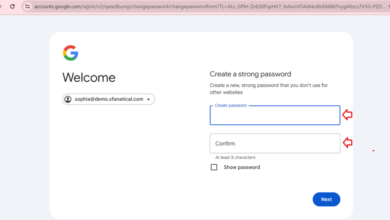
G Suite Passwords Stored in Plain Text for 14 Years
G Suite passwords stored in plain text for 14 years? That’s a headline that sent shivers down my spine when…
Read More » -
Cloud Security

Fundamental Cloud Security Practices to Consider
Fundamental cloud security practices to consider are more crucial than ever in today’s interconnected world. Think of it like this:…
Read More » -
International Relations

France Suspects Russia Behind 24,000 Cyber Attacks
France suspects russia behind the 24000 cyber attacks – France suspects Russia behind 24,000 cyber attacks – a shocking accusation…
Read More » -
Cybersecurity
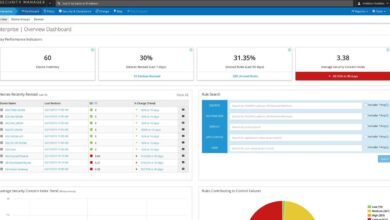
Firemon Announces Intelligent Cloud Security Management Solution
Firemon announces an intelligent cloud security management solution – a game-changer in the world of cybersecurity! Forget juggling multiple tools…
Read More »