-
IT Security

5 Reasons Why Governance Must Be a Priority for Secure File Sharing
5 Reasons Why Governance Must Be a Priority when it comes to secure file sharing: In today’s hyper-connected world, secure…
Read More » -
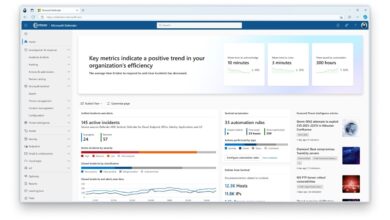
Cybersecurity

3 Ways AI Strengthens Cybersecurity Defense
3 ways in which ai strengthens cybersecurity defense – 3 Ways AI Strengthens Cybersecurity Defense sets the stage for a…
Read More » -
Tech News
FTC Slaps Avast with $16.5M Penalty for Selling Data
Ftc slaps avast with 16 5m penalty for selling browser data – FTC slaps Avast with a $16.5 million penalty…
Read More » -
Cybersecurity

12 Common Concerns of the Permeable IoT Attack Surface
12 Common Concerns of the Permeable IoT Attack Surface: Ever felt that nagging unease when your smart devices are “too”…
Read More » -
Streaming Services

Netflix Password Sharing Crackdown Yields Excellent Results
Netflix password sharing crackdown yields excellent results! Who would have thought cracking down on password sharing could be so lucrative?…
Read More » -
Technology Ethics

Googles Gemini AI Data Privacy Invasion?
Google to do data privacy invasion in the name of gemini ai development – Google’s Gemini AI: Data Privacy Invasion?…
Read More » -
Finance

The Evolution of Financial Fraud
The evolution of financial fraud is a fascinating, and frankly, terrifying journey through history. From simple swindles in pre-industrial societies…
Read More » -
IT Security

Addressing Legacy System Patching Neglect
Addressing legacy system patching neglect isn’t just about ticking boxes; it’s about proactively safeguarding your organization from potentially catastrophic security…
Read More » -
Cloud Computing
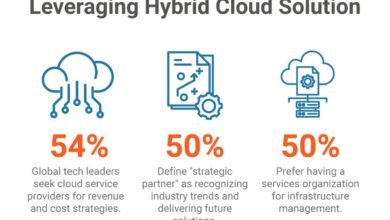
The Importance of Zero-Touch in Cloud Security
The importance of zero touch in cloud security – The importance of zero-touch in cloud security is rapidly becoming a…
Read More »
Privacy Overview
This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Strictly Necessary Cookies
Strictly Necessary Cookie should be enabled at all times so that we can save your preferences for cookie settings.
If you disable this cookie, we will not be able to save your preferences. This means that every time you visit this website you will need to enable or disable cookies again.