Bitglass Security Spotlight GCP, Synack, Drupal Defense
Bitglass security spotlight google synack drupal integration offers a powerful approach to bolstering security for Drupal websites hosted on Google Cloud Platform. This detailed exploration delves into the intricacies of this integration, examining how Bitglass Security Spotlight, coupled with Synack’s security research, strengthens Drupal’s defenses against emerging threats.
We’ll cover everything from the foundational overview of Bitglass Security Spotlight to its practical applications in securing Drupal on GCP. Understanding the specific security implications for Drupal and how Bitglass addresses them is key, as is exploring the synergy with Google Cloud Platform and Synack’s security research. This integration promises enhanced security posture and a proactive approach to mitigating vulnerabilities.
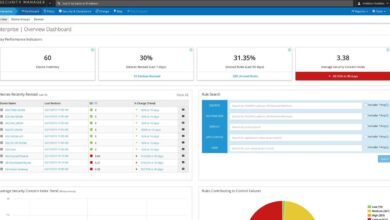
Bitglass Security Spotlight
Bitglass Security Spotlight is a powerful security solution designed to proactively identify and mitigate threats across diverse cloud environments. It offers a comprehensive approach to cloud security, focusing on protecting sensitive data and ensuring compliance with industry regulations. This solution stands out through its innovative architecture and integration capabilities, providing a robust defense against modern cyberattacks.Bitglass Security Spotlight goes beyond basic threat detection by analyzing intricate patterns and anomalies within user activity and data flows.
I’ve been digging into Bitglass’s security spotlight on Google, Synack, and Drupal lately. It’s fascinating how these security concerns intersect, especially with recent news about the Department of Justice’s safe harbor policy for Massachusetts transactions. This policy, detailed in a recent update here , could potentially impact how these security concerns are addressed. Regardless, it’s crucial to stay updated on the latest developments in the Bitglass security spotlight on Google, Synack, and Drupal.
This proactive approach helps organizations stay ahead of emerging threats and safeguard sensitive information. The platform’s intuitive interface allows for easy management and monitoring of security policies, making it accessible to both technical and non-technical users.
Overview of Key Features
Bitglass Security Spotlight offers a suite of features to bolster security posture. These features include real-time threat detection, granular control over data access, and automated policy enforcement. The platform’s core strength lies in its ability to analyze a vast amount of data to identify subtle indicators of malicious activity, thereby preventing potential breaches. This proactive approach ensures that sensitive data remains protected, regardless of the location or device used for access.
Types of Security Threats Detected
Bitglass Security Spotlight effectively identifies various security threats. These threats range from phishing attacks and malware to data exfiltration attempts and insider threats. The platform employs advanced threat intelligence feeds and machine learning algorithms to identify and respond to emerging threats in real-time. Its comprehensive approach allows it to detect sophisticated attacks that evade traditional security measures.
Architecture and Technical Implementation
Bitglass Security Spotlight leverages a multi-layered architecture to ensure robust threat detection and response. This architecture incorporates advanced threat intelligence, machine learning algorithms, and a cloud-based platform for scalability and efficiency. The platform is designed to integrate seamlessly with existing security infrastructure, minimizing disruption to ongoing operations. The solution’s architecture ensures that data flows are analyzed efficiently, enabling quick identification and mitigation of threats.
Integration with Other Security Tools
The platform is designed for seamless integration with other security tools, such as SIEMs and vulnerability management systems. This integration enhances the overall security posture by providing a unified view of the security landscape. This unified view allows for correlation of events across different security systems, providing a holistic picture of potential threats and risks.
Enhanced Security Posture
Bitglass Security Spotlight enhances an organization’s security posture by providing a proactive approach to threat detection and response. The platform’s comprehensive features and flexible architecture allow organizations to adapt to evolving threats and maintain compliance with industry regulations. Through continuous monitoring and analysis of data and user activity, Bitglass Security Spotlight minimizes the risk of data breaches and enhances the overall security of sensitive information.
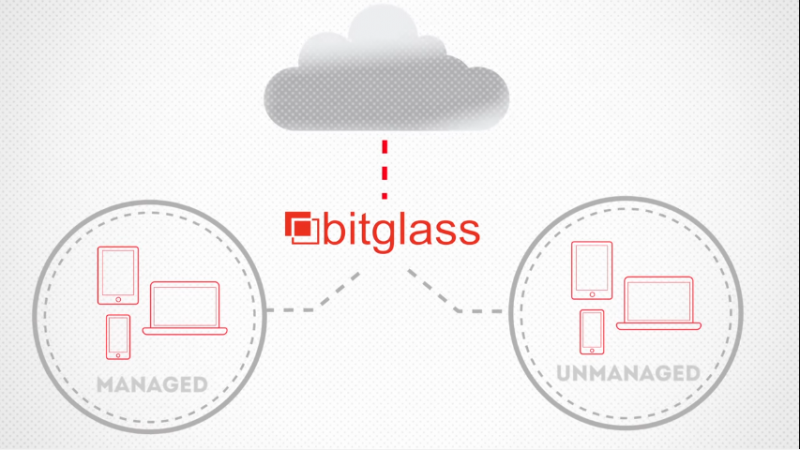
Google Cloud Platform Integration
Bitglass Security Spotlight’s integration with Google Cloud Platform (GCP) offers a powerful approach to securing sensitive data within the Google ecosystem. This integration leverages Bitglass’s cloud security expertise to provide a robust layer of protection for data accessed and shared via GCP services. It’s a key element in enabling organizations to securely utilize GCP while maintaining data privacy and compliance.This integration allows organizations to control and monitor data access across various GCP services, including storage, compute, and networking.
By implementing this integration, companies can achieve a more comprehensive security posture across their cloud infrastructure.
Integration Process Overview
The integration process typically involves several key steps. First, the necessary Bitglass Security Spotlight components need to be provisioned and configured. This includes setting up the appropriate API keys and permissions within GCP and Bitglass. Secondly, configuring policies and access controls within Bitglass to govern data access and sharing from specific GCP resources is crucial. This step is critical to ensuring that sensitive data is protected from unauthorized access.
The Bitglass security spotlight on Google, Synack, and Drupal highlights critical vulnerabilities in various platforms. Recently, though, a concerning vulnerability emerged in Microsoft Azure Cosmos DB, requiring immediate attention. For detailed insights on the specific issues affecting Azure Cosmos DB, check out the full report on Azure Cosmos DB Vulnerability Details. Understanding these vulnerabilities helps security teams better prepare for similar threats, directly impacting the Bitglass security spotlight’s focus on comprehensive platform protection.
Third, testing the integration thoroughly is essential to validate that the setup is working as expected and that all necessary security controls are in place.
Security Benefits
Integrating Bitglass Security Spotlight with GCP provides a significant enhancement to security posture. This integration helps prevent data breaches by enforcing granular access controls. This prevents unauthorized access and exfiltration of sensitive information. Moreover, it enables organizations to meet regulatory compliance requirements more effectively by demonstrating their commitment to data security. Finally, Bitglass Security Spotlight helps organizations track and manage data access across GCP, improving visibility and control.
Configuration Steps and Best Practices
- API Key Management: Ensure proper API key management within GCP and Bitglass. Follow Bitglass’s documentation meticulously for API key creation and configuration. This is critical for secure communication between the two systems. Incorrectly configured API keys can lead to security vulnerabilities.
- Policy Configuration: Carefully define and implement policies in Bitglass that govern access to specific GCP resources. These policies should reflect the organization’s data security policies and regulatory requirements. Granular control over data access is essential for maintaining data security.
- Testing and Validation: Thorough testing is essential to validate the integration’s effectiveness. Simulate real-world scenarios to ensure that the setup functions as expected. This is a critical step to avoid costly errors or security vulnerabilities after deployment.
Potential Security Risks and Mitigation Strategies
- Misconfigured Policies: Improperly configured policies in Bitglass can create loopholes for unauthorized access. Careful review and testing of policies are crucial. Organizations should implement a thorough policy review process to ensure the policies align with their security needs.
- Insufficient Access Control: Insufficient access control mechanisms can expose sensitive data to risks. Implement robust access controls to limit access to only authorized users and resources. This ensures that sensitive data is only accessible to those who need it.
- Lack of Monitoring: Insufficient monitoring of data access and activity can lead to unnoticed security breaches. Enable comprehensive monitoring and alerting capabilities within Bitglass to identify potential threats promptly. This proactive approach to security can significantly reduce the impact of potential incidents.
Troubleshooting Integration Issues
- API Key Verification: Double-check the API keys to confirm they are correctly configured in both systems. Review Bitglass and GCP documentation to ensure the API key configuration is compliant. Incorrectly configured API keys often lead to integration failures.
- Policy Review: Review the policies in Bitglass to confirm they are correctly targeting the desired GCP resources. Mismatched policies can cause unexpected behavior or errors. Ensure that policies are consistently reviewed and updated as needed.
- Testing Environment: Use a dedicated testing environment to isolate and debug any integration issues before deploying to production. This approach helps prevent disruptions to the production environment and allows for thorough testing.
Synack Security Research Integration
Bitglass Security Spotlight, with its comprehensive threat intelligence capabilities, benefits greatly from partnerships like the one with Synack. This integration leverages Synack’s vast network of security researchers to proactively identify and address potential vulnerabilities before they can be exploited. This approach transforms security from a reactive process to a proactive, anticipatory one, minimizing the risk of breaches and ensuring a robust security posture.This integration seamlessly connects Bitglass Security Spotlight with Synack’s security research platform.
This allows for the immediate identification and prioritization of vulnerabilities discovered by Synack researchers, ensuring that critical issues are addressed quickly. The flow of information between the platforms is streamlined, facilitating a rapid response to potential threats and enabling organizations to stay ahead of evolving attack vectors.
Integration Details
The integration between Bitglass Security Spotlight and Synack’s security research platform operates on a shared intelligence model. Synack researchers, through their engagement with various applications and systems, identify vulnerabilities. This information is then fed into the Bitglass Security Spotlight system. The system analyzes the reported vulnerabilities, correlates them with existing threat intelligence, and prioritizes them based on their potential impact.
This allows organizations to focus on the most critical issues and allocate resources effectively.
Proactive Security Measures
This integrated approach significantly enhances proactive security measures. By incorporating Synack’s research into the Bitglass Security Spotlight platform, organizations gain access to a broader range of potential vulnerabilities. This allows them to patch and mitigate weaknesses before malicious actors can exploit them, thus reducing the likelihood of successful attacks. The speed at which vulnerabilities are addressed is crucial in minimizing the window of opportunity for attackers.
Comparison of Platforms, Bitglass security spotlight google synack drupal
| Feature | Synack | Bitglass Security Spotlight |
|---|---|---|
| Vulnerability Discovery | Specializes in finding vulnerabilities through a global community of security researchers. | Provides a comprehensive view of threat intelligence, including vulnerabilities from various sources. |
| Threat Intelligence | Focuses on discovering and reporting vulnerabilities. | Provides a centralized platform for analyzing and responding to threats, including vulnerabilities from various sources. |
| Response Mechanism | Facilitates communication and collaboration between researchers and organizations. | Offers tools for prioritizing and addressing identified vulnerabilities. |
| Scalability | Leverages a large community of researchers, allowing for rapid identification of a broad range of vulnerabilities. | Scales to support organizations of various sizes and complexities. |
| Cost | Typically involves a subscription model based on engagement and research scope. | Cost depends on the chosen plan and features utilized. |
Addressing Security Vulnerabilities
The integrated approach allows organizations to address a wider range of security vulnerabilities than either platform could independently. For example, a vulnerability in a web application discovered by a Synack researcher can be immediately flagged and prioritized within Bitglass Security Spotlight. This allows the organization to deploy the appropriate patches and safeguards before a malicious actor can exploit the flaw.
Furthermore, the platform’s analysis can identify similar vulnerabilities across different systems, helping to develop a more holistic security strategy.
Drupal Security Implications
Drupal, a popular open-source content management system (CMS), powers numerous websites and applications. While providing a robust platform for content creation, its widespread adoption also exposes it to potential security vulnerabilities. Understanding these risks and how to mitigate them is crucial for maintaining the integrity and security of Drupal-based systems.
Security Risks Associated with Drupal Websites and Applications
Drupal’s open-source nature, while beneficial for community development, also means its code is publicly accessible. This accessibility, while fostering collaboration, presents a significant security risk. Malicious actors can potentially identify vulnerabilities in the code and exploit them for unauthorized access or data breaches. Further, the complex architecture of Drupal, involving various modules and integrations, introduces numerous points of potential compromise.
A vulnerability in one module can potentially impact the entire system. Poorly configured Drupal installations and inadequate security measures can further exacerbate the risk.
How Bitglass Security Spotlight Addresses Drupal Security Risks
Bitglass Security Spotlight provides a comprehensive approach to safeguarding Drupal-based systems. It proactively identifies and mitigates threats by analyzing data flow and user behavior. By focusing on granular access controls and real-time threat detection, Bitglass can effectively limit the impact of security vulnerabilities. Its granular control over sensitive data movement and user interactions allows for a more tailored and responsive security posture.
Examples of Security Vulnerabilities Frequently Encountered in Drupal Environments
Common vulnerabilities in Drupal environments include cross-site scripting (XSS), SQL injection, and cross-site request forgery (CSRF). XSS attacks inject malicious scripts into legitimate web pages, potentially compromising user sessions or stealing sensitive information. SQL injection exploits vulnerabilities in database queries to gain unauthorized access to data. CSRF attacks manipulate users into performing unwanted actions on a website without their knowledge.
Table: Common Drupal Security Threats and Bitglass Security Spotlight Mitigations
| Security Threat | Description | Bitglass Security Spotlight Mitigation |
|---|---|---|
| Cross-Site Scripting (XSS) | Attackers inject malicious scripts into web pages viewed by other users. | Bitglass’s web security controls can detect and block malicious scripts embedded in content, preventing their execution. |
| SQL Injection | Attackers manipulate database queries to gain unauthorized access to data. | Bitglass’s database access controls can monitor and block suspicious queries, protecting sensitive data. |
| Cross-Site Request Forgery (CSRF) | Attackers trick users into performing unwanted actions on a website. | Bitglass’s user authentication and authorization mechanisms can verify requests and prevent unauthorized actions. |
| File Inclusion Vulnerabilities | Attackers exploit vulnerabilities to execute malicious files. | Bitglass’s file access controls and real-time threat detection can identify and prevent attempts to execute unauthorized files. |
Scenario: Preventing a Security Threat to a Drupal Website
Imagine a Drupal website hosting user accounts and sensitive financial data. An attacker identifies a vulnerability in a custom module allowing remote code execution. Without Bitglass Security Spotlight, the attacker could exploit this vulnerability to gain unauthorized access, potentially exfiltrating user data or injecting malicious code. However, with Bitglass Security Spotlight, the real-time threat detection component immediately flags suspicious activity related to the identified vulnerability.
Bitglass’s security spotlight on Google, Synack, and Drupal highlights the ever-evolving threat landscape. Modernizing security practices is crucial, and that includes deploying AI code safety tools like those discussed in Deploying AI Code Safety Goggles Needed. Ultimately, staying ahead of potential vulnerabilities in open-source platforms like Drupal, especially with the increasing reliance on AI, requires proactive strategies like those outlined in the Bitglass report.
Furthermore, granular access controls can limit the attacker’s ability to access and manipulate sensitive data. This proactive approach prevents the attacker from achieving their goal and safeguards the integrity of the Drupal website and its data.
Use Cases and Practical Applications

Integrating Bitglass Security Spotlight with Google Cloud Platform (GCP), Synack Security Research, and Drupal security provides a robust defense strategy against evolving cyber threats. This comprehensive approach empowers organizations to proactively identify and mitigate vulnerabilities, safeguarding sensitive data and critical applications hosted on GCP. This integration offers a powerful platform for enhanced security posture and a layered defense against sophisticated attacks.
Real-World Use Cases for Drupal and GCP Security
Organizations leveraging Drupal on GCP can benefit significantly from integrated security solutions. A hypothetical e-commerce platform, for example, heavily relies on Drupal for its web presence and GCP for hosting. By integrating Bitglass Security Spotlight, they gain real-time visibility into user activity and file transfers, allowing them to quickly identify and respond to suspicious behavior within the Drupal application.
Protecting Sensitive Data within a Drupal Environment
Bitglass Security Spotlight acts as a critical component in safeguarding sensitive data within a Drupal environment. It monitors all data access attempts, both internal and external, providing a granular level of control. For example, if a user attempts to download sensitive customer data outside the permitted parameters, Bitglass will flag the activity for review. This granular control, combined with the threat intelligence provided by Synack, allows for more effective threat hunting and proactive security measures.
Detecting and Preventing Targeted Attacks
By integrating Synack’s security research into the Bitglass Security Spotlight framework, organizations can leverage a proactive threat intelligence feed. This allows for the detection and prevention of targeted attacks that may be specifically tailored to exploit Drupal vulnerabilities. For instance, if Synack identifies a new vulnerability in a Drupal module, Bitglass can immediately alert the organization, allowing them to patch the application before an attacker can exploit it.
This proactive approach minimizes the risk of data breaches and operational disruptions.
Configuring and Deploying Bitglass Security Spotlight
The configuration and deployment of Bitglass Security Spotlight to protect a Drupal website hosted on Google Cloud are straightforward. The initial setup involves integrating Bitglass with the GCP environment. This usually entails setting up API keys and configuring security policies that reflect the specific security needs of the Drupal website. These policies should include granular controls to manage data access, file sharing, and user behavior.
Furthermore, establishing alerts for suspicious activities is crucial for rapid incident response.
Enhanced Security Posture with Integrated Solutions
The combined approach of Bitglass Security Spotlight, Google Cloud Platform, Synack, and Drupal security integrations strengthens the overall security posture of organizations. By providing a unified platform for security monitoring and threat intelligence, these integrations significantly reduce the attack surface and provide proactive defense against sophisticated attacks. This comprehensive approach ensures that organizations using Drupal and GCP have a layered defense against cyber threats.
This strategy ensures the continuous protection of critical assets and data within the Drupal environment.
Security Best Practices and Recommendations: Bitglass Security Spotlight Google Synack Drupal
Integrating Bitglass Security Spotlight with Google Cloud Platform (GCP) and Synack security research enhances your organization’s security posture. These integrations, combined with robust Drupal security practices, provide a layered defense against evolving threats. This section Artikels best practices to maximize the effectiveness of these technologies.Implementing these recommendations is crucial for mitigating risks and maintaining a secure online presence.
A proactive approach to security audits, updates, and hardening significantly reduces the likelihood of successful cyberattacks.
Bitglass Security Spotlight Integration Best Practices
Integrating Bitglass Security Spotlight with GCP and Synack requires a strategic approach. Prioritize establishing clear communication channels between security teams responsible for each platform. This ensures seamless information sharing and coordinated responses to security events. Regularly scheduled security briefings and joint exercises are vital for maintaining alignment and fostering collaboration. This approach enables quick incident response and reduces the window of vulnerability.
- Establish Clear Communication Channels: Establish dedicated communication channels for incident reporting and security updates between Bitglass, GCP, and Synack teams. This facilitates swift information sharing and collaborative responses.
- Implement Automated Alerting Systems: Configure automated alerting systems to notify relevant teams of potential security threats detected by Bitglass, GCP, and Synack integrations. This proactive approach enables rapid response and minimizes the impact of security breaches.
- Regular Security Assessments: Conduct regular security assessments of your GCP environment, focusing on areas where Bitglass Spotlight identifies potential risks. This proactive approach allows you to stay ahead of emerging threats.
Drupal Security Audits and Updates
Regular security audits and updates are essential to maintain a secure Drupal environment. Automated vulnerability scanning tools can help identify potential weaknesses and prioritize remediation efforts. Proactive patching and updates are vital in mitigating known vulnerabilities and ensuring the Drupal site remains resistant to attacks.
- Automated Vulnerability Scanning: Employ automated tools to regularly scan your Drupal environment for vulnerabilities. This proactive approach enables timely identification and mitigation of potential security weaknesses.
- Proactive Patching and Updates: Implement a robust patching strategy to address security vulnerabilities promptly. Prioritize updates for core Drupal components, extensions, and modules.
- Regular Security Audits: Conduct regular security audits to evaluate the effectiveness of your security measures and identify any weaknesses that may have developed since the last audit. This proactive approach ensures a secure Drupal environment.
Drupal Hardening Recommendations
Hardening Drupal websites involves implementing measures to minimize potential vulnerabilities. These recommendations focus on improving the overall security posture of your Drupal website, preventing exploitation by attackers. Restricting access to only authorized personnel and implementing strong authentication measures are essential.
- Access Control Restrictions: Implement strict access control measures to limit access to sensitive data and functionalities. Restrict access to only authorized users and roles.
- Strong Authentication Measures: Utilize strong password policies and multi-factor authentication (MFA) to enhance security. This reduces the risk of unauthorized access.
- Input Validation: Implement robust input validation to prevent cross-site scripting (XSS) and other injection attacks. This safeguards your website from malicious code injection.
Security Assessment Guide
A structured security assessment involves a phased approach. This includes initial reconnaissance, vulnerability scanning, and penetration testing to identify potential threats. Thorough documentation and reporting are crucial for effective threat management.
- Reconnaissance: Begin by identifying potential vulnerabilities by conducting reconnaissance, analyzing publicly available information about your website and associated services.
- Vulnerability Scanning: Employ automated tools to scan for known vulnerabilities in your Drupal environment, identifying potential weak points.
- Penetration Testing: Conduct penetration testing to simulate real-world attacks and assess your website’s resilience to sophisticated threats. This helps identify potential weaknesses and vulnerabilities.
Implementing Security Controls in Integrated Environment
Implementing security controls in a Drupal environment integrated with GCP and Bitglass requires a phased approach. Begin by assessing existing security controls, identifying gaps, and implementing appropriate mitigation strategies. This includes setting up appropriate access controls, implementing strong passwords, and configuring MFA.
- Security Control Assessment: Evaluate existing security controls in your Drupal, GCP, and Bitglass Security Spotlight environment to identify any gaps and weaknesses.
- Gap Analysis and Mitigation: Address identified gaps by implementing appropriate security controls, such as access controls, strong passwords, and multi-factor authentication.
- Monitoring and Reporting: Establish comprehensive monitoring and reporting mechanisms to track security events and identify potential threats.
Wrap-Up
In conclusion, integrating Bitglass Security Spotlight with Google Cloud Platform, Synack, and Drupal offers a robust layered security approach. This comprehensive integration empowers organizations to proactively identify and address security vulnerabilities, strengthening their defenses against targeted attacks and ensuring the protection of sensitive data within their Drupal environments. The use cases, practical applications, and best practices detailed here highlight the potential for improved security posture and peace of mind.
Question & Answer Hub
What specific types of security threats does Bitglass Security Spotlight detect?
Bitglass Security Spotlight can detect various threats, including malware, phishing attempts, and unauthorized access attempts, providing a layered defense against potential breaches.
How does the integration with Synack’s platform enhance proactive security measures?
By integrating with Synack’s security research, Bitglass Security Spotlight can leverage the collective knowledge of a vast network of security researchers to identify and address potential vulnerabilities proactively, enhancing the security posture.
What are some common Drupal security vulnerabilities that Bitglass can help mitigate?
Common Drupal vulnerabilities include cross-site scripting (XSS), SQL injection, and insecure direct object referencing. Bitglass Security Spotlight helps mitigate these vulnerabilities by providing proactive detection and response mechanisms.
What are the key steps to configuring Bitglass Security Spotlight for a Drupal website on GCP?
The specific configuration steps will vary based on the particular setup. However, the process typically involves integration with Google Cloud Platform’s security tools, ensuring compatibility and optimal protection for the Drupal environment.