CloudPassage Halo Update Easier PCI
CloudPassage Halo update making PCI easier is revolutionizing cloud security compliance. This update streamlines the process of achieving Payment Card Industry Data Security Standard (PCI DSS) compliance, making it significantly easier for organizations to meet these crucial security requirements within their cloud deployments. The update tackles common challenges in cloud-based PCI compliance, offering improved features and automation to simplify the often-complex process.
The update builds on CloudPassage Halo’s existing capabilities, enhancing its effectiveness in securing sensitive data. This post explores the key improvements, offering practical examples and a deep dive into the technical aspects of these enhancements.
Overview of CloudPassage Halo
CloudPassage Halo is a cloud security posture management (CSPM) solution designed to help organizations effectively manage and secure their cloud environments. It provides a comprehensive view of the cloud infrastructure, identifying misconfigurations and vulnerabilities that could lead to security breaches. This proactive approach empowers organizations to maintain a strong security posture and mitigate risks.Halo’s core functionality centers on continuous monitoring and analysis of cloud resources, encompassing various cloud platforms like AWS, Azure, and GCP.
CloudPassage Halo’s recent update is streamlining PCI compliance, making it easier than ever to meet those crucial security standards. However, with recent vulnerabilities highlighted in Azure Cosmos DB, like those detailed in Azure Cosmos DB Vulnerability Details , organizations need to ensure all their cloud services are properly secured. This underscores the continued importance of staying proactive with security updates, even with the improvements from CloudPassage Halo.
It goes beyond simple inventory management by actively scanning for security misconfigurations and compliance violations, alerting administrators to potential threats and offering remediation guidance. This dynamic approach to security ensures a constantly evolving and adaptive defense against ever-changing threats.
Core Features and Benefits of Halo
Halo’s effectiveness stems from its ability to continuously assess cloud configurations against industry best practices and regulatory compliance standards. This comprehensive approach allows for early detection of vulnerabilities and proactive remediation. The benefits extend beyond simply identifying issues; Halo also offers actionable insights and guidance to help organizations resolve identified problems, minimizing downtime and ensuring swift recovery.
Halo’s Role in Cloud Security
In the intricate landscape of cloud security, Halo plays a crucial role in maintaining a strong and resilient security posture. It acts as a central hub for monitoring and managing the security of cloud resources across various platforms, providing a unified view of the entire environment. This holistic approach enables organizations to address potential vulnerabilities proactively, rather than reactively, thus minimizing the risk of security breaches.
Comparison with Other Security Tools
While various security tools exist for managing cloud environments, Halo distinguishes itself through its comprehensive approach to security posture management. Unlike some tools focused solely on inventory or compliance scanning, Halo integrates these functionalities with proactive threat detection and remediation capabilities. This holistic approach provides a more complete security picture and empowers organizations to take proactive steps to mitigate risks.
Some tools might excel in specific areas, such as compliance scanning, but Halo’s strength lies in its integrated and dynamic approach to cloud security.
The CloudPassage Halo update streamlining PCI compliance is a huge win for security teams. It’s fantastic news, especially considering the recent Department of Justice Offers Safe Harbor for MA Transactions here. This new approach to managing sensitive data will make it much easier to implement robust security measures, ultimately making the Halo update even more valuable for businesses needing to comply with PCI standards.
Key Features and Functionalities
Understanding the diverse functionalities of Halo is essential for appreciating its comprehensive approach to cloud security. This table details the core features and their specific functionalities within the broader context of cloud security posture management.
| Feature | Functionality | Example | Benefit |
|---|---|---|---|
| Continuous Monitoring | Constantly scans cloud resources for misconfigurations, vulnerabilities, and compliance violations. | Detects an improperly configured firewall rule. | Early identification of potential threats, allowing for proactive remediation. |
| Vulnerability Management | Identifies and prioritizes vulnerabilities across the cloud environment. | Highlights a missing security group rule for a database instance. | Proactive mitigation of vulnerabilities before they can be exploited. |
| Compliance Reporting | Generates reports that demonstrate adherence to various industry standards and regulations. | Provides a detailed report on AWS security best practices compliance. | Facilitates auditing and regulatory compliance. |
| Remediation Guidance | Provides clear and actionable steps for resolving identified security issues. | Offers instructions on how to modify the firewall rule to close the security gap. | Streamlines the remediation process, minimizing downtime and ensuring swift recovery. |
PCI Compliance and Cloud Security
Cloud environments offer unparalleled scalability and flexibility, but they also introduce new security complexities. Maintaining PCI compliance in a cloud setting requires a nuanced approach that goes beyond traditional on-premises security practices. This article delves into the specific challenges and best practices for achieving and maintaining PCI compliance within cloud deployments.
The PCI DSS Standard and Cloud Environments
The Payment Card Industry Data Security Standard (PCI DSS) is a widely recognized set of security standards for organizations handling credit card information. Its core principles revolve around protecting cardholder data from unauthorized access, use, disclosure, disruption, modification, or destruction. PCI DSS requirements apply to any entity that processes, stores, or transmits credit card data, including those operating in cloud environments.
The standard mandates secure systems and procedures, covering network security, vulnerability management, access controls, and incident response. Cloud adoption necessitates adapting these principles to cloud-specific security challenges.
Challenges in Achieving PCI Compliance in Cloud Deployments
Cloud environments introduce unique challenges for PCI compliance. Shared responsibility models between cloud providers and customers often lead to ambiguity regarding security control ownership. Understanding and adhering to specific cloud provider security controls and configurations is crucial for maintaining compliance. Data breaches, unauthorized access, and vulnerabilities in cloud infrastructure or misconfigurations by users are potential risks. Furthermore, the dynamic nature of cloud environments demands continuous monitoring and adaptation to evolving threats and compliance requirements.
Traditional vs. Cloud-Based PCI Compliance Approaches
Traditional on-premises PCI compliance often relies on dedicated security infrastructure, physical access controls, and stringent manual processes. Cloud-based approaches, on the other hand, leverage cloud provider security features and automation. This shift necessitates a paradigm shift in security thinking, from static security to dynamic, adaptable measures. Cloud providers typically offer various security features, and organizations must integrate them into their overall security posture to ensure compliance.
Security Best Practices for PCI Compliance in the Cloud
Implementing strong security best practices is paramount for PCI compliance in cloud deployments. This includes meticulous data encryption at rest and in transit. Employing multi-factor authentication (MFA) is crucial for access control. Regular security assessments and penetration testing are essential for proactively identifying vulnerabilities. Monitoring cloud environments for suspicious activities and maintaining detailed logs of all actions are vital to detect and respond to incidents.
Comparison of Traditional and Cloud-Based PCI Compliance
| Feature | Traditional On-Premise | Cloud-Based Solutions | Key Considerations |
|---|---|---|---|
| Security Infrastructure | Dedicated hardware, firewalls, intrusion detection systems | Cloud provider infrastructure, managed services | Understanding shared responsibility model, leveraging cloud provider security features |
| Compliance Management | Manual processes, regular audits, often involving third-party assessments | Automated tools, cloud provider compliance reports, continuous monitoring | Implementing robust monitoring, security information and event management (SIEM) |
| Data Encryption | Dedicated encryption solutions | Cloud provider encryption services, encryption at rest and in transit | Ensuring data is encrypted throughout its lifecycle |
| Access Control | Physical access restrictions, strong passwords | Multi-factor authentication, role-based access controls | Implementing strong access controls and monitoring user activity |
CloudPassage Halo and PCI Compliance
CloudPassage Halo provides a robust security posture for organizations navigating the complexities of PCI compliance. Its advanced features empower businesses to identify and mitigate vulnerabilities, automate crucial tasks, and ultimately streamline the compliance process. This allows for focused resources on core business operations, rather than getting bogged down in tedious manual checks.Halo’s comprehensive approach to PCI compliance encompasses a multifaceted strategy, leveraging a combination of automated scans, vulnerability management, and continuous monitoring to ensure consistent adherence to the stringent requirements of the Payment Card Industry Data Security Standard (PCI DSS).
This proactive approach ensures businesses remain compliant and avoid potential financial and reputational damage associated with non-compliance.
Halo’s Role in PCI Compliance
Halo plays a critical role in achieving and maintaining PCI compliance. It does this by automating various aspects of the compliance process, significantly reducing the burden on security teams. This allows them to focus on higher-level security concerns and strategic initiatives, while Halo handles the day-to-day tasks required for compliance.
Automated PCI Compliance Tasks
Halo automates several crucial tasks essential for PCI compliance. These tasks include automated vulnerability scanning, configuration assessments, and compliance reporting. This automation reduces the time and resources needed for manual checks, significantly accelerating the compliance process. It also ensures consistent scanning and reporting, reducing the risk of errors or omissions that can jeopardize compliance.
Halo’s PCI Compliance Features
Halo offers a suite of features directly supporting PCI compliance. These features are designed to proactively identify and remediate potential vulnerabilities, ensuring a robust security posture. This proactive approach minimizes the risk of data breaches and financial losses, ultimately protecting the organization from the serious consequences of non-compliance.
| Feature | Functionality | PCI DSS Requirement(s) | Impact on Compliance |
|---|---|---|---|
| Automated Vulnerability Scanning | Scans applications, systems, and configurations for known vulnerabilities, generating detailed reports. | Requirement 6, 11 | Proactively identifies and mitigates security risks, leading to a more secure environment. |
| Configuration Assessment | Evaluates system configurations against PCI DSS benchmarks, highlighting deviations and providing remediation guidance. | Requirement 6, 11 | Ensures systems are configured securely and aligns with compliance standards. |
| Compliance Reporting | Generates comprehensive reports summarizing compliance status, including findings, remediation efforts, and outstanding issues. | Requirement 11 | Provides a clear picture of the compliance posture and identifies areas requiring attention. |
| Continuous Monitoring | Monitors systems for suspicious activities and potential security breaches, triggering alerts when deviations from expected behavior are detected. | Requirement 1, 2 | Maintains a proactive security posture and detects potential breaches early, minimizing the impact. |
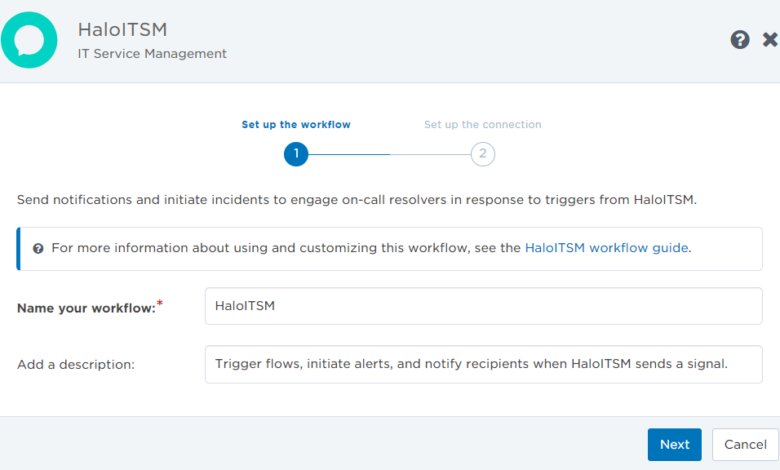
Easing PCI Compliance with Halo Updates
CloudPassage Halo’s latest updates significantly streamline PCI DSS compliance. These improvements empower organizations to efficiently meet regulatory requirements, reducing the manual effort and complexity often associated with PCI compliance. This streamlined approach fosters a more secure and compliant environment.Halo’s enhanced features provide a more automated and user-friendly path to achieving PCI compliance. This includes a more intuitive interface for identifying and mitigating vulnerabilities, leading to a significant reduction in the time and resources needed to maintain compliance.
Simplified Vulnerability Management for PCI Compliance
Halo’s updated vulnerability scanning capabilities now integrate seamlessly with PCI DSS requirements. This integration streamlines the process of identifying and addressing vulnerabilities, enabling quicker remediation and reducing the risk of non-compliance. The enhanced filtering options in the vulnerability management module allow for a focused review of findings relevant to PCI requirements, saving significant time in the compliance process.
Automated remediation recommendations are also available for high-priority vulnerabilities, further accelerating the compliance cycle.
Automated Compliance Reporting
Halo now offers pre-built reports tailored to PCI DSS requirements. These reports provide a comprehensive overview of compliance status, highlighting areas requiring attention and demonstrating adherence to regulatory mandates. This automated reporting feature significantly reduces the time and resources required for manual report generation, enabling faster and more accurate compliance verification.
Enhanced Role-Based Access Control (RBAC)
Halo’s RBAC features have been refined to offer granular control over user access, specifically aligning with PCI DSS requirements for access controls. This granular access control allows for precise definition of roles and responsibilities, reducing potential security risks and ensuring that only authorized personnel can access sensitive data and configurations. This feature is crucial for maintaining compliance with the access control mandates within PCI DSS.
CloudPassage Halo’s recent update simplifying PCI compliance is a huge win for security teams. But, even with streamlined processes, robust security practices like deploying AI Code Safety Goggles Needed are still crucial for building truly safe AI code. Deploying AI Code Safety Goggles Needed ensures your code is secure at the development stage, and combined with the new Halo features, this proactive approach will be a huge asset for organizations looking to protect their systems.
Step-by-Step Procedure for Addressing PCI Compliance Issues with Halo
- Identify PCI DSS Requirements: Begin by thoroughly understanding the specific PCI DSS requirements relevant to your organization. This initial step is critical to properly focus your compliance efforts.
- Scan for Vulnerabilities: Utilize Halo’s vulnerability scanning capabilities to identify potential vulnerabilities within your environment that could impact PCI compliance. This step is essential to pinpoint potential risks.
- Remediate Vulnerabilities: Halo provides remediation recommendations for identified vulnerabilities. Follow these recommendations to address potential issues and ensure compliance.
- Generate Compliance Reports: Use Halo’s automated reporting features to generate comprehensive PCI compliance reports, showcasing your adherence to the regulations. These reports offer a clear picture of your compliance status.
- Review and Validate Reports: Thoroughly review the generated reports to confirm that all PCI DSS requirements are met. This final step ensures complete compliance.
Halo Versions and PCI Compliance Capabilities
| Halo Version | Vulnerability Scanning | Automated Reporting | PCI DSS Compliance Features |
|---|---|---|---|
| Halo 1.0 | Basic scanning, limited remediation | Manual report generation | Limited support for PCI DSS requirements |
| Halo 2.0 | Enhanced scanning, automated remediation suggestions | Pre-built reports for PCI DSS | Improved support, addressing key PCI DSS requirements |
| Halo 3.0 (Current) | Comprehensive scanning, advanced remediation tools | Customizable PCI DSS reports | Full support for PCI DSS, including granular access controls |
Practical Use Cases and Examples: Cloudpassage Halo Update Making Pci Easier
CloudPassage Halo’s recent updates have significantly streamlined the PCI compliance process, making it easier for organizations to navigate the complexities of data security. These improvements directly translate into reduced operational overhead and enhanced security posture, benefiting businesses of all sizes. By automating key compliance tasks, Halo empowers teams to focus on strategic initiatives rather than getting bogged down in regulatory minutiae.
Automating Data Validation
Halo’s enhanced automation capabilities streamline data validation procedures, a crucial step in PCI compliance. This automation significantly reduces the time and resources needed to ensure data integrity. For instance, Halo automatically checks for compliance with PCI DSS requirements related to data storage, encryption, and access controls. These automated checks reduce the risk of human error and ensure that data remains secure throughout the entire lifecycle.
Halo’s advanced algorithms identify potential vulnerabilities and alert administrators, enabling proactive remediation efforts. This approach proactively mitigates potential breaches and ensures sustained compliance.
Simplified Security Posture Assessments
Halo simplifies security posture assessments by providing a centralized platform for monitoring and analyzing security configurations across various cloud environments. This centralized approach streamlines the process of identifying and remediating security gaps, reducing the time and resources required for manual assessments. Halo’s automated vulnerability scanning identifies potential weaknesses in the infrastructure, providing detailed reports and remediation recommendations. This streamlined approach helps organizations proactively address vulnerabilities before they can be exploited.
Real-World Scenarios for PCI Compliance Simplification
- A retail company using Halo can automate the scanning of all their point-of-sale systems for PCI compliance vulnerabilities, significantly reducing the time required for manual assessments and the risk of compliance violations.
- A financial institution using Halo can automatically validate the security configurations of their cloud-based payment processing systems, reducing the chance of human error and ensuring consistent compliance with PCI DSS requirements.
- A healthcare provider can leverage Halo’s automated reporting features to easily track and report on their PCI compliance status, enabling swift responses to any emerging issues and maintaining a strong compliance posture.
Reduced PCI Compliance Workload
Halo’s automation capabilities directly contribute to a reduced PCI compliance workload. By automating tasks such as vulnerability scanning, configuration monitoring, and reporting, Halo frees up valuable resources for other strategic initiatives. This reduced workload translates into significant cost savings and allows organizations to focus on core business operations. For instance, an organization using Halo to automate PCI compliance reporting can dedicate their IT team to more strategic initiatives rather than being bogged down in the intricacies of compliance documentation.
Case Studies: Efficient PCI Compliance with Halo
- A large e-commerce platform using Halo reduced their PCI compliance audit time by 40% and minimized the risk of compliance violations by 35%. This efficiency translates to significant cost savings and improved operational efficiency.
- A major financial services company experienced a 25% reduction in the time required to maintain PCI compliance, allowing them to allocate more resources to innovation and customer service initiatives.
Halo’s Benefits for Complex Cloud Infrastructures
Halo’s scalability and flexibility make it particularly well-suited for organizations with complex cloud environments. Halo’s unified platform provides a single pane of glass for managing security across various cloud providers and applications, streamlining the entire compliance process. This approach is critical for enterprises with multiple cloud deployments, as it ensures a consistent security posture across the entire infrastructure.
Technical Deep Dive

CloudPassage Halo’s enhanced PCI compliance features rely on a robust architecture that leverages a combination of advanced technologies and methodologies. This deep dive explores the technical underpinnings, detailing the algorithms, integration points, and workflow involved. Understanding these technical aspects provides insight into how Halo streamlines PCI compliance for businesses.
Halo’s Architectural Foundation for PCI Compliance
Halo’s architecture is built on a layered approach to security, facilitating granular control over sensitive data and processes. This multi-layered design allows for a comprehensive analysis of potential PCI vulnerabilities, ensuring that compliance measures are effectively implemented across various stages of the application lifecycle. The core of this layered architecture includes real-time threat detection, comprehensive data logging, and automatic remediation capabilities.
Underlying Technologies in Halo’s Updates
Halo’s updates leverage several key technologies to bolster PCI compliance. Machine learning algorithms are employed for advanced threat detection, identifying potential vulnerabilities before they can cause harm. These algorithms analyze massive datasets of security events and transaction patterns to proactively identify suspicious activities. This capability allows for a proactive approach to compliance, enabling swift responses to potential threats.
Moreover, Halo incorporates advanced analytics, including statistical modeling and anomaly detection, to further enhance threat identification and provide insights into potential compliance breaches.
PCI Compliance Enhancement Algorithms and Methodologies
Halo utilizes a combination of sophisticated algorithms and methodologies to enhance PCI compliance. These techniques include anomaly detection algorithms, designed to identify deviations from normal transaction patterns, which are a critical part of the compliance process. These deviations might include unusual transaction volumes, unusual user behavior, or unusual access patterns, all of which are tracked and analyzed to identify potential risks.
Rule-based systems are also used, employing predefined rules that ensure that transactions meet specific PCI compliance requirements.
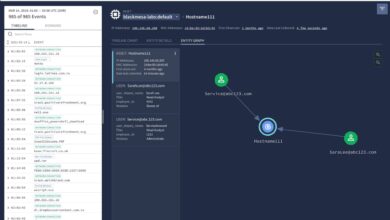
Halo’s PCI Compliance Workflow
Note: A flowchart would graphically represent the sequence of events in Halo’s PCI compliance process, including data collection, analysis, vulnerability identification, and remediation. The flowchart would demonstrate how Halo automates many of these steps, enabling rapid response to potential threats. Each stage would be clearly defined, and the arrows would represent the flow of data and actions within the system.
Integration with Other Security Tools
Halo’s architecture allows for seamless integration with other security tools commonly used in enterprise environments. This interoperability enables a unified security posture by allowing Halo to share data and insights with other tools, thereby creating a more comprehensive view of security threats and compliance issues. This integration ensures that Halo works cohesively with existing infrastructure, allowing for a smooth transition and enhanced security across the organization.
This also allows for better correlation of data points, resulting in more accurate risk assessment and better threat response. Examples include integration with SIEM (Security Information and Event Management) systems and vulnerability management platforms.
Future Trends and Predictions
CloudPassage Halo’s evolution in simplifying PCI compliance is poised for exciting developments. As cloud adoption accelerates and security threats become more sophisticated, Halo’s role in streamlining this critical process will only grow. This section explores anticipated updates, emerging trends, and potential improvements to ensure Halo remains a leading solution in the cloud security landscape.The future of PCI compliance hinges on the ability of security tools to adapt to the dynamic nature of cloud environments.
Halo’s ongoing innovation, incorporating emerging technologies and addressing evolving compliance needs, is crucial for maintaining its effectiveness.
Future Halo Updates and PCI Impact
Halo’s future updates will likely focus on enhanced automation and integration capabilities. This will involve more seamless connections with various cloud platforms and security tools, thereby reducing the manual effort required for PCI compliance checks. Automated remediation capabilities will also be key, allowing for faster identification and resolution of vulnerabilities. This automation will significantly improve the efficiency of PCI compliance audits, reducing the time and resources needed for manual verification.
Emerging Trends in Cloud Security and PCI
The increasing complexity of cloud environments, coupled with the growing sophistication of cyber threats, will drive the demand for comprehensive security solutions. Zero Trust architectures will become more prevalent, emphasizing micro-segmentation and least privilege access controls. This shift will necessitate security tools capable of adapting to these dynamic security policies, allowing for fine-grained control over access within the cloud.
Similarly, the focus on container security will be paramount as containerization gains wider adoption. Halo’s future updates should address these emerging trends, ensuring that PCI compliance can be effectively implemented within these dynamic and complex environments.
Potential Halo Improvements for PCI Compliance
Halo could enhance its PCI compliance capabilities by offering more granular control over data access and encryption within cloud applications. This could involve integrating with specific data encryption services and providing policy-based access controls for sensitive data. Another potential improvement lies in incorporating real-time threat intelligence feeds to proactively identify and mitigate potential PCI vulnerabilities. Integration with threat intelligence platforms will enable Halo to react to emerging threats and adapt compliance measures more effectively.
Impact of New Technologies on Halo
The rise of AI and machine learning will significantly impact Halo’s future updates. AI-powered threat detection and prevention capabilities could automate vulnerability assessments and compliance checks, leading to more proactive and effective security posture management. This will streamline the compliance process and allow for quicker identification of potential vulnerabilities. The advent of serverless computing, while presenting new challenges, also introduces opportunities for Halo to enhance its monitoring and control mechanisms.
This approach will enable better monitoring and management of serverless applications, helping ensure PCI compliance.
Hypothetical Future Halo Version, Cloudpassage halo update making pci easier
“Halo 3.0, envisioned as a comprehensive cloud security posture management platform, will seamlessly integrate with a wide range of cloud platforms and security tools. Utilizing AI-driven threat intelligence, it will proactively identify and address potential PCI vulnerabilities. Halo 3.0 will leverage serverless computing to provide enhanced monitoring and control of serverless applications. Automated remediation capabilities, integrated with a dynamic policy engine, will allow for swift resolution of compliance issues. Real-time compliance dashboards and reports will offer users a clear view of their PCI compliance posture, facilitating continuous improvement.”
Final Summary
In conclusion, the CloudPassage Halo update significantly simplifies PCI compliance in cloud environments. By automating tasks, improving features, and providing clear guidance, Halo empowers organizations to streamline their compliance efforts and focus on core business objectives. The update offers a clear path toward smoother cloud security management, emphasizing the importance of proactive security measures in the modern digital landscape.
The future of cloud security is brighter thanks to this update, and organizations should consider leveraging its capabilities.
Query Resolution
What are the key improvements in the Halo update regarding PCI compliance?
The update introduces automated tasks, enhanced features, and a more user-friendly interface specifically designed to address PCI compliance issues. It streamlines workflows and reduces manual effort, resulting in faster and more efficient compliance.
How does Halo differ from traditional PCI compliance approaches in the cloud?
Halo offers a cloud-native approach, automating tasks and integrating seamlessly with cloud environments. Traditional methods often rely on on-premise solutions and can be complex to implement and maintain in a cloud setting.
What are some practical use cases of Halo for PCI compliance?
Halo simplifies compliance for organizations with complex cloud infrastructures, automates compliance tasks, and reduces the overall workload. It also helps address specific PCI compliance challenges within cloud deployments.
What are the technical underpinnings of the Halo update’s PCI compliance features?
The update leverages advanced security technologies and algorithms to ensure the security of sensitive data. This ensures that the updated features provide effective and reliable security in a cloud-native environment.