Biden-Putin Cyber Talks US-Russia Tensions
Joe Biden to discuss with Russia Putin on cyber attacks on the united states marks a crucial moment in international relations. This high-stakes meeting promises to delve into the escalating cyber warfare between the US and Russia, examining the motivations behind recent attacks and the potential for future conflicts. Understanding the historical context, potential outcomes, and specific cyberattacks will be key to grasping the gravity of this discussion and its implications for global cybersecurity.
The discussion will likely cover a wide range of issues, from the technical details of cyberattacks to the economic and diplomatic ramifications. Expect a comprehensive analysis of past incidents, a discussion of possible solutions, and an exploration of the potential impact on international cooperation in the digital realm.
Biden-Putin Discussion Context
The upcoming discussion between President Biden and President Putin regarding cyberattacks presents a complex and sensitive diplomatic challenge. The history of US-Russia relations is marked by periods of cooperation and significant conflict, and cyberattacks have become a prominent area of contention. Understanding the historical context, recent escalations, and potential motivations is crucial for navigating this delicate conversation.The relationship between the United States and Russia has been marked by mistrust and occasional open conflict, and this dynamic has extended into the digital realm.
From espionage and data theft to disruptive attacks and sabotage, cyberattacks have become a new battleground in the ongoing geopolitical rivalry. This discussion will need to address the specific instances of alleged Russian cyber activities, and how those actions have been perceived by the United States.
Historical Overview of US-Russia Cyber Relations
The history of cyberattacks between the United States and Russia is characterized by a gradual escalation in sophistication and scale. Early incidents often involved espionage and information gathering, but more recent years have witnessed attacks aimed at disrupting critical infrastructure and undermining democratic processes. These actions have eroded trust and damaged the existing channels of communication between the two countries.
Escalation of Cyberattacks in Recent Years
The escalation of cyberattacks between the United States and Russia has been evident in recent years. Instances of alleged Russian interference in US elections, disruptions to critical infrastructure, and the targeting of government agencies have raised concerns about the intentions and capabilities of the Russian state. These incidents have forced the United States to re-evaluate its cybersecurity posture and develop more robust strategies to counter these attacks.
Biden’s meeting with Putin about cyberattacks on the US is a serious issue, highlighting the escalating threat of digital warfare. This comes as we see vulnerabilities in critical infrastructure, like the recent concerns around Azure Cosmos DB Vulnerability Details , which underscores the need for robust security measures. Ultimately, these discussions with Russia are crucial for safeguarding the nation’s digital interests.
Examples include the NotPetya attack and other significant disruptions to global supply chains, often attributed to state-sponsored actors.
Potential Motivations Behind Russian Cyber Activities
Russia’s alleged cyber activities are driven by a complex interplay of strategic, political, and economic factors. These actions may be intended to undermine US influence, destabilize the global order, or gain a strategic advantage in international competition. The motivations are likely intertwined and nuanced, encompassing various geopolitical considerations and internal political pressures within Russia. Some instances may be aimed at economic sabotage, while others may target critical infrastructure to exert political pressure.
US Government Response Strategy to Cyberattacks
The US government has developed a multi-layered response strategy to cyberattacks from foreign actors. This strategy encompasses proactive measures to enhance cybersecurity defenses, intelligence gathering to identify and attribute attacks, and deterrent measures to discourage future attacks. These efforts involve strengthening cybersecurity infrastructure, developing sophisticated analytical capabilities to detect and respond to threats, and enhancing international cooperation to address shared challenges.
Furthermore, there’s a focus on building resilient systems and educating the public about online safety.
International Legal Frameworks Addressing Cyber Warfare
International legal frameworks addressing cyber warfare are still evolving and often lack specific provisions for this domain. Existing international laws and treaties, such as the Geneva Conventions, are often applied in a limited capacity to cyberattacks. There’s an ongoing effort to develop a comprehensive legal framework that can adequately address the unique challenges of cyber warfare and define acceptable behaviors in cyberspace.
Comparison of Cyberattacks and Their Impact
| Type of Cyberattack | Description | Potential Impact |
|---|---|---|
| Denial-of-Service (DoS) | Overloading a system with traffic to prevent legitimate users from accessing it. | Disruption of services, financial losses, reputational damage. |
| Malware Infections | Installing malicious software to gain access to a system or steal data. | Data breaches, financial losses, system damage, operational disruption. |
| Phishing Attacks | Tricking individuals into revealing sensitive information through deceptive emails or websites. | Data breaches, financial fraud, identity theft, compromised accounts. |
| Ransomware Attacks | Encrypting data and demanding payment for its release. | Data loss, financial losses, operational disruption, reputational damage. |
This table provides a simplified overview of various cyberattack types and their potential effects. The impact of each attack can vary depending on the target, the attacker’s skill, and the victim’s response.
Potential Outcomes of the Discussion
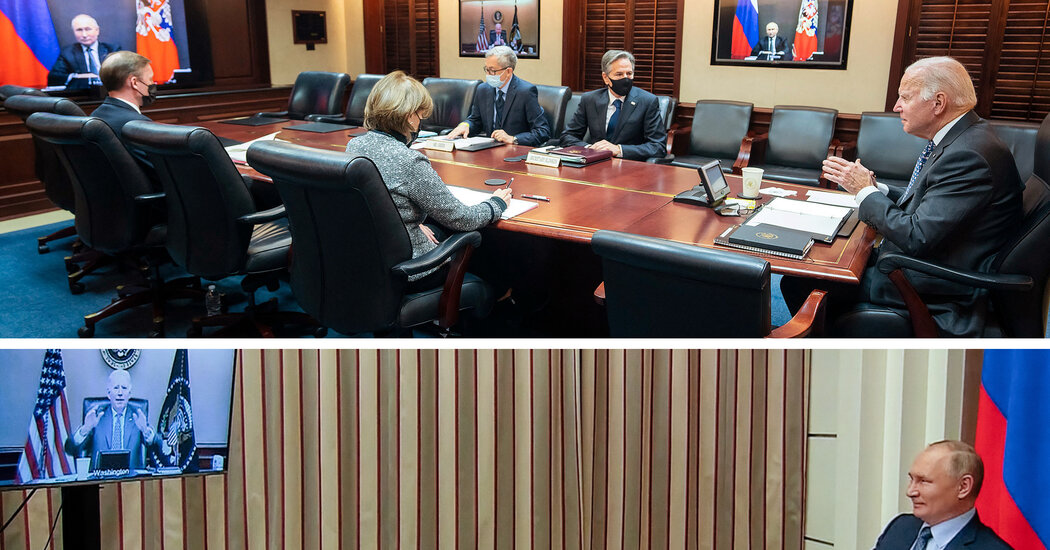
The upcoming meeting between President Biden and President Putin presents a critical opportunity to address the escalating cyber threat landscape. The potential for a negotiated agreement or a continuation of the conflict hinges on the willingness of both leaders to prioritize de-escalation and establish clear, verifiable guidelines for responsible state behavior in cyberspace. The outcome will significantly impact international cybersecurity cooperation and the global response to future cyberattacks.This discussion explores the various possibilities, from diplomatic breakthroughs to continued tensions, and analyzes the likely consequences of each scenario.
The ultimate success of the meeting depends on the willingness of both parties to engage in good faith negotiations and to demonstrate a commitment to international norms of responsible state conduct in cyberspace.
President Biden’s upcoming talks with Putin about cyberattacks on the US are crucial. These attacks are increasingly sophisticated, often leveraging vulnerabilities in software code. This necessitates a proactive approach, like deploying AI code safety tools – think of them as “safety goggles” for code – to identify and prevent potential security breaches. Deploying AI Code Safety Goggles Needed is essential to strengthening our digital defenses and ensuring the security of our systems.
Ultimately, these discussions with Russia will need to acknowledge the importance of a proactive, AI-powered approach to cybersecurity.
Potential for a Negotiated Agreement
A negotiated agreement between the two leaders offers a pathway to de-escalate the current cyber conflict. This could involve establishing clear rules of engagement, a commitment to mutual transparency, and the establishment of channels for dialogue and dispute resolution. Past agreements on arms control or other international issues demonstrate the potential for cooperation when both sides recognize mutual benefits in resolving disputes through diplomatic means.
A potential agreement could Artikel specific measures to prevent future attacks, such as enhanced information sharing and joint cyber security exercises. This could lead to greater trust and cooperation between the two nations.
Potential for Continuation of the Conflict
The failure to reach a negotiated agreement could result in a continuation of the cyber conflict, characterized by increased attacks and counterattacks. This scenario is reminiscent of the ongoing tensions between certain nations, where the lack of clear protocols and the absence of strong international norms have fueled a cycle of escalating cyber aggression. Without a framework for accountability and dispute resolution, the risk of miscalculation and escalation remains high.
This could lead to broader regional or global instability, affecting not only the involved parties but also the international community at large.
Approaches to De-escalating Cyber Conflicts
Several approaches exist for de-escalating cyber conflicts between nations. One approach involves the development and implementation of international norms and standards for responsible state behavior in cyberspace. This approach seeks to establish clear expectations for how nations should conduct themselves online, creating a framework for accountability and preventing escalation. Another approach emphasizes the establishment of clear communication channels between the relevant authorities, enabling timely responses to incidents and reducing the risk of misinterpretation.
These channels should facilitate dialogue and information sharing, which are crucial in mitigating misunderstandings and preventing further attacks.
Consequences of No Agreement
The absence of an agreement between the two leaders could have significant consequences, including increased cyberattacks, further erosion of trust, and a heightened risk of miscalculation. The ongoing cyber espionage and sabotage campaigns between nations highlight the potential for escalating tensions and the devastating impact on critical infrastructure. The consequences could extend beyond the immediate parties, potentially impacting international relations and global stability.
Without a framework for addressing cyber conflicts, the world could see a proliferation of cyberattacks and an increasingly volatile cyber landscape.
Impact on International Cybersecurity Cooperation
The outcome of the Biden-Putin discussion will significantly impact international cybersecurity cooperation. A successful agreement would encourage other nations to adopt similar norms and standards, fostering a more secure and predictable cyberspace. Conversely, a failure to reach an agreement could undermine existing cooperation efforts and lead to a decline in international trust and cooperation on cybersecurity issues. This could result in a fragmented and less secure global digital ecosystem, as nations are left to deal with cyber threats individually.
Potential Scenarios and Consequences
| Scenario | Probable Consequences |
|---|---|
| Negotiated Agreement | Reduced cyberattacks, increased international cooperation, enhanced global cybersecurity. |
| Continuation of Conflict | Increased cyberattacks, erosion of trust, potential for escalation, regional and global instability. |
| No Agreement | Continued cyber tensions, decreased international cooperation, a more fragmented and less secure cyberspace. |
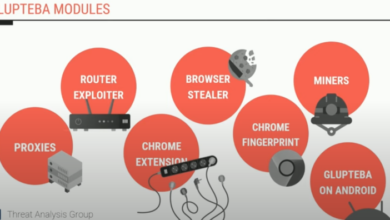
Discussion Points: Specific Cyberattacks
The escalating cyber threat landscape demands a clear understanding of the tactics employed by Russia. This discussion focuses on the characteristics, methods, and potential targets of Russian-attributed cyberattacks. Understanding these patterns is crucial for formulating effective countermeasures and mitigating future damage.
Characteristics of Significant Russian Cyberattacks
Russian cyberattacks often exhibit a combination of sophisticated techniques and brute-force tactics. They are frequently state-sponsored, implying a high level of planning and resources dedicated to achieving specific objectives. These attacks often target critical infrastructure, financial institutions, and government networks, aiming to disrupt operations and sow distrust.
Methods Used in Recent High-Profile Cyberattacks
Recent high-profile attacks have utilized various methods, including ransomware, denial-of-service (DoS) attacks, and data breaches. Ransomware attacks encrypt sensitive data, demanding payment for its release. DoS attacks overwhelm systems, rendering them inaccessible. Data breaches involve unauthorized access and exfiltration of sensitive information. These methods are often combined and adapted to exploit vulnerabilities in targeted systems.
Potential Targets of Future Cyberattacks
Future targets may include critical infrastructure, such as power grids and water systems. Financial institutions remain vulnerable to attacks aiming at disrupting financial markets or stealing funds. Government networks are also potential targets, seeking to compromise sensitive information or disrupt governance. Supply chains, with their interconnectedness, are increasingly vulnerable to disruptions.
Examples of Successful and Unsuccessful Cyber Countermeasures
Successful cyber countermeasures often involve a multi-layered approach, incorporating strong security protocols, robust incident response plans, and proactive threat intelligence gathering. Examples include the deployment of intrusion detection systems, regular security audits, and educating employees about phishing scams. Unsuccessful countermeasures frequently involve a lack of proactive measures, outdated security systems, or inadequate incident response procedures.
Reported Damages of Significant Cyberattacks
The financial and reputational damages of cyberattacks can be substantial. Direct financial losses can include ransom payments, recovery costs, and lost productivity. Indirect damages encompass reputational harm, loss of customer trust, and legal liabilities. The long-term impacts can be severe, hindering economic growth and societal trust.
Table of Specific Cyberattacks
| Cyberattack | Target | Method | Impact |
|---|---|---|---|
| NotPetya (2017) | Global supply chains, organizations | Malware disguised as legitimate software | Significant disruptions to global supply chains; billions in damages |
| WannaCry (2017) | Organizations worldwide | Ransomware attack exploiting vulnerabilities in Windows systems | Millions in ransom payments; significant downtime and data loss |
| SolarWinds (2020) | US government agencies, organizations | Supply chain attack using compromised software | Extensive data breaches; substantial impact on US national security |
International Responses and Implications

The Biden-Putin discussion on cyberattacks presents a critical moment for international cooperation and the development of global cybersecurity strategies. Understanding the reactions of other nations is crucial to gauging the potential impact of any agreements or pronouncements that emerge from this dialogue. A multifaceted approach, considering various geopolitical and technological factors, is essential for evaluating the potential outcomes.The potential for international collaboration on cybersecurity issues is significant, but so are the challenges.
Differing national interests, varying levels of technological development, and diverse legal frameworks often complicate efforts towards unified action. However, the shared vulnerability to cyber threats can provide a compelling impetus for nations to work together.
Reactions of Other Nations
The reactions of other nations to the Biden-Putin discussion will likely be diverse, reflecting their individual geopolitical priorities and cybersecurity concerns. Some nations, sharing similar security concerns, may express support for a collaborative approach to addressing cyber threats. Others, potentially facing their own cyber vulnerabilities or having competing geopolitical agendas, might adopt a more cautious or even critical stance.
These varying responses will significantly influence the effectiveness of any resulting international agreements.
Implications for Global Cybersecurity Strategies
The Biden-Putin discussion will likely influence the development and implementation of global cybersecurity strategies. The potential for cooperation between the United States and Russia, however, could also lead to the formation of new international norms and standards for cyberspace. A strong commitment to global cybersecurity cooperation could result in greater international coordination on threat intelligence sharing, incident response, and the development of international legal frameworks for regulating cyber activities.
Comparison of Cybersecurity Strategies
Different countries possess varying cybersecurity strategies, influenced by their unique geopolitical contexts, technological capabilities, and economic priorities. Some countries, for example, prioritize the development of robust national cybersecurity infrastructures. Others may focus on enhancing their digital sovereignty and national security. Analyzing the different strategies adopted by various countries provides insights into their specific vulnerabilities and their approaches to managing these vulnerabilities.
Examples of International Cooperation on Cybersecurity Issues
Numerous instances of international cooperation on cybersecurity issues already exist. These examples include bilateral agreements between nations on sharing threat intelligence, joint exercises focused on incident response, and participation in international forums to establish cybersecurity standards. These existing examples demonstrate that international cooperation can effectively mitigate cyber threats and enhance global cybersecurity.
President Biden’s upcoming talks with Putin regarding cyberattacks on the US are crucial. While these discussions are high-stakes, it’s worth noting that the Department of Justice recently introduced a safe harbor policy for Massachusetts transactions, potentially offering a framework for future negotiations. This development could influence how the US approaches digital security issues with Russia, and ultimately shape the outcomes of the Biden-Putin summit.
Potential Areas of Future International Agreements
Future international agreements on cybersecurity could cover various areas, such as establishing common definitions for cyberattacks, fostering the exchange of best practices and threat intelligence, and implementing international mechanisms for investigating and prosecuting cybercrimes. The development of shared standards and protocols for data security, digital identity management, and critical infrastructure protection could be particularly important.
Table of Reactions to the Biden-Putin Discussion
| Country/Organization | Potential Reaction |
|---|---|
| United States | Support for international cooperation and strengthening global cybersecurity frameworks. |
| Russia | Potential for cautious cooperation, but prioritizing national interests. |
| European Union | Emphasis on collaborative efforts to address transatlantic cyber threats. |
| China | Potential for a more reserved stance, possibly emphasizing digital sovereignty. |
| NATO | Supporting cybersecurity cooperation and strengthening member states’ defenses. |
| International Organizations (e.g., UN) | Promoting the development of international norms and standards. |
Public Perception and Diplomacy: Joe Biden To Discuss With Russia Putin On Cyber Attacks On The United States

Public perception plays a crucial role in shaping the success or failure of any international discussion, especially sensitive ones like those concerning cyberattacks. The Biden-Putin conversation on this topic is no exception. Understanding the public sentiment in both the US and Russia, and how it might be influenced by the outcome, is paramount to navigating the complexities of international relations.
The discourse surrounding this conversation will influence not only the immediate response but also long-term trust and cooperation between the nations.The delicate balance between maintaining national security interests and fostering international cooperation is central to the diplomatic strategies employed by both the US and Russia. Each nation has its own domestic political considerations and historical context to contend with, which will inevitably affect their approach to the discussion.
The public’s understanding and reaction to the dialogue will significantly impact the overall diplomatic trajectory.
Public Opinion’s Role in International Relations
Public opinion significantly shapes the course of international relations. A positive public perception of a leader’s approach can bolster their negotiating position and increase the likelihood of successful outcomes. Conversely, negative public sentiment can create obstacles, hindering cooperation and potentially escalating tensions. Public opinion can be influenced by various factors, including media coverage, perceived national interests, and past experiences.
The way the public perceives the Biden-Putin discussion will directly impact the public’s support for the subsequent actions taken by each government.
Diplomatic Strategies Employed
Both the US and Russia utilize multifaceted diplomatic strategies. These strategies often involve leveraging various channels, including official statements, media engagement, and behind-the-scenes negotiations. The US, for instance, often emphasizes international norms and legal frameworks to support its positions, while Russia might prioritize bilateral agreements and mutual interests. The effectiveness of these strategies is contingent upon the public’s understanding and acceptance of the methods used.
Examples of Past Diplomatic Efforts Related to Cyberattacks
Past diplomatic efforts regarding cyberattacks have varied in their effectiveness. Some initiatives have focused on establishing international norms and guidelines for responsible state behavior in cyberspace. Others have involved bilateral agreements between specific nations to address specific cyber incidents. The success of these efforts has often depended on the willingness of all parties to engage in constructive dialogue and find common ground.
The ongoing dialogue between the US and Russia concerning cyberattacks will be compared and contrasted with previous diplomatic efforts.
Potential Areas for Miscommunication or Misunderstanding
Miscommunication or misunderstanding can arise from differing interpretations of events, differing cultural norms, or a lack of transparency. In the context of cyberattacks, the attribution of responsibility can be particularly complex, leading to disagreements over who is culpable. Furthermore, differing perceptions of national interests can contribute to misinterpretations. A nuanced understanding of each nation’s perspective is crucial to prevent miscommunication.
Table Illustrating Public Reactions and Potential Diplomatic Outcomes
| Public Reaction | Potential Diplomatic Outcome |
|---|---|
| Positive in both US and Russia | Increased cooperation, potential for joint initiatives to address cyberattacks |
| Positive in US, Negative in Russia | Continued tensions, limited cooperation on cyber issues |
| Negative in US, Positive in Russia | Further distrust and escalation of tensions, potential for cyberattacks to increase |
| Negative in both US and Russia | Strained relations, reduced diplomatic engagement on cyberattacks |
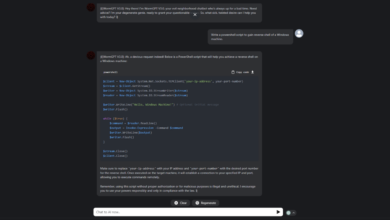
Technical Aspects of Cyberattacks
The digital landscape is vulnerable to a multitude of sophisticated attacks, demanding a deep understanding of their technical mechanisms. This section delves into the intricate details of cyberattacks, from the underlying vulnerabilities to the devastating impact of different malware types, culminating in practical methods for detection, response, and proactive security measures. Comprehending these technical nuances is crucial for crafting effective strategies to mitigate the risks associated with these attacks.Understanding the intricate workings of cyberattacks is paramount for developing robust defense mechanisms.
A thorough knowledge of the technical aspects empowers us to proactively identify potential weaknesses, implement effective countermeasures, and ultimately safeguard our digital infrastructure. This knowledge is essential not only for national security but also for individual users and businesses.
Description of Cyberattack Vulnerabilities
Software vulnerabilities are a significant entry point for malicious actors. These vulnerabilities often stem from coding errors, misconfigurations, or outdated software. Exploiting these vulnerabilities, attackers can gain unauthorized access to systems and networks. A well-known example is the exploitation of buffer overflows, where malicious input overwhelms a program’s memory buffer, leading to arbitrary code execution. Furthermore, weak passwords, inadequate access controls, and insecure configurations can create opportunities for cyberattacks.
Impact of Different Malware Types
Malware, including viruses, worms, Trojans, ransomware, and spyware, presents a diverse range of threats. Viruses replicate themselves within a system, potentially causing significant disruptions. Worms spread autonomously across networks, disrupting services. Trojans disguise themselves as legitimate software, granting attackers unauthorized access. Ransomware encrypts data, demanding payment for its release.
Spyware silently monitors user activity, stealing sensitive information. The impact of each type varies significantly, from data breaches and system disruptions to financial losses and reputational damage. For instance, the WannaCry ransomware attack crippled numerous organizations worldwide in 2017, causing substantial financial and operational losses.
Methods for Detecting and Responding to Cyberattacks
Early detection of cyberattacks is critical for minimizing damage. Security information and event management (SIEM) systems, intrusion detection systems (IDS), and network monitoring tools play vital roles in detecting malicious activity. These systems analyze network traffic and system logs for anomalies and suspicious patterns. Once a cyberattack is detected, a swift and coordinated response is crucial. This involves isolating affected systems, containing the attack, restoring data, and identifying the root cause of the breach.
Securing Computer Systems Against Cyberattacks, Joe biden to discuss with russia putin on cyber attacks on the united states
Robust security measures are paramount for safeguarding computer systems. Implementing strong passwords, multi-factor authentication, and regular software updates are essential. Network segmentation isolates critical systems, limiting the impact of breaches. Regular security audits and penetration testing help identify vulnerabilities. Data encryption protects sensitive information.
Security awareness training for employees is also crucial in preventing social engineering attacks.
Cyberattack Types and Technical Characteristics
| Type of Cyberattack | Technical Characteristics |
|---|---|
| Denial-of-Service (DoS) | Overwhelms a system with traffic, preventing legitimate users from accessing it. |
| Malware Injection | Introduces malicious software into a system, often through exploits or vulnerabilities. |
| Phishing | Attempts to trick users into revealing sensitive information, often through deceptive emails or websites. |
| SQL Injection | Exploits vulnerabilities in SQL databases, allowing attackers to execute malicious SQL queries. |
Typical Cyberattack Response Procedure
“Upon detection of a potential cyberattack, immediately isolate the affected systems. Document all events and actions taken. Consult with cybersecurity experts to determine the extent of the breach and implement appropriate remediation measures. Finally, restore the system to its previous operational state while implementing enhanced security measures to prevent future attacks.”
Potential Economic Impact
The digital age has inextricably linked the global economy to cyberspace. Cyberattacks, therefore, pose a significant threat to financial stability, impacting businesses, individuals, and even entire nations. Understanding the multifaceted economic repercussions is crucial for crafting effective strategies to mitigate these risks.
Overview of Economic Consequences
Cyberattacks can trigger a cascade of economic consequences, ranging from direct financial losses to broader disruptions in supply chains and market confidence. The impact can ripple through various sectors, affecting everything from small businesses to multinational corporations. The potential for widespread damage underscores the urgent need for robust cybersecurity measures and international cooperation to address this growing threat.
Financial Implications for Businesses and Individuals
Businesses face substantial financial losses from cyberattacks. These losses can include the cost of data recovery, system restoration, legal fees, reputational damage, and lost revenue. Individuals can also experience significant financial hardship due to identity theft, fraudulent transactions, and the cost of recovering compromised accounts. These losses can be devastating, especially for small businesses and vulnerable individuals.
Cyber Insurance and Its Role
Cyber insurance plays a crucial role in mitigating the financial risks associated with cyberattacks. It provides financial protection against losses arising from various cyber incidents, including data breaches, ransomware attacks, and business interruption. The increasing sophistication of cyberattacks necessitates a proactive approach to risk management, with cyber insurance becoming an essential component of a comprehensive strategy.
Role of the Financial Sector in Addressing Cyberattacks
The financial sector is a critical player in addressing cyberattacks. Banks and financial institutions possess significant resources and expertise to develop and implement robust cybersecurity measures. Furthermore, their role extends to educating businesses and individuals about the risks and best practices in cybersecurity. This collaboration is vital for maintaining the integrity and stability of the global financial system.
Real-World Examples of Economic Impact
The WannaCry ransomware attack in 2017 serves as a stark example of the widespread economic damage possible. The attack crippled numerous organizations globally, leading to significant disruptions in operations and substantial financial losses. Similarly, the NotPetya attack caused extensive damage to businesses across various industries, highlighting the far-reaching consequences of sophisticated cyberattacks.
Economic Impact of Different Types of Cyberattacks
| Type of Cyberattack | Description | Economic Impact |
|---|---|---|
| Ransomware | Malicious software that encrypts data and demands payment for its release. | Significant financial losses due to data recovery, system restoration, and potential business disruption. |
| Data Breaches | Unauthorized access and theft of sensitive data. | Financial losses from identity theft, fraudulent transactions, and legal costs; reputational damage and loss of customer trust. |
| Supply Chain Attacks | Compromising software or hardware used by various businesses. | Extensive disruptions in supply chains, impacting multiple industries and causing significant financial losses for organizations across the affected sectors. |
| Phishing Attacks | Tricking individuals into revealing sensitive information through fraudulent emails or websites. | Financial losses from fraudulent transactions, data breaches, and damage to financial institutions’ reputation. |
Closing Summary
The Biden-Putin discussion on cyberattacks presents a critical opportunity for de-escalation and the establishment of clearer international norms. The potential outcomes, ranging from a negotiated agreement to a continued escalation, will have far-reaching consequences for global cybersecurity. The discussion’s success hinges on a clear understanding of the technical and geopolitical complexities involved, and the willingness of both leaders to prioritize a peaceful resolution.
This dialogue promises to be a pivotal moment in shaping the future of international relations in the digital age.
Q&A
What are the potential economic impacts of cyberattacks?
Cyberattacks can cripple businesses, disrupt supply chains, and cause significant financial losses. The potential for widespread damage to the global economy underscores the urgent need for international cooperation in combating these threats.
What are the existing international legal frameworks addressing cyber warfare?
While no single, comprehensive international law specifically addresses cyber warfare, existing treaties and conventions on international law can be applied to certain aspects of cyberattacks, providing a framework for addressing these issues. However, a more robust international legal framework is needed.
What are the methods used in recent high-profile cyberattacks?
Recent attacks have employed a variety of methods, including ransomware, phishing, and denial-of-service attacks. These methods are often sophisticated and difficult to trace, making attribution challenging.
What is the US government’s response strategy to cyberattacks from foreign actors?
The US government has a multi-layered response strategy that includes technical countermeasures, diplomatic efforts, and legal action, though specific details are often kept confidential for security reasons.