Google Takes the Blame for Indias Aadhaar Data Controversy
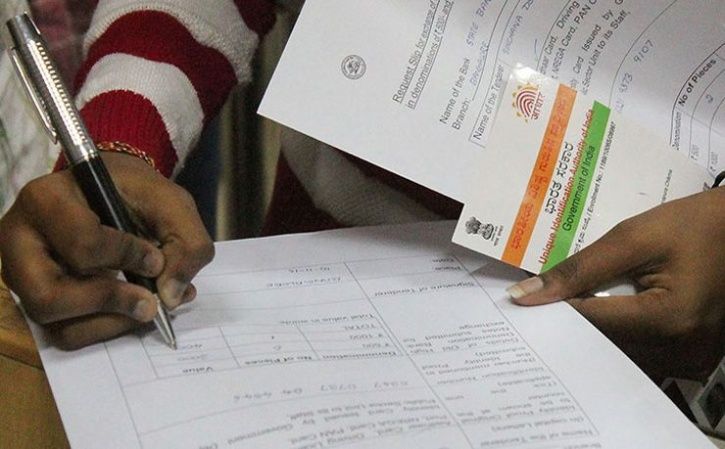
Google takes the blame for india uidai aadhaar data controversy – Google takes the blame for India’s UIDAI Aadhaar data controversy, sparking a debate about data privacy and responsibility in the tech world. This incident highlights the complex interplay between global tech giants and national regulations, particularly in the context of India’s Aadhaar program and its sensitive user data.
The controversy centers on allegations that Google mishandled user data linked to India’s Aadhaar biometric identification system. Concerns arise over potential breaches, data security vulnerabilities, and the implications for user trust. This situation necessitates a careful examination of the specifics of Google’s involvement, the regulatory framework in India, and the potential repercussions for both the company and the citizens.
Background of the UIDAI-Aadhaar Data Controversy
The Aadhaar scheme, a unique identification number for Indian residents, has been a subject of intense debate and scrutiny. Its introduction aimed to streamline various government services, but the scheme’s implementation has faced considerable criticism regarding data privacy and security. This controversy, particularly involving Google, underscores the complex interplay between national identity projects, technological advancements, and data protection regulations.The Aadhaar scheme, launched in 2009, aimed to create a unique identity for every Indian citizen.
Initially hailed as a tool for streamlining government services and reducing corruption, the scheme has since become entangled in debates surrounding data privacy, security, and potential misuse. The controversies surrounding Aadhaar highlight the need for a balanced approach that considers the benefits of such initiatives alongside the crucial protection of individual rights.
Google taking the blame for the India UIDAI Aadhaar data controversy highlights a critical need for robust security measures. This underscores the importance of implementing rigorous checks and balances in data handling, especially when dealing with sensitive personal information. Thankfully, solutions like deploying AI Code Safety Goggles Needed, as discussed in this insightful article, Deploying AI Code Safety Goggles Needed , can help prevent future data breaches and strengthen the foundations of digital security.
Ultimately, the Google situation serves as a stark reminder of the vulnerabilities inherent in large-scale data processing, and proactive measures like these are crucial to address them.
Historical Overview of the Aadhaar Scheme
The Aadhaar scheme began as a voluntary program for biometric identification, but it has gradually become mandatory for numerous government services. This evolution, while aiming for efficiency, has triggered concerns about the scope of data collection and its potential misuse. Early adopters of the system included banks, telecom companies, and various government agencies.
Key Aspects of Data Privacy Concerns Surrounding Aadhaar
Concerns surrounding Aadhaar revolve primarily around the vast amount of personal data collected and stored. The biometric data, including fingerprints and iris scans, along with demographic information, raises questions about data security, potential breaches, and the lack of transparency in how this data is handled. Concerns also exist about the potential for misuse and discrimination based on access to services linked to the Aadhaar number.
Specific Instances Leading to Controversy Surrounding Google’s Role
While Google’s direct involvement in the Aadhaar scheme is not always clear, the company has been implicated in the broader controversy due to its role in providing technology solutions for various government agencies. These agencies utilize Aadhaar data in various applications, and Google’s association raises questions about the company’s accountability for data handling and security.
Regulatory Framework Governing Data Handling in India
India’s data protection landscape has evolved significantly, but concerns persist about the enforcement of existing regulations and the adequacy of safeguards for sensitive data. The Information Technology Act (IT Act) of 2000, amended over the years, is a cornerstone of this framework, outlining rules for electronic data handling. However, the increasing reliance on digital platforms and the handling of biometric data require more specific regulations.
Comparison of Indian and International Data Privacy Regulations
| Feature | Indian Data Protection Regulations | International Data Privacy Regulations (e.g., GDPR) |
|---|---|---|
| Scope | Focuses on data handled electronically, but with limited specifics on biometric data. | Broader scope, including data collected through various means, with a particular emphasis on user rights. |
| Data Subject Rights | Limited rights for data subjects; enforcement mechanisms are still evolving. | Stronger data subject rights, including rights to access, rectification, and erasure of data. |
| Enforcement Mechanisms | Enforcement relies on the IT Act and other related legislation. The process can be complex and lengthy. | Clearer and more robust enforcement mechanisms, often with independent data protection authorities. |
| Cross-Border Data Transfer | Specific provisions, but the framework may not be as comprehensive as international standards. | Specific rules and safeguards regarding cross-border data transfers, ensuring a high level of protection. |
The table above provides a concise comparison of the Indian and international data privacy regulations. It highlights the differences in scope, data subject rights, enforcement mechanisms, and cross-border data transfer provisions. International regulations often offer a more comprehensive and stringent approach to data protection.
Google’s Alleged Role and Responsibility
Google’s involvement in handling Aadhaar data, a cornerstone of India’s digital identity system, is at the heart of the current controversy. Understanding the specifics of Google’s role is crucial to assessing its potential liabilities. The company’s actions, statements, and potential legal exposure require careful examination.The controversy surrounding Google’s alleged handling of Aadhaar data centers on the nature of the data’s use in Google services and the company’s transparency in this process.
Google’s recent fall guy role in the Indian UIDAI Aadhaar data controversy highlights the complex web of responsibility around data handling. While the finger-pointing is understandable, it’s worth noting that similar concerns regarding data security are also prevalent in other sectors. For instance, the Department of Justice Offers Safe Harbor for MA Transactions here , potentially setting a precedent for handling sensitive information in other contexts.
This brings the whole issue back to the heart of the matter: how do we ensure data security and privacy across the board, especially when dealing with potentially vulnerable user information like that linked to the Aadhaar system?
This involves examining the technical aspects of data transfer, storage, and processing, along with Google’s communication regarding these matters. Furthermore, the legal framework surrounding data protection in India plays a significant role in determining potential liabilities.
Nature of Google’s Involvement in Handling Aadhaar Data
Google’s involvement in handling Aadhaar data is multifaceted. The precise nature of this involvement varies depending on the specific Google services and features that utilize Aadhaar for authentication or other purposes. For instance, some services might use Aadhaar for verification while others may integrate it with other user data. This complex interplay necessitates a thorough investigation into Google’s specific practices regarding data collection, storage, and usage.
Google’s Public Statements Regarding Its Role in the Controversy
Google’s public statements concerning its handling of Aadhaar data have been a significant point of discussion. These statements are crucial in assessing the company’s perspective on its role in the controversy. The statements should be scrutinized for consistency and transparency, evaluating whether they align with Google’s stated commitment to data privacy and user protection. These statements are often analyzed for their implications on Google’s future operations and public image.
Potential Legal Implications for Google in This Scenario
Google’s potential legal exposure in this scenario hinges on several factors. These include the specific laws governing data privacy and security in India, the nature of Google’s agreement with UIDAI (Unique Identification Authority of India), and the interpretation of those agreements by legal authorities. Furthermore, the precedents set by other similar cases involving data handling and privacy violations play a crucial role in predicting potential outcomes.
Table Outlining Google’s Potential Liabilities Based on Different Legal Interpretations
| Legal Interpretation | Potential Liabilities |
|---|---|
| Strict interpretation of data privacy laws | Potentially significant fines, injunctions to cease processing of Aadhaar data, and reputational damage. |
| Moderate interpretation of data privacy laws | Potentially substantial fines, and obligations to implement enhanced data protection measures. |
| Lenient interpretation of data privacy laws | Potentially lower fines, or the need to implement corrective actions in a limited scope. |
| Violation of user agreement with UIDAI | Possible legal action from UIDAI, including demands for data deletion or other remedial actions. |
Impact of the Controversy on Google and Indian Users

The UIDAI-Aadhaar data controversy, implicating Google’s role in handling Indian user data, has significant ramifications for both the tech giant and the citizens of India. The accusations of data mishandling and potential breaches have the potential to erode trust and alter the landscape of data partnerships in the country. Understanding the potential fallout is crucial for assessing the long-term consequences.
Potential Impact on Google’s Reputation and Market Share, Google takes the blame for india uidai aadhaar data controversy
Google’s reputation, built on a foundation of trust and user privacy, faces a serious threat. Negative publicity surrounding the controversy could damage its brand image, potentially leading to a decline in user trust and a decrease in market share. This is especially true in a market like India, where Google has substantial operations and a large user base.
The controversy could also deter potential investors and partners, further impacting Google’s financial performance. Similar controversies in the past, involving data breaches or misuse, have resulted in significant reputational damage and loss of market share for other tech companies.
Potential Consequences on Trust between Google and Indian Citizens
The controversy has the potential to severely damage the trust between Google and Indian citizens. The perception of data mishandling could fuel distrust, potentially leading to reduced usage of Google services and an increased preference for alternative platforms. This loss of trust can have long-lasting effects on the company’s relationship with the Indian market. Historical examples show that eroded trust takes considerable time and effort to rebuild.
Possible Implications on Future Data Partnerships in India
The controversy may deter Google and other tech companies from entering into or continuing data partnerships in India. The increased regulatory scrutiny and the potential for legal challenges could make such partnerships riskier and less attractive. The current controversy casts a shadow on the trustworthiness of data handling practices, leading to a more cautious approach from companies involved in data partnerships in India.
This could have wider implications for the development of technology and innovation in the country.
Potential Negative Impacts on Google’s Brand Image
The controversy can negatively affect Google’s brand image in several ways. A tarnished reputation can lead to decreased brand value, reduced customer loyalty, and a decline in consumer confidence.
Google taking the blame for India’s UIDAI Aadhaar data controversy highlights the crucial need for robust data security measures. While this is a serious issue, it’s also worth noting the recent vulnerabilities discovered in Azure Cosmos DB, a Microsoft product. These vulnerabilities, detailed in this insightful report Azure Cosmos DB Vulnerability Details , show how easily sensitive data can be compromised, emphasizing the importance of proactive security measures in a world increasingly reliant on cloud-based services.
Ultimately, the Aadhaar data breach underscores the ongoing battle against data breaches, and the constant need for vigilance in this space.
| Aspect | Negative Impact |
|---|---|
| Public Perception | Negative publicity and decreased trust from Indian citizens |
| Investor Confidence | Reduced investor interest and potential stock price decline |
| Market Share | Loss of market share to competing tech companies |
| Regulatory Scrutiny | Increased regulatory oversight and potential fines |
| Data Partnerships | Reduced willingness to engage in data partnerships in India |
Potential Solutions and Future Implications

The UIDAI-Aadhaar data controversy and Google’s alleged role highlight critical vulnerabilities in the current data handling framework. Addressing these issues requires a multifaceted approach encompassing stronger regulations, enhanced transparency, and a shift towards more user-centric data practices. The future of data security and privacy in India hinges on the effective implementation of these solutions.
Potential Solutions to Mitigate Future Controversies
Robust regulatory frameworks are crucial to prevent similar incidents. These frameworks should clearly define the responsibilities of both technology companies and data custodians, including specific protocols for data access, use, and transfer. Clear guidelines for user consent and data minimization principles should be established, alongside mechanisms for user redressal.
- Strengthened Data Governance: A comprehensive data governance framework is essential. This framework should include stringent data security protocols, robust auditing mechanisms, and clearly defined roles and responsibilities for data handling. This includes provisions for independent audits of data handling practices and penalties for violations.
- Enhanced User Transparency and Control: Users need greater transparency regarding how their data is collected, used, and shared. This should include clear and concise language in terms and conditions, allowing users to easily understand and exercise control over their data. Providing tools for users to access, correct, and delete their data is paramount.
- Independent Oversight Mechanisms: Establishing independent bodies to oversee data practices and investigate complaints is essential. These bodies should have the authority to enforce regulations and provide a platform for user redressal, thus fostering trust and accountability.
Importance of Transparent Data Practices in the Tech Industry
Transparency is paramount in the tech industry. Open communication about data collection, usage, and sharing builds trust and fosters user confidence. Transparency enables users to make informed decisions about sharing their personal data, reducing the risk of misuse and controversy. Furthermore, transparency promotes accountability and encourages companies to adopt ethical data practices.
- Clear Data Policies: Companies must articulate their data policies clearly and concisely. Users should readily understand how their data is being handled, including the purposes for collection, storage, and potential sharing. This includes providing specific examples of how data is utilized, such as in targeted advertising or research initiatives.
- Proactive Disclosure: Companies should proactively disclose potential risks associated with data handling. This includes notifying users of any vulnerabilities or potential breaches, allowing them to take appropriate measures to protect their information. This proactive disclosure builds trust and demonstrates a commitment to data security.
- User Feedback Mechanisms: Implementing user feedback mechanisms allows companies to understand user concerns and adjust their practices accordingly. Feedback channels should encourage open dialogue and enable users to report issues or suggest improvements to data handling policies.
Possible Long-Term Implications on Data Security and Privacy in India
The controversy has the potential to significantly impact data security and privacy in India. A lack of trust in data handling practices could discourage the adoption of digital services and potentially hinder India’s digital transformation. It can also lead to increased scrutiny of international tech companies operating in the country.
Regulatory Responses and Actions from Google and the Indian Government
The Indian government and Google are likely to face scrutiny and pressure to address the issues raised by the controversy. The government may introduce stricter data protection regulations, while Google may need to revise its data handling policies and practices. These actions may involve increased oversight, compliance measures, and transparency initiatives.
- Governmental Action: The Indian government may strengthen data protection laws, such as the Personal Data Protection Bill, to incorporate specific provisions for cross-border data transfers. This may include stricter regulations for data localization and greater enforcement mechanisms.
- Google’s Response: Google may implement enhanced data security measures and adopt more user-centric data policies, including improved consent mechanisms and data minimization principles. It may also increase transparency regarding its data handling practices in India and address user concerns proactively.
Analysis of Public Perception

The UIDAI-Aadhaar data controversy, involving Google’s alleged role, sparked a significant public discourse. Public opinion was multifaceted, ranging from concerns about data privacy and security to discussions about the broader implications of government-backed identification systems. Understanding these varied perspectives is crucial for evaluating the long-term impact of this issue.
Public Discourse Summary
The public discourse surrounding the controversy was marked by a wide range of opinions and concerns. Discussions spanned online forums, social media platforms, and traditional news outlets. The core themes revolved around data security, government overreach, and the role of technology companies in handling sensitive user information. A significant portion of the discussion focused on the potential risks associated with sharing personal data with both government agencies and technology platforms.
Public Reactions to the Controversy
The public’s reaction to the controversy was diverse and included a spectrum of emotions and viewpoints. Reactions varied from expressing trust in government initiatives to raising concerns about potential misuse of personal information. Significant segments of the population were apprehensive about the implications of linking personal data to government-issued identification systems.
Different Public Perspectives
Public perspectives on the Aadhaar data controversy and Google’s role varied significantly. Different segments of the population held distinct viewpoints, based on their understanding of the issue, their perceived risk, and their individual values.
| Perspective | Summary | Example Statements |
|---|---|---|
| Supportive of Aadhaar | This perspective generally viewed Aadhaar as a crucial tool for citizen identification and social inclusion, highlighting its potential benefits in reducing fraud and promoting financial inclusion. | “Aadhaar is essential for India’s development. It streamlines government services and helps prevent fraud.” |
| Concerned about Data Privacy | This perspective emphasized the potential for misuse of personal data linked to Aadhaar, expressing concern about government overreach and the lack of robust privacy protections. | “Aadhaar data must be handled with utmost care. We need stronger privacy safeguards to protect our personal information.” |
| Critical of Google’s Role | This perspective focused on Google’s role as a tech giant handling sensitive user data, highlighting concerns about potential breaches and the lack of transparency in data usage. | “Google’s involvement raises serious concerns about data security and user privacy. They must be more transparent about how they handle user information.” |
| Neutral/Cautious | This perspective generally observed the issue with caution, emphasizing the need for a balanced approach that addresses both the benefits and risks of Aadhaar and its associated data handling. | “There are legitimate concerns about data privacy, but Aadhaar also offers benefits. A careful balance is needed.” |
Illustrative Case Studies of Data Breaches: Google Takes The Blame For India Uidai Aadhaar Data Controversy
The UIDAI-Aadhaar data controversy highlights a critical issue: the vulnerability of personal data in the digital age. Understanding past data breaches provides valuable context for assessing the potential risks and implications of this current situation. Analyzing similar incidents helps to identify patterns, potential causes, and the effectiveness of responses. This section will examine notable data breaches, examining their causes, consequences, and responses to illuminate parallels and differences with the current controversy.
Examples of Prominent Data Breaches
Numerous data breaches have occurred across various sectors in the tech industry, impacting millions of users. Understanding these events provides a framework for analyzing the Aadhaar controversy.
- Equifax Breach (2017): This massive breach exposed sensitive personal information of approximately 147 million Americans, including names, Social Security numbers, dates of birth, and addresses. The breach was caused by a vulnerability in Equifax’s systems, allowing hackers to gain unauthorized access. The consequences were significant, including identity theft, financial losses, and reputational damage for the company. Equifax’s response involved implementing security measures, providing credit monitoring services to affected individuals, and paying substantial settlements.
This incident illustrates the potential for widespread damage and the need for robust data security measures.
- Yahoo! Data Breaches (2013, 2014): These breaches compromised the personal data of billions of users, exposing account information, passwords, and email addresses. The cause was again a security vulnerability in Yahoo’s systems. The consequences included identity theft, financial fraud, and significant reputational harm. Yahoo’s response involved patching security flaws, notifying affected users, and implementing new security protocols. The lengthy duration of the breaches and the significant number of affected users underscore the potential for long-lasting damage and the importance of proactive security measures.
- Cambridge Analytica Scandal (2018): This case involved the unauthorized collection and use of personal data from millions of Facebook users. The data was collected by Cambridge Analytica, a political consulting firm, without the users’ consent. The consequences included concerns about data privacy, manipulation of political discourse, and reputational damage for Facebook. Facebook’s response involved implementing stricter data privacy policies and enhancing user controls.
Comparing the Aadhaar Controversy to Previous Breaches
Analyzing the Aadhaar controversy in the context of these previous breaches reveals similarities and differences. The Aadhaar data, containing highly sensitive personal information, shares similarities with the data compromised in previous breaches. However, the context of the Aadhaar data, being government-held, carries unique implications.
| Feature | Aadhaar Controversy | Equifax Breach | Yahoo! Breaches | Cambridge Analytica |
|---|---|---|---|---|
| Data Type | Biometric and demographic data | Financial and personal information | Account details and email addresses | Facebook user data |
| Data Source | Government-run database | Credit reporting agency | Internet service provider | Social media platform |
| Potential Impact | Identity theft, fraud, misuse of data | Identity theft, financial fraud | Identity theft, financial fraud, spam | Political manipulation, privacy concerns |
| Cause (Likely) | Data handling and security flaws, potential unauthorized access | Vulnerability in systems | Vulnerability in systems | Data collection without user consent |
Analysis of Similarities and Differences
The Aadhaar controversy shares similarities with previous breaches in terms of the potential for significant harm and the need for robust security measures. However, the unique nature of the data and its government association distinguishes it from other incidents. The scale of data involved in Aadhaar, coupled with the potential for misuse by unauthorized actors, necessitates a thorough examination of security protocols and safeguards.
Ending Remarks
The Google-Aadhaar data controversy underscores the urgent need for robust data protection regulations and transparent data practices in the tech industry. The incident forces us to re-evaluate the responsibilities of multinational corporations when handling sensitive personal information within specific national contexts. Looking forward, this case study serves as a crucial learning opportunity to prevent similar incidents in the future.
Query Resolution
What is the Aadhaar program?
Aadhaar is a biometric identification program in India that aims to provide unique identification for citizens. It’s a large-scale project encompassing various aspects of public services and personal transactions. However, its use has been subject to debate.
What are the key data privacy concerns surrounding Aadhaar?
Concerns revolve around the collection, storage, and usage of sensitive personal data, including biometric information. Questions about potential misuse, data breaches, and lack of transparency have been raised.
What is Google’s alleged role in this controversy?
Google is accused of handling Aadhaar data as part of its services in India, and questions have been raised about the company’s compliance with Indian data privacy regulations.