Cybersecurity
-
Dealing with Stolen Data in Ransomware Attacks A Comprehensive Guide
Dealing with stolen data in ransomware attacks a comprehensive guide provides a crucial roadmap for organizations facing the devastating impact…
Read More » -

Israel Cyberattack, Iran Port, Texas Ransomware
Israel cyber attack on Iran port and Texas transport ransomware attack highlight a dangerous new era in global cybersecurity. These…
Read More » -

ISC² Congress Adaptability in Cybersecurity
Isc2congress we got this adaptability is nothing new to cybersecurity – ISC²congress we got this adaptability is nothing new to…
Read More » -

ISC2 Congress COVID Minimal Impact on Cyber Jobs
ISC2congress recruiter COVID had a minimal impact on the cybersecurity job market, suggesting a surprising resilience in the sector. Pre-pandemic,…
Read More » -

ISC2 Study Improved Cybersecurity Pro Perceptions
ISC2 study reveals vastly improved perceptions about cybersecurity professionals, showing a significant shift in public opinion. The study delves into…
Read More » -

THaaS Threat Hunting as a Service for You
Is threat hunting as a service thaas for you – Is threat hunting as a service (THaaS) right for you?…
Read More » -

Is It the Solution to Filling Cybersecurity Workforce Gap 2?
Is it the solution to filling cybersecurity workforce gap 2? This exploration delves into a crucial question facing organizations today.…
Read More » -
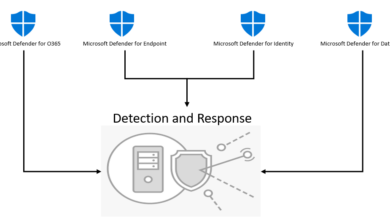
XDR Cybersecurity Infrastructures Foundation
Is extended detection and response xdr the ultimate foundation of cybersecurity infrastructure – Is extended detection and response (XDR) the…
Read More » -

Is Backup the Only Ransomware Blocker?
Is backup the only solution to block ransomware threats? This exploration delves into the critical question of ransomware protection, examining…
Read More » -

Jihadi Cyber Attack A Prowl
Is a jihadi cyber attack on the prowl? This exploration delves into the evolving threat landscape, examining the motivations, tactics,…
Read More »
