Cybersecurity
-

Tesla Data Breach Insider Threat Exposed
Insider threat leads to Tesla data breach, highlighting a significant security vulnerability. This incident reveals how seemingly trusted individuals can…
Read More » -
Insider Threat Detection What You Need to Know
Insider threat detection what you need to know sets the stage for understanding a critical security issue in today’s digital…
Read More » -

Insider Threat Alert Data Theft by Exiting Employees
Insider threat alert as employees take data while leaving a job is a growing concern for businesses. This issue highlights…
Read More » -

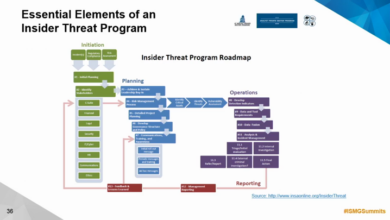
Insider Threat and Mitigation Best Practices
Insider threat and mitigation best practices are crucial for organizations to protect sensitive data and systems. Understanding the different types…
Read More » -

Insider Risk Unconventional Thoughts & Lessons Learned
Insider risk unconventional thoughts and lessons learned – Insider risk: unconventional thoughts and lessons learned. This exploration delves into the…
Read More » -

Indian Cybercrime Alert Job Scams
Indian government issues cyber crime alert in view of job offers, highlighting the rising tide of online job scams targeting…
Read More » -

Imperva Cloud Firewall Hack Data Exposed
Imperva announces that data of its cloud firewall was exposed to hackers, sparking immediate concern about the security of sensitive…
Read More » -

Immutable Data Storage Ransomwares Last Stand
Immutable data storage is last line of defense against ransomware – Immutable data storage is the last line of defense…
Read More » -
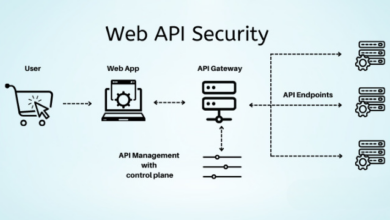
API Security Risks Graylogs Solution
If your business is not vulnerable to api security risks then you are not paying attention graylog – If your…
Read More »

