Malware Waits for No CASB A Critical Threat
Malware waits for no CASB. Cloud environments are increasingly attractive targets for malicious actors, and traditional security measures often fall short. CASB solutions aim to bolster defenses, but attackers are constantly evolving their tactics to bypass them. This article delves into the dynamic relationship between malware and CASBs, exploring the vulnerabilities, evolving strategies, and crucial proactive measures needed to protect cloud assets.
Understanding the intricacies of malware and its constant evolution is critical. We’ll explore the diverse forms of malware, from viruses to ransomware, and examine how they bypass traditional security measures. This understanding is crucial for effectively countering the threats posed by these sophisticated attacks.
Defining Malware and its Evolving Nature
Malware, short for malicious software, is a broad category of harmful programs designed to infiltrate and damage computer systems. Its core function is to disrupt, disable, or gain unauthorized access to a targeted device or network. This malicious intent extends beyond mere annoyance; it encompasses financial theft, data breaches, and even physical damage in certain cases. The evolving nature of malware necessitates constant vigilance and adaptation in security measures.Malware manifests in various forms, each with its unique modus operandi.
From the insidious spread of viruses to the targeted extortion of ransomware, the spectrum of malicious software is vast and constantly evolving. Understanding these diverse forms and their mechanisms is crucial for effective defense.
Core Characteristics of Malware
Malware exhibits several key characteristics, including the ability to replicate, spread, and cause damage. The diverse forms of malware include viruses, worms, Trojans, ransomware, spyware, and adware, each with its own unique attack vector. Viruses, for instance, require an existing program to replicate and spread, while worms can propagate autonomously across networks. Trojans, disguised as legitimate software, trick users into installing them, often leading to unauthorized access or data breaches.
Evolution of Malware Techniques
Malware’s evolution is a constant arms race between attackers and defenders. Sophisticated techniques like polymorphic and metamorphic malware are becoming increasingly prevalent. Polymorphic malware alters its code structure to evade detection by antivirus software, making it more difficult to identify and eliminate. Metamorphic malware goes a step further, completely transforming its code structure during each infection, further obscuring its true intent.
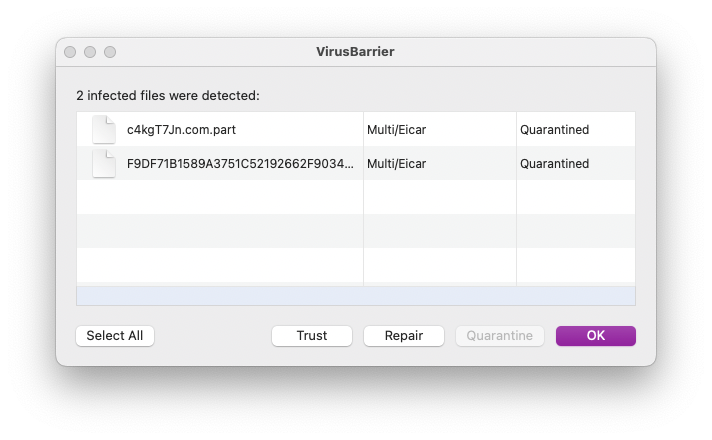
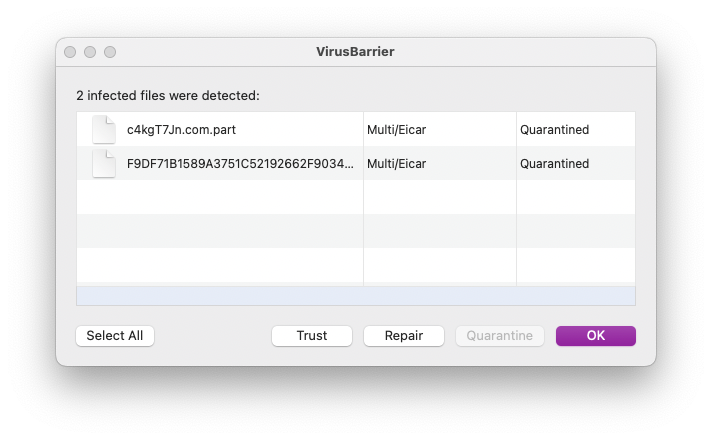
Malware Bypassing Security Measures
Traditional security measures, such as signature-based antivirus software, often struggle to detect these advanced forms of malware. Malware frequently employs techniques like obfuscation, encryption, and code packing to evade detection. For instance, malware can use obfuscation to make its code more complex and less easily recognizable, thus evading signature-based detection.
Classifying Malware Based on Behavior and Impact
Malware can be categorized based on its behavior and the impact it has on the targeted system. One classification system focuses on the malware’s function, like data theft or system disruption. Another approach categorizes malware by its propagation methods, such as network worms or file-infecting viruses. These classifications help in developing targeted security strategies.
Comparison of Malware Types
| Malware Type | Common Tactics | Impact |
|---|---|---|
| Virus | Infects files, replicates, spreads through files, often through user interaction or network shares. | File corruption, system instability, potential data loss. |
| Worm | Spreads autonomously through networks, exploits vulnerabilities in operating systems or applications. | Network congestion, denial-of-service attacks, potential data breaches. |
| Trojan | Disguises itself as legitimate software, gains unauthorized access to a system. | Data theft, remote access, system compromise. |
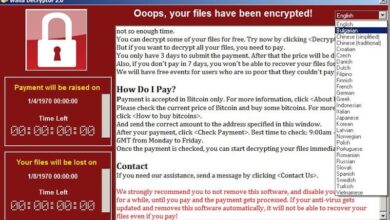
| Ransomware | Encrypts files, demands payment for decryption. | Data loss, financial loss, potential system downtime. |
| Spyware | Monitors user activity, collects personal information. | Privacy violations, potential identity theft, data breaches. |
The Role of CASB in Modern Cybersecurity: Malware Waits For No Casb
Cloud computing has revolutionized how businesses operate, but this shift also introduces new security challenges. Traditional security tools often struggle to protect sensitive data and applications residing in the cloud. This necessitates specialized security solutions to address the unique characteristics of cloud environments. Cloud Access Security Brokers (CASBs) play a crucial role in bridging this gap.CASBs act as a central point of control for cloud security, providing visibility and governance over cloud resources and user access.
They empower organizations to enforce security policies across various cloud platforms, ensuring compliance and minimizing risks. The key to their effectiveness lies in their ability to monitor and manage cloud activities in real-time.
Essential Functions of a CASB
CASBs perform a variety of critical functions to safeguard cloud environments. They provide comprehensive visibility into cloud activity by monitoring user access, data transfers, and application usage. This real-time monitoring allows for quick identification of suspicious behavior and potential threats. Furthermore, CASBs enforce security policies by controlling access to cloud resources and applications, limiting the impact of potential breaches.
Malware waits for no CASB, and that’s a harsh reality for security teams. We need proactive defenses, and deploying AI Code Safety Goggles is crucial to proactively identify and mitigate threats before they breach. Deploying AI Code Safety Goggles Needed highlights the importance of this, and ultimately, these strategies are critical for preventing the next wave of malware attacks.
So, while CASB is important, it’s not enough; we need more advanced tools to stay ahead of the curve.
These policies can be tailored to specific users, applications, and data, ensuring appropriate levels of access and protection.
How CASBs Mitigate Threats in Cloud Environments
CASBs mitigate threats by actively monitoring cloud activities and promptly responding to potential issues. They detect malicious or unauthorized access attempts, such as data exfiltration or unauthorized application deployments. This proactive approach allows organizations to take swift action, preventing further damage and minimizing the impact of security incidents. Moreover, CASBs enable granular control over cloud resources, empowering organizations to enforce policies that restrict access to sensitive data and applications.
This granular control effectively reduces the attack surface within the cloud environment.
Malware, unfortunately, waits for no security measure, not even a robust CASB. This is especially true when considering recent vulnerabilities like the one found in Azure Cosmos DB. Learning about these vulnerabilities, like the ones detailed in Azure Cosmos DB Vulnerability Details , is crucial for proactively bolstering your defenses. The takeaway remains the same: malware waits for no CASB, so staying ahead of the curve is paramount.
Limitations of Traditional Security Tools in Cloud Environments
Traditional security tools, designed for on-premises environments, often lack the capabilities to effectively address the unique challenges posed by cloud computing. Their inability to monitor and control access to cloud resources in real-time hinders their effectiveness in cloud-based threat detection and response. Furthermore, the distributed nature of cloud environments makes it difficult for traditional tools to maintain visibility and enforce policies across multiple cloud platforms and applications.
Key Features and Benefits of Various CASB Solutions
| CASB Feature | Benefit | Example |
|---|---|---|
| Real-time Monitoring | Provides immediate visibility into cloud activities, enabling quick detection of threats and suspicious behavior. | Monitoring user logins, data transfers, and application usage in real-time. |
| Policy Enforcement | Enables organizations to enforce security policies across various cloud platforms and applications, ensuring compliance and minimizing risks. | Restricting access to sensitive data based on user roles and permissions. |
| Data Loss Prevention (DLP) | Protects sensitive data from unauthorized access or exfiltration within cloud environments. | Blocking the transfer of sensitive data outside predefined boundaries. |
| Cloud Inventory Management | Provides a comprehensive inventory of all cloud resources, facilitating better security management and control. | Identifying all cloud applications, services, and data stores. |
| Compliance Reporting | Generates reports to demonstrate compliance with relevant security regulations and standards. | Creating detailed reports to satisfy regulatory requirements, like GDPR or HIPAA. |
Malware’s Tactics to Circumvent CASB

Cloud Access Security Brokers (CASBs) are crucial for securing cloud environments, but sophisticated malware constantly adapts to evade detection. Understanding these evasion techniques is paramount for effective cybersecurity. Malware actors leverage various strategies to bypass CASB controls, making it challenging to maintain a secure cloud ecosystem.
Common Malware Evasion Strategies
Malware employs diverse techniques to circumvent CASB detection. These tactics often focus on masking malicious activities or exploiting vulnerabilities in the cloud infrastructure. Obfuscation, polymorphism, and evasive coding are key components in this arsenal.
Obfuscation
Obfuscation techniques render malware code difficult to understand and analyze. This makes it harder for security tools, including CASBs, to identify malicious intent. Compilers, encryption, and the use of complex code structures are common methods of obfuscation. The obfuscated code may still perform malicious actions, but its true nature is obscured from traditional analysis. For example, a piece of malware might use advanced encryption techniques to obscure its instructions, making it difficult for a CASB to determine if the code is malicious.
Polymorphism
Polymorphism is another powerful evasion tactic. Malware using polymorphism modifies its code structure each time it infects a new system. This makes it difficult for signature-based detection methods to identify the malware, as the signature is constantly changing. This adaptation makes the malware harder to identify and track, as the signature of the malware shifts every time it replicates.
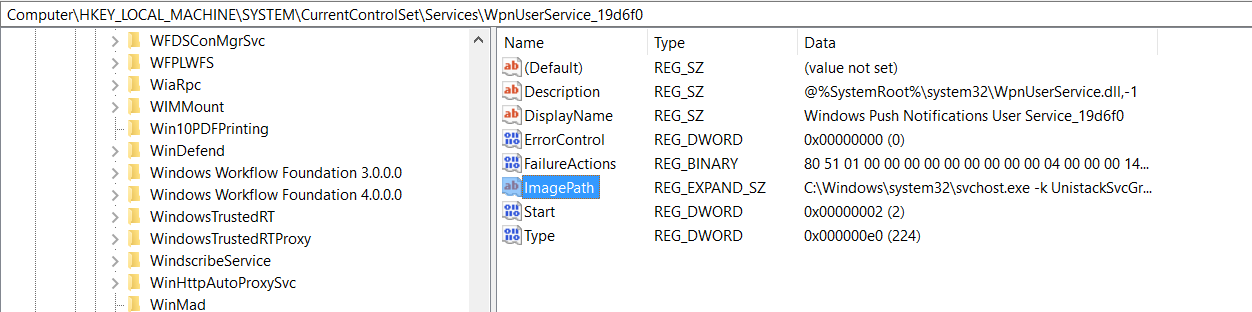
Evasive Coding
Evasive coding involves employing techniques to bypass or circumvent security controls. This may include using specific code sequences or exploiting known vulnerabilities in CASB systems. Malware authors might exploit flaws in CASB algorithms or bypass their control mechanisms to infiltrate the cloud environment. These methods can include using shellcode to evade detection or employing techniques to hide malicious activities within seemingly legitimate processes.
Penetration Techniques in Cloud Environments
Malware infiltrates cloud environments through various vectors. Compromised credentials, phishing attacks, and exploiting vulnerabilities in cloud services are common methods. Malicious actors may also leverage social engineering tactics to trick users into granting unauthorized access to cloud resources.
Challenges in Detecting Zero-Day Threats
Zero-day threats are a significant challenge for CASB solutions. These threats exploit previously unknown vulnerabilities, meaning that CASBs lack pre-built signatures to identify them. Malware authors often create zero-day exploits to exploit vulnerabilities that are unknown to the security community, which allows them to quickly and easily penetrate systems.
CASB Vulnerability Exploitation by Malware
| Malware Technique | CASB Vulnerability | Mitigation |
|---|---|---|
| Obfuscation | Inability to analyze the code’s intent | Implement advanced code analysis techniques |
| Polymorphism | Signature-based detection failure | Employ heuristic analysis and behavioral detection |
| Evasive Coding | Bypass of security controls | Enhance security controls and improve detection of malicious behavior |
| Compromised Credentials | Weak authentication | Implement strong authentication methods and multi-factor authentication |
| Phishing Attacks | User manipulation | Educate users on phishing tactics and implement security awareness training |
| Exploiting Vulnerabilities | Unpatched cloud services | Maintain up-to-date cloud services and patch promptly |
| Social Engineering | Exploitation of user trust | Implement strong security awareness training and vigilance |
The Concept of “Malware Waits for No CASB”
The phrase “Malware waits for no CASB” encapsulates a crucial reality in modern cybersecurity. It highlights the constant, relentless evolution of malicious actors and their relentless pursuit of vulnerabilities, often surpassing the capabilities of existing security solutions, including Cloud Access Security Brokers (CASBs). This dynamic environment necessitates a proactive and adaptable approach to security.The statement underscores the fact that attackers are not static.
They constantly adapt their methods and tools to bypass security measures. This means that CASBs, while valuable in controlling access and enforcing policies, are not a failsafe against all types of attacks. Malware authors are continuously developing new tactics to exploit vulnerabilities, forcing organizations to stay ahead of the curve.
Significance of the Phrase
The phrase emphasizes the urgency and dynamism of the cybersecurity landscape. Malware is not passively waiting for a security solution to be implemented. Instead, it actively seeks and exploits weaknesses. This means organizations cannot afford a reactive security posture.
Implications for Cybersecurity Strategies, Malware waits for no casb
The implication is clear: organizations must shift from a reactive to a proactive security model. Traditional security approaches that rely on identifying and responding to attacks after they occur are no longer sufficient. Organizations must prioritize prevention, detection, and response to threats. Proactive strategies encompass measures like threat intelligence gathering, vulnerability management, and security awareness training.
Importance of Proactive Security Measures
Proactive security measures are essential to mitigating the impact of malware bypassing CASBs. They strengthen the overall security posture, making it more resilient to attacks. This approach involves continuously monitoring and analyzing threats, identifying vulnerabilities, and implementing countermeasures. Regular security audits, penetration testing, and incident response planning are vital components of a robust proactive strategy.
Examples of Real-World Incidents Where Malware Bypassed CASB Solutions
Unfortunately, specific, publicly available details regarding malware bypassing CASB solutions are often limited for security and competitive reasons. However, anecdotal evidence suggests that attackers have successfully exploited vulnerabilities in CASB configurations or bypasses through sophisticated techniques such as using legitimate tools in malicious ways or leveraging zero-day exploits to circumvent CASB controls.
Malware waits for no CASB, and unfortunately, companies often find themselves scrambling to react after a breach. Thankfully, the Department of Justice Offers Safe Harbor for MA Transactions here might offer some much-needed relief and a framework for handling these complex situations. But even with safeguards, the proactive approach of robust security remains paramount in this constantly evolving threat landscape.
Table Demonstrating How Proactive Measures Strengthen CASB Effectiveness
| Proactive Measure | Impact on CASB | Example |
|---|---|---|
| Threat Intelligence Gathering | Enhances CASB’s ability to identify and respond to emerging threats. | Utilizing threat intelligence feeds to update CASB threat detection rules. |
| Vulnerability Management | Reduces the attack surface by patching vulnerabilities proactively. | Regularly scanning and patching software vulnerabilities, including those in CASB components. |
| Security Awareness Training | Reduces the risk of social engineering attacks, which can bypass CASB. | Educating employees about phishing, malware disguised as legitimate files, and other social engineering tactics. |
| Regular Security Audits | Identifies gaps in CASB configurations and overall security controls. | Conducting periodic security assessments to identify vulnerabilities in the CASB deployment and other systems. |
| Penetration Testing | Simulates real-world attacks to evaluate the effectiveness of CASB in preventing and detecting breaches. | Testing the CASB’s response to simulated attacks to identify vulnerabilities. |
Future Trends in Malware and CASB
The cybersecurity landscape is constantly evolving, with malware authors continuously adapting their tactics to bypass existing defenses. CASB solutions, while effective, must also adapt to these evolving threats to maintain their efficacy. Predicting future trends in malware and CASB is crucial for proactively strengthening security posture. This exploration delves into potential future developments, anticipated improvements in CASB technology, and the essential need for continuous learning and adaptation.The future of cybersecurity demands a proactive and adaptable approach.
Malware developers will likely leverage emerging technologies to create more sophisticated and evasive threats. CASB solutions must stay ahead of the curve, incorporating new features and functionalities to counteract these threats. The need for a multi-layered security approach is paramount to ensure comprehensive protection.
Future Malware Techniques
Malware authors will likely exploit vulnerabilities in cloud-native technologies, including containerization and serverless computing. They will also use AI and machine learning to generate more sophisticated and personalized attacks, targeting specific user behavior and preferences. Furthermore, the rise of ransomware-as-a-service (RaaS) will empower less skilled actors, potentially leading to a surge in ransomware attacks targeting organizations of all sizes.
Cryptojacking, a method of using a victim’s computing resources to mine cryptocurrency, will continue to evolve, targeting cloud environments to maximize efficiency.
Potential New Threats to Cloud Security
Supply chain attacks will increasingly target cloud service providers, potentially compromising multiple customer accounts. Data breaches caused by insider threats, including malicious actors or negligent employees with access to cloud resources, remain a critical concern. Phishing attacks will leverage AI to craft highly personalized and convincing emails, aiming to deceive users into compromising their cloud accounts. Furthermore, the use of cloud-based botnets will likely increase, enabling malicious actors to launch distributed denial-of-service (DDoS) attacks and other malicious activities from cloud infrastructure.
Anticipated Improvements in CASB Technologies
CASB solutions will likely incorporate more advanced machine learning algorithms to detect anomalies and identify sophisticated malware in real time. Increased integration with other security tools, like endpoint detection and response (EDR) and security information and event management (SIEM) systems, will provide a more comprehensive security posture. Improved threat intelligence sharing and collaboration among security providers will be crucial in responding to emerging threats.
Furthermore, CASB solutions will likely focus on granular control and fine-grained access management to restrict unauthorized activities within cloud environments.
Importance of Continuous Learning and Adaptation
Cybersecurity is a dynamic field. Organizations need to foster a culture of continuous learning and adaptation to stay ahead of evolving threats. Investing in security awareness training for employees and staying updated on emerging threats and vulnerabilities is crucial. Continuous monitoring and analysis of security logs, combined with proactive threat hunting, are essential for identifying and responding to emerging threats in real-time.
This proactive approach to security is essential in the face of continuously evolving attacks.
Need for a Multi-Layered Security Approach
A robust security posture requires a multi-layered approach that incorporates CASB solutions with other security tools and strategies. This includes strong access controls, robust endpoint security, regular security audits, and employee training. Security should extend to cloud infrastructure and services, with measures such as network segmentation and data loss prevention (DLP) technologies. By implementing a multi-layered approach, organizations can create a more resilient defense against evolving malware threats.
Comparison of CASB Solutions
| CASB Solution | Strengths | Weaknesses |
|---|---|---|
| Solution A | Strong machine learning capabilities, effective threat detection | Higher initial cost, potentially complex implementation |
| Solution B | Excellent integration with existing security tools, comprehensive visibility | Slower response time to new threats, limited customization |
| Solution C | Ease of deployment, low initial cost | Less advanced threat detection capabilities, limited customization options |
Different CASB solutions vary in their capabilities and effectiveness in combating evolving malware threats. Choosing the right solution depends on factors such as organizational size, budget, and specific security needs. Thorough evaluation and comparison of different CASB solutions are essential to ensure the best fit for a given organization.
Best Practices for Strengthening Cloud Security
The ever-expanding cloud landscape necessitates robust security measures to counter sophisticated malware threats. Implementing best practices across various aspects of cloud security is crucial to safeguarding sensitive data and maintaining operational continuity. Effective strategies are vital for mitigating risks and fortifying defenses against increasingly advanced attacks.Cloud security is no longer a luxury, but a necessity. Organizations must adopt a proactive approach to threat detection and mitigation, rather than reacting to breaches.
This proactive approach involves a layered defense strategy, incorporating various security protocols and best practices.
Essential Security Protocols for Cloud Environments
A multi-faceted approach to security protocols is vital for a robust cloud security posture. These protocols encompass various aspects of cloud infrastructure, from access control to data encryption. Proper implementation of these protocols minimizes the attack surface and safeguards sensitive information.
- Identity and Access Management (IAM): Implementing strong IAM policies is paramount. This involves meticulously controlling user access to cloud resources, using least privilege principles and multi-factor authentication. Strict access controls minimize the potential damage from compromised accounts.
- Data Encryption: Encrypting data both in transit and at rest is essential. This protects sensitive information from unauthorized access, even if a system is compromised. Encryption safeguards data confidentiality and integrity, irrespective of data location.
- Network Security: Implementing robust network security measures within the cloud environment is critical. This includes firewalls, intrusion detection systems (IDS), and network segmentation. Effective network security acts as a first line of defense against malicious actors.
Best Practices for Deploying and Managing CASB Solutions
A CASB solution, strategically deployed and managed, can significantly enhance cloud security posture. Its effectiveness hinges on proper configuration and continuous monitoring.
- Comprehensive Policy Definition: Clearly defining policies for access, usage, and data handling within the cloud environment is crucial. CASB solutions should be configured to enforce these policies consistently across all cloud applications and services.
- Continuous Monitoring and Alerting: Implementing continuous monitoring of cloud activity is vital. This includes tracking user behavior, application usage, and data movement. The system should generate alerts for suspicious activity, enabling swift response and remediation.
- Regular Security Assessments: Regularly assessing the effectiveness of the CASB solution is essential. This involves periodic audits and vulnerability scans to identify potential weaknesses and gaps in the security posture.
Importance of Employee Training and Awareness
Employee training and awareness programs play a pivotal role in bolstering cloud security. Educated employees are the first line of defense against phishing attacks and other social engineering tactics.
- Security Awareness Training: Regular training programs should equip employees with the knowledge to identify and avoid phishing attempts, suspicious links, and other potential security threats. Regular training programs should be comprehensive and include practical exercises and scenarios.
- Security Best Practices: Training should emphasize best practices for handling sensitive data, password management, and secure remote access. Employees should understand the importance of adhering to company security policies.
Significance of Incident Response Plans
A well-defined incident response plan is critical for mitigating the impact of security incidents in the cloud environment. Having a structured approach to handling breaches minimizes disruption and data loss.
- Proactive Planning: Developing a comprehensive incident response plan that Artikels procedures for detecting, containing, and recovering from security incidents is paramount. This includes identifying key personnel, roles, and responsibilities.
- Regular Testing: Regularly testing and updating the incident response plan ensures that it remains effective and relevant. Simulating potential incidents allows for practice and refinement of the response mechanisms.
Security Audits and Vulnerability Assessments
Regular security audits and vulnerability assessments are essential for identifying and mitigating security weaknesses within the cloud environment. These processes provide a comprehensive view of the security posture and pinpoint potential vulnerabilities.
- Regular Audits: Conducting regular security audits helps to identify gaps in security controls and policies. These audits evaluate the effectiveness of existing security measures and highlight areas requiring improvement.
- Proactive Vulnerability Assessments: Proactively identifying and addressing vulnerabilities is critical. These assessments pinpoint weaknesses in the system and provide recommendations for remediation.
Strategies for Regular Security Updates and Patching
Regular security updates and patching are vital for maintaining the security posture of cloud environments. These updates address known vulnerabilities and enhance the overall security of the system.
- Automated Patching: Implementing automated patching procedures minimizes the risk of security breaches and reduces downtime. This ensures that systems are consistently protected against emerging threats.
- Proactive Patch Management: Proactive patch management is essential. This includes scheduling regular updates and addressing any potential conflicts or dependencies.
Concluding Remarks
In conclusion, the “malware waits for no CASB” reality underscores the urgent need for a proactive and multi-layered security approach. Organizations must not only deploy robust CASB solutions but also embrace continuous learning, adaptation, and employee training to stay ahead of the evolving threat landscape. Ultimately, a strong security posture requires vigilance, continuous improvement, and a comprehensive strategy that anticipates and mitigates the ever-changing nature of cyberattacks.
FAQ Explained
Q: What are some common tactics used by malware to bypass CASB solutions?
A: Malware employs various techniques, including obfuscation (making code harder to understand), polymorphism (changing its form), and evasive coding (using methods to avoid detection). They also exploit vulnerabilities within the cloud environment and target zero-day threats, which are unknown vulnerabilities.
Q: How can organizations strengthen their cloud security posture beyond CASB solutions?
A: A multi-layered approach is essential. Proactive measures, such as employee training, incident response plans, regular security audits, and vulnerability assessments, combined with strong security protocols for cloud environments and continuous updates, significantly enhance CASB effectiveness.
Q: What are the future trends in malware that pose a threat to cloud security?
A: Future malware might leverage AI and machine learning to adapt to and bypass security measures more quickly. We can anticipate new threats targeting cloud infrastructure and services, and CASB solutions will need to adapt and improve to counter these developments.