AI Adoption Data Privacy and Security Concerns
Data privacy and security become most worrisome for AI adoption decision makers. It’s a brave new world of artificial intelligence, brimming with potential but shadowed by legitimate anxieties. The rapid advancement of AI, especially generative AI and sophisticated machine learning models, has thrust data privacy and security to the forefront of every conversation. We’re not just talking about theoretical risks; we’re seeing real-world data breaches and the erosion of user trust.
This isn’t just a tech problem; it’s a societal one, impacting how businesses operate and how individuals interact with technology.
This post dives deep into the complexities of balancing innovation with responsible data handling in the age of AI. We’ll explore the specific privacy risks associated with different AI models, examine relevant legal frameworks like GDPR and CCPA, and discuss practical strategies for securing AI systems. We’ll also look at the ethical considerations, the impact on AI adoption decisions, and the future trends shaping this critical landscape.
Data Privacy Concerns in AI Adoption: Data Privacy And Security Become Most Worrisome For Ai Adoption Decision Makers
The rapid advancement and widespread adoption of artificial intelligence (AI) present significant challenges to data privacy. AI systems, particularly those reliant on vast datasets for training and operation, inherently involve the processing of personal information, raising concerns about the potential for misuse, unauthorized access, and breaches of confidentiality. Understanding these risks and the legal landscape surrounding them is crucial for responsible AI development and deployment.
Specific Data Privacy Risks Associated with Different AI Models
Generative AI models, such as large language models (LLMs), pose unique data privacy risks. These models are trained on massive datasets often containing personal information scraped from the internet. This data can be inadvertently memorized and reproduced by the model, leading to the leakage of sensitive information like names, addresses, or even medical records. Similarly, machine learning models, while not explicitly generative, can still reveal sensitive information through inferences drawn from the data they are trained on.
For example, a model trained on anonymized medical data might still be able to identify individuals based on unique combinations of seemingly innocuous features. The risk is amplified when dealing with sensitive personal data like genetic information or biometric data.
Legal and Regulatory Frameworks Impacting AI Data Privacy
Several legal and regulatory frameworks aim to address the data privacy concerns associated with AI. The General Data Protection Regulation (GDPR) in the European Union and the California Consumer Privacy Act (CCPA) in the United States are prominent examples. GDPR establishes strict rules around the collection, processing, and storage of personal data, including the requirement for explicit consent and the right to be forgotten.
CCPA grants California residents similar rights, including the right to know what data is collected about them and the right to opt out of the sale of their personal information. These regulations, along with others emerging globally, impose significant compliance obligations on organizations using AI systems that process personal data. Non-compliance can result in substantial fines and reputational damage.
Examples of Data Breaches Stemming from AI Applications and Their Impact on User Trust
Several high-profile data breaches have highlighted the vulnerabilities of AI systems to privacy violations. For example, a hypothetical scenario might involve a facial recognition system used for security purposes inadvertently exposing sensitive personal information due to a vulnerability in its data storage or processing mechanisms. A breach like this could result in identity theft, reputational harm, and a significant loss of user trust in the technology.
Similarly, the misuse of AI-powered recommendation systems to profile users and target them with personalized advertising without their consent could erode trust and lead to regulatory scrutiny. Such incidents underscore the importance of robust security measures and ethical considerations in the development and deployment of AI systems.
Comparison of Data Privacy Practices of Leading AI Companies
| Company | Data Minimization | Transparency | Security Measures | Compliance with Regulations |
|---|---|---|---|---|
| Company A | Strong commitment to collecting only necessary data | Detailed privacy policy readily available | Robust encryption and access controls | Actively complies with GDPR and CCPA |
| Company B | Moderate data collection practices | Privacy policy available but less detailed | Standard security measures in place | Demonstrates compliance with major regulations |
| Company C | Limited focus on data minimization | Less transparent data handling practices | Security measures are less robust | Compliance efforts are ongoing |
| Company D | Data collection practices are unclear | Lack of transparency regarding data handling | Security measures are unclear | Compliance status is unknown |
Security Challenges of AI Systems
The increasing reliance on artificial intelligence (AI) across various sectors brings forth a new set of security concerns. AI systems, while offering immense potential, are vulnerable to sophisticated cyberattacks that can compromise their integrity, confidentiality, and availability. Understanding these vulnerabilities and implementing robust security measures is crucial for responsible AI adoption.AI systems are not immune to the traditional cybersecurity threats faced by other software systems, but they present unique challenges due to their complexity and data-driven nature.
The very data that fuels their power also becomes a primary target for malicious actors. Furthermore, the opacity of some AI models makes it difficult to understand how they function and identify vulnerabilities.
Data Poisoning Attacks
Data poisoning involves manipulating the training data of an AI model to induce erroneous or malicious behavior. Attackers might inject subtly altered data points into the training dataset, causing the model to make incorrect predictions or classifications. For example, an attacker could subtly alter images in a facial recognition system’s training data to cause it to misidentify specific individuals.
The impact can range from minor inaccuracies to catastrophic failures, depending on the system’s application. Robust data validation and anomaly detection techniques are essential to mitigate this threat. Regular audits of the training data, including checks for outliers and inconsistencies, are crucial.
Model Theft
The intellectual property embedded within AI models represents significant value. Model theft involves unauthorized access and replication of a trained model, potentially allowing attackers to exploit its capabilities for malicious purposes or gain a competitive advantage. This can be achieved through various methods, including unauthorized access to model parameters stored in cloud storage or inferring the model’s architecture and weights through a series of carefully crafted queries.
Protecting against model theft requires robust access control mechanisms, encryption of model parameters, and techniques like model watermarking, which embeds a unique identifier into the model to detect unauthorized copies.
Securing AI Models and Datasets
Securing AI models and datasets requires a multi-layered approach encompassing various security controls. This includes robust authentication and authorization mechanisms to control access to sensitive data and models, encryption of data both in transit and at rest, and the implementation of intrusion detection and prevention systems to monitor for suspicious activity. Regular security audits and penetration testing can help identify vulnerabilities and weaknesses in the system.
Furthermore, employing differential privacy techniques can help protect the privacy of individuals within the training data without significantly impacting model accuracy.
The Role of Encryption and Access Control, Data privacy and security become most worrisome for ai adoption decision makers
Encryption plays a vital role in securing AI data by transforming it into an unreadable format, protecting it from unauthorized access even if compromised. Different encryption methods can be applied depending on the sensitivity of the data and the specific security requirements. Access control mechanisms, including role-based access control (RBAC) and attribute-based access control (ABAC), regulate who can access specific data and models based on their roles and attributes.
These mechanisms help prevent unauthorized access and ensure that only authorized personnel can interact with sensitive information.
Security Architecture for an AI System
A robust security architecture for an AI system should prioritize data protection and integrity from the initial data collection stage to the deployment and maintenance phases. This architecture should include:
- Secure data storage and management using encryption and access control.
- Model versioning and control to track changes and revert to previous versions if necessary.
- Regular security assessments and penetration testing to identify and address vulnerabilities.
- Incident response plan to handle security breaches effectively.
- Data loss prevention (DLP) mechanisms to prevent sensitive data from leaving the system.
Implementing these measures ensures that the AI system remains secure and reliable, minimizing the risk of data breaches and malicious attacks. A well-defined security architecture is a critical component of responsible AI development and deployment.
Balancing Innovation and Privacy in AI

The rapid advancement of artificial intelligence presents incredible opportunities across various sectors, but this progress must be carefully balanced against the crucial need for robust data privacy and security. Ignoring privacy concerns can lead to public distrust, regulatory hurdles, and ultimately, stifle the very innovation AI promises. Successfully navigating this delicate balance requires a proactive and ethical approach to AI development and deployment.
This involves carefully considering data minimization strategies, employing strong anonymization techniques, and implementing privacy-preserving technologies.
Best Practices for Minimizing Data Collection and Usage
Designing AI systems that respect user privacy starts with a fundamental shift in mindset: collect only the data absolutely necessary for the AI to function effectively. This principle of data minimization significantly reduces the risk of data breaches and misuse. Instead of collecting vast amounts of personal information, developers should explore alternative approaches such as federated learning, where models are trained on decentralized data without the need to centralize sensitive information.
Another effective strategy is to use synthetic data for training, generating artificial datasets that mimic the characteristics of real data without containing any actual personal information. This allows for the development and testing of AI systems without compromising individual privacy. For instance, a healthcare AI system could be trained on synthetic patient data that preserves statistical properties while eliminating personally identifiable information.
Comparison of Data Anonymization and Pseudonymization Techniques
Data anonymization and pseudonymization are crucial techniques for protecting personal information while still allowing for data analysis. Anonymization aims to remove all identifying information from a dataset, making it impossible to link the data back to individuals. This can involve techniques like data generalization (replacing specific values with broader ranges) or suppression (removing certain attributes). However, perfect anonymization is often difficult to achieve, and re-identification attacks can sometimes reveal sensitive information.
Pseudonymization, on the other hand, replaces identifying information with pseudonyms, allowing for data linkage across different datasets while maintaining a level of privacy. This technique is often used in medical research, where patients are assigned unique identifiers that protect their identities while enabling researchers to track their progress over time. The choice between anonymization and pseudonymization depends on the specific application and the level of privacy required.
For example, in a customer relationship management system, pseudonymization might be sufficient, while in a sensitive medical context, more rigorous anonymization techniques might be necessary.
Implementing Differential Privacy
Differential privacy is a powerful technique that adds carefully calibrated noise to the results of data analysis, making it extremely difficult to infer individual data points from the aggregate results. This approach guarantees that the inclusion or exclusion of a single individual’s data has a negligible impact on the overall outcome. The level of noise added is determined by a privacy parameter (ε), which controls the trade-off between privacy and accuracy.
A smaller ε value provides stronger privacy guarantees but may reduce the accuracy of the analysis. Differential privacy can be implemented in various ways, including adding noise to query responses or using differentially private mechanisms for data release. For instance, a differentially private algorithm could be used to analyze census data, providing aggregate statistics on income levels without revealing the income of any specific individual.
The level of privacy offered is mathematically provable, making it a robust technique for protecting sensitive information.
Ethical Considerations for AI Development Related to Data Privacy
Developing ethical AI systems requires a careful consideration of various ethical principles. Transparency is paramount: users should be informed about how their data is collected, used, and protected. Accountability mechanisms should be in place to address any potential misuse of data. Fairness is crucial; AI systems should not discriminate against certain groups or individuals based on protected characteristics.
Furthermore, data security measures must be implemented to prevent unauthorized access or breaches. Finally, user consent should be freely given, informed, and specific, ensuring individuals have control over their personal data. These considerations should be integrated throughout the entire AI lifecycle, from design and development to deployment and monitoring. Failure to address these ethical implications can lead to significant negative consequences, undermining public trust and hindering the responsible adoption of AI technologies.
The Impact of Data Privacy on AI Adoption Decisions
Data privacy is no longer a secondary concern for organizations considering AI adoption; it’s a primary driver shaping decisions about which technologies to implement and which vendors to partner with. The increasing regulatory landscape, coupled with heightened public awareness of data breaches, means that businesses must carefully weigh the potential benefits of AI against the risks to their reputation and bottom line associated with data misuse.
This careful consideration permeates every stage of the AI adoption process, from initial planning to ongoing maintenance.Data privacy concerns significantly influence the selection of AI vendors and technologies. Companies are increasingly prioritizing vendors who demonstrate a robust commitment to data security and privacy compliance. This includes looking for vendors with strong track records, certifications like ISO 27001, and transparent data handling practices.
The choice of AI technology itself is also influenced by privacy considerations. For example, federated learning techniques, which allow for model training on decentralized data without the need to centralize sensitive information, are becoming increasingly popular due to their enhanced privacy capabilities. Conversely, technologies that require the aggregation and centralization of large datasets are scrutinized more closely, leading many organizations to opt for more privacy-preserving alternatives.
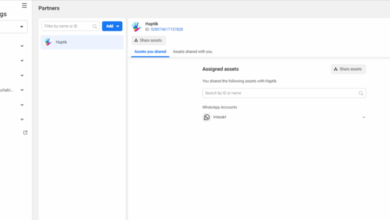
Vendor Selection and Data Privacy Compliance
Companies are actively seeking out AI vendors who demonstrate strong data privacy practices. This involves scrutinizing vendor contracts for clauses regarding data ownership, access control, and data destruction protocols. Furthermore, companies are increasingly conducting thorough due diligence on vendors, including audits and background checks, to assess their security posture and compliance with relevant regulations such as GDPR and CCPA.
Data privacy and security are top concerns for businesses considering AI, rightfully so! Building secure AI solutions requires careful planning, and that’s where platforms like Domino, discussed in this great article on domino app dev the low code and pro code future , become crucial. Ultimately, robust development methods are key to mitigating those data privacy and security risks inherent in AI adoption.
The emphasis is shifting from simply choosing the most technically advanced solution to selecting the solution that best balances technological capabilities with robust privacy safeguards. This often translates to a higher initial investment, but it’s viewed as a necessary cost to mitigate long-term risks.
Addressing Data Privacy Challenges to Accelerate AI Adoption
Several strategies are employed to address data privacy challenges and accelerate AI adoption. Differential privacy, a technique that adds carefully calibrated noise to datasets to protect individual data points while preserving aggregate trends, is gaining traction. Homomorphic encryption, which allows computations to be performed on encrypted data without decryption, is another promising technology that protects sensitive data during AI model training and inference.
Furthermore, many organizations are investing in robust data anonymization and pseudonymization techniques to minimize the risk of identifying individuals from the data used for AI applications. These methods allow companies to leverage their data for AI while maintaining compliance with privacy regulations.
Cost Implications of Robust Data Privacy Measures
Implementing robust data privacy measures for AI projects carries significant cost implications. These costs include: investments in secure infrastructure, personnel training on data privacy best practices, the development and implementation of data governance frameworks, and the ongoing monitoring and auditing of data security. The cost of data breaches and regulatory fines can far outweigh the initial investment in data privacy, however, making a proactive approach financially prudent.
The precise costs vary greatly depending on the scale and complexity of the AI project, the sensitivity of the data being used, and the regulatory environment. However, the overall trend is toward a greater emphasis on cost-effective solutions that balance data privacy with the business value of AI.
Visual Representation of Data Privacy Concerns and AI Adoption Rates
Imagine a graph with AI adoption rate on the y-axis and the level of data privacy concern on the x-axis. The x-axis ranges from “Low Concern” to “High Concern,” while the y-axis shows adoption rates from 0% to 100%. The graph would show a clear negative correlation: as data privacy concerns increase (moving along the x-axis from left to right), the AI adoption rate (y-axis) generally decreases.
The line representing this relationship would not be perfectly linear; it might show a steeper decline at higher levels of concern, reflecting the point where the perceived risks outweigh the potential benefits for many organizations. This visualization effectively communicates the significant impact that data privacy worries have on the widespread adoption of AI technologies across various sectors.
Future Trends in AI Data Privacy and Security
The intersection of artificial intelligence and data privacy is rapidly evolving, driven by technological advancements, stricter regulations, and a growing awareness of the ethical implications of AI. Understanding the future trends in this space is crucial for organizations looking to leverage AI responsibly and effectively. This exploration focuses on emerging technologies, regulatory impacts, the role of AI itself in enhancing security, and predictions for the coming years.
Emerging Technologies Enhancing AI Data Privacy and Security
Several emerging technologies hold significant promise for bolstering AI data privacy and security. These technologies offer innovative approaches to data handling, access control, and security protocols, ultimately shaping a more trustworthy AI ecosystem.
- Blockchain Technology: Blockchain’s decentralized and immutable nature can enhance data security and transparency. By recording data access and modifications on a distributed ledger, blockchain can create an auditable trail, making it more difficult for unauthorized actors to tamper with sensitive information used for AI training. For example, a healthcare provider could use blockchain to securely store and share patient data for AI-powered diagnostics, while maintaining a complete record of access and usage.
- Federated Learning: This technique allows AI models to be trained on decentralized datasets without directly sharing the data itself. Instead, individual devices or organizations train local models on their own data, and only the model updates are shared with a central server to improve the overall model accuracy. This approach minimizes the risk of data breaches and protects sensitive information, making it ideal for applications like collaborative drug discovery or personalized recommendations where data privacy is paramount.
For instance, multiple hospitals could collaborate on a disease prediction model without sharing their individual patient records.
- Homomorphic Encryption: This advanced encryption method allows computations to be performed on encrypted data without decryption. This means that AI models can be trained on encrypted data, preserving privacy while still enabling analysis and model building. This technology is still relatively nascent, but its potential for enhancing privacy in AI is substantial. Imagine a financial institution using homomorphic encryption to train a fraud detection model without ever exposing the raw transaction data.
The Impact of New Regulations and Standards on the AI Industry
The landscape of AI regulation is rapidly evolving, with numerous jurisdictions implementing or considering new laws and standards designed to protect data privacy in the context of AI. These regulations will significantly shape the development and deployment of AI systems.The impact of these regulations is multifaceted. It will drive increased investment in privacy-enhancing technologies, necessitate changes in data governance practices, and potentially slow down the adoption of certain AI applications in sectors with strict regulatory environments, such as healthcare and finance.
For example, the GDPR in Europe and CCPA in California have already had a significant influence on how organizations handle personal data, and similar regulations are emerging globally. This increased regulatory scrutiny will push the AI industry towards more responsible and ethical data handling practices.
The Role of AI in Improving Data Privacy and Security
Paradoxically, AI itself can play a crucial role in enhancing data privacy and security. AI-powered tools can be deployed to detect and respond to security threats, analyze large datasets to identify privacy risks, and automate data governance tasks.AI can be used for tasks such as anomaly detection in network traffic to identify potential cyberattacks, or for automated data anonymization techniques to reduce the risk of re-identification.
AI-powered systems can also monitor data access and usage patterns to flag suspicious activities and enforce access control policies. This proactive approach to security and privacy management can greatly improve the overall security posture of AI systems and the data they utilize.
Data privacy and security are top concerns for anyone considering AI adoption; the risks are simply too high to ignore. That’s why understanding solutions like cloud security posture management is crucial, and checking out this article on bitglass and the rise of cloud security posture management is a great place to start. Ultimately, robust security measures are non-negotiable for responsible AI implementation, ensuring both data integrity and user trust.
Predictions for the Future Landscape of AI Data Privacy and Security
The future of AI data privacy and security is likely to be characterized by a continued tension between innovation and regulation. We can anticipate several key trends:The increased adoption of privacy-enhancing technologies will be driven by both regulatory pressures and the growing awareness of the importance of data privacy. We will see more sophisticated AI models capable of handling data securely and ethically, potentially leading to increased trust in AI systems.
However, the development and deployment of these technologies will also present challenges, including the need for robust security measures to protect against new types of attacks targeting these technologies themselves. Furthermore, the complexity of AI systems and the increasing sophistication of adversarial attacks will require a continuous evolution of security and privacy practices to stay ahead of emerging threats.
The ongoing development of international standards and harmonization of regulations will be critical to fostering a global ecosystem where AI can be developed and deployed responsibly, fostering trust and innovation.
Wrap-Up
Ultimately, the successful integration of AI hinges on addressing the very real concerns surrounding data privacy and security. It’s not a matter of choosing between innovation and protection; it’s about finding a harmonious balance. By proactively implementing robust security measures, adhering to ethical guidelines, and staying informed about evolving regulations, businesses can harness the power of AI while safeguarding user trust and upholding ethical standards.
The future of AI is inextricably linked to our ability to navigate these challenges responsibly.
Detailed FAQs
What are the biggest data privacy risks associated with generative AI?
Generative AI models, trained on massive datasets, can inadvertently memorize and reproduce sensitive information, leading to privacy violations. The potential for bias in training data also poses a significant risk.
How can companies demonstrate compliance with data privacy regulations when using AI?
Companies need to implement comprehensive data governance programs, including data minimization, anonymization techniques, robust security measures, and transparent privacy policies. Regular audits and impact assessments are also crucial.
What role does encryption play in securing AI data?
Encryption is vital for protecting AI data both in transit and at rest. It renders data unreadable to unauthorized parties, even if a breach occurs.
What are some emerging technologies that can improve AI data privacy?
Federated learning, homomorphic encryption, and blockchain technology offer promising solutions for enhancing AI data privacy and security by enabling computation on encrypted data or distributed data without compromising privacy.