Understanding Your Customers Intentions Why You Should Care
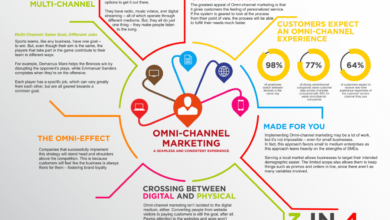
Understanding your customers intentions and why you should care – Understanding your customers’ intentions and why you should care is more than just a business buzzword; it’s the key to unlocking sustainable growth and building genuine connections. Think about it: wouldn’t you rather spend your time and resources on things your customers actually
-want*? This isn’t about guessing; it’s about strategically uncovering their needs and desires to build a business that thrives, not just survives.
This post dives deep into practical methods for understanding what motivates your customers, from analyzing data to conducting insightful interviews. We’ll explore how to translate these insights into actionable strategies, measure their impact, and adapt as your customer base evolves. Get ready to transform your business by truly understanding the “why” behind your customers’ choices.
The Value of Understanding Customer Intentions

Understanding your customers’ intentions is the bedrock of any successful business. It’s not just about knowing what they buy; it’s about delving deeper to understandwhy* they buy it, what motivates their choices, and what unmet needs they might have. This deep understanding directly translates into increased sales, stronger customer loyalty, and ultimately, sustainable business growth.Understanding customer intentions allows businesses to tailor their offerings, marketing strategies, and customer service to precisely meet the needs and desires of their target audience.
This targeted approach is far more effective than a generic, one-size-fits-all strategy, leading to a higher return on investment and a stronger competitive advantage.
Examples of Businesses Thriving Through Customer Intention Understanding
Several companies have demonstrated the power of understanding customer intentions. Netflix, for example, utilizes vast amounts of data on viewing habits to personalize recommendations and create original content that aligns with viewer preferences. This data-driven approach has propelled Netflix to become a global entertainment giant. Similarly, Amazon’s recommendation engine, fueled by a deep understanding of customer browsing and purchasing behavior, drives a significant portion of its sales.
By anticipating customer needs and presenting relevant products, Amazon has created a highly personalized and efficient shopping experience.
Negative Consequences of Ignoring Customer Intentions
Imagine a hypothetical scenario: “FloppyDisk”, a company selling outdated floppy disks, stubbornly refuses to adapt to the digital age. They ignore the clear shift in consumer preference towards cloud storage and digital media, continuing to market their product as if it were still in high demand. The result? Declining sales, dwindling profits, and ultimately, business failure. This highlights the critical importance of staying attuned to evolving customer needs and intentions.
Ignoring these shifts can lead to irrelevancy and ultimately, the demise of a business.
Comparison of Successful and Unsuccessful Business Strategies
| Feature | Successful Businesses | Unsuccessful Businesses |
|---|---|---|
| Customer Research | Regularly conduct in-depth market research, including surveys, focus groups, and data analytics to understand customer needs and motivations. | Limited or no market research; rely on assumptions and gut feelings rather than data. |
| Product Development | Develop products and services that directly address identified customer needs and pain points. Iterate based on customer feedback. | Develop products based on internal assumptions, ignoring customer feedback and market trends. |
| Marketing & Communication | Tailor marketing messages to resonate with specific customer segments, emphasizing the value proposition relevant to their intentions. | Use generic marketing messages that fail to connect with the target audience’s needs or desires. |
| Customer Service | Provide personalized and proactive customer service that addresses individual customer needs and concerns. | Offer impersonal and reactive customer service, failing to build strong customer relationships. |
Methods for Uncovering Customer Intentions
Understanding your customers’ intentions is crucial for business success. It allows you to tailor your products, services, and marketing efforts to resonate with their needs and desires, ultimately leading to increased customer satisfaction and loyalty. But how do you actually uncover these often unspoken intentions? Several methods exist, each with its own strengths and weaknesses.
Gathering data on customer intentions involves a blend of qualitative and quantitative approaches. Qualitative methods delve into the “why” behind customer behavior, providing rich insights into motivations and feelings. Quantitative methods, on the other hand, focus on measurable data, providing a broader picture of trends and patterns. A balanced approach, combining both, offers the most comprehensive understanding.
Surveys, Understanding your customers intentions and why you should care
Surveys are a widely used quantitative method for gathering data on customer intentions. They can be distributed online, via mail, or even in person, allowing for broad reach and the collection of structured data. However, response rates can be low, and the reliance on pre-defined answers might miss nuanced intentions. For example, a simple multiple-choice question about preferred product features might overlook a crucial unmet need that isn’t explicitly listed.
Furthermore, poorly designed surveys can lead to biased or unreliable results.
Focus Groups
Focus groups offer a qualitative approach, bringing together a small group of customers to discuss a specific topic. Moderated discussions can uncover deeper insights into customer motivations, perceptions, and intentions than surveys can. However, focus groups can be expensive and time-consuming to conduct, and the results might not be generalizable to the broader customer base. The presence of a moderator can also influence participant responses.
For instance, participants might be more inclined to offer answers they believe the moderator wants to hear.
Social Media Monitoring
Social media platforms provide a rich source of qualitative data on customer intentions. By monitoring conversations, comments, and reviews, businesses can gain valuable insights into customer opinions, preferences, and unmet needs. However, this method requires careful analysis and interpretation, as social media data can be noisy and unstructured. Furthermore, the data may not represent the entire customer base, as only a subset of customers are active on social media.
For example, analyzing customer reviews on a product page can reveal common complaints or praise for specific features, but it might not capture the intentions of customers who didn’t leave a review.
Customer Interviews
In-depth customer interviews offer a powerful qualitative method for understanding individual customer intentions. These interviews allow for open-ended questions and deeper exploration of customer motivations and experiences. However, interviews are time-consuming and can be expensive, making it difficult to conduct a large number of them. The interviewer’s skill and ability to build rapport with the interviewee can significantly influence the quality of data obtained.
Effective customer interviews require careful planning and execution. The following steps ensure you gather valuable and reliable information:
- Define clear objectives: Specify the information you want to gather before you start.
- Develop a structured interview guide: Create a list of open-ended questions that will guide the conversation, but allow for flexibility.
- Recruit appropriate participants: Select participants who represent your target customer base.
- Create a comfortable and relaxed atmosphere: Put participants at ease to encourage open and honest responses.
- Listen actively and probe for deeper understanding: Ask follow-up questions to explore interesting points in more detail.
- Record and transcribe the interviews: This ensures you have a complete record of the conversation.
- Analyze the data: Identify key themes and patterns in the responses.
Analyzing Customer Data to Identify Intentions

Understanding customer intentions goes beyond simply knowing what they say they want. It involves digging deeper into the data they generate to uncover the unspoken needs and motivations driving their behavior. By effectively analyzing this data, businesses can gain a significant competitive advantage, crafting products and services that truly resonate with their target audience.
Analyzing customer data requires a multifaceted approach. It’s not just about looking at the numbers; it’s about understanding the context and the story behind those numbers. This involves combining quantitative data (like sales figures and website analytics) with qualitative data (like customer reviews and survey responses) to build a comprehensive picture of customer intentions.
Techniques for Analyzing Customer Data
Several techniques help unveil underlying intentions beyond stated preferences. For instance, sentiment analysis can gauge the emotional tone of customer feedback, revealing underlying satisfaction or frustration. Clustering techniques can group customers with similar behaviors and preferences, highlighting segments with shared intentions. Predictive modeling can forecast future behaviors based on past data, allowing businesses to anticipate needs and proactively address potential issues.
Finally, text mining can unearth valuable insights from unstructured data like open-ended survey responses and social media comments.
Common Biases in Data Interpretation
Interpreting customer data is prone to several biases that can skew results. Confirmation bias, for example, leads us to favor information confirming pre-existing beliefs, potentially overlooking contradictory evidence. Selection bias occurs when the sample of data isn’t representative of the entire customer base. Survivorship bias focuses only on successful outcomes, ignoring failures which could offer valuable lessons. Finally, anchoring bias can lead to overreliance on initial data points, influencing subsequent interpretations.
Being aware of these biases is crucial for objective analysis.
A Step-by-Step Guide to Interpreting Complex Customer Feedback
Interpreting complex customer feedback requires a systematic approach. First, gather all relevant data sources – surveys, reviews, social media comments, support tickets. Second, organize and categorize this data, perhaps using thematic analysis to identify recurring themes and sentiments. Third, analyze the data using appropriate techniques like sentiment analysis or qualitative coding. Fourth, synthesize the findings, identifying key patterns and insights.
Finally, validate the interpretations by checking them against other data sources and business knowledge.
Visualizing Customer Data to Reveal Hidden Intentions
Visualizations are critical for revealing hidden patterns in customer data. A well-designed chart or graph can quickly communicate complex information, making it easier to identify trends and insights.
Consider these examples:
| Visualization Type | Data Represented | Insight Revealed | Example |
|---|---|---|---|
| Scatter Plot | Customer age vs. spending | Correlation between age and spending habits | A scatter plot showing a positive correlation between age and spending on luxury goods, indicating a potential target market. |
| Bar Chart | Customer satisfaction ratings by product feature | Areas for product improvement | A bar chart showing low satisfaction scores for a specific product feature, highlighting the need for design changes. |
| Heatmap | Website clickstream data | User navigation patterns and areas of interest | A heatmap showing high click density on certain website sections, revealing popular content and potential areas for improvement in website navigation. |
| Pie Chart | Customer demographics | Market segmentation | A pie chart showing the proportion of customers from different age groups, geographic locations, or income levels. |
Translating Intentions into Actionable Strategies
Understanding customer intentions is only half the battle. The real value lies in translating those insights into concrete strategies that drive business growth. This involves transforming qualitative data into quantitative goals and developing targeted marketing and product development plans. We need to move from “knowing what customers want” to “doing something about it.”
This process requires a structured approach. We need to define specific, measurable, achievable, relevant, and time-bound (SMART) goals based on the identified customer intentions. These goals will form the foundation of our actionable strategies, providing a clear roadmap for implementation and measurement of success. By aligning our actions directly with customer desires, we maximize our chances of achieving our business objectives.
SMART Goal Setting Based on Customer Intentions
Let’s illustrate how to translate customer intentions into SMART goals. Imagine our customer intention research reveals a significant segment of our customers intend to purchase a premium version of our product for its advanced features, but are hesitant due to the price. This translates into a SMART goal:
Increase sales of the premium product by 25% within the next quarter by implementing a targeted marketing campaign focusing on the value proposition of the advanced features and offering a limited-time discount.
This goal is specific (increase premium product sales), measurable (25% increase), achievable (a realistic target based on market analysis), relevant (directly addresses the identified customer intention), and time-bound (within the next quarter). Other intentions might lead to different goals, such as improving customer service response time or expanding product offerings.
Marketing Strategies Based on Customer Intentions
Different customer intentions necessitate different marketing strategies. For instance, if customers express an intention to use our product more frequently, a loyalty program with rewards could be implemented. If they show an intention to switch to a competitor due to pricing, a competitive pricing strategy or value-added services might be the answer. If customers express a need for better tutorials, creating comprehensive online guides and video tutorials would be an effective strategy.
Consider a hypothetical example: a coffee shop discovers through customer surveys that customers intend to buy more coffee if they had more convenient mobile ordering options. This intention directly translates into a marketing strategy of developing a mobile app for ordering and payment. Another example: a clothing retailer finds that customers intend to purchase more sustainably sourced clothing. This leads to a marketing strategy focused on highlighting the sustainable aspects of their product line and sourcing more sustainable materials.
Case Studies of Successful Implementation
Many companies have successfully leveraged customer intention data to improve their products and services. Netflix, for example, uses viewing data to understand viewer intentions and preferences, leading to personalized recommendations and the creation of original content tailored to specific audience segments. This has been instrumental in their continued success. Another example is Spotify, which uses listening data to curate personalized playlists and recommend new music based on user listening habits, reflecting the users’ underlying intention to discover new music they will enjoy.
Flowchart: Transforming Customer Insights into Actionable Strategies
The process of transforming customer insights into actionable strategies can be visualized using a flowchart.
The flowchart would begin with “Identify Customer Intentions” (using methods like surveys, focus groups, social listening, etc.), flowing into “Analyze Customer Data” (to identify patterns and trends), followed by “Define SMART Goals” (based on the identified intentions), leading to “Develop Actionable Strategies” (marketing campaigns, product improvements, etc.), and finally “Implement and Monitor” (track progress, make adjustments as needed). Each stage would have decision points and feedback loops to ensure continuous improvement and alignment with customer needs.
The flowchart would visually represent the iterative nature of the process, emphasizing the importance of continuous monitoring and adaptation based on ongoing customer feedback.
Measuring the Impact of Understanding Customer Intentions
Understanding customer intentions isn’t just a nice-to-have; it’s a crucial driver of business success. But how do you actuallyprove* its value? Measuring the impact requires a strategic approach, focusing on key performance indicators (KPIs) that directly reflect the success of strategies informed by customer insights. By tracking these metrics, you can demonstrate the tangible return on investment (ROI) of understanding your customers.
Effective measurement requires a clear link between the customer intentions you’ve identified and the resulting business outcomes. This involves setting specific, measurable, achievable, relevant, and time-bound (SMART) goals based on your customer insights, and then choosing KPIs that directly reflect progress toward those goals. This isn’t just about vanity metrics; it’s about showing how a deeper understanding of customer needs has led to tangible improvements in key areas of your business.
Key Performance Indicators (KPIs) for Measuring Impact
Several KPIs can effectively demonstrate the value of understanding customer intentions. The specific KPIs you choose will depend on your business goals and the types of intentions you’ve identified. However, some common and powerful indicators include:
- Conversion Rate: This measures the percentage of website visitors or leads who complete a desired action (e.g., making a purchase, signing up for a newsletter). An increase in conversion rate directly demonstrates the effectiveness of strategies tailored to customer intentions.
- Customer Lifetime Value (CLTV): This metric measures the total revenue a customer is expected to generate throughout their relationship with your business. By focusing on high-value customer segments identified through intention understanding, you can significantly increase CLTV.
- Customer Churn Rate: This indicates the percentage of customers who stop doing business with you within a specific period. By addressing customer pain points and unmet needs revealed through intention analysis, you can reduce churn and improve customer retention.
- Customer Satisfaction (CSAT) Score: This measures how satisfied your customers are with your products or services. Improvements in CSAT scores directly reflect the positive impact of meeting customer needs and expectations.
- Net Promoter Score (NPS): This measures customer loyalty and willingness to recommend your business to others. A higher NPS score suggests that your efforts to understand and meet customer intentions are paying off.
Tracking Progress Towards Goals
Tracking progress requires a systematic approach. Regular monitoring of your chosen KPIs, combined with qualitative feedback from customers, allows you to assess the effectiveness of your strategies and make necessary adjustments. This could involve using dashboards to visualize key metrics, setting up automated alerts for significant changes, and conducting regular customer surveys to gauge satisfaction and identify areas for improvement.
Sample Impact Report
A report demonstrating the impact of understanding customer intentions should clearly articulate the goals, the strategies implemented, the KPIs tracked, and the results achieved. Here’s a simplified example:
| Goal | Strategy | KPI | Baseline (Before) | After (Post-Implementation) | % Change |
|---|---|---|---|---|---|
| Increase Conversion Rate on Website | Redesigned website based on user journey analysis revealing a desire for simpler navigation | Conversion Rate | 2% | 4% | +100% |
| Improve Customer Retention | Implemented a proactive customer support system based on identified customer pain points | Customer Churn Rate | 15% | 8% | -47% |
Using A/B Testing to Compare Strategies
A/B testing is a powerful method for comparing the effectiveness of different strategies informed by customer intentions. By creating two versions of a website, email campaign, or other marketing material, and randomly assigning users to each version, you can directly measure which approach resonates better with your target audience. For example, you could test two different website designs, both informed by customer intentions, to see which one drives higher conversion rates.
The results of A/B testing provide concrete evidence of which strategy is most effective in achieving your goals.
Adapting to Evolving Customer Intentions
Understanding customer intentions isn’t a one-time task; it’s an ongoing process. The market, technology, and even societal trends are constantly shifting, meaning what customers want and expect today might be entirely different tomorrow. Successfully navigating this dynamic landscape requires a commitment to continuous monitoring, adaptation, and a proactive approach to anticipating future needs.The ability to adapt to evolving customer intentions is crucial for business survival and growth.
Failing to keep pace with changing preferences can lead to declining sales, loss of market share, and ultimately, business failure. Conversely, companies that effectively monitor and respond to shifting customer needs are well-positioned to thrive in a competitive market. They can leverage these insights to innovate, refine their offerings, and strengthen their customer relationships.
Identifying Emerging Trends and Anticipating Future Needs
Identifying emerging trends requires a multi-faceted approach. This involves analyzing various data sources, including social media listening, customer feedback surveys, market research reports, and competitor analysis. By carefully examining these data points, businesses can start to identify patterns and predict future customer needs. For example, a surge in online searches for “sustainable fashion” might indicate a growing customer preference for environmentally friendly products.
Similarly, an increase in negative reviews related to a particular product feature could signal a need for design improvements. Combining quantitative data (like sales figures and website analytics) with qualitative data (like customer interviews and focus groups) provides a more complete picture of emerging trends and allows for more accurate predictions. Proactive businesses often invest in trend forecasting tools and techniques to further refine their ability to anticipate future customer needs.
Examples of Successful Adaptation to Shifting Customer Intentions
Netflix’s transition from DVD rentals to a streaming service is a prime example of successfully adapting to evolving customer intentions. Recognizing the growing demand for on-demand, digital content, Netflix proactively invested in streaming technology and shifted its business model accordingly. This strategic adaptation not only saved the company but also propelled it to become a global entertainment giant.
Similarly, the rise of mobile commerce forced many brick-and-mortar retailers to develop robust e-commerce platforms to meet the changing shopping habits of their customers. Those who failed to adapt quickly faced significant challenges, while those who embraced the shift thrived. Another compelling example is the rapid growth of plant-based meat alternatives. Driven by increasing consumer interest in health, sustainability, and ethical food choices, companies like Beyond Meat and Impossible Foods have capitalized on this shift in customer intentions, experiencing significant growth and reshaping the food industry.
Best Practices for Staying Ahead of the Curve
Staying ahead of the curve requires a proactive and multifaceted approach. Here are some best practices to consider:
Implementing these strategies will empower businesses to not only react to changing customer intentions but to anticipate them, placing them in a position of strength and innovation within their respective markets.
- Continuous Monitoring: Regularly track key metrics, analyze customer feedback, and actively monitor social media conversations to detect shifts in customer preferences.
- Proactive Research: Conduct regular market research, including surveys, focus groups, and interviews, to understand emerging trends and unmet needs.
- Agile Development: Adopt an agile approach to product development, allowing for rapid iteration and adaptation based on customer feedback.
- Data-Driven Decision Making: Use data analytics to identify patterns, predict future trends, and inform strategic decisions.
- Customer Relationship Management (CRM): Leverage CRM systems to personalize customer interactions and proactively address evolving needs.
- Embrace Experimentation: Test new products, services, and marketing strategies to gauge customer response and refine your offerings.
- Invest in Employee Training: Equip your team with the skills and knowledge needed to understand and respond to changing customer expectations.
Final Thoughts
Ultimately, understanding your customers’ intentions isn’t just about boosting sales; it’s about building a loyal following and creating a business that resonates with its audience. By consistently seeking to understand your customers’ motivations, you’ll not only improve your bottom line but also foster a deeper connection with your brand. It’s a continuous journey of learning, adapting, and building a business that truly serves its customers.
So, start listening – your customers are talking!
Popular Questions: Understanding Your Customers Intentions And Why You Should Care
How do I know if my current methods of understanding customer intentions are effective?
Track key performance indicators (KPIs) like customer satisfaction, retention rates, and conversion rates. Compare these metrics before and after implementing strategies based on customer insights. A significant improvement indicates effectiveness.
What if my customers don’t explicitly state their intentions?
Look beyond stated preferences. Analyze their behavior (website activity, purchase history, social media engagement) to uncover underlying intentions. Qualitative methods like interviews and focus groups can also reveal hidden motivations.
How much time and resources should I dedicate to understanding customer intentions?
It’s an ongoing process, not a one-time project. Start with a small, focused initiative, then gradually integrate customer intention understanding into your regular workflow. The return on investment justifies the effort.
What if my customer base is diverse and has conflicting intentions?
Segment your customer base into smaller groups with shared characteristics and intentions. Tailor your strategies to each segment to address their specific needs and motivations.