Low Bandwidth BlackNurse DDoS Attacks Firewall Disruption
Low bandwidth blacknurse ddos attacks can disrupt firewalls, a surprisingly potent threat often overlooked in favor of high-bandwidth assaults. These stealthy attacks exploit firewall vulnerabilities, using minimal bandwidth to overwhelm resources and cause significant disruptions. Understanding the intricacies of these attacks, from their varied methods to the effective mitigation strategies, is crucial for network security professionals.
This in-depth analysis delves into the mechanics of low-bandwidth DDoS attacks, focusing on how they target firewalls and the cascading effects on network operations. We’ll explore the motivations behind these attacks, the common techniques employed, and crucial strategies for defending against them.
Introduction to Low Bandwidth DDoS Attacks
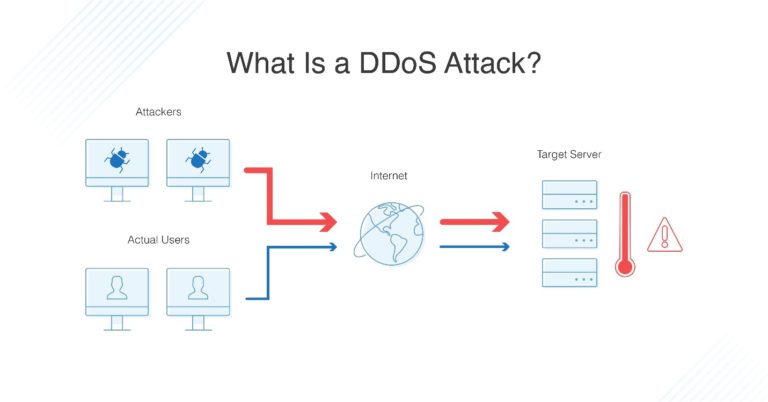
Low bandwidth Distributed Denial-of-Service (DDoS) attacks, often overlooked in favor of their high-bandwidth counterparts, pose a significant threat to online infrastructure. These attacks, while seemingly less potent, can be highly effective when deployed strategically and are capable of causing considerable disruption. They leverage the unique vulnerabilities of specific targets and exploit network protocols to overwhelm the targeted systems, resulting in service outages and financial losses.Low bandwidth DDoS attacks differ from high-bandwidth attacks in their approach and impact.
While high-bandwidth attacks rely on overwhelming the target with massive amounts of traffic, low bandwidth attacks focus on exploiting vulnerabilities and creating significant network congestion with smaller, more targeted packets. This characteristic makes them more difficult to detect and mitigate, as they can often slip past traditional security measures designed to identify and block large-scale attacks.
Types of Low Bandwidth DDoS Attacks
Low bandwidth DDoS attacks encompass a variety of techniques, each exploiting specific weaknesses in network protocols or applications. Examples include:
- SYN Flood: This attack floods the target with SYN requests, a common part of the TCP connection establishment process. The target responds with SYN-ACK packets, but the attacker never completes the connection, tying up resources on the target’s server.
- UDP Flood: This attack sends a massive volume of UDP packets to the target’s server. These packets often have random ports, making it difficult for the server to determine which packets are legitimate and leading to significant processing overhead.
- Fragmentation Attacks: The attacker fragments packets in a way that overwhelms the target’s ability to reassemble them, causing delays and resource depletion.
- Ping of Death: This attack sends malformed ICMP (Internet Control Message Protocol) echo request packets that exceed the maximum size allowed by the target system, causing it to crash.
These attacks are not mutually exclusive; attackers may employ multiple techniques simultaneously or in sequence to amplify the impact of the attack.
Motivations Behind Low Bandwidth DDoS Attacks
The motivations behind low bandwidth DDoS attacks vary, but they often stem from a desire to disrupt services, damage reputations, or extort financial gains. These motivations can range from political activism to financial gain. Some attacks are launched by individuals seeking notoriety, while others are carried out by organized groups with specific agendas. Further, attacks may be launched to disrupt competitor businesses, or simply as a form of malicious mischief.
Comparison of Low and High Bandwidth DDoS Attacks
| Attack Type | Bandwidth | Target | Impact |
|---|---|---|---|
| High Bandwidth DDoS | High (Gigabits per second or more) | Broad range of servers and networks | Overwhelm the target with sheer volume of traffic |
| Low Bandwidth DDoS | Low (Kilobits to Megabits per second) | Specific vulnerabilities and services | Exploit specific weaknesses to cause significant disruption with minimal traffic volume. |
Targeting Firewalls with Low Bandwidth DDoS: Low Bandwidth Blacknurse Ddos Attacks Can Disrupt Firewalls
Low bandwidth DDoS attacks, while seemingly insignificant due to their modest data volume, pose a surprising threat to network infrastructure. These attacks exploit vulnerabilities in firewalls and other security systems, often achieving devastating results disproportionate to the attack’s size. Understanding the tactics employed in such attacks is crucial for developing effective defense strategies.Low bandwidth attacks, though less noticeable than high-volume floods, can still cripple network performance and availability.
By concentrating on specific vulnerabilities, attackers can effectively overload firewall resources and disrupt services, sometimes with minimal detectable traffic. This requires a shift in perspective from solely considering attack volume to examining the specific attack methods and exploiting points.
Firewall Vulnerabilities to Low Bandwidth DDoS
Firewalls, acting as the gatekeepers of network traffic, are often the primary targets of low bandwidth DDoS attacks. These attacks leverage the inherent limitations and design flaws within firewall software, often exploiting features intended for normal network functions.
Attack Methods Exploiting Firewall Weaknesses
Low bandwidth DDoS attacks utilize various techniques to exploit firewall vulnerabilities. These methods are often subtle, making detection and mitigation challenging. Some common methods involve:
- Exploiting specific protocols: Targeted attacks against protocols like HTTP, DNS, or even custom protocols designed for specific applications can overwhelm the firewall’s processing capacity. This can lead to a denial of service for legitimate users trying to access resources.
- Triggering intensive processing loops: Crafting requests that induce complex processing within the firewall, such as recursive queries or intricate pattern matching, can consume significant resources, making the firewall unresponsive.
- Leveraging firewall configuration flaws: Vulnerabilities in the firewall’s configuration, such as improper access controls or misconfigured security rules, can be exploited to direct traffic toward specific resources, overwhelming them. This includes misconfigured rate limiting or insufficient memory allocated for handling incoming connections.
Common Low Bandwidth DDoS Attack Methods Against Firewalls
The common thread in low bandwidth DDoS attacks against firewalls is to exploit specific vulnerabilities in their handling of certain types of traffic. Attackers don’t just flood the firewall with data; they flood it with the
Low-bandwidth black nurse DDoS attacks, though seemingly subtle, can surprisingly disrupt firewalls. This vulnerability often gets overlooked, but understanding the potential impact is crucial. Fortunately, the Department of Justice Offers Safe Harbor for MA Transactions here is a great example of proactive measures. These protections are vital, as even seemingly minor attacks can cause substantial issues, and this is a key consideration for network security strategies, especially when facing low-bandwidth black nurse DDoS attacks.
right* kind of data to trigger specific responses. Examples include
- Slowloris: This technique gradually consumes firewall resources by sending incomplete HTTP requests, forcing the firewall to maintain open connections. This overwhelms the server’s ability to handle new connections, leading to a denial of service.
- HTTP Flood: A variation of Slowloris, where the attack sends numerous partial HTTP requests, tying up connections and consuming CPU resources. It aims to exhaust the available resources, including the firewall’s connection pools and processing capabilities.
- Connection Flood: This method overwhelms the firewall by establishing numerous connections to a target server or resource. This method aims to exhaust the available connections the firewall can handle, resulting in a denial of service.
Firewall Vulnerability and Exploitation Summary
| Vulnerability | Attack Method | Impact | Mitigation |
|---|---|---|---|
| Protocol-Specific Exploits | Targeted requests against specific protocols (e.g., DNS, HTTP) | Firewall overload, service disruption | Stronger protocol filtering, rate limiting |
| Configuration Flaws | Exploiting misconfigured access controls or security rules | Directed traffic overload, resource exhaustion | Regular firewall configuration audits, security hardening |
| Resource Exhaustion | Slowloris, HTTP flood, connection flood | CPU overload, memory exhaustion, connection pool depletion | Advanced firewall features, intrusion detection systems, traffic shaping |
Impact on Network Operations
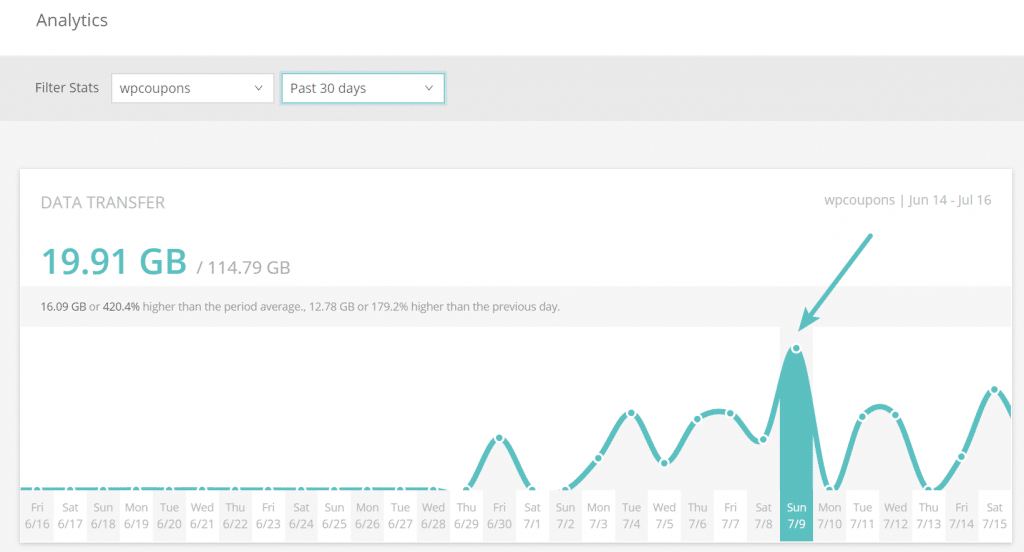
Low-bandwidth DDoS attacks, though seemingly insignificant due to their small volume of traffic, can inflict surprisingly devastating consequences on network operations. These attacks, often underestimated, can effectively cripple a network’s performance and disrupt critical services. Their stealthy nature makes them challenging to detect and mitigate, further exacerbating the impact on affected organizations.Low-bandwidth attacks can overload network resources and disrupt operations in various ways.
They exploit vulnerabilities in network infrastructure, particularly firewalls, to achieve their disruptive goals. By targeting the firewall, attackers can significantly hinder the network’s ability to function normally, leading to widespread service disruptions and slowdowns for legitimate users. The insidious nature of these attacks lies in their ability to generate a considerable impact with a comparatively small amount of traffic.
Consequences of Low-Bandwidth DDoS Attacks on Network Operations
Low-bandwidth DDoS attacks can cause a cascade of problems, affecting various aspects of network functionality. These attacks can disrupt essential services, leading to significant financial losses and reputational damage.
Low-bandwidth blacknurse DDoS attacks, surprisingly, can sometimes overwhelm firewalls, even though they seem minor. This highlights the need for proactive security measures beyond basic firewall configurations. Modernizing our approach to code security is crucial, like deploying AI code safety goggles to help identify vulnerabilities before they become exploits, as detailed in Deploying AI Code Safety Goggles Needed.
Ultimately, these advanced tools can help prevent the types of disruptions caused by those seemingly small but impactful low-bandwidth blacknurse DDoS attacks.
Disruptions to Network Operations
Low-bandwidth DDoS attacks can disrupt network operations in several ways. They can flood the firewall with illegitimate requests, consuming its processing capacity and preventing it from handling legitimate traffic. This overload can cause service disruptions and slowdowns, impacting everything from website access to internal communications. By exploiting vulnerabilities in the firewall’s configuration or design, attackers can overwhelm its processing capabilities, leading to a complete denial of service.
This can result in decreased efficiency, increased costs, and significant downtime for legitimate users.
Service Disruptions and Slowdowns
Service disruptions and slowdowns are direct consequences of a low-bandwidth DDoS attack. These attacks can lead to website outages, email delivery delays, and difficulty accessing online resources. The cumulative effect of these disruptions can lead to a significant loss of productivity and revenue for the affected organization. Furthermore, the unpredictable nature of these attacks makes it difficult to implement preventative measures, as the attacker can easily adapt and change their approach.
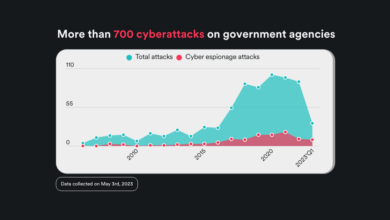
Real-World Examples of Low-Bandwidth DDoS Attacks
Several documented incidents highlight the real-world impact of low-bandwidth DDoS attacks. For example, a small-scale attack targeting a specific gaming server could cause lag and disconnections for players, resulting in lost revenue and a negative user experience. Similarly, a similar attack targeting an online retailer could result in transaction failures and lost sales. These instances underscore the potential for widespread disruption even with a seemingly minor attack.
Flowchart of a Low-Bandwidth DDoS Attack Targeting a Firewall
[Start] --> [Attacker Identifies Target Firewall] --> [Attacker Chooses Attack Vector] --> [Attacker Initiates Attack] --> [Firewall Overwhelmed by illegitimate Requests] --> [Firewall Slows Down or Crashes] --> [Service Disruptions Occur] --> [End]
The flowchart above illustrates the general steps involved in a low-bandwidth DDoS attack targeting a network’s firewall. The simplicity of the attack vector hides the potentially devastating impact it can have on the target network.
Techniques to Disrupt Firewalls

Low-bandwidth DDoS attacks, while seemingly less powerful than their high-bandwidth counterparts, can be surprisingly effective at disrupting firewall performance. They leverage subtle but persistent resource exhaustion to overwhelm the firewall’s capacity, causing it to malfunction or become unresponsive. These attacks often rely on clever techniques that exploit the very architecture of firewalls, making them a significant threat.
Targeting firewalls with low-bandwidth attacks requires a deep understanding of the firewall’s internal workings and vulnerabilities. Attackers tailor their methods to exploit weaknesses in the firewall’s processing and memory management, creating a sustained stream of requests that exhaust resources.
Spoofing and Amplification Techniques
Spoofing and amplification techniques are frequently used in low-bandwidth DDoS attacks against firewalls. Spoofing involves forging source IP addresses to mask the true origin of the attack traffic. This can overwhelm the firewall’s ability to filter legitimate traffic from malicious requests. Amplification techniques involve exploiting services like DNS or NTP to amplify the impact of the attack. A small number of requests from the attacker can generate a large volume of responses from the targeted service, flooding the firewall with traffic.
Application-Layer Attacks
Application-layer attacks target specific vulnerabilities in the firewall’s application layer protocols. These attacks are designed to consume significant processing resources within the firewall. For example, an attacker might send a large number of complex HTTP requests, each requiring extensive processing by the firewall.
Examples of Attack Scenarios
One common scenario involves sending a flood of requests to a firewall’s authentication service. Each request requires substantial processing, leading to a backlog and ultimately slowing down the entire system. Another scenario is overwhelming the firewall’s intrusion detection system (IDS) with crafted packets designed to trigger false positives, causing it to consume excessive resources. These examples demonstrate how seemingly small amounts of traffic can be detrimental when strategically targeted at specific functions within the firewall.
Common Low Bandwidth DDoS Attack Techniques
- HTTP Flood: A continuous stream of HTTP requests targeting a specific web application or service. This technique leverages the resources needed to process each request.
Example: A large volume of GET or POST requests to a web server, often with complex headers, can overwhelm the firewall.
- SYN Flood: Exploiting the TCP three-way handshake. Attackers send a large number of SYN requests but never complete the connection, consuming firewall resources in trying to establish these connections.
Example: A significant number of SYN packets are sent without acknowledging any of the subsequent packets, resulting in an overwhelming queue of half-open connections.
- UDP Flood: Attackers send a large number of UDP packets to various ports on the target. Firewalls often handle UDP traffic differently, sometimes making it more vulnerable.
Example: A massive UDP flood to port 53 (DNS) can consume significant firewall resources as it attempts to process each packet.
- DNS Amplification: Attackers exploit DNS servers by sending spoofed requests. Legitimate DNS servers respond to these requests, creating a large volume of amplified traffic directed at the target firewall.
Example: An attacker sends a small DNS query to an open DNS resolver, and in return receives a massive DNS response, overwhelming the target.
Mitigation Strategies
Low-bandwidth DDoS attacks, though seemingly less potent than their high-bandwidth counterparts, pose a significant threat to firewalls and network operations. These attacks exploit vulnerabilities in firewall configurations and rely on sustained, often subtle, traffic to overwhelm the system’s resources. Effective mitigation requires a multi-faceted approach that combines various techniques to identify, filter, and contain malicious traffic.
Traffic Filtering and Rate Limiting
Traffic filtering is a cornerstone of DDoS mitigation. By analyzing incoming traffic based on predefined rules, firewalls can identify and block packets exhibiting characteristics associated with malicious activity. This could include examining source IP addresses, ports, protocols, and packet sizes. Rate limiting complements this by setting limits on the rate at which traffic from a particular source is allowed.
Exceeding these limits triggers the blocking of further traffic from that source, effectively throttling the attack. This method is particularly crucial in low-bandwidth attacks where the sheer volume of requests, though not high, can overwhelm the firewall’s processing capabilities.
Intrusion Detection and Prevention Systems (IDS/IPS)
IDS/IPS systems act as a second line of defense, constantly monitoring network traffic for suspicious patterns. These systems identify anomalies, including those indicative of DDoS attacks, and can either block the malicious traffic or alert administrators to take action. IDS/IPS solutions are crucial in detecting subtle, low-bandwidth attacks that might slip through traditional firewall filtering. Their proactive nature allows for rapid response and containment of threats before they cause widespread disruption.
Enhanced Firewall Configurations
Strengthening firewall configurations is vital for withstanding low-bandwidth DDoS attacks. This involves configuring firewalls with granular rules tailored to the specific network’s needs and vulnerabilities. Regular updates to firewall firmware are also crucial to ensure the latest security patches are applied. Implementing advanced features like connection tracking and stateful inspection can help identify and block malicious connections more effectively.
By fine-tuning these configurations, administrators can increase the resilience of the firewall to attacks.
Comparison of Mitigation Strategies
| Strategy | Description | Effectiveness | Implementation Complexity |
|---|---|---|---|
| Traffic Filtering | Examining traffic characteristics (IP, ports, protocols) to identify and block malicious packets. | High, when rules are well-defined. | Medium. Requires understanding of network traffic patterns and defining appropriate rules. |
| Rate Limiting | Setting limits on the rate of traffic from a single source. | High, when thresholds are appropriately set. | Medium. Requires careful monitoring and adjustment of thresholds. |
| IDS/IPS | Proactively monitoring network traffic for suspicious patterns and anomalies, potentially blocking or alerting. | High, with well-configured signatures and rules. | High. Requires specialized expertise and regular maintenance of signatures. |
| Enhanced Firewall Configurations | Implementing granular rules, firmware updates, connection tracking, and stateful inspection to increase resilience. | Medium to High, dependent on the level of customization. | Medium to High. Requires understanding of firewall configurations and potential impact of changes. |
Case Studies and Examples
Low-bandwidth DDoS attacks, while often underestimated, can be surprisingly effective in disrupting firewall operations. These attacks leverage the vulnerabilities inherent in firewall designs and configurations, often exploiting limitations in processing power or connection handling capabilities. Understanding real-world examples is crucial to appreciating the potential impact and devising effective mitigation strategies.
Real-World Attack Scenarios, Low bandwidth blacknurse ddos attacks can disrupt firewalls
Low-bandwidth DDoS attacks targeting firewalls often exploit predictable patterns in network traffic. Attackers can flood the firewall with a specific type of packet, or a continuous stream of seemingly innocuous data packets, overwhelming the firewall’s ability to distinguish legitimate traffic from malicious intent. This often leads to performance degradation or complete system shutdown. The impact varies significantly based on the target’s defenses and the nature of the attack.
Specific Techniques Employed
Attackers employ various techniques to achieve a low-bandwidth denial-of-service effect. One common approach involves sending a continuous stream of fragmented packets, designed to overload the firewall’s processing capacity. Another technique involves generating SYN flood packets, but at a much slower rate than in traditional SYN floods. This approach aims to consume firewall resources without overwhelming the network infrastructure as a whole.
The attacker can also exploit vulnerabilities in the firewall’s protocol handling or connection tracking mechanisms.
Impact on Network Operations
The impact of a low-bandwidth DDoS attack on a firewall can be devastating. The firewall, overwhelmed by the constant stream of malicious traffic, might fail to process legitimate requests. This results in service disruptions, preventing users from accessing critical resources. Furthermore, the constant barrage of requests can lead to resource exhaustion, potentially compromising the stability of the entire network infrastructure.
Mitigation Strategies Employed
Various mitigation strategies are used to counter low-bandwidth DDoS attacks. Firewalls can be configured to drop or filter malicious packets based on predefined criteria. Implementing rate-limiting mechanisms helps to prevent the firewall from being overwhelmed by excessive traffic from a single source. Intrusion detection systems (IDS) and intrusion prevention systems (IPS) can help identify and block malicious traffic patterns.
Monitoring network traffic in real-time allows for quick identification of anomalous behavior. This proactive approach is crucial for minimizing the impact of an attack.
Summary of Case Studies
| Attack Details | Impact | Mitigation | Lessons Learned |
|---|---|---|---|
| A financial institution experienced a slow but persistent attack targeting their firewall’s connection tracking mechanism. The attack was characterized by a steady stream of SYN packets. | The firewall’s performance significantly degraded, leading to delays in transaction processing and impacting customer service. | The institution implemented a SYN cookie mechanism and adjusted firewall rules to prioritize legitimate traffic. | Low-bandwidth attacks can still have a considerable impact. Proactive monitoring and flexible mitigation strategies are essential. |
| A web hosting provider was targeted with a fragmented packet attack, aimed at overwhelming the firewall’s packet processing capacity. | The attack caused a significant drop in website responsiveness, impacting the provider’s revenue. | The provider upgraded their firewall hardware and implemented a more robust packet filtering mechanism. | Investing in robust firewall hardware and sophisticated filtering techniques can enhance resistance to low-bandwidth attacks. |
| A government agency faced a sustained attack targeting a specific protocol vulnerability in their firewall. The attacker exploited a known flaw in the protocol handling. | The attack caused a complete disruption of critical services, impacting citizens’ access to government resources. | The agency patched the vulnerability and implemented a more secure protocol stack. | Regular security audits and prompt patching of vulnerabilities are critical for preventing exploitation. |
Future Trends and Predictions
Low-bandwidth DDoS attacks, despite their apparent simplicity, are constantly evolving. The ingenuity of attackers, coupled with the ever-increasing sophistication of network infrastructures, fuels a dynamic interplay of attack and defense. Understanding future trends in these attacks is crucial for proactively strengthening defenses and anticipating emerging threats.
The future of low-bandwidth DDoS attacks will likely involve a combination of established and novel techniques. Attackers will continue to leverage vulnerabilities in existing systems and protocols, but also explore new avenues to exploit emerging technologies. This evolution demands a proactive approach to network security, one that anticipates potential weaknesses and implements adaptive defenses.
Low-bandwidth BlackNurse DDoS attacks, while seemingly subtle, can surprisingly overwhelm firewalls. This is especially true when considering vulnerabilities in cloud services like Azure Cosmos DB, which could potentially be exploited. For more detailed information on the recent Azure Cosmos DB Vulnerability Details, check out this comprehensive resource: Azure Cosmos DB Vulnerability Details. Understanding these vulnerabilities is crucial for bolstering defenses against these types of low-bandwidth attacks and preventing widespread disruptions.
Future Attack Vectors and Techniques
Attackers will likely refine existing low-bandwidth techniques by focusing on exploiting specific network protocols and services. This might include targeting vulnerabilities in widely used protocols like DNS or HTTP, potentially leveraging them in a more nuanced and efficient manner. They might also combine low-bandwidth attacks with other types of attacks, like application-layer attacks, to overwhelm the target’s resources.
Furthermore, attackers may increasingly employ automated tools and scripts to orchestrate these attacks, leading to a higher volume and frequency of such assaults.
Emerging Defense Technologies
New technologies are constantly emerging to combat these attacks. One such technology is the development of more sophisticated intrusion detection and prevention systems (IDS/IPS). These systems will need to be capable of identifying and responding to subtle anomalies and patterns associated with low-bandwidth attacks. Advanced machine learning algorithms can be employed to analyze network traffic, identify suspicious patterns, and trigger appropriate responses, thereby enhancing the effectiveness of security measures.
Furthermore, advanced network segmentation and traffic filtering techniques can be implemented to isolate potential attack sources and prevent widespread damage.
Advancements in Network Security
Advancements in network security are crucial for mitigating the threat of low-bandwidth DDoS attacks. The implementation of proactive security measures, such as robust access controls and regular security audits, can significantly reduce the attack surface. Furthermore, employing network monitoring tools that provide real-time visibility into network traffic can aid in early detection of anomalous activity. By proactively identifying and mitigating vulnerabilities, organizations can create a more resilient network infrastructure capable of withstanding these evolving attacks.
Future Research Directions
Future research in low-bandwidth DDoS attacks should focus on developing more sophisticated detection and mitigation techniques. Researchers should investigate new and innovative ways to identify and analyze low-bandwidth attack patterns in real-time. Furthermore, research into the development of adaptive defense mechanisms that can learn and adapt to changing attack patterns is essential. Investigating the potential impact of emerging technologies, such as the Internet of Things (IoT), on the evolution of low-bandwidth DDoS attacks is also critical.
This comprehensive approach to research will contribute to a more resilient and secure digital ecosystem.
Closure
In conclusion, low-bandwidth DDoS attacks, exemplified by the blacknurse variant, pose a serious threat to network security. Their ability to disrupt firewalls and cause widespread operational issues necessitates proactive measures and a thorough understanding of attack methodologies. By examining the various attack techniques, vulnerabilities, and mitigation strategies discussed, organizations can better prepare for and defend against these evolving threats.
Future research into emerging attack vectors is crucial to staying ahead of the curve in this ever-changing landscape.
User Queries
What distinguishes low bandwidth DDoS attacks from high bandwidth ones?
Low bandwidth attacks rely on the sheer volume of connections, often exploiting specific vulnerabilities, to overwhelm the target. High bandwidth attacks, on the other hand, flood the target with excessive data volume. Both aim to disrupt service, but the means and the target vulnerabilities differ.
What are some common motivations behind low bandwidth DDoS attacks?
Motivations can range from disrupting online services for ideological reasons to causing financial damage or gaining access to sensitive information. These attacks can be launched by various actors, including individuals, groups, or even nation-states.
How can traffic filtering and rate limiting help defend against low bandwidth DDoS attacks?
Traffic filtering can identify and block malicious traffic patterns, while rate limiting controls the rate of incoming connections. These techniques can help prevent attackers from overwhelming the firewall’s resources.
What is the role of intrusion detection and prevention systems (IDS/IPS) in mitigating low bandwidth DDoS attacks?
IDS/IPS systems monitor network traffic for malicious activity, alerting administrators to suspicious patterns and potentially blocking attacks. They are valuable tools in the arsenal of network security.