Kalay Platform Vulnerability IoT Attack Risk
Kalay platform vulnerability exposes millions of IoT devices to cyber attacks, opening a terrifying avenue for hackers to exploit millions of interconnected devices. This vulnerability, impacting everything from smart homes to industrial controls, presents a significant threat to individuals and organizations alike. The potential consequences are vast and demand immediate attention.
The Kalay platform vulnerability affects a wide range of IoT devices, including smart home appliances, industrial controllers, and even medical equipment. This broad reach underscores the critical need for robust security measures across the entire IoT ecosystem.
Introduction to the Kalay Platform Vulnerability
The Kalay platform, a widely used system for connecting Internet of Things (IoT) devices, recently revealed a critical vulnerability. This flaw potentially exposes millions of interconnected devices to cyberattacks, highlighting the escalating risks in the increasingly digitized world. Addressing this vulnerability was crucial to mitigate the substantial potential damage to both individuals and organizations.The vulnerability allowed unauthorized access to the Kalay platform, which controls numerous IoT devices.
This compromised access could be exploited for various malicious purposes, ranging from data theft to the disruption of services. Understanding the nature of the affected devices and the potential consequences is essential for both users and manufacturers.
Affected IoT Device Types
The Kalay platform controls a diverse range of IoT devices. These range from everyday smart home devices to more complex industrial controllers and even medical equipment. This broad spectrum of devices underscores the wide-reaching implications of this vulnerability.
| Category | Examples | Potential Impact |
|---|---|---|
| Smart Home Devices | Smart thermostats, security cameras, smart lighting systems | Unauthorized access could lead to data breaches, privacy violations, and potentially physical harm if coupled with other vulnerabilities. For example, a compromised smart thermostat could lead to energy theft or unwanted temperature adjustments. |
| Industrial Controllers | Manufacturing equipment, automated systems, supply chain monitoring | Disruption of industrial processes, production downtime, potential safety hazards. A compromised industrial controller could disrupt manufacturing lines, leading to substantial financial losses. |
| Medical Devices | Heart monitors, insulin pumps, imaging equipment | Critical health implications, including patient harm, loss of data, or even life-threatening situations. A compromised medical device could alter vital signs readings or malfunction during a critical procedure. |
Potential Impact on Individuals and Organizations
The impact of this vulnerability spans across individuals and organizations, affecting various aspects of daily life. This includes financial losses, privacy violations, and even potential physical harm.The vulnerability’s implications for individuals include compromised personal data, potential financial losses, and the disruption of everyday routines. For organizations, the vulnerability could lead to significant operational disruptions, financial losses, and damage to their reputation.
The risk of data breaches and unauthorized access to sensitive information is particularly concerning. In the case of medical devices, this vulnerability poses a critical health risk, emphasizing the importance of prompt mitigation efforts.
Mitigation and Prevention Strategies
Manufacturers have already released patches and updates to address the vulnerability. Users should promptly install these updates to secure their devices.
“Security updates are crucial in mitigating vulnerabilities and protecting against cyberattacks.”
Understanding the Nature of the Vulnerability
The Kalay Platform vulnerability exposed a significant weakness in a wide range of Internet of Things (IoT) devices, leaving millions susceptible to cyberattacks. Understanding the specific vulnerabilities and how they’re exploited is crucial to mitigating future risks. This analysis delves into the technical details, potential attack vectors, and security flaws that enabled this breach.The Kalay Platform vulnerability exploited a combination of weaknesses, potentially including outdated firmware, insecure communication protocols, and lack of robust authentication mechanisms.
These vulnerabilities allowed attackers to gain unauthorized access to sensitive data and potentially control affected devices. A crucial aspect of understanding this vulnerability is recognizing the interconnected nature of IoT systems and how a single compromised device can open pathways to other connected systems.
Specific Vulnerabilities Exploited
The precise vulnerabilities exploited in the Kalay Platform are not publicly disclosed due to security reasons. However, common IoT vulnerabilities often targeted include weak or default passwords, insecure network configurations, and the use of known, exploitable software flaws in the firmware. These vulnerabilities, if left unpatched, can allow attackers to gain unauthorized access to device functionalities.
Technical Details of the Exploit (Simplified)
Exploiting IoT vulnerabilities often involves exploiting known flaws in the device’s software or communication protocols. Attackers might use automated tools or scripts to scan for vulnerable devices and then attempt to exploit identified weaknesses. This process can be simplified by using readily available tools that can be adapted to specific device types and configurations. For instance, if a device uses an outdated protocol like Telnet or a known vulnerable library, attackers could exploit that weakness to gain access.
Comparison with Other IoT Vulnerabilities
Many IoT vulnerabilities share common characteristics. Often, vulnerabilities stem from inadequate security design choices during the development and deployment of IoT devices. These vulnerabilities frequently involve weak or default passwords, easily guessed or cracked encryption keys, or insufficient access control measures. The Kalay Platform vulnerability is consistent with this pattern of inadequate security practices.
Potential Attack Vectors
Cybercriminals could exploit the Kalay Platform vulnerability through various attack vectors, including:
- Network-based attacks: Exploiting vulnerabilities in the network infrastructure connected to the affected devices. This might involve intercepting communication or manipulating network traffic to gain unauthorized access.
- Compromised Credentials: Exploiting weak or default credentials on devices. Attackers may attempt to brute-force passwords or use stolen credentials to gain access.
- Exploiting Software Flaws: Leveraging vulnerabilities in the firmware or software running on the devices. This could involve exploiting buffer overflows, cross-site scripting (XSS), or other known security flaws.
Potential Methods to Compromise IoT Devices
Compromising IoT devices often involves exploiting known weaknesses in the device’s software or firmware. Attackers might employ sophisticated methods such as exploiting vulnerabilities in communication protocols, or exploiting vulnerabilities in libraries or services the device relies on. Attackers may also employ social engineering techniques to trick users into providing sensitive information.
Security Flaws that Enabled the Vulnerability
Several security flaws potentially enabled the vulnerability in the Kalay Platform. These include:
- Insufficient security hardening: Inadequate security measures implemented during the design and development process. This might involve using easily guessed passwords, weak encryption, or inadequate authentication mechanisms.
- Lack of regular updates and patches: Failing to update the firmware of IoT devices regularly, leaving them vulnerable to known exploits.
- Inadequate security testing: Insufficient security testing during the development lifecycle, leading to the presence of undetected vulnerabilities.
Vulnerability and Risk Level Table
| Vulnerability Category | Description | Risk Level |
|---|---|---|
| Outdated Firmware | Using old, unpatched software versions | High |
| Weak Authentication | Using weak or default passwords | Medium |
| Insecure Communication Protocols | Using unencrypted or vulnerable protocols | High |
| Lack of Access Control | Inadequate access control measures | Medium |
Impact on Various Sectors
The Kalay Platform vulnerability, exposing millions of IoT devices, presents a significant threat across diverse sectors. The interconnected nature of modern systems means a breach in one area can quickly ripple through others, impacting everything from personal convenience to critical infrastructure. Understanding the potential consequences for each sector is crucial to mitigating the risks.
Smart Home Industry
The smart home industry, with its interconnected devices, is particularly vulnerable. A successful attack could compromise numerous appliances, potentially leading to unauthorized access to sensitive data, such as home security systems and personal information. This could allow attackers to remotely control devices, potentially disrupting normal operation or even creating a security risk. For example, a compromised smart thermostat could lead to excessive energy consumption, or a hacked smart lock could allow unauthorized entry into the home.
Industrial Automation Systems
Industrial automation systems, crucial for manufacturing and other critical processes, face severe risks. A breach in these systems could lead to disruptions in production, causing significant economic losses. Compromised control systems could allow attackers to manipulate machinery, potentially leading to safety hazards, equipment damage, and environmental risks. Consider a scenario where a compromised industrial control system controlling a water treatment plant malfunctions, leading to contamination or a sudden power outage.
Critical Infrastructure
Critical infrastructure, such as power grids, water treatment plants, and transportation systems, is highly vulnerable to attack. A successful breach could disrupt essential services, causing widespread damage and economic instability. A compromised power grid could lead to widespread blackouts, affecting homes, businesses, and essential services.
Healthcare Systems and Medical Devices
Healthcare systems and medical devices are increasingly connected, raising concerns about data breaches and patient safety. Compromised medical devices could lead to inaccurate diagnoses, incorrect treatments, or even physical harm to patients. Malicious actors could also steal sensitive patient data, leading to identity theft or other privacy violations. A compromised insulin pump, for example, could lead to potentially life-threatening complications.
The recent Kalay platform vulnerability is a serious concern, exposing millions of IoT devices to potential cyberattacks. This highlights the critical need for robust security measures in the connected devices space. Interestingly, a similar issue, a vulnerability in Azure Cosmos DB, also underscores the importance of scrutinizing cloud-based services. For more details on the Azure Cosmos DB Vulnerability, check out this resource: Azure Cosmos DB Vulnerability Details.
Ultimately, the Kalay platform vulnerability serves as a stark reminder of the ever-present threat landscape in our increasingly interconnected world.
Financial Institutions
Financial institutions rely on interconnected systems for transactions and data storage. A vulnerability in these systems could expose sensitive financial information, leading to fraud and significant financial losses. Hackers could potentially gain access to customer accounts, manipulate transactions, or steal large sums of money. A compromised ATM network could be used to redirect funds to attacker accounts.
| Sector | Potential Impact |
|---|---|
| Smart Homes | Unauthorized access to data, remote control of devices, potential safety risks |
| Industrial Automation | Production disruptions, safety hazards, equipment damage, environmental risks |
| Critical Infrastructure | Disruption of essential services, widespread damage, economic instability |
| Healthcare | Inaccurate diagnoses, incorrect treatments, patient safety risks, data breaches |
| Financial Institutions | Fraud, financial losses, theft of sensitive information |
Mitigation Strategies and Recommendations
The Kalay Platform vulnerability has exposed millions of IoT devices to severe cyber risks. Effective mitigation strategies are crucial to protect these devices and prevent widespread exploitation. These strategies range from patching vulnerable software to implementing robust security protocols for both manufacturers and individual device owners. Addressing this vulnerability requires a multifaceted approach involving all stakeholders in the IoT ecosystem.
Patching Vulnerable Devices
Patching vulnerable devices is paramount. Manufacturers should promptly release and distribute patches to address the identified vulnerabilities. Users need clear instructions and support to apply these patches successfully. Delayed patching significantly increases the risk of exploitation. The process should be standardized and easily accessible to prevent delays and ensure widespread adoption.
Security Best Practices for IoT Device Manufacturers, Kalay platform vulnerability exposes millions of iot devices to cyber attacks
Robust security practices are essential for IoT device manufacturers. These practices include incorporating security by design principles from the initial stages of product development. Regular security audits and penetration testing are vital to identify and address potential vulnerabilities before they are exploited. Implementing secure communication protocols and authentication mechanisms are critical. Manufacturers should also establish clear procedures for handling reported vulnerabilities and prioritize their remediation.
Thorough documentation of security features and processes should be maintained.
Importance of Regular Security Audits for IoT Systems
Regular security audits are indispensable for maintaining the security of IoT systems. These audits help identify vulnerabilities that might have been introduced during development, deployment, or maintenance. Regular assessments ensure that security measures remain effective and that any emerging threats are detected early. Comprehensive audits should cover all aspects of the IoT system, including hardware, software, communication protocols, and data storage.
Strong Passwords and Multi-Factor Authentication
Strong passwords and multi-factor authentication (MFA) are fundamental for protecting IoT devices. Users should be encouraged to create strong, unique passwords for each device. The complexity and length of passwords are essential. Implementing MFA adds an extra layer of security by requiring multiple verification methods. This significantly reduces the risk of unauthorized access, even if a password is compromised.
Secure Network Configurations
Secure network configurations are crucial for protecting IoT devices. Devices should be placed on a separate, secured network segment to limit their exposure. Network segmentation minimizes the impact of a breach on other devices and systems. Proper firewall configurations and intrusion detection systems are necessary to monitor and block malicious activity. Network configurations should be regularly reviewed and updated to reflect evolving threats.
Procedure for Device Owners to Identify and Update Vulnerable Devices
Device owners need a clear procedure for identifying and updating vulnerable devices. Manufacturers should provide readily available tools and resources for device owners to identify their specific devices and determine if they are vulnerable. A clear and easily accessible online database of vulnerabilities and associated patches can be invaluable. A step-by-step guide for applying patches should be provided.
This guide should be easily understandable and accessible to all users, irrespective of their technical expertise.
Mitigation Steps and Effectiveness
| Mitigation Step | Effectiveness |
|---|---|
| Prompt patch releases by manufacturers | High – reduces attack surface |
| Clear instructions and support for patching | High – increases adoption |
| Security by design in device development | High – prevents future vulnerabilities |
| Regular security audits | High – proactive identification of vulnerabilities |
| Strong passwords and MFA | Medium to High – significant security boost |
| Secure network configurations | High – isolates devices and reduces risk |
| User-friendly identification and update tools | High – facilitates user compliance |
Case Studies and Real-World Examples
The Kalay Platform vulnerability highlights a critical weakness in IoT security. Understanding real-world examples of similar attacks provides crucial insights into the potential consequences and necessary mitigation strategies. These cases illuminate the destructive potential of compromised IoT devices and underscore the importance of proactive cybersecurity measures.IoT devices, while convenient, often lack robust security measures. This inherent vulnerability creates a fertile ground for attackers, who can exploit weaknesses to gain unauthorized access to networks and systems.
The recent Kalay platform vulnerability, exposing millions of IoT devices to potential cyberattacks, highlights the urgent need for improved security measures. This underscores the critical role of deploying AI code safety tools like those described in Deploying AI Code Safety Goggles Needed. Ultimately, robust AI-powered security solutions are essential to mitigate vulnerabilities like the one in the Kalay platform, preventing further widespread cyber threats to these vulnerable devices.
The consequences can range from minor inconveniences to significant disruptions and financial losses.
Real-World Examples of IoT Attacks
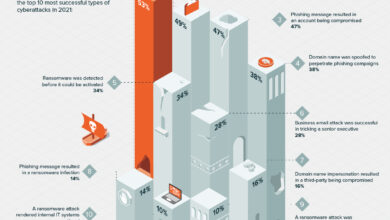
Numerous attacks targeting IoT devices have been reported in recent years. These attacks often exploit vulnerabilities in the devices’ firmware or software, allowing attackers to take control of them and use them for malicious purposes. A notable example is the Mirai botnet attack, which leveraged compromised IoT devices to launch distributed denial-of-service (DDoS) attacks against various targets, including critical infrastructure and online services.
Consequences of IoT Attacks
The consequences of IoT attacks can be far-reaching and devastating. Beyond the immediate disruption caused by DDoS attacks, attackers can utilize compromised devices for various malicious activities. For instance, they might steal sensitive data, install malware, or even use the devices to launch further attacks. The financial losses associated with these attacks can be substantial, as organizations grapple with restoration costs, legal fees, and reputational damage.
Furthermore, the attacks can have a broader impact, affecting public trust and confidence in the systems that rely on these devices.
Response Strategies Implemented by Affected Organizations
Organizations affected by IoT attacks often implement a multifaceted response strategy. This typically includes identifying the compromised devices, isolating them from the network, and patching the vulnerabilities to prevent future attacks. Security audits and penetration testing are also critical to proactively identify and address potential weaknesses in systems. In addition, affected organizations often work with cybersecurity experts to develop a comprehensive incident response plan to handle future threats.
Role of Cybersecurity Awareness Training
Cybersecurity awareness training plays a crucial role in preventing future attacks. Educating employees and users about common threats and potential attack vectors can empower them to identify and report suspicious activities. Training should focus on recognizing phishing attempts, avoiding unsafe downloads, and maintaining strong passwords. This proactive approach fosters a culture of security awareness within the organization, creating a robust defense against potential threats.
Successful Vulnerability Mitigation Strategies
Successful vulnerability mitigation strategies often involve a combination of proactive and reactive measures. Proactive strategies focus on preventing attacks by implementing strong security protocols, regularly updating software and firmware, and conducting regular security assessments. Reactive strategies, on the other hand, involve responding to attacks quickly and effectively, isolating compromised systems, and implementing measures to prevent future attacks. A comprehensive strategy encompassing both approaches is essential for mitigating IoT vulnerabilities.
Severity of Past IoT Attacks
| Attack Name | Affected Devices (Estimated) | Impact (Summary) | Severity (Low/Medium/High) |
|---|---|---|---|
| Mirai Botnet | Millions | Massive DDoS attacks, disrupting online services | High |
| IoT malware campaign | Thousands | Data theft, system compromise | High |
| Smart thermostat compromise | Hundreds of thousands | Unauthorized access to user data | Medium |
| Smart home device hacking | Tens of thousands | Remote control of devices, privacy breaches | High |
Future Implications and Predictions
The Kalay platform vulnerability serves as a stark reminder of the escalating threat landscape surrounding Internet of Things (IoT) devices. The potential for widespread disruption and malicious exploitation extends far beyond immediate consequences. Understanding the future implications is crucial for mitigating risk and developing robust security strategies.
Long-Term Effects of the Vulnerability
The long-term effects of the Kalay vulnerability are multifaceted and potentially devastating. Compromised IoT devices can be leveraged for distributed denial-of-service (DDoS) attacks, enabling attackers to overwhelm critical infrastructure and services. Further, the vulnerability may facilitate data breaches, potentially exposing sensitive personal and financial information. This compromised data could be used for identity theft, financial fraud, or other malicious activities.
Furthermore, compromised devices could be incorporated into botnets, used for illicit activities like spamming or cryptocurrency mining.
Evolution of IoT Vulnerabilities
The nature of IoT vulnerabilities is constantly evolving, mirroring the rapid advancements in technology. As IoT devices become more sophisticated and interconnected, the attack surface expands. New vulnerabilities emerge, and existing vulnerabilities are exploited in novel ways. The sophistication of attackers also increases, leading to more targeted and complex attacks. This necessitates continuous adaptation of security measures and a proactive approach to vulnerability management.
A critical example is the rise of sophisticated malware specifically designed to target IoT devices, potentially disrupting critical infrastructure.
The Kalay platform vulnerability is a serious concern, exposing millions of IoT devices to potential cyberattacks. Fortunately, the Department of Justice Offers Safe Harbor for MA Transactions, a policy designed to protect transactions in Massachusetts , highlights a proactive approach to security, which could potentially help mitigate some of the risks involved in this massive IoT vulnerability.
This vulnerability still demands immediate attention and robust security measures across the board, to protect these vulnerable devices.
Importance of Proactive Security Measures
Proactive security measures are paramount to mitigating the long-term effects of IoT vulnerabilities. This includes rigorous security assessments of all IoT devices, particularly those used in critical infrastructure, alongside the implementation of robust security protocols. Early detection and rapid response mechanisms are essential for containing breaches and minimizing the impact of attacks. Developing and enforcing industry standards for IoT security is also critical.
Need for Enhanced Security Protocols
Enhanced security protocols are crucial for safeguarding IoT devices and preventing malicious exploitation. This includes implementing strong authentication mechanisms, encryption protocols, and secure communication channels. The use of multi-factor authentication, for instance, can significantly enhance the security of IoT devices, making them harder targets for attackers. Implementing regular security audits and penetration testing can identify and address vulnerabilities before they are exploited.
Ongoing Need for Continuous Security Updates
The ongoing need for continuous security updates is vital to maintaining the security of IoT devices. Vulnerabilities are constantly being discovered and patched. Failing to apply these updates leaves devices susceptible to exploitation. A proactive approach to security updates and a strong security patching process are essential. This includes automated update mechanisms and clear communication to users about the importance of applying security updates.
Potential for Widespread Disruption
“The vulnerability of IoT devices could potentially lead to widespread disruption across critical infrastructure, from power grids to transportation systems, creating significant economic and social ramifications.”
This potential for widespread disruption underscores the importance of proactive security measures. Failing to address these vulnerabilities could have devastating consequences, affecting millions and impacting the global economy. Real-world examples of large-scale disruptions highlight the potential for damage, emphasizing the need for robust security measures and ongoing vigilance.
Concluding Remarks

In conclusion, the Kalay platform vulnerability highlights the urgent need for enhanced security protocols and proactive measures within the IoT sector. Understanding the nature of the vulnerability, its potential impact on various sectors, and the available mitigation strategies are crucial to safeguarding our increasingly interconnected world. The future of IoT security depends on collective vigilance and a commitment to continuous improvement.
FAQ Summary: Kalay Platform Vulnerability Exposes Millions Of Iot Devices To Cyber Attacks
What specific types of IoT devices are most vulnerable?
The vulnerability affects a wide range of devices, including smart home appliances, industrial control systems, and medical devices. The exact models affected are still being identified, but this comprehensive nature of the attack underscores the need for proactive security measures across the board.
What are the potential consequences of a successful attack?
Consequences can range from data breaches and privacy violations to physical damage and disruption of critical services. The severity of the impact depends on the targeted device and the attacker’s intent.
How can I protect my IoT devices from this vulnerability?
Update your devices to the latest firmware whenever possible, use strong passwords, and enable multi-factor authentication wherever available. Consider a firewall and network security measures to limit access to your devices.
Are there any resources available to help identify vulnerable devices?
Stay tuned to official security advisories from the Kalay platform and other reputable sources. Online forums and communities may also offer useful information as the situation evolves.