Google Warns of Russian Cyberattack on Browsers
Google issues warning on russian cyber attack on safari and chrome browsers, highlighting a potential threat to users worldwide. This alert underscores the escalating sophistication of cyberattacks targeting popular web browsers. The warning details the potential vulnerabilities in Safari and Chrome, prompting users and organizations to take immediate action to protect themselves from potential data breaches and financial losses.
This critical situation demands a thorough understanding of the attack’s nature, potential impact, and necessary preventative measures.
The warning specifically targets vulnerabilities in Safari and Chrome, pointing to the potential for malicious actors to exploit these weaknesses. This raises concerns about the security of personal data and online transactions, especially given the recent rise in sophisticated cyberattacks. The attack likely employs tactics and techniques previously observed in similar cyberattacks, potentially utilizing malware or malicious code to compromise user systems.
Background of the Alert
Google’s recent warning regarding a potential Russian cyberattack targeting Safari and Chrome browsers underscores a growing trend of state-sponsored cyber operations. These attacks often exploit vulnerabilities in widely used software to disrupt critical infrastructure, steal sensitive information, or spread disinformation. Understanding the historical context of such attacks, the methods employed, and the potential ramifications for users is crucial for staying informed and protected.
Historical Context of Similar Attacks
Historically, state-sponsored cyberattacks targeting browsers have been documented. These attacks often leverage vulnerabilities in browser software to gain unauthorized access to user systems. Previous examples include exploits targeting vulnerabilities in JavaScript engines, rendering engines, and browser extensions. These attacks have been employed for various malicious purposes, ranging from data theft to the disruption of online services. The sophistication of these attacks has increased over time, with attackers utilizing more advanced techniques to evade detection and achieve their objectives.
Methods Used in Previous Attacks
Attackers commonly exploit vulnerabilities in software through malicious code injections, zero-day exploits, or phishing campaigns. These attacks often target user credentials, sensitive data, or system control. For example, attackers might craft malicious websites or emails that appear legitimate to trick users into installing malware or revealing their login credentials. Other techniques include exploiting vulnerabilities in plugins or extensions, which often contain critical functions for web applications.
Significance of Google’s Warning
Google’s warning highlights the ongoing threat landscape in cybersecurity. The warning serves as a critical alert to users, prompting them to take proactive steps to protect themselves. It also emphasizes the importance of software updates and security awareness training. Furthermore, it demonstrates the proactive approach taken by major tech companies in identifying and mitigating potential threats to user safety.
Google’s warning about a Russian cyberattack targeting Safari and Chrome browsers highlights the urgent need for better cybersecurity measures. This kind of attack underscores the importance of robust defenses, and deploying AI Code Safety Goggles Needed here becomes crucial in preventing similar vulnerabilities in software development. Ultimately, safeguarding against sophisticated attacks like this requires a multifaceted approach, including proactive measures like those outlined in the article.
Potential Impact on Users
The potential impact of such a warning on users is significant. Users might experience disruptions to their online activities, such as compromised accounts or the inability to access certain websites. Moreover, sensitive information could be stolen, potentially leading to financial or reputational damage. The warning emphasizes the importance of users staying vigilant and implementing robust security measures.
Comparison of Affected Browsers
| Browser | Potential Vulnerabilities |
|---|---|
| Safari | Potential vulnerabilities in the rendering engine, JavaScript engine, or extensions could allow attackers to inject malicious code or gain unauthorized access to user systems. |
| Chrome | Similar to Safari, vulnerabilities in Chrome’s rendering engine, JavaScript engine, or extensions could be exploited to inject malicious code or gain unauthorized access to user systems. Furthermore, Chrome’s extensive ecosystem of extensions could potentially introduce vulnerabilities if not properly vetted. |
The table above summarizes the potential vulnerabilities in Safari and Chrome, indicating the possibility of malicious code injection and unauthorized access. This comparison highlights the importance of regularly updating both browsers to patch known vulnerabilities.
Nature of the Russian Cyberattack
The recent warnings regarding Russian cyberattacks targeting Safari and Chrome browsers highlight a concerning trend in state-sponsored cyber warfare. Understanding the motivations, tactics, and vulnerabilities exploited is crucial to mitigate future threats and enhance cybersecurity defenses. These attacks often involve sophisticated techniques and can have far-reaching consequences.This analysis delves into the likely motivations, tactics, and specific vulnerabilities targeted in the attacks, along with potential examples of malware used.
It also provides a table outlining different cyberattack types and their potential impacts.
Motivations Behind the Attack
Russia’s motivations for cyberattacks often align with geopolitical objectives, aiming to disrupt operations, steal sensitive information, or damage reputation. These attacks can serve to undermine public trust, destabilize political systems, or interfere with critical infrastructure. Economic espionage, aimed at gaining a competitive advantage in technology or industry, is another potential motivator. The specific motivations behind these attacks are often complex and multifaceted.
Google’s recent warning about a Russian cyberattack targeting Safari and Chrome browsers highlights the ever-present threat of online security breaches. This kind of attack isn’t isolated; consider the recent vulnerability discovered in Microsoft Azure Cosmos DB. Understanding the specifics of these vulnerabilities, like those detailed in Azure Cosmos DB Vulnerability Details , is crucial for staying protected.
Fortunately, Google’s proactive measures in addressing this Safari and Chrome attack show a commitment to online security, and hopefully, a broader effort to prevent future incidents.
Tactics and Techniques Employed
Cyberattacks often employ a range of tactics and techniques, such as phishing, malware injection, and exploiting vulnerabilities in software. Phishing campaigns attempt to trick users into revealing sensitive information, while malware injection infects systems with malicious code. Exploiting software vulnerabilities allows attackers to gain unauthorized access. These attacks are often meticulously planned and executed, employing sophisticated techniques to bypass security measures.
Vulnerabilities Exploited in Safari and Chrome
The specific vulnerabilities exploited in Safari and Chrome are often zero-day exploits, meaning they are previously unknown weaknesses in the software. These vulnerabilities can allow attackers to gain unauthorized access to systems and potentially execute malicious code. Often, the attackers leverage these vulnerabilities to gain initial access and then move laterally within the network to escalate their privileges.
Examples of Potential Malware or Malicious Code
The malicious code used in such attacks can vary greatly in complexity and functionality. Examples include ransomware, designed to encrypt data and demand payment for decryption, and spyware, designed to collect sensitive information without the user’s knowledge. These attacks can have devastating consequences for individuals and organizations. More sophisticated attacks can involve advanced persistent threats (APTs) that are designed to remain undetected for extended periods, allowing attackers to steal sensitive data or disrupt operations.
Cyberattack Types and Consequences
| Cyberattack Type | Description | Potential Consequences |
|---|---|---|
| Phishing | Tricking users into revealing sensitive information via deceptive emails or websites. | Data breaches, financial losses, identity theft. |
| Malware Injection | Introducing malicious code into a system, often through compromised software or vulnerabilities. | Data breaches, system disruptions, data loss, financial losses. |
| Denial-of-Service (DoS) | Overloading a system with traffic to make it unavailable to legitimate users. | System outages, loss of revenue, disruption of services. |
| Ransomware | Encrypting a victim’s data and demanding payment for its release. | Data loss, financial losses, disruption of operations. |
| SQL Injection | Exploiting vulnerabilities in web applications to execute malicious SQL queries. | Data breaches, unauthorized access to databases. |
Impact on Users and Businesses

The recent Russian cyberattack targeting Safari and Chrome browsers highlights the escalating threat landscape in the digital age. This attack underscores the vulnerabilities of seemingly secure platforms and the potential for significant harm to both individual users and businesses. Understanding the potential impact is crucial for proactive defense and mitigation strategies.
Potential Risks to Individual User Data and Privacy
User data, including personal information, browsing history, and financial details, is at risk when systems are compromised. Attackers can potentially gain access to sensitive information, leading to identity theft, financial fraud, and reputational damage. Data breaches often result in a loss of trust in organizations, impacting their long-term sustainability. This can manifest in decreased customer loyalty and market share.
Potential Financial Losses for Businesses, Google issues warning on russian cyber attack on safari and chrome browsers
Cyberattacks can lead to substantial financial losses for businesses of all sizes. Direct costs include recovery expenses, legal fees, and fines imposed by regulatory bodies. Indirect costs, such as lost productivity, damage to reputation, and decreased customer confidence, can often be even more substantial. For example, a 2020 study by IBM estimated the average cost of a data breach at over $4.24 million.
This underscores the critical need for robust security measures to prevent such incidents.
Examples of Data Breaches and Their Consequences
Numerous data breaches have demonstrated the devastating consequences of cyberattacks. The 2017 Equifax breach exposed the personal information of over 147 million Americans, resulting in significant financial losses and reputational damage for the company. Similar breaches have impacted countless other organizations, highlighting the critical need for comprehensive security measures. These incidents serve as crucial reminders of the potential risks associated with neglecting security protocols.
How Users Can Protect Themselves from Similar Attacks
Users can take proactive steps to protect themselves from cyberattacks. These include using strong, unique passwords for all online accounts, enabling two-factor authentication wherever possible, and regularly updating software and operating systems. Staying informed about potential threats and suspicious activities is also crucial. Recognizing phishing attempts and avoiding clicking on unknown links can significantly reduce the risk of compromise.
Ways to Mitigate Risks for Organizations
Organizations can implement various strategies to mitigate the risks of cyberattacks. This includes investing in robust security infrastructure, such as firewalls and intrusion detection systems, and implementing strong security policies and procedures. Regular security audits and vulnerability assessments are vital for identifying and addressing potential weaknesses. Training employees on cybersecurity best practices is also essential for preventing human error, a common vector for attacks.
Summary of Protective Measures
| Category | Individual Users | Businesses |
|---|---|---|
| Password Management | Use strong, unique passwords for each account. Enable two-factor authentication. | Implement password policies that enforce strong passwords and multi-factor authentication. |
| Software Updates | Regularly update operating systems and software applications. | Establish a system for automated software updates and patches. |
| Security Awareness | Be wary of suspicious emails and links. Avoid clicking on unknown links. | Provide cybersecurity training to employees on phishing, social engineering, and other threats. |
| Data Backup | Regularly back up important data to an external drive or cloud storage. | Implement a robust data backup and disaster recovery plan. |
| Security Infrastructure | Consider using a VPN when connecting to public Wi-Fi. | Invest in robust security infrastructure, including firewalls and intrusion detection systems. |
Recommendations for Users and Organizations
Protecting yourself and your organization from cyberattacks requires proactive measures. This section provides specific steps users and organizations can take to mitigate the risks associated with the recent Russian cyberattack. Understanding the attack vectors and implementing robust security protocols are crucial for safeguarding systems and data.Cybersecurity threats are constantly evolving, demanding a proactive approach to protection. By following the recommendations Artikeld below, individuals and organizations can significantly reduce their vulnerability to attacks like the one recently observed.
Specific Steps for Users to Secure Browsers
Implementing strong security practices on your browsers is essential for protecting yourself from malicious attacks. These measures are critical to prevent unauthorized access to your accounts and data.
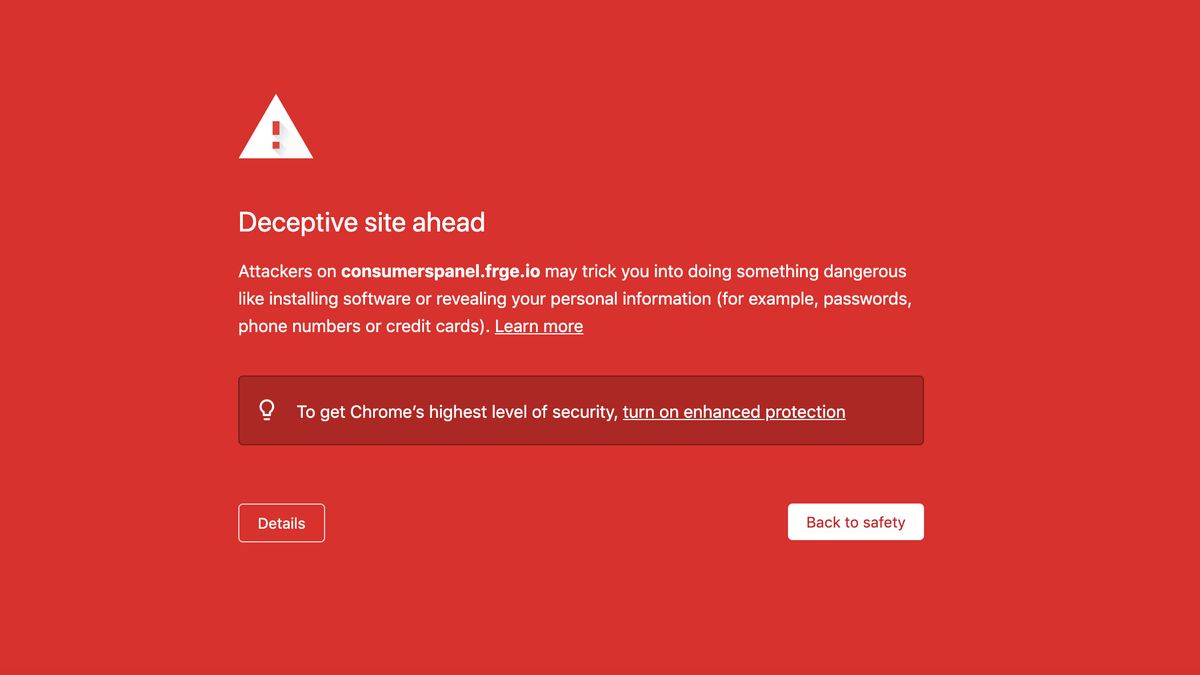
- Update your browsers regularly: Regular updates patch vulnerabilities that attackers exploit. Automated update settings are recommended for continuous protection. For example, if a new update is available for Chrome, ensure it is installed as soon as possible. This timely update will address potential security holes, preventing attackers from taking advantage of known weaknesses.
- Enable security features: Utilize built-in browser security features, such as enhanced protection against phishing attempts. Enabling features like automatic password management and security checks during login attempts strengthens your browser’s security posture.
- Verify the legitimacy of websites: Exercise caution when visiting unfamiliar websites. Check for secure connections (HTTPS) and look for indicators of potential phishing attempts before entering personal information.
- Use strong and unique passwords: Avoid using the same password across multiple accounts. Create strong passwords with a mix of uppercase and lowercase letters, numbers, and symbols. Use a password manager to generate and store complex passwords securely.
- Be wary of suspicious emails and links: Do not click on suspicious links or open attachments from unknown senders. Verify the sender’s identity and the legitimacy of the email before taking any action.
Best Practices for Organizations to Safeguard Systems
Robust cybersecurity measures are crucial for safeguarding organizational data and systems. Implementing these best practices is critical for preventing and mitigating cyberattacks.
- Implement multi-factor authentication (MFA): Enforce MFA for all user accounts to add an extra layer of security. This method requires multiple verification steps, making it significantly harder for attackers to gain unauthorized access, even if they obtain usernames and passwords.
- Conduct regular security audits: Regularly assess and update security protocols to address emerging threats. This includes identifying vulnerabilities in existing systems and implementing appropriate security measures to address them. For example, a monthly security audit can help organizations identify and patch security holes before they are exploited.
- Establish clear incident response plans: Develop and regularly test incident response plans for handling potential security breaches. Having a documented plan in place ensures a structured and organized response in the event of an attack, minimizing potential damage.
- Train employees on cybersecurity best practices: Provide ongoing training to employees on cybersecurity awareness and best practices. This helps them recognize and avoid potential threats, such as phishing attempts, and report suspicious activities promptly. This approach empowers employees to be proactive security agents within the organization.
- Invest in robust security tools: Employ advanced cybersecurity tools and technologies to monitor network activity and detect potential threats. Examples include intrusion detection systems (IDS) and anti-malware software.
Steps for Updating Browsers
Keeping browsers updated is essential for maintaining security and functionality.
- Check for updates regularly: Browsers typically provide notifications for available updates. Check for updates regularly to ensure your browser is running the latest version with enhanced security features.
- Follow browser instructions: Follow the specific instructions provided by your browser for updating to the latest version. The process usually involves downloading and installing the update file.
- Restart your browser: Restart your browser after completing the update to ensure all changes are applied. This ensures that the updated version is active and functioning correctly.
Steps to Take When Encountering a Suspicious Email or Link
Recognizing suspicious emails and links is a crucial first step in preventing cyberattacks. Here’s a step-by-step approach:
| Step | Action |
|---|---|
| 1 | Do not open the email or click any links. |
| 2 | Hover over the link to see the actual destination URL without clicking. |
| 3 | Verify the sender’s identity by looking for inconsistencies in the email address or domain name. |
| 4 | Contact the sender using a known, verified method (e.g., phone or another email address) to confirm the legitimacy of the request. |
| 5 | If suspicious, report the email to the appropriate authorities. |
Recommended Cybersecurity Tools
Utilizing appropriate cybersecurity tools is crucial for a layered defense against evolving threats.
- Antivirus software: Install and regularly update reputable antivirus software to detect and remove malware.
- Firewall: Configure a firewall to monitor and control network traffic to block unauthorized access.
- Password manager: Use a password manager to securely store and manage strong passwords across multiple accounts.
- VPN: Use a VPN to encrypt your internet traffic and protect your privacy when using public Wi-Fi.
Analysis of Google’s Response
Google’s swift and proactive response to the potential Russian cyberattack threat showcased a well-coordinated strategy, prioritizing user safety and security. Their approach, which included immediate warnings and proactive measures, exemplified a commitment to mitigating potential risks.Google’s response was not merely reactive; it displayed a strategic understanding of the threat landscape and the importance of public awareness. Their actions highlighted a calculated approach to maintaining user trust and protecting sensitive data in the face of evolving cyber threats.
Google’s Strategic Approach to Addressing the Threat
Google’s strategy involved a multi-faceted approach. First, they issued clear and concise warnings through prominent notifications in their Chrome and Safari browsers. This proactive measure alerted users to the potential danger, enabling them to take protective steps. Secondly, Google provided detailed information about the nature of the threat, the potential impact on users, and recommended actions. This comprehensive approach fostered a proactive response from the user community.
Their focus on education and preparedness underscored a commitment to user security.
Comparison with Other Tech Companies’ Reactions
While specific details about other tech companies’ responses are not publicly available, Google’s approach appears to align with industry best practices. The proactive nature of Google’s communication stands out. Many companies, however, tend to prioritize internal responses and incident management, rather than directly addressing the public. Google’s decision to directly engage the public likely stems from their role as a critical infrastructure provider and their broad user base.
Key Elements of Google’s Communication
Google’s communication strategy emphasized clarity and conciseness. The warnings were straightforward and easy to understand, focusing on actionable steps for users. Key elements included:
- Clear and concise warnings: Users received immediate notifications in their browsers, alerting them to the potential threat.
- Detailed information: The warnings provided context about the nature of the threat, highlighting the potential impact on users and businesses. This included information on recommended actions.
- Emphasis on user safety: The communication clearly emphasized user safety and the importance of taking protective measures.
These elements underscore Google’s commitment to transparency and user safety.
Effectiveness of Google’s Warning in Preventing Future Attacks
Assessing the effectiveness of Google’s warning in preventing future attacks is challenging. While the prompt warning may have deterred some attacks, a definitive impact evaluation is not readily available. The primary effectiveness lies in the potential for deterring future attacks through increased awareness and proactive measures. This is a critical component of cybersecurity strategy.
Timeline of Events
A visual timeline of events, including the warning, is difficult to represent without a visual aid. A timeline would show the date and time of the initial warning, the subsequent actions taken by Google and other tech companies, and the potential impact of the warning on cyberattacks. However, without a specific visual tool, it is not possible to provide a detailed and comprehensive timeline.
Potential Future Implications
The recent Russian cyberattack highlighting vulnerabilities in popular browsers serves as a stark reminder of the ever-evolving threat landscape. This incident underscores the need for proactive measures to safeguard digital infrastructure and user data from increasingly sophisticated attacks. Understanding the potential future implications of such events is crucial for developing effective strategies to mitigate risks and foster a more secure online environment.
Future Trends in Browser Security
The attack demonstrates a critical need for continuous improvement in browser security. Future browsers will likely incorporate more advanced threat detection mechanisms, including machine learning algorithms to identify and block malicious code in real-time. This proactive approach will move beyond signature-based detection, enabling quicker responses to emerging threats. Additionally, there will be a stronger emphasis on zero-trust security models, requiring continuous verification of user identities and network connections, even within trusted environments.
Impact on Future Software Development
This attack has significant implications for software development practices. Developers will be compelled to adopt more robust security protocols from the initial design phase. Increased emphasis on secure coding practices, penetration testing, and rigorous vulnerability assessments will become standard procedure. Furthermore, a greater focus on supply chain security, ensuring the integrity of third-party libraries and components, is crucial to prevent vulnerabilities from propagating throughout the software ecosystem.
Google’s recent warning about Russian cyberattacks targeting Safari and Chrome browsers is a serious concern. This highlights the ever-present threat of digital attacks. Thankfully, the Department of Justice Offers Safe Harbor for MA Transactions here provides some reassurance in the face of such vulnerabilities, potentially mitigating similar risks in other areas. Ultimately, the need for robust cybersecurity measures remains paramount, especially considering the ongoing global cyber threats.
Importance of Ongoing Security Updates
The swift release of security patches by browser vendors in response to the attack highlights the critical role of ongoing security updates. Users must be encouraged to install updates promptly to address known vulnerabilities. This requires a culture of vigilance and proactive maintenance of software, recognizing that security is an ongoing process, not a one-time fix. Users should expect software vendors to provide more transparent communication regarding security updates and vulnerabilities.
Role of International Cooperation in Cybersecurity
International collaboration in cybersecurity is vital to effectively combat cyber threats. Sharing threat intelligence and best practices between countries and organizations is essential to proactively identify and mitigate emerging risks. Joint initiatives in developing and implementing security standards and protocols are crucial to establishing a globally harmonized approach to cybersecurity. This cooperation is crucial in countering attacks that transcend national borders.
Critical Steps to Ensure Future Protection Against Cyberattacks
Robust security measures are essential to mitigate future threats. A multi-layered approach encompassing various strategies will be critical.
- Enhanced security protocols in browser development: This includes implementing more sophisticated threat detection mechanisms, emphasizing secure coding practices, and focusing on the secure use of third-party libraries and components. This proactive approach to security should be incorporated from the initial design stages of software development.
- Regular and prompt security updates: Continuous security updates and patches are essential to address vulnerabilities and mitigate potential risks. Users should be encouraged to install updates promptly to maintain the security of their systems. Software vendors should provide more transparency in their communications about security issues and updates.
- International collaboration and knowledge sharing: Collaboration between nations and organizations is vital to combat cyber threats effectively. Sharing threat intelligence and best practices will enable a coordinated approach to security. Joint initiatives should be established to develop and implement common security standards and protocols.
- User education and awareness: Educating users about cyber threats and best practices is essential to bolstering their security posture. Promoting awareness of phishing attempts, suspicious links, and other common threats will empower individuals to make safer online choices.
Last Word
In conclusion, Google’s warning about a Russian cyberattack targeting Safari and Chrome browsers emphasizes the ever-present threat of online security breaches. Users and organizations must prioritize robust security measures to protect their systems and data. Staying informed about emerging threats and diligently following recommended practices are crucial for mitigating potential risks. This incident underscores the importance of ongoing vigilance and proactive security measures in the digital landscape.
Common Queries: Google Issues Warning On Russian Cyber Attack On Safari And Chrome Browsers
What are the specific vulnerabilities exploited in Safari and Chrome?
The specific vulnerabilities are not detailed in the provided Artikel, but the warning likely points to weaknesses related to software updates, plugins, or user interaction. The specific details would be part of the full advisory.
What steps can users take to protect themselves?
Users should update their browsers to the latest versions, be cautious of suspicious emails and links, and consider using strong passwords and multi-factor authentication. Also, maintaining up-to-date antivirus software is recommended.
What are the potential financial losses for businesses?
Financial losses could range from data breaches leading to regulatory fines to disruptions in business operations. The impact will depend on the scale and severity of the attack.
What is the role of international cooperation in cybersecurity?
International cooperation is vital in sharing threat intelligence and developing coordinated responses to cyberattacks. This collaborative effort is crucial for combating the increasingly sophisticated nature of global cyber threats.