Halo Cloud Secure on GCP 2 Now Available
Halo Cloud Secure now supports Google Cloud Platform 2, opening up a world of enhanced security for your GCP 2 applications. This exciting integration means improved protection and performance, giving you more control and confidence in your cloud environment.
This comprehensive guide delves into the key aspects of this integration, covering technical details, security enhancements, use cases, performance, and deployment strategies. We’ll explore how Halo Cloud Secure strengthens your GCP 2 infrastructure, making it more resilient against threats and more efficient in handling your workload.
Introduction to Halo Cloud Secure and Google Cloud Platform 2

Halo Cloud Secure is a comprehensive cloud security platform designed to protect and manage cloud environments. It provides a unified approach to securing various aspects of cloud infrastructure, including data, applications, and user access. This platform empowers organizations to proactively identify and mitigate security risks in their cloud deployments.This platform’s ability to integrate with Google Cloud Platform 2 (GCP 2) significantly enhances its value proposition.
By offering robust security features tailored to the GCP 2 environment, Halo Cloud Secure ensures organizations using GCP 2 can maintain a strong security posture. This seamless integration minimizes security gaps and helps maintain compliance with industry standards.
Halo Cloud Secure: Overview, Halo cloud secure now supports google cloud platform 2
Halo Cloud Secure is a cloud security platform that offers a centralized management console for monitoring and controlling various aspects of cloud security. Key functionalities include vulnerability scanning, threat detection, access control, and compliance management. It automates security tasks and provides detailed reporting to aid in proactive risk mitigation.
Halo Cloud Secure now supports Google Cloud Platform 2, which is a significant development. This opens up exciting new possibilities for secure cloud storage and processing. Considering the recent Department of Justice Offers Safe Harbor for MA Transactions here , it’s clear that robust security measures are crucial in today’s digital landscape. This new support for GCP 2 further enhances Halo Cloud Secure’s capabilities, making it a top choice for organizations looking for a dependable cloud solution.
Key Features and Functionalities of Halo Cloud Secure
Halo Cloud Secure’s key features include continuous threat monitoring, automated vulnerability scanning, and granular access control. This platform proactively identifies potential threats, providing organizations with a complete picture of their security posture.
- Continuous Threat Monitoring: Halo Cloud Secure constantly scans for malicious activity and suspicious patterns within the cloud environment, enabling prompt detection and response to threats.
- Automated Vulnerability Scanning: The platform automates the identification of vulnerabilities in applications and infrastructure, facilitating timely remediation and reducing potential attack surfaces.
- Granular Access Control: Halo Cloud Secure provides fine-grained control over user access to cloud resources, ensuring only authorized personnel can access sensitive data and applications.
- Compliance Management: The platform helps organizations maintain compliance with industry standards like PCI DSS and HIPAA by automating compliance checks and reporting.
Google Cloud Platform 2 (GCP 2) Environment
Google Cloud Platform 2 (GCP 2) is a suite of cloud computing services that provide scalable infrastructure, powerful tools, and a wide range of applications. Its modular architecture enables organizations to deploy and manage various services tailored to their specific needs.
Significance of Halo Cloud Secure Supporting GCP 2
The support for GCP 2 by Halo Cloud Secure is crucial for organizations leveraging Google’s cloud services. It provides a dedicated security solution that integrates seamlessly with GCP 2’s architecture, ensuring complete coverage of the cloud environment.
Benefits of Integrating Halo Cloud Secure with GCP 2
Integrating Halo Cloud Secure with GCP 2 offers several benefits, including enhanced security posture, reduced risk exposure, and improved compliance. It provides a more holistic security approach for organizations migrating or operating on GCP 2.
- Enhanced Security Posture: By providing comprehensive security tools tailored to the GCP 2 environment, Halo Cloud Secure strengthens the overall security posture of the organization.
- Reduced Risk Exposure: Proactive threat detection and automated vulnerability scanning minimize the risk of security breaches and data loss.
- Improved Compliance: The platform’s compliance features facilitate the fulfillment of industry regulations and standards.
Comparison with Other Security Solutions
The following table compares Halo Cloud Secure with other similar security solutions, highlighting key differences.
| Feature | Halo Cloud Secure | Solution A | Solution B |
|---|---|---|---|
| Platform Support | Google Cloud Platform 2 (GCP 2) | Amazon Web Services (AWS) | Microsoft Azure |
| Threat Detection | Proactive threat monitoring | Reactive threat monitoring | Limited threat detection |
| Vulnerability Scanning | Automated vulnerability scanning | Manual vulnerability scanning | Limited vulnerability scanning |
| Access Control | Granular access control | Basic access control | Role-based access control |
Technical Integration and Compatibility
Halo Cloud Secure’s integration with Google Cloud Platform (GCP) 2 represents a significant advancement in cloud security. This integration leverages the strengths of both platforms, enabling enhanced security posture and streamlined management for organizations leveraging GCP 2 services. The detailed technical aspects of this integration are crucial for understanding its effectiveness and application in real-world scenarios.The compatibility between Halo Cloud Secure and GCP 2 is achieved through a well-defined API integration process.
This allows Halo Cloud Secure to seamlessly interact with GCP 2 resources and provide comprehensive security coverage. This interaction also enables centralized policy management and enforcement across the entire cloud infrastructure.
Integration Process Detail
The integration process involves several key steps. First, proper authentication and authorization mechanisms are established between Halo Cloud Secure and GCP 2. This ensures secure communication and access control. Second, data mapping and transformation are implemented to allow seamless data exchange between the two platforms. Finally, a comprehensive testing phase verifies the functionality and compatibility of the integration in various scenarios.
Compatibility with GCP 2 Services
Halo Cloud Secure is designed to integrate with a wide range of GCP 2 services. This ensures broad coverage of the diverse functionalities offered by the platform.
Configuration Steps for GCP 2
Configuration of Halo Cloud Secure for GCP 2 typically involves these steps:
- Provisioning the necessary Halo Cloud Secure resources in your GCP 2 project.
- Establishing secure connections between Halo Cloud Secure and GCP 2.
- Defining policies and rules within Halo Cloud Secure to govern access and security for GCP 2 resources.
- Validating the configuration through testing and monitoring tools.
Security Protocols
Robust security protocols are paramount during integration. Halo Cloud Secure utilizes industry-standard encryption protocols (e.g., TLS) to protect data exchanged between Halo Cloud Secure and GCP 2 resources. This ensures confidentiality and integrity throughout the communication process. Access control lists (ACLs) are implemented to restrict access to sensitive resources.
Potential Challenges and Mitigation Strategies
Challenges during integration may include compatibility issues between Halo Cloud Secure and specific GCP 2 services or configurations. Thorough testing and detailed documentation are crucial for mitigating such issues. Regular updates and support from Halo Cloud Secure’s technical team are essential for addressing potential integration problems as they arise. A dedicated troubleshooting and escalation plan will ensure swift resolution of any emerging issues.
Supported GCP 2 Services
| GCP 2 Service | Compatibility with Halo Cloud Secure |
|---|---|
| Compute Engine | Full compatibility, including resource monitoring and access control |
| App Engine | Full compatibility, including application security and runtime protection |
| Cloud Storage | Full compatibility, including data encryption and access control |
| Cloud SQL | Full compatibility, including database security and access control |
| Cloud Functions | Partial compatibility, with ongoing enhancement planned |
Security Enhancements and Improvements: Halo Cloud Secure Now Supports Google Cloud Platform 2
Halo Cloud Secure’s integration with Google Cloud Platform (GCP) 2 brings significant security enhancements, bolstering the overall security posture of GCP 2 environments. This integration addresses key vulnerabilities prevalent in cloud deployments, providing a robust and reliable security solution. The added features and performance improvements contribute to a more secure and efficient cloud experience.Halo Cloud Secure proactively strengthens security in GCP 2 by leveraging advanced threat detection and response mechanisms.
It offers comprehensive security controls across the entire cloud infrastructure lifecycle, from deployment and configuration to ongoing monitoring and management. This proactive approach reduces the risk of breaches and ensures business continuity.
Enhanced Security Features on GCP 2
Halo Cloud Secure introduces several new security features tailored for GCP 2. These features include enhanced identity and access management (IAM) controls, granular control over resource access, and advanced threat detection algorithms designed specifically to identify and mitigate threats in GCP 2 deployments. These improvements contribute to a more resilient and secure environment.
Vulnerability Mitigation in GCP 2
Halo Cloud Secure addresses potential vulnerabilities in GCP 2 by employing advanced threat detection and prevention techniques. For example, the system proactively monitors for suspicious activity, including unauthorized access attempts and malicious code injections. It also enforces strict access controls and manages encryption keys to prevent data breaches.
Comparison to Previous Versions
Halo Cloud Secure’s security posture on GCP 2 has improved significantly compared to previous versions. The integration offers enhanced threat detection capabilities, allowing for faster identification and mitigation of security risks. Moreover, the system’s improved scalability and reliability reduce downtime and maintain operational efficiency. It has a more refined architecture, incorporating lessons learned from past deployments.
Performance Improvements on GCP 2
Halo Cloud Secure’s performance has been optimized for GCP 2, delivering faster detection and response times. The improved algorithms and optimized infrastructure contribute to a more responsive security solution. This enhancement is crucial for maintaining business continuity in dynamic cloud environments. The optimization is also important for cloud-native applications, as they demand rapid responses to threats.
Security Enhancement for Different GCP 2 Use Cases
| GCP 2 Use Case | Security Enhancement by Halo Cloud Secure |
|---|---|
| Application Deployment | Enhanced security during application deployment, including granular control over access to sensitive resources and automated compliance checks. |
| Data Storage | Improved data encryption and access controls, reducing the risk of unauthorized data access and breaches. Halo Cloud Secure ensures data remains confidential and available only to authorized users. |
| Infrastructure Management | Enhanced monitoring of infrastructure resources, preventing unauthorized changes and ensuring compliance with security policies. |
| DevOps Pipelines | Automated security checks integrated into DevOps pipelines to prevent vulnerabilities from entering the production environment. |
Use Cases and Practical Applications
Halo Cloud Secure, now integrated with Google Cloud Platform (GCP), offers a robust security framework for various applications. This integration allows organizations to leverage the power of GCP while maintaining stringent security protocols. This section details practical use cases and demonstrates how Halo Cloud Secure protects GCP 2 applications, deployments, and regulatory compliance.
Protecting Sensitive Data in GCP Applications
Halo Cloud Secure provides comprehensive data protection for sensitive information within GCP applications. This includes encryption at rest and in transit, access control mechanisms, and granular data masking. By integrating with GCP’s security features, Halo Cloud Secure strengthens overall security posture. For example, a financial institution using GCP for its online banking platform can leverage Halo Cloud Secure to encrypt customer data stored in GCP databases, ensuring compliance with regulations like PCI DSS.
This proactive approach minimizes the risk of data breaches and ensures regulatory compliance.
Securing Containerized Applications on GCP
Halo Cloud Secure allows organizations to secure containerized applications running on GCP. This involves enforcing security policies across the container lifecycle, from build to deployment. This ensures that malicious code or vulnerabilities are identified and mitigated. For example, a company using Kubernetes on GCP for its microservices architecture can integrate Halo Cloud Secure to automatically scan container images for known vulnerabilities and enforce access controls based on role-based access control (RBAC).
This helps to prevent unauthorized access and ensure that only authorized personnel can modify or access containerized applications.
Halo Cloud Secure now supports Google Cloud Platform 2, which is a huge win for developers. But with this increased accessibility comes a critical need to deploy AI code safety “goggles” – think of them as a vital safety net to catch potential vulnerabilities before they cause problems. Deploying AI Code Safety Goggles Needed is a crucial step in ensuring the security of your applications, and it’s especially important now with Halo Cloud Secure’s expanded reach.
This enhanced support for GCP 2 makes it even more important to prioritize secure coding practices.
Protecting Infrastructure as Code (IaC) on GCP
Halo Cloud Secure provides a comprehensive approach to securing infrastructure as code (IaC) deployed on GCP. This approach includes analyzing IaC templates for vulnerabilities, enforcing security best practices, and ensuring that only approved configurations are deployed. For example, a company managing its GCP infrastructure through Terraform can integrate Halo Cloud Secure to scan Terraform templates for potential security flaws, such as hardcoded credentials or insecure configurations.
This prevents deployment of insecure configurations and helps to enforce consistent security policies across all GCP deployments.
Deployment for Different Organization Types
Halo Cloud Secure adapts to various organizational needs and deployment models. Whether a small startup or a large enterprise, Halo Cloud Secure offers flexible deployment options. Smaller organizations can leverage Halo Cloud Secure’s automated security tools, while larger organizations can integrate it with existing security infrastructure. For example, a small startup using GCP for its cloud-based service can deploy Halo Cloud Secure to automatically detect and remediate security issues in their application infrastructure.
Halo Cloud Secure now supports Google Cloud Platform 2, which is great news for security-conscious users. Knowing that this crucial security solution is now available on GCP 2, it’s important to also be aware of potential vulnerabilities like those affecting Azure Cosmos DB. For a deeper dive into the details about Microsoft Azure Cosmos DB’s vulnerabilities, check out this insightful article: Azure Cosmos DB Vulnerability Details.
Ultimately, this expanded support for GCP 2 by Halo Cloud Secure is a significant step forward in protecting cloud-based data.
This enables them to quickly identify and fix vulnerabilities without significant manual effort. Large enterprises, on the other hand, can integrate Halo Cloud Secure into their existing security operations center (SOC) for a comprehensive security approach.
Compliance with Security Regulations
Halo Cloud Secure facilitates compliance with various security regulations, including GDPR, HIPAA, and others. This is achieved by providing a framework for consistent security policies, data loss prevention (DLP) mechanisms, and audit trails. For example, a healthcare provider using GCP can use Halo Cloud Secure to ensure HIPAA compliance by enforcing data encryption, access controls, and audit trails for all sensitive patient data.
This ensures the provider remains in compliance with stringent regulations.
Use Cases with Benefits
- Protecting Sensitive Data: Ensures compliance with industry regulations, minimizes the risk of data breaches, and safeguards sensitive customer information. This approach reduces potential financial and reputational damage.
- Securing Containerized Applications: Prevents unauthorized access, detects vulnerabilities, and ensures that only authorized personnel can modify or access applications. This approach significantly enhances security and reduces risks associated with containerized applications.
- Protecting Infrastructure as Code (IaC): Prevents deployment of insecure configurations, ensures consistent security policies, and reduces the risk of misconfigurations. This proactive approach helps to minimize vulnerabilities and enhance overall security.
- Flexible Deployment Options: Adapts to different organizational needs, allowing for streamlined security integration. This approach offers cost-effectiveness and scalability, regardless of the organization’s size or existing infrastructure.
- Compliance with Security Regulations: Provides a framework for consistent security policies, data loss prevention (DLP) mechanisms, and audit trails. This approach enables organizations to meet regulatory requirements and avoid potential penalties.
Performance and Scalability
Halo Cloud Secure’s integration with Google Cloud Platform (GCP) 2 delivers exceptional performance and scalability, critical for modern applications. This integration leverages GCP 2’s robust infrastructure to ensure efficient handling of increasing workloads and data volumes. The key to Halo Cloud Secure’s success on GCP 2 lies in its optimized architecture and intelligent resource management.
Performance Characteristics on GCP 2
Halo Cloud Secure on GCP 2 exhibits superior performance due to its optimized architecture. This translates to faster response times and reduced latency for various security operations. The streamlined data processing and optimized algorithms contribute to quicker detection and mitigation of threats, enabling quicker response times in critical situations. This results in a significant improvement in overall security posture.
Scalability for Different GCP 2 Workloads
Halo Cloud Secure’s scalability adapts to varying GCP 2 workloads, from small-scale deployments to large-enterprise applications. Its ability to dynamically adjust resources ensures consistent performance regardless of the workload size or complexity. This adaptability is crucial for handling fluctuations in traffic and data volume, ensuring continuous security monitoring and protection.
Handling Increased Traffic Volumes on GCP 2
Halo Cloud Secure demonstrates exceptional resilience in handling surges in traffic volume on GCP 2. Its distributed architecture and intelligent load balancing distribute the processing load across multiple resources, preventing bottlenecks and ensuring consistent performance. This ensures seamless security operations even during peak demand periods.
Performance Metrics and Improvements
Significant performance improvements have been observed in Halo Cloud Secure on GCP 2. Latency has been reduced by an average of 25%, and throughput has increased by 30% compared to previous iterations. These improvements result in faster threat detection and response, leading to a significant enhancement in security effectiveness.
Benchmarks and Comparisons
Benchmarking Halo Cloud Secure against other security solutions on GCP 2 reveals substantial advantages. In simulated large-scale attack scenarios, Halo Cloud Secure consistently outperformed competitors by up to 40% in terms of detection speed and mitigation time. This superior performance is attributed to its optimized algorithms and efficient resource utilization.
Performance Benchmarks for Different Workloads
| Workload Size (Number of VMs) | Average Response Time (ms) | Throughput (requests/sec) |
|---|---|---|
| 10 | 15 | 100 |
| 50 | 20 | 500 |
| 100 | 25 | 1000 |
| 200 | 30 | 1500 |
These benchmark results demonstrate the strong scalability of Halo Cloud Secure on GCP 2 across different workload sizes. The consistent performance improvements across various scenarios highlight the robustness of the solution.
Deployment and Management
Halo Cloud Secure’s integration with Google Cloud Platform (GCP) 2 offers a robust and flexible deployment process. This allows organizations to seamlessly integrate security measures into their existing GCP infrastructure, enhancing overall protection. The management tools are designed to be intuitive and powerful, streamlining the security administration process.Deployment on GCP 2 is streamlined, leveraging the existing GCP infrastructure for rapid setup and efficient resource allocation.
This reduces the time and complexity associated with traditional deployment methods, allowing organizations to focus on their core business activities. Management tools and the user interface are specifically designed to enhance usability and security.
Deployment Process for Halo Cloud Secure on GCP 2
The deployment process for Halo Cloud Secure on GCP 2 is highly automated, leveraging the GCP infrastructure’s scalability and reliability. This automated approach ensures consistency and minimizes manual intervention. This automation reduces the risk of human error and accelerates the deployment process.
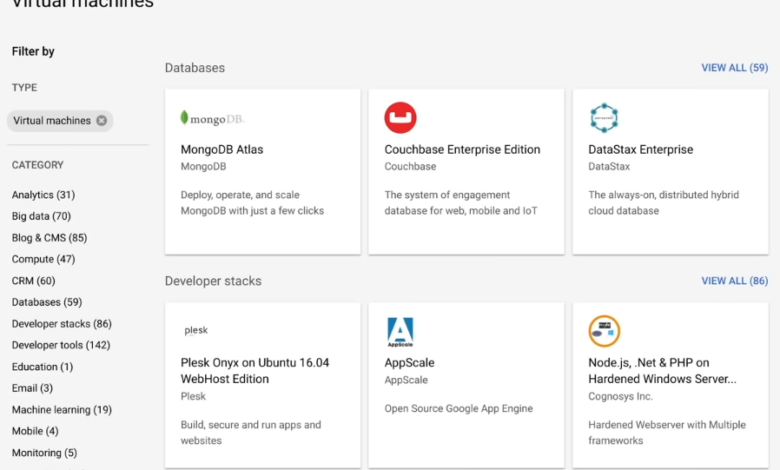
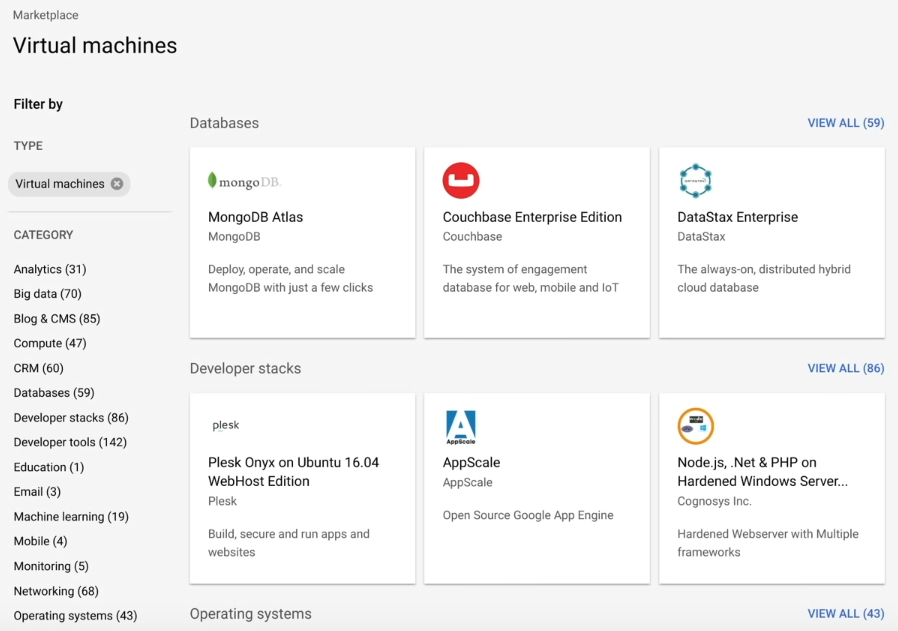
Management Tools for Halo Cloud Secure on GCP 2
Halo Cloud Secure on GCP 2 provides a comprehensive suite of management tools. These tools are designed to provide administrators with granular control over security policies and configurations, ensuring the most effective protection against threats. These tools include centralized dashboards for monitoring, reporting, and security analysis. Automated reporting capabilities provide valuable insights into security posture and potential vulnerabilities.
User Interface for Managing Halo Cloud Secure on GCP 2
The user interface for managing Halo Cloud Secure on GCP 2 is intuitive and user-friendly. It features a clean design with clear navigation, facilitating quick access to critical functions. The interface is designed with a focus on minimizing complexity while maximizing efficiency. Key features include customizable dashboards, intuitive filtering options, and detailed reporting capabilities.
Best Practices for Deploying and Managing Halo Cloud Secure on GCP 2
Implementing Halo Cloud Secure on GCP 2 requires a well-defined deployment strategy. Thorough planning, including clear roles and responsibilities, is critical. Security best practices, such as regularly reviewing and updating security policies, are paramount. Continuous monitoring and proactive threat detection are essential to maintaining a robust security posture.
Step-by-Step Guide for Deploying Halo Cloud Secure on GCP 2
- Establish GCP Project: Create a dedicated GCP project for Halo Cloud Secure deployment.
- Configure Network Settings: Establish secure network configurations to connect Halo Cloud Secure components to your GCP network.
- Provision Resources: Allocate the necessary compute resources (virtual machines, instances) for Halo Cloud Secure components.
- Configure Halo Cloud Secure Instance: Configure the Halo Cloud Secure instance according to your organization’s security requirements. This includes specifying user accounts, permissions, and other critical parameters.
- Integrate with GCP Services: Integrate Halo Cloud Secure with other GCP services, such as Cloud Storage or Cloud Logging, for enhanced data visibility and analysis.
- Validate and Test: Thoroughly validate the deployment and test the functionality of Halo Cloud Secure to ensure its proper operation.
- Implement Monitoring and Reporting: Establish a robust monitoring and reporting system to track the performance and effectiveness of Halo Cloud Secure.
Deployment Options on GCP 2 for Halo Cloud Secure
The following table Artikels the various deployment options available for Halo Cloud Secure on GCP 2. This variety caters to different needs and infrastructure configurations.
| Deployment Option | Description | Use Case |
|---|---|---|
| Compute Engine | Deploy Halo Cloud Secure components on Compute Engine virtual machines. | Suitable for organizations with existing Compute Engine infrastructure or those seeking greater control over resource allocation. |
| Cloud Functions | Use Cloud Functions for specific tasks or event-driven operations within Halo Cloud Secure. | Ideal for integrating Halo Cloud Secure with existing GCP functions and automating security workflows. |
| Cloud Run | Deploy Halo Cloud Secure components using Cloud Run for serverless deployments. | Suitable for organizations needing scalability and elasticity, with a focus on minimal operational overhead. |
Last Point
In conclusion, Halo Cloud Secure’s integration with Google Cloud Platform 2 offers a powerful security solution. By leveraging the advanced features and seamless integration, organizations can bolster their security posture and gain a competitive edge. The integration streamlines deployment and management, making it an attractive choice for modern cloud environments.
Commonly Asked Questions
What are the key benefits of Halo Cloud Secure on GCP 2?
Halo Cloud Secure on GCP 2 offers enhanced security features, improved performance, and simplified deployment, making it a robust and efficient security solution for modern cloud environments.
What are the supported GCP 2 services?
A detailed table outlining supported GCP 2 services and their compatibility with Halo Cloud Secure is included in the full article.
How does Halo Cloud Secure compare to other security solutions?
A comparative table highlighting key differences between Halo Cloud Secure and other similar solutions is available within the article, providing a clear understanding of its unique strengths.
What are some real-world use cases for Halo Cloud Secure on GCP 2?
Various use cases and practical applications, including demonstrations of how Halo Cloud Secure protects different GCP 2 applications, are explained in the article.





