Intel Zombieload Hacker Target
Intel Zombieload vulnerability might expose sensitive data like passwords to hackers. This sophisticated attack leverages a previously unknown flaw in Intel processors, potentially allowing malicious actors to steal sensitive information like passwords, financial details, and personal data. Understanding the mechanics of this vulnerability, its potential impact, and the protective measures is crucial for individuals and organizations to safeguard their digital assets.
This vulnerability is a wake-up call about the ever-evolving threat landscape in cybersecurity.
The vulnerability targets specific Intel processor architectures, making it crucial to understand the affected generations and models to take proactive steps in mitigation. This article explores the technical aspects of the vulnerability, the potential data exposure risks, and actionable steps to protect systems and data.
Intel Zombieload Vulnerability Overview
The Intel Zombieload vulnerability, a significant security flaw, allows unauthorized access to sensitive data. This vulnerability exploits a hardware-level weakness in certain Intel processor architectures, potentially exposing confidential information like passwords and other sensitive credentials. Its discovery highlighted the critical need for constant vigilance in safeguarding computing systems against novel and sophisticated attacks.
Vulnerability Details
The Zombieload vulnerability leverages a hardware mechanism designed for power management. Malicious actors can potentially exploit this mechanism to trigger unintended actions within the processor, allowing them to retrieve sensitive data. The precise method involves exploiting the processor’s ability to silently execute pre-loaded instructions, even when the processor isn’t actively handling a task. This covert execution allows for data leakage without triggering any noticeable system alerts.
Affected Intel processor architectures include those with specific power management features.
The Intel Zombieload vulnerability is a serious concern, potentially exposing sensitive data like passwords to hackers. This highlights the critical need for proactive security measures, like deploying AI Code Safety Goggles Needed to prevent similar vulnerabilities in the future. Deploying AI Code Safety Goggles Needed is crucial to scrutinizing code for potential flaws and ensuring the safety of systems, which in turn mitigates the risk of sensitive data breaches like those potentially caused by Zombieload.
Ultimately, the security of our systems is paramount, and proactive measures like these are essential.
Affected Intel Processor Architectures
The Zombieload vulnerability affects specific generations of Intel processors. These processors have unique hardware features that, if exploited, could lead to unintended data leakage. Understanding the affected models is crucial for implementing mitigation strategies.
The Intel Zombieload vulnerability is a serious concern, potentially exposing sensitive data like passwords to hackers. It’s crucial to understand how these vulnerabilities can impact our systems, especially when considering other potential exploits. Fortunately, Microsoft is actively addressing similar issues with the Azure Cosmos DB Vulnerability, which offers valuable insight into the broader landscape of potential cyber threats.
For more detailed information on the Azure Cosmos DB Vulnerability, check out the Azure Cosmos DB Vulnerability Details. Ultimately, the takeaway is that staying vigilant about vulnerabilities like Zombieload is essential to protecting our data.
| Processor Generation | Affected Models | Mitigation Strategies |
|---|---|---|
| Skylake | Specific Skylake models with certain power management features | Firmware updates and software patches are crucial mitigation strategies. |
| Kaby Lake | Specific Kaby Lake models with certain power management features | Firmware updates and software patches are crucial mitigation strategies. |
| Coffee Lake | Specific Coffee Lake models with certain power management features | Firmware updates and software patches are crucial mitigation strategies. |
| Comet Lake | Specific Comet Lake models with certain power management features | Firmware updates and software patches are crucial mitigation strategies. |
| Ice Lake | Specific Ice Lake models with certain power management features | Firmware updates and software patches are crucial mitigation strategies. |
Potential Impact, Intel zombieload vulnerability might expose sensitive data like passwords to hackers
The potential impact of the Zombieload vulnerability extends across various computing systems and software applications. Systems running affected Intel processors are at risk of unauthorized data access, leading to significant security breaches. The impact is significant, especially in systems handling sensitive information like financial transactions, healthcare records, or government data. Malicious actors could exploit this vulnerability to steal confidential information or disrupt operations.
Mitigation Strategies
Intel released updates to address the Zombieload vulnerability. These updates, including firmware updates and software patches, are essential for protecting affected systems. Users should regularly check for and install these updates to mitigate the risk of exploitation. Failure to update systems exposes them to potential security risks.
Data Exposure Risks
The Intel Zombieload vulnerability, while addressed, highlights a critical concern: the potential for sensitive data exposure. Attackers could leverage this type of vulnerability to gain unauthorized access to personal and financial information, creating significant risks for individuals and organizations. Understanding these risks is paramount for mitigating potential damage.The vulnerability allows attackers to potentially gain unauthorized access to systems, enabling them to steal or manipulate sensitive data.
This could involve a range of data types, from passwords and credit card information to personally identifiable information (PII) and confidential business documents. The ability to access this data can have profound and long-lasting consequences for individuals and organizations.
Potential Data Types at Risk
Understanding the types of data potentially exposed is crucial for effective risk assessment. Various categories of data, both personal and organizational, could be compromised. The potential impact of a breach varies greatly depending on the sensitivity of the exposed data.
| Data Type | Description | Potential Impact |
|---|---|---|
| Passwords | User accounts, application access credentials. | Unauthorized access to accounts, identity theft, financial fraud. |
| Financial Information | Credit card numbers, bank account details, transaction history. | Financial loss, fraud, identity theft, reputational damage. |
| Personally Identifiable Information (PII) | Names, addresses, phone numbers, dates of birth, social security numbers. | Identity theft, fraud, harassment, violation of privacy. |
| Health Information | Medical records, diagnoses, treatment plans. | Medical fraud, identity theft, violation of privacy, potential harm to health. |
| Intellectual Property | Trade secrets, designs, patents. | Loss of competitive advantage, financial losses, legal issues. |
Exploitation Methods and Real-World Examples
Attackers can exploit vulnerabilities in various ways. They may use social engineering tactics to trick users into revealing sensitive information, or they may employ sophisticated malware to gain unauthorized access. Sophisticated phishing campaigns have successfully targeted individuals and organizations, gaining access to confidential information. Past vulnerabilities have shown the severity of data breaches.The Target data breach, for instance, exposed millions of credit card numbers and other sensitive information.
This resulted in significant financial losses for Target and eroded consumer trust. Similar breaches have impacted other major corporations, emphasizing the critical need for robust security measures.
Financial and Reputational Damage
Data breaches can cause significant financial and reputational damage to organizations. The cost of data breaches can include not only direct financial losses but also legal fees, regulatory penalties, and damage to brand reputation. The cost of restoring systems and recovering from a breach can be substantial, and long-term trust may be damaged.A compromised system could lead to significant financial loss and reputational damage, as customer trust and confidence are eroded.
Recovering from such an incident can be time-consuming and costly, with lasting implications for the organization’s future.
Impact on Different Sectors
The Intel Zombieload vulnerability, while initially identified as a CPU-level issue, has far-reaching implications across various sectors. Its potential for exploitation transcends simple data breaches, affecting operational stability and potentially causing significant financial losses. Understanding the diverse impacts is crucial for proactive mitigation and risk management.The Zombieload vulnerability allows attackers to potentially hijack CPU resources without the user’s knowledge or consent.
This covert nature makes it a particularly insidious threat. The implications extend beyond simple data breaches to encompass disruptions in critical operations and potential financial ruin for vulnerable organizations.
Susceptible Sectors
Numerous sectors are vulnerable to attacks exploiting the Zombieload vulnerability. These include, but are not limited to, finance, healthcare, government, and critical infrastructure. Each sector faces unique challenges and potential consequences, ranging from financial losses to significant operational disruptions.
Financial Sector
The financial sector is particularly vulnerable due to the high value of data and the reliance on robust security systems. Compromised systems could lead to unauthorized access to sensitive financial information, including account details, transaction records, and customer data. This could result in substantial financial losses through fraudulent transactions and reputational damage. The 2017 Equifax data breach, which exposed the personal information of millions, serves as a stark reminder of the potential impact of such vulnerabilities.
Financial institutions must implement robust security measures and regularly update their systems to prevent exploitation.
Healthcare Sector
The healthcare sector faces unique challenges with Zombieload, as patient data is extremely sensitive and confidential. Compromised systems could lead to the theft of medical records, including diagnoses, treatment plans, and personal information. This could have severe implications for patient privacy and potentially jeopardize their health and well-being. The potential for unauthorized access to medical data highlights the critical need for strong security protocols and robust data encryption within healthcare organizations.
Government Sector
The government sector, responsible for managing sensitive national information, is also at risk. Exploiting the Zombieload vulnerability could provide unauthorized access to classified information, national security data, and critical infrastructure details. This could have far-reaching consequences, impacting national security, public safety, and the stability of the government itself. The importance of robust security measures and continuous monitoring is paramount for government agencies.
Critical Infrastructure Sector
Critical infrastructure sectors, such as energy, transportation, and utilities, are also highly vulnerable. A successful attack could disrupt essential services, causing widespread damage and operational disruption. The cascading effects of such attacks can have catastrophic consequences, affecting public safety and potentially causing widespread panic and chaos. The reliance on uninterrupted operations within these sectors necessitates strong security protocols and robust incident response plans.
Comparative Impact Table
| Sector | Potential Impact | Mitigation Strategies |
|---|---|---|
| Finance | Financial losses, fraud, reputational damage, compromised customer data. | Robust security measures, multi-factor authentication, regular security audits, data encryption. |
| Healthcare | Theft of medical records, patient privacy violations, potential harm to patient health, reputational damage. | Strong encryption, access controls, regular security assessments, incident response plans. |
| Government | Unauthorized access to classified information, national security breaches, disruption of critical operations. | Enhanced security protocols, regular security audits, advanced threat detection systems, secure data handling procedures. |
| Critical Infrastructure | Disruption of essential services, widespread damage, operational disruptions, potential public safety concerns. | Robust security systems, redundancy, fail-safes, incident response plans, continuous monitoring. |
Mitigation Strategies and Prevention
The Intel Zombieload vulnerability necessitates proactive measures to minimize the risk of exploitation. Effective mitigation strategies encompass various approaches, ranging from operating system updates to user-level precautions. Understanding these strategies is crucial for safeguarding sensitive data and maintaining system integrity.
Operating System and Software Updates
Regular updates are paramount in countering vulnerabilities. Operating systems and software applications frequently receive patches addressing known security flaws. These updates often include fixes for vulnerabilities like Zombieload, strengthening the system’s defenses against exploitation attempts. Failure to apply these updates leaves systems susceptible to attacks.
Hardware Patches
While less common, hardware patches can also be crucial. Intel, in response to the Zombieload vulnerability, might release firmware updates that address the underlying hardware issue. These updates often require specialized tools and procedures for deployment, and their efficacy depends on the specific hardware configuration.
User-Level Security Practices
Users play a critical role in mitigating the risk. Strong passwords, enabling two-factor authentication, and avoiding suspicious links or downloads can significantly reduce the likelihood of compromise. Regular security awareness training can empower users to recognize and respond to potential threats.
Recommended Actions for Individuals and Organizations
A proactive approach requires a multi-faceted strategy. Individuals should prioritize regular software updates, use strong passwords, and avoid untrusted sources. Organizations should implement robust patch management systems, conduct regular security audits, and train employees on security best practices. This comprehensive approach is essential for safeguarding against exploitation.
- Keep operating systems and software updated: Regularly checking for and installing updates is critical. Automated update systems can simplify this process and ensure that the latest security patches are applied promptly.
- Use strong passwords and enable multi-factor authentication: Employing complex passwords and enabling two-factor authentication adds an extra layer of security, making it harder for attackers to gain unauthorized access.
- Avoid suspicious links and downloads: Be cautious about clicking on links or downloading files from untrusted sources. Phishing emails and malicious websites are common methods used to exploit vulnerabilities like Zombieload.
- Implement robust patch management systems: Organizations should establish a system for regularly identifying, testing, and deploying security patches for all software and hardware components.
- Conduct regular security audits: Regular security audits help identify vulnerabilities and weaknesses in systems and processes, allowing for timely remediation.
- Provide security awareness training to employees: Educating employees about common security threats and best practices is essential for creating a security-conscious environment.
Patching and Updating System Flowchart
This flowchart Artikels the process of patching and updating systems to prevent exploitation.
| Step | Action |
|---|---|
| 1 | Identify Vulnerability: Regularly scan systems and software for known vulnerabilities like Zombieload. |
| 2 | Obtain Patches/Updates: Download necessary patches and updates from official sources (e.g., vendor websites). |
| 3 | Testing Patches: Thoroughly test patches in a non-production environment to ensure compatibility and functionality. |
| 4 | Deployment Planning: Create a detailed deployment plan, including scheduling and resource allocation. |
| 5 | Deployment: Apply patches and updates to affected systems according to the plan. |
| 6 | Post-Deployment Verification: Verify that the updates have been successfully applied and that systems are functioning correctly. |
Future Implications and Research
The Intel Zombieload vulnerability highlights a critical gap in our understanding of system-level security, exposing the potential for insidious and long-lasting threats. The ongoing research into this vulnerability is crucial to preventing future attacks and ensuring the safety of sensitive data. This exploration delves into the potential for future exploits, the evolving threat landscape, and the required research to mitigate these risks.Understanding the long-term impact of this vulnerability necessitates a deep dive into the potential for future attacks and the ongoing research efforts.
The implications extend beyond immediate security concerns and touch upon fundamental trust in computing systems.
Ongoing Research and Development Efforts
Researchers are actively investigating various aspects of the vulnerability, including the extent of its impact across different hardware architectures. The primary focus is on developing effective mitigation strategies and understanding the root causes of the vulnerability. Academic institutions and industry groups are collaborating to address the issue, creating a dynamic research landscape. This collaborative approach is crucial to accelerate the development of robust countermeasures and future-proof systems.
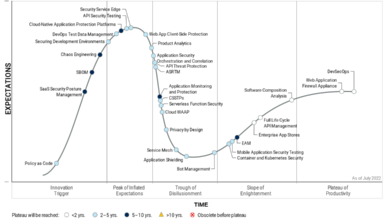
Potential for Future Attacks and Exploits
The potential for future attacks leveraging Zombieload-like vulnerabilities is significant. Attackers could exploit similar weaknesses in other hardware platforms, or potentially develop novel methods to circumvent existing security measures. The sophisticated nature of the Zombieload attack highlights the need for proactive security measures beyond traditional software-based approaches. Understanding how the vulnerability might manifest in future designs, especially in embedded systems or IoT devices, is crucial.
Long-Term Implications on the Security Landscape
The Zombieload vulnerability demonstrates a critical shift in the threat landscape. The attack vector, hidden within the hardware, challenges traditional security paradigms. This underscores the importance of a multi-layered security approach that combines hardware, firmware, and software protections. A future security strategy must include rigorous hardware security assessments and a greater emphasis on secure design practices throughout the entire product lifecycle.
The Intel Zombieload vulnerability is a serious concern, potentially exposing sensitive data like passwords to hackers. Fortunately, the Department of Justice’s recent safe harbor policy for Massachusetts transactions, outlined in Department of Justice Offers Safe Harbor for MA Transactions , might offer some reassurance for affected users, but ultimately, the risk of compromised data remains.
We need to stay vigilant and prioritize strong security practices to mitigate the risk of data breaches.
This means scrutinizing the entire system, from the chip level to the application layer.
Evolving Threat Landscape and Impact on Cybersecurity Strategies
The Zombieload vulnerability serves as a stark reminder that security threats are constantly evolving. Traditional software-centric approaches are insufficient to combat sophisticated hardware-level attacks. Future cybersecurity strategies must adapt to this new reality, incorporating hardware security assessments and robust threat modeling. Organizations need to develop comprehensive security strategies that include proactive vulnerability detection and mitigation.
Potential Research Areas to Further Understand the Vulnerability
Several areas require further research to fully comprehend and address the Zombieload vulnerability. These include:
- Developing Standardized Hardware Security Assessment Methods: Creating standardized and reliable methods to evaluate the security of hardware components is essential. This will help to identify and address vulnerabilities like Zombieload in future designs. These methods should be universally adopted.
- Improving Firmware Security Practices: The vulnerability highlights the critical role of firmware security. Research should focus on developing secure firmware development methodologies and incorporating robust security checks into the firmware development lifecycle.
- Exploring Novel Hardware Security Architectures: Innovative approaches to hardware design that inherently mitigate such vulnerabilities are crucial. This includes researching new architectural patterns and design principles that make it harder for malicious actors to exploit vulnerabilities. The research should focus on enhancing the security at the micro-architectural level.
Security Best Practices: Intel Zombieload Vulnerability Might Expose Sensitive Data Like Passwords To Hackers
The Zombieload vulnerability highlights the critical need for proactive security measures beyond patching. Protecting sensitive data and systems requires a multifaceted approach encompassing strong passwords, multi-factor authentication, regular audits, and a culture of security awareness. This section delves into practical security best practices to mitigate the risk of data breaches and maintain system integrity.Implementing robust security measures is not just a technical exercise; it’s a crucial aspect of responsible digital stewardship.
By adopting these best practices, organizations can significantly reduce their vulnerability to cyber threats and safeguard sensitive information.
Strong Password Policies and Practices
Strong passwords are the first line of defense against unauthorized access. Weak passwords are easily guessed or cracked, leaving systems vulnerable. A robust password policy should enforce complexity requirements and regular password changes. Users should be educated on the importance of creating and using strong passwords. Password managers can be valuable tools to help users generate and store complex passwords securely.
Avoid using easily guessed passwords like birthdays, names, or common phrases.
Multi-Factor Authentication (MFA)
Multi-factor authentication adds an extra layer of security by requiring more than one form of verification. This significantly reduces the risk of unauthorized access even if a password is compromised. MFA typically involves a combination of something you know (password), something you have (security token, mobile device), or something you are (biometric authentication). Employing MFA across all sensitive accounts, especially for online banking, email, and cloud storage, is crucial.
Regular Security Audits and Assessments
Regular security audits and assessments are essential to identify vulnerabilities and weaknesses in systems and processes. These assessments should cover various aspects, including network security, access controls, and application security. Results from audits and assessments should be used to prioritize remediation efforts. Security assessments should be conducted on a regular basis, as threats and vulnerabilities evolve over time.
The frequency and scope of these assessments should be tailored to the specific needs and risk profile of the organization.
Security Best Practices Overview
| Practice | Description | Importance |
|---|---|---|
| Strong Password Policies | Enforce complexity requirements, regular password changes, and education on creating strong passwords. | First line of defense against unauthorized access. |
| Multi-Factor Authentication (MFA) | Implement MFA across all sensitive accounts to require more than one form of verification. | Adds an extra layer of security, reducing risk even if passwords are compromised. |
| Regular Security Audits and Assessments | Conduct periodic assessments of systems and processes to identify vulnerabilities. | Proactive identification of weaknesses and prioritization of remediation efforts. |
| Security Awareness Training | Educate users about phishing attacks, social engineering, and other security threats. | Reduces human error in security breaches and promotes a culture of security. |
Summary
In conclusion, the Intel Zombieload vulnerability presents a significant security risk, potentially exposing sensitive data to malicious actors. Understanding the nature of the vulnerability, its impact across various sectors, and the available mitigation strategies is paramount. By implementing robust security measures, including regular software updates and strong password policies, individuals and organizations can significantly reduce the risk of exploitation.
The ongoing research and development in this area are vital for maintaining a secure digital environment.
Q&A
What are the most common types of data that could be compromised by this vulnerability?
Sensitive data such as usernames, passwords, financial information, and personal details are at risk. Attackers could potentially gain unauthorized access to sensitive data stored on compromised systems.
How can individuals protect themselves from this vulnerability?
Staying updated with the latest security patches and updates for operating systems and software is crucial. Implementing strong passwords, enabling multi-factor authentication where available, and practicing safe online habits are also key protective measures.
What sectors are most vulnerable to attacks exploiting this vulnerability?
Financial institutions, healthcare organizations, and government agencies are particularly vulnerable due to the high value and sensitive nature of the data they handle.
Are there any known cases of this vulnerability being exploited in the real world?
While this vulnerability is relatively new, the potential for exploitation is high, and there’s a strong likelihood that attackers will seek ways to leverage it.