Connecting Dots Complex Threat Landscape
How to connect all the dots in a complex threat landscape is crucial for modern security. This exploration delves into the multifaceted nature of threats, revealing how vulnerabilities, actors, and attack vectors interconnect. We’ll uncover key indicators, analyze attack pathways, and develop a holistic security strategy to navigate this intricate threat environment.
Understanding the interconnectedness of threats is paramount. A siloed approach falls short; instead, a comprehensive view across physical, digital, and human factors is needed to fully grasp the complexities of today’s threat landscape. This involves examining various attack pathways, from single incidents to multi-stage campaigns targeting multiple interconnected systems.
Defining the Threat Landscape
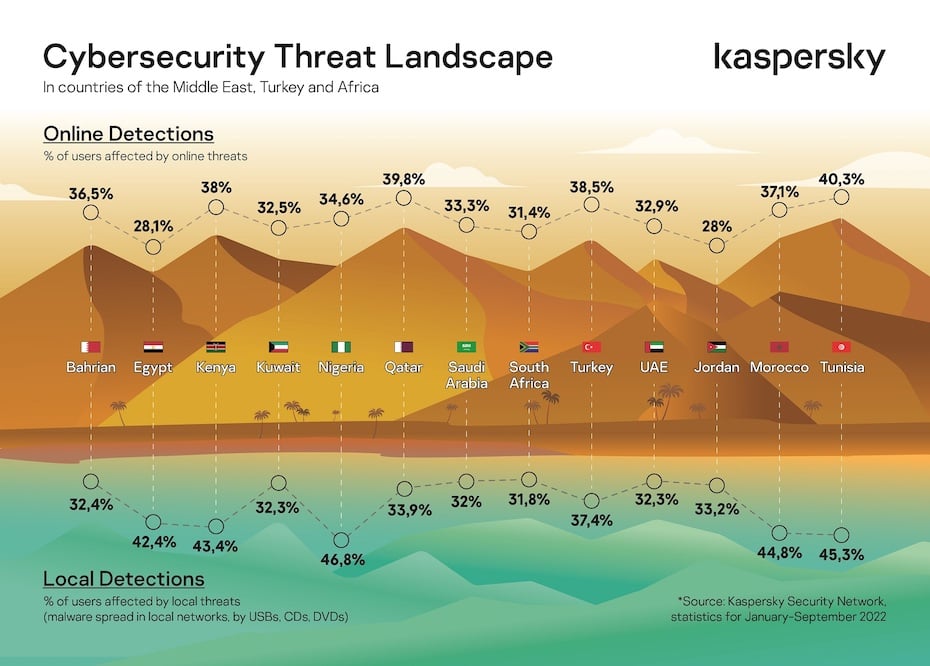
The modern threat landscape is a complex web of interconnected vulnerabilities, actors, and attack vectors. Understanding this intricate network is crucial for effective security strategies. It’s no longer sufficient to consider threats in isolation; instead, we must recognize the relationships and dependencies between different elements. A comprehensive understanding of this landscape is essential for proactively mitigating risks and bolstering overall security posture.The threat landscape is not static.
Figuring out a complex threat landscape is like piecing together a puzzle with missing pieces. You need to gather all the intel, from various sources, like a detective. Understanding the Department of Justice Offers Safe Harbor for MA Transactions here can be one of those pieces. This policy, like a key to unlocking a safe, can give you a better view of potential vulnerabilities, which helps in connecting those fragmented dots to get a more complete picture of the threat.
Ultimately, this all helps in better threat detection and response.
It evolves constantly, adapting to technological advancements, societal changes, and the actions of malicious actors. This dynamic nature necessitates a continuous, holistic assessment to identify emerging threats and adapt defenses accordingly.
Components of a Complex Threat Landscape
The complex threat landscape is comprised of various interacting components. These elements are not isolated entities; instead, they influence and interact with one another in intricate ways. Understanding these interactions is key to developing effective security strategies.
- Vulnerabilities: These represent weaknesses in systems, processes, or human behavior that can be exploited by attackers. Vulnerabilities exist in software, hardware, network configurations, and even organizational policies. The interconnectedness of systems often magnifies the impact of vulnerabilities, creating cascading effects. For example, a vulnerability in a supply chain component can impact multiple downstream systems.
- Actors: Malicious actors encompass a wide spectrum of individuals and groups. These range from nation-state adversaries to organized crime groups, hacktivists, and lone wolves. Each actor has unique motivations, capabilities, and target preferences. Understanding these motivations and capabilities is crucial for predicting potential attacks and developing appropriate countermeasures.
- Attack Vectors: Attack vectors represent the pathways or methods attackers use to exploit vulnerabilities. These include phishing emails, malware infections, compromised credentials, and social engineering tactics. The emergence of new attack vectors and their increasing sophistication necessitate continuous adaptation of security measures.
Interconnectivity in Threat Landscapes
Interconnectivity is a defining characteristic of modern threat landscapes. Different components interact in complex ways, amplifying the potential for widespread damage. For example, a compromise of a financial institution’s systems can have repercussions for the entire financial sector. A breach in a healthcare organization’s network can affect patient confidentiality and safety.
- Supply Chain Attacks: Vulnerabilities in supply chains can expose multiple organizations to risks. A malicious actor could compromise a software vendor, introducing malware into the products used by numerous companies. This demonstrates the critical importance of supply chain security and the need for robust vetting and monitoring processes.
- Financial Sector Interconnections: The interconnected nature of financial institutions and markets means that a breach in one organization can quickly spread to others. The financial sector is particularly susceptible to sophisticated attacks exploiting vulnerabilities in payment systems, trading platforms, and customer databases.
- Healthcare Sector Risks: The healthcare sector faces unique threats related to patient data breaches and disruptions to critical services. A cyberattack could expose sensitive patient information, leading to significant privacy violations and potentially impacting treatment plans. The interconnected nature of healthcare systems makes them vulnerable to cascading failures.
Holistic vs. Siloed Approaches
A holistic view of the threat landscape recognizes the interdependencies between various elements. This approach contrasts with a siloed approach that examines threats in isolation. A holistic view fosters a more comprehensive understanding of risks, enabling more effective strategies for mitigation and response.
Layers of the Threat Landscape
| Layer | Description |
|---|---|
| Physical | This layer encompasses the physical infrastructure, including buildings, equipment, and access controls. Physical security measures are crucial for preventing unauthorized access and protecting assets. |
| Digital | This layer encompasses the network infrastructure, software applications, and data systems. Robust cybersecurity measures are needed to protect digital assets from breaches and attacks. |
| Human | This layer involves the human element, including employees, contractors, and customers. Human error, social engineering, and lack of awareness are critical factors that can compromise security. Security awareness training and policies play a significant role in mitigating these risks. |
Identifying Interconnections
Connecting the dots in a complex threat landscape isn’t just about identifying individual threats; it’s about understanding the relationships between them. This crucial step reveals the bigger picture, allowing for proactive security measures and a more effective response strategy. By recognizing the interconnections, organizations can anticipate and mitigate emerging threats, rather than reacting to them. Understanding how different attacks relate, and where vulnerabilities lie, is paramount in modern cybersecurity.Understanding the relationships between seemingly disparate security events is vital for effective threat hunting and incident response.
This understanding allows for the development of more comprehensive and targeted security strategies, rather than reacting to individual threats in isolation. By analyzing the interconnectedness of events, organizations can identify trends, predict future attacks, and proactively strengthen their defenses.
Key Indicators and Signals for Spotting Interconnections
Identifying key indicators and signals for spotting interconnections is crucial. These signals often include unusual patterns in network traffic, unusual login attempts from specific IP addresses, or the use of similar malware across different systems. Analyzing these patterns helps reveal underlying relationships and potential threats. For instance, a surge in login attempts from a specific IP range in conjunction with a known phishing campaign might indicate a coordinated attack.
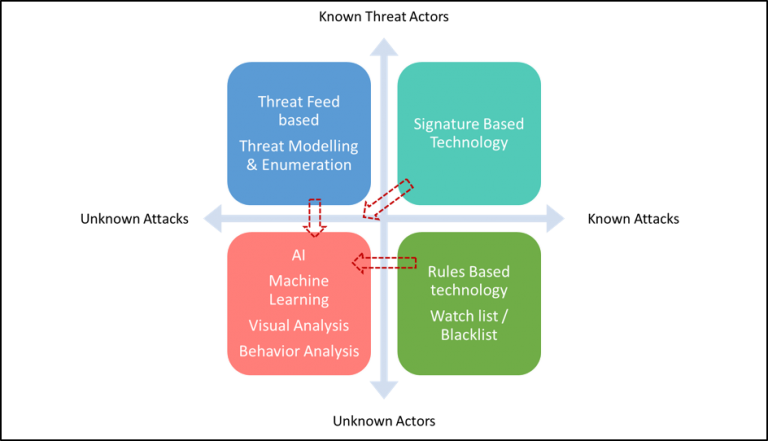
Analyzing Threat Intelligence Data for Relationships
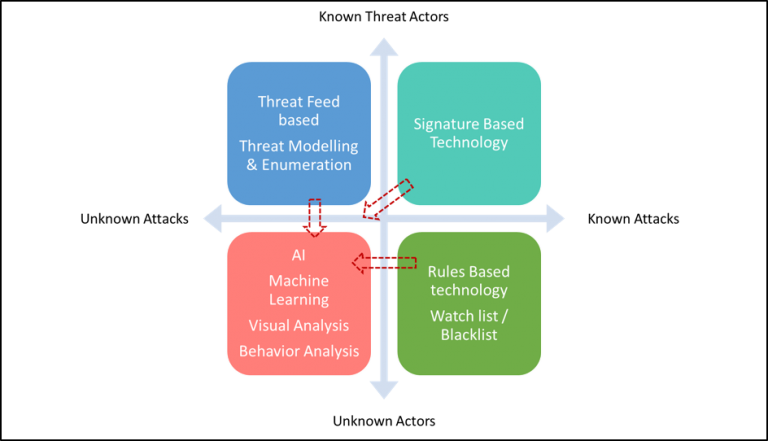
Threat intelligence data, when analyzed for relationships, provides a rich source of insights. Methods include correlation analysis, which identifies patterns and anomalies in collected data. Advanced techniques, like machine learning algorithms, can detect subtle relationships that might be missed by traditional methods. For example, identifying a common malware family across multiple victims can reveal a sophisticated criminal operation.
Mapping and Visualizing Threat Relationships
Mapping and visualizing relationships between threats allows for a comprehensive view of the threat landscape. This can be achieved through various visualization tools that create diagrams showing connections between different actors, events, and vulnerabilities. For instance, a map might show the path of a ransomware attack from initial compromise to data exfiltration, highlighting the interconnected vulnerabilities exploited.
Analyzing Interconnected Security Incidents
Analyzing the interconnectedness of various security incidents is crucial for understanding the scope and impact of attacks. This involves a systematic approach to identifying patterns, overlaps, and common threads across different incidents. Tools and methodologies like threat hunting play a crucial role. For example, a series of phishing attacks targeting specific departments might indicate a targeted social engineering campaign.
Comparing Threat Intelligence Platforms
Different threat intelligence platforms offer varying capabilities for identifying connections. Some specialize in network traffic analysis, while others focus on malware analysis. A comprehensive approach often requires combining data from multiple platforms to gain a holistic view. Comparison should include features like correlation capabilities, visualization tools, and integration with existing security systems. For example, a platform with robust correlation engines can identify connections between disparate events more efficiently than one lacking such capabilities.
Threat Intelligence Sources and Interconnection Potential
| Threat Intelligence Source | Potential for Identifying Interconnections |
|---|---|
| Security Information and Event Management (SIEM) data | High; identifies patterns in logs, network traffic, and user activity |
| Open-source intelligence (OSINT) | Medium; can uncover relationships between actors and activities |
| Threat feeds from security vendors | High; often contain detailed information about campaigns and connections |
| Vulnerability databases | Medium; can highlight connections between vulnerabilities exploited in different attacks |
| Dark web forums and marketplaces | High; provide insight into attackers’ tactics and motivations, and potential future attacks |
Understanding Attack Pathways
Navigating a complex threat landscape requires a deep understanding of how attackers operate. This involves more than just identifying vulnerabilities; it’s about comprehending the interconnected pathways they use to exploit those vulnerabilities. This section delves into the intricacies of attack pathways, focusing on multi-stage attacks and the role of human error.Attackers leverage the intricate connections between systems to their advantage.
They employ sophisticated techniques to exploit vulnerabilities in one system to gain access to others, creating a cascading effect of potential harm. Understanding these pathways is crucial for developing robust defenses.
Different Attack Pathways
Attack pathways are not linear. They can involve multiple stages, exploits, and entry points. Attackers may initially target a seemingly minor system, using it as a stepping stone to gain access to more critical assets. This often involves exploiting vulnerabilities in interconnected systems, which is crucial to understand.
Multi-Stage Attacks
Multi-stage attacks are a common tactic in today’s threat landscape. These attacks involve multiple phases, each designed to exploit specific vulnerabilities and progressively escalate access privileges. They typically involve a series of actions that build upon each other.
Methods of Exploitation
Attackers utilize a variety of methods to exploit interconnected systems. These include phishing, social engineering, malware, and exploiting known software vulnerabilities. They leverage the interconnectedness of systems to move laterally across the network.
Human Error as a Pathway
Human error plays a significant role in creating attack pathways. Weak passwords, clicking malicious links, or failing to update software can provide attackers with an entry point. This is why security awareness training is essential.
Figuring out the interconnectedness of threats in a complex landscape can be tricky. It’s like trying to assemble a puzzle with missing pieces. To truly connect all the dots, you need the right tools, and that includes deploying AI Code Safety Goggles Needed Deploying AI Code Safety Goggles Needed to identify potential vulnerabilities in code. Ultimately, these advanced tools are crucial for seeing the full picture and preventing future breaches.
Examples of Exploitation
Attackers frequently exploit vulnerabilities in interconnected systems. For instance, a compromised email server might be used to launch phishing attacks against other systems in the network. This illustrates the potential harm of not understanding attack pathways.
Steps in a Multi-Stage Attack
A multi-stage attack targeting multiple interconnected systems might involve these steps:
- Initial Compromise: Attackers gain initial access through a vulnerable system, often a web server or email account.
- Lateral Movement: Attackers use the initial access to move laterally through the network, exploiting vulnerabilities in other systems. This is achieved through exploiting weaknesses in firewalls, network segmentation, and other security controls.
- Privilege Escalation: Attackers elevate their access privileges, gaining control over critical systems and data. This could involve exploiting vulnerabilities in operating systems or applications.
- Data Exfiltration: Attackers extract sensitive data from the compromised systems. This data could include financial records, intellectual property, or customer information.
- Data Destruction: In some cases, attackers may deliberately destroy or modify data to disrupt operations or cause damage.
Illustrative Flowchart
The following flowchart depicts a potential multi-stage attack across various components:
(Imagine a flowchart here, if you were using a drawing tool, that would visually illustrate the multi-stage attack process. This would include boxes for each step mentioned above, connected by arrows to show the sequence. You could show different systems as separate boxes, like a web server, database server, and email server, connected to each other. You could also show the attacker’s actions in each step.)
Developing a Holistic Security Strategy: How To Connect All The Dots In A Complex Threat Landscape
Connecting the dots in a complex threat landscape requires a proactive and integrated security strategy. Simply reacting to attacks is no longer sufficient. A holistic approach demands understanding the interconnected nature of threats, anticipating potential attack pathways, and building a resilient security posture capable of adapting to evolving dangers. This involves a multifaceted framework that goes beyond individual security controls to encompass the entire organization’s security posture.A comprehensive security strategy must recognize that threats are not isolated events but rather interconnected parts of a larger ecosystem.
This strategy must proactively identify and mitigate potential vulnerabilities, not just react to incidents. This requires a deep understanding of the organization’s digital footprint, its interconnected systems, and the potential attack vectors that could exploit these connections.
Framework for a Comprehensive Security Strategy
A robust security strategy requires a framework that considers the interconnected nature of threats. This framework should encompass all aspects of the organization’s digital environment, from individual devices to complex enterprise applications and cloud infrastructure. Key elements include a defined incident response plan, clear communication channels, and regular security assessments.
Figuring out a complex threat landscape often feels like connecting scattered puzzle pieces. A key element in this process is understanding specific vulnerabilities, like the ones detailed in Azure Cosmos DB Vulnerability Details. By examining these details, you gain a clearer picture of the potential weaknesses and how they might fit into the bigger picture of potential attacks.
This helps in strategizing stronger defenses and proactive security measures.
Importance of Proactive Threat Hunting and Intelligence Gathering
Proactive threat hunting and intelligence gathering are critical components of a holistic security strategy. They allow organizations to anticipate and address potential threats before they materialize into actual attacks. This involves actively searching for malicious activity within the organization’s systems and networks, as well as monitoring external threat intelligence sources to identify emerging risks. Organizations must maintain a continuous awareness of the threat landscape and adapt their defenses accordingly.
Methods for Building a Resilient Security Posture
Building a resilient security posture involves several key methods. First, implement layered security controls to mitigate vulnerabilities at multiple points within the system. Second, ensure regular security assessments and penetration testing to identify and address weaknesses. Third, develop a comprehensive incident response plan, including clear communication channels and well-defined roles and responsibilities. Finally, promote a security-conscious culture within the organization, encouraging employees to report suspicious activity and adhere to security protocols.
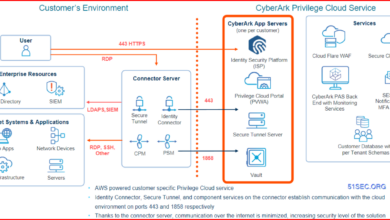
Integrating Different Security Measures Across Interconnected Systems
Integrating different security measures across interconnected systems is crucial for a holistic approach. This requires establishing clear communication and data sharing protocols between security teams responsible for different systems or applications. Implementing a centralized security information and event management (SIEM) system can help correlate security events across various platforms, improving threat detection and response capabilities. Security tools must be integrated seamlessly to provide a unified view of the security posture.
Prioritizing Security Controls Based on Identified Interconnections
Prioritizing security controls is essential to focus resources on the most critical areas. A risk assessment methodology is needed to determine the impact and likelihood of potential threats exploiting interconnections. Controls should be prioritized based on the identified vulnerabilities and potential impact of a successful attack. For instance, critical infrastructure or data repositories should receive higher priority than less sensitive systems.
Security Control Matrix for Interconnected Systems
| Security Control | Impact (High/Medium/Low) | Likelihood (High/Medium/Low) | Priority (High/Medium/Low) | Mitigation Strategy |
|---|---|---|---|---|
| Network Segmentation | High | Medium | High | Isolate critical systems, enforce access controls |
| Multi-factor Authentication | High | High | High | Implement MFA across all critical systems |
| Endpoint Detection and Response (EDR) | Medium | Medium | Medium | Monitor endpoint activity, identify malicious behavior |
| Vulnerability Management | High | Low | Medium | Regular scans, patch management |
This table provides a simplified example of a security control matrix. A real-world implementation would require a more comprehensive assessment of the organization’s specific vulnerabilities and threat landscape.
Illustrating Complex Interconnections
Mapping the intricate web of threats in a modern digital landscape requires more than just identifying individual vulnerabilities. It necessitates visualizing the intricate connections between them, understanding how a weakness in one area can potentially unlock access to other, seemingly unrelated systems. This visualization process is crucial for developing effective security strategies and proactive incident responses.
Visual Representation of a Complex Threat Landscape
A comprehensive threat landscape visualization should depict interconnected nodes representing different systems, applications, and data stores. Each node should be linked to others based on their functional dependencies and data flows. Color-coding can highlight critical systems or those with high vulnerability scores. Arrows can indicate potential attack pathways, emphasizing the flow of data and the potential for exploitation.
This visual representation aids in identifying the points of vulnerability and the interconnectedness of systems, providing a holistic view of the threat landscape.
Vulnerabilities Leading to Exploitation
Weaknesses in one area can act as stepping stones for attacks on other parts of the system. For example, a compromised employee account with access to a customer database could allow attackers to exfiltrate sensitive data. This compromised account could then be used to gain access to a network management system, allowing attackers to escalate their privileges and potentially disrupt critical services.
This demonstrates how vulnerabilities in seemingly disparate systems can create a cascading effect, enabling sophisticated attacks.
Intersecting Attack Vectors
Various attack vectors often converge within a complex system. A phishing campaign, for instance, might exploit a vulnerability in a web application, giving attackers access to sensitive data. Simultaneously, a compromised network device might provide a backdoor, allowing attackers to move laterally within the network. Identifying these intersecting attack vectors is essential for comprehensive threat modeling. This requires considering the various attack avenues, the potential for lateral movement, and the interconnectedness of systems.
Real-World Incident Example: The Target Breach
The 2013 Target data breach exemplifies interconnected threats. Attackers initially exploited a vulnerability in a third-party vendor’s HVAC system. This access provided a foothold to penetrate Target’s network, allowing them to move laterally and eventually steal millions of customer credit card numbers. This incident highlighted the importance of considering the interconnectedness of systems, even those seemingly unrelated to the core business.
The breach emphasized the risk posed by vulnerabilities in third-party vendors and the need for robust security monitoring across the entire supply chain.
Successful Incident Response Case Study: Equifax, How to connect all the dots in a complex threat landscape
While not a perfect example ofsuccessful* response, the Equifax breach shows how a multifaceted approach to interconnected threats can be implemented. Equifax initially failed to detect the intrusion, which was due to the complexity of the threat landscape. The response involved a significant effort to contain the breach, investigate the attack, and notify affected customers. While this incident showcased the limitations of traditional security approaches, it also demonstrated the need for a proactive, interconnected security strategy that anticipates and addresses potential attacks from multiple vectors.
Visualizing Threat Evolution
A dynamic visualization tool can track the evolution of a threat across interconnected systems. This tool would track the movement of malware, the exploitation of vulnerabilities, and the escalation of privileges over time. Color-coded nodes could represent the systems, and lines of varying thickness and color could indicate the intensity and frequency of the threat. Such a tool would enable security teams to understand how an attack unfolds and anticipate future threats.
This proactive approach is crucial in preventing and mitigating the impact of complex threats in interconnected systems.
Tools and Technologies
Navigating the intricate web of interconnected threats requires robust tools and technologies. Simply identifying vulnerabilities isn’t enough; effective security relies on the ability to monitor, analyze, and respond to the dynamic interactions within the threat landscape. This necessitates sophisticated tools capable of detecting subtle connections and predicting potential attack pathways. The right technologies empower organizations to proactively address emerging threats, minimize impact, and strengthen their overall security posture.Sophisticated threat intelligence platforms, coupled with automated monitoring systems, form the backbone of a proactive security strategy.
These tools aren’t just reactive; they empower security teams to anticipate and respond to evolving threats, fostering a more resilient security architecture.
Threat Intelligence Platforms
Threat intelligence platforms are crucial for analyzing and understanding interconnected threats. They provide a centralized repository of threat data, enabling security analysts to connect disparate pieces of information and identify emerging patterns. These platforms leverage machine learning and advanced analytics to detect anomalies, identify potential attack vectors, and provide actionable intelligence. Examples include platforms from companies like Recorded Future, Dragos, and Mandiant.
Security Information and Event Management (SIEM) Systems
SIEM systems are fundamental for collecting and analyzing security logs from various sources within an organization. They provide a comprehensive view of security events, enabling analysts to identify anomalies, track suspicious activity, and respond to potential threats. The key advantage of SIEM is its ability to aggregate data from multiple sources, providing a unified view of the security posture.
This consolidated view facilitates the identification of connections between seemingly disparate events, allowing security teams to respond to interconnected threats more effectively. Popular SIEM vendors include Splunk, QRadar, and ArcSight.
Endpoint Detection and Response (EDR) Tools
EDR tools monitor endpoints for malicious activity, enabling swift detection and response to potential threats. They can be instrumental in identifying and isolating compromised endpoints, preventing the spread of malware and containing the damage from a sophisticated attack. EDR tools also play a crucial role in identifying the interconnections between compromised endpoints and the broader threat landscape, providing critical insights for incident response.
Examples include CrowdStrike Falcon, Carbon Black, and SentinelOne.
Vulnerability Management Systems
Vulnerability management systems (VMS) are critical for identifying and mitigating vulnerabilities within an organization’s IT infrastructure. These systems automate the process of scanning for vulnerabilities, prioritizing them based on severity, and providing remediation recommendations. A crucial aspect of VMS is the ability to link identified vulnerabilities to potential attack vectors and threat actors, providing valuable context for threat modeling and incident response.
Popular VMS include Nessus, OpenVAS, and QualysGuard.
Network Security Monitoring (NSM) Tools
NSM tools monitor network traffic for suspicious activity, providing valuable insights into potential threats. They allow security teams to identify anomalous patterns, track malicious actors, and proactively mitigate potential attacks. NSM tools often correlate network events with other security data sources, such as SIEM and EDR systems, to provide a more holistic view of the threat landscape. Examples include SolarWinds NTA, Palo Alto Networks, and Cisco’s Firepower.
Comparison of Threat Analysis Tools
| Tool Type | Description | Interconnection Analysis Capabilities | Strengths | Weaknesses |
|---|---|---|---|---|
| Threat Intelligence Platforms | Centralized threat data repository | Excellent, correlates various data points | Comprehensive view, proactive threat hunting | Requires significant data ingestion and processing |
| SIEM | Collects and analyzes security logs | Good, can identify connections between events | Comprehensive log analysis, alerts on anomalies | May require significant configuration and expertise |
| EDR | Monitors endpoints for malicious activity | Good, isolates compromised endpoints, identifies attacker behavior | Quick detection, proactive response | Relies on endpoint agents, agent management can be complex |
| VMS | Identifies and prioritizes vulnerabilities | Moderate, links vulnerabilities to potential attack vectors | Automated vulnerability scanning, prioritization | May not always identify all interconnections, requires integration |
| NSM | Monitors network traffic for suspicious activity | Good, identifies network anomalies and attacker behavior | Real-time network visibility, threat detection | Requires network access and expertise |
Wrap-Up
In conclusion, connecting the dots in a complex threat landscape requires a proactive and holistic approach. By understanding the interconnections between vulnerabilities, actors, and attack vectors, organizations can develop a robust security strategy. This involves a combination of threat intelligence analysis, proactive threat hunting, and a resilient security posture, adaptable to evolving threats. The journey towards a secure future hinges on our ability to see the full picture.
Key Questions Answered
What are some common indicators of interconnected threats?
Common indicators include unusual activity patterns, unusual data flow, and unusual access attempts across different systems or departments. Correlation and analysis of these signals across different security data points are key.
How can I improve my organization’s ability to detect and respond to interconnected threats?
Improving threat detection and response hinges on a robust threat intelligence program, a strong security information and event management (SIEM) system, and skilled personnel who can analyze the data to identify patterns and relationships.
What are some real-world examples of interconnected threats?
Supply chain attacks, where a weakness in one vendor’s security can compromise multiple downstream clients, and phishing campaigns that exploit multiple vulnerabilities within an organization are two examples. Financial fraud involving multiple entities is another real-world example.
What are the essential steps for developing a holistic security strategy for interconnected systems?
Developing a holistic security strategy requires defining clear security goals, establishing threat intelligence protocols, implementing strong security controls across the enterprise, and ensuring clear communication channels and collaborative processes between departments.