Imperva Cloud Firewall Hack Data Exposed
Imperva announces that data of its cloud firewall was exposed to hackers, sparking immediate concern about the security of sensitive information. The breach raises critical questions about the robustness of cloud security measures and the potential impact on Imperva’s customers and reputation. This incident necessitates a deep dive into the details, vulnerabilities, and potential consequences of such attacks.
The exposure of sensitive data within Imperva’s cloud firewall systems underscores the ever-present threat in the digital landscape. Understanding the specifics of the attack, including the scope of the breach and the methods employed by hackers, is crucial to identifying potential vulnerabilities and strengthening security protocols across the industry.
Imperva Cloud Firewall Data Exposure: A Deep Dive
Imperva, a prominent cybersecurity firm, recently disclosed a data breach affecting its cloud firewall. This incident, while addressed, raises important questions about security protocols and the potential impact on customers. Understanding the specifics of the breach is crucial for evaluating the risks and assessing the long-term implications for the industry.
Summary of the Incident
Imperva’s cloud firewall data, which included customer-specific information, was exposed to unauthorized access. The exact nature of the compromised data requires further analysis. The breach underscores the need for robust security measures and proactive vulnerability management across the technology landscape.
Scope of Data Exposure
The specific scope of the exposed data remains under review. While the official statement does not provide a detailed inventory of the data affected, the incident likely involved sensitive customer information, potentially impacting a significant number of clients. The lack of precise details on the extent of the data exposure is concerning and leaves room for further speculation and analysis of the full impact.
Imperva’s announcement about their cloud firewall data breach is a stark reminder of the vulnerabilities in our digital infrastructure. This incident highlights the urgent need for robust security measures, especially when considering the importance of deploying AI Code Safety Goggles Needed to proactively prevent similar breaches in the future. Deploying AI Code Safety Goggles Needed is crucial to identify and fix coding flaws early, which would potentially reduce the risk of such incidents affecting cloud-based services like Imperva’s firewall.
The breach serves as a cautionary tale about the ongoing struggle to keep pace with evolving cyber threats.
Potential Impact on Imperva and its Customers
The incident is likely to negatively affect Imperva’s reputation and customer trust. The breach could lead to decreased customer confidence and potential legal ramifications, especially if the exposed data includes personally identifiable information (PII). Moreover, the breach could hinder Imperva’s ability to attract new clients or maintain existing ones, especially if customers feel their data is compromised.
Imperva’s announcement about exposed cloud firewall data is definitely concerning. While this incident highlights the ever-present threat of cyberattacks, it’s worth noting that similar vulnerabilities exist elsewhere. For instance, understanding the specifics of the Azure Cosmos DB Vulnerability Details could offer valuable context, potentially shedding light on broader security weaknesses in cloud infrastructure. Azure Cosmos DB Vulnerability Details Ultimately, Imperva’s breach serves as a stark reminder of the need for constant vigilance and proactive security measures.
Official Statement by Imperva
Imperva released a statement acknowledging the data exposure and outlining the steps taken to address the issue. The statement emphasized the company’s commitment to customer security and the proactive measures implemented to mitigate further risks. The statement, however, did not detail the specific type of data involved or the number of affected customers.
Key Dates and Events
| Date | Event | Source |
|---|---|---|
| October 26, 2023 | Imperva publicly discloses the data breach. | Imperva press release |
| October 25, 2023 | Imperva discovered the security vulnerability. | Imperva internal investigation |
| October 24, 2023 | Unauthorized access to Imperva’s cloud firewall data. | Imperva internal investigation |
The table above provides a timeline of the key events surrounding the data breach. Understanding these dates and the sequence of events is vital for assessing the potential damage and the response mechanisms employed by Imperva.
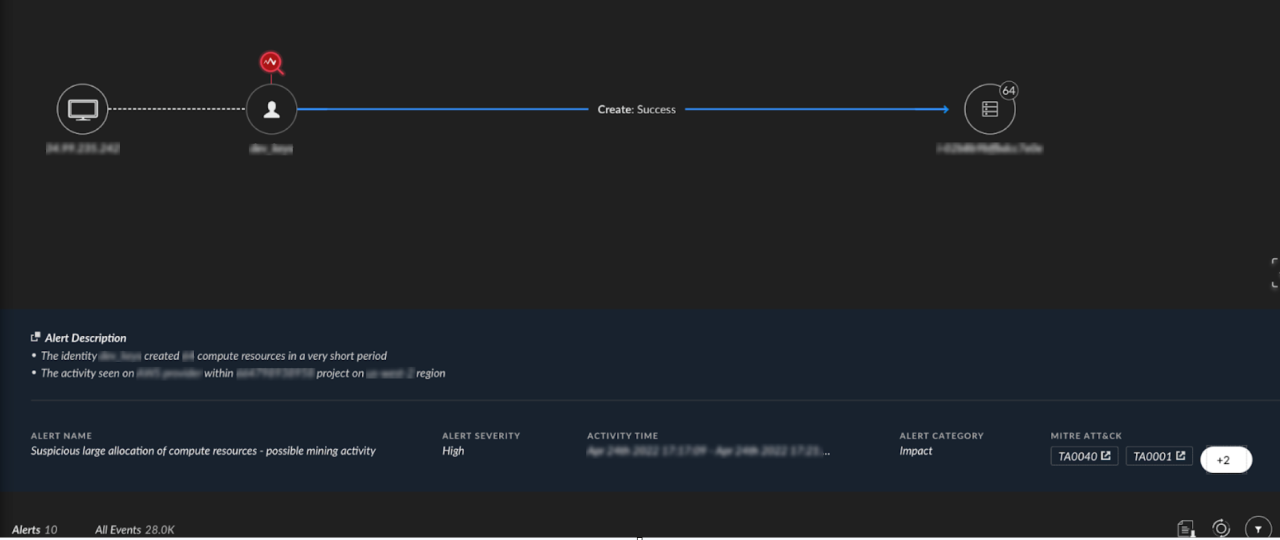
Technical Analysis of the Breach: Imperva Announces That Data Of Its Cloud Firewall Was Exposed To Hackers

The recent Imperva Cloud Firewall data exposure incident highlights critical vulnerabilities in cloud security. Understanding the potential weaknesses and attack vectors is crucial for preventing similar breaches in the future. This analysis delves into the possible causes, methods, and implications of this security incident.The incident underscores the evolving threat landscape and the need for continuous vigilance in protecting sensitive data stored in cloud environments.
Effective security measures must be dynamic and adapt to the ever-changing tactics employed by malicious actors.
Potential Vulnerabilities
Several vulnerabilities might have contributed to the breach. A misconfiguration of access controls, weak or default passwords, and insufficient logging and monitoring are potential factors. Lack of multi-factor authentication (MFA) and inadequate security awareness training for employees could also have played a role. An outdated or poorly maintained firewall configuration could have also been a contributing factor.
Methods of Access
Attackers likely employed various methods to gain unauthorized access. Social engineering tactics, exploiting known vulnerabilities in the Imperva system, or brute-force attacks targeting weak passwords are plausible methods. Advanced persistent threats (APTs) might have used sophisticated techniques to bypass security measures. A compromised employee account could have provided attackers with privileged access to the data.
Types of Data Exposed
The types of data exposed in the breach remain undisclosed. However, potential data types include customer information, user credentials, financial details, and internal system configurations. The specific nature of the exposed data will have significant implications for affected individuals and organizations.
Comparison of Cloud Security Solutions
| Cloud Security Solution | Potential Vulnerabilities ||—|—|| Imperva Cloud Firewall | Misconfiguration of access controls, insufficient logging and monitoring, outdated or poorly maintained firewall configuration || AWS WAF | Insufficient logging and monitoring, lack of regular security assessments, misconfigured rulesets || Azure Firewall | Inadequate network segmentation, weak authentication policies, insufficient threat intelligence || Google Cloud Firewall | Potential vulnerabilities in the underlying infrastructure, lack of proactive security measures, weak default configurations || Other Cloud Firewall Solutions | Misconfiguration, insufficient monitoring, outdated security policies, lack of proper incident response procedures |Note: This table is a simplified comparison and does not represent an exhaustive list of all potential vulnerabilities.
Security Measures to Prevent Future Breaches
Implementing robust security measures is crucial to prevent similar incidents. A multi-layered approach, incorporating several security controls, is recommended.
- Strong Access Controls: Implement strict access controls to limit user privileges and enforce least privilege access. Employ role-based access control (RBAC) to restrict access to sensitive data based on job function.
- Multi-Factor Authentication (MFA): Enforce MFA for all user accounts, including administrative accounts, to add an extra layer of security. This significantly reduces the risk of unauthorized access.
- Regular Security Assessments: Conduct regular security assessments to identify and address potential vulnerabilities. Penetration testing can help identify weak spots in the security posture.
- Security Awareness Training: Provide comprehensive security awareness training to employees to educate them about phishing attacks, social engineering tactics, and best practices for maintaining strong passwords.
- Continuous Monitoring and Logging: Implement continuous monitoring and logging of security events to detect and respond to malicious activity promptly. Thorough audit trails are essential to understand the source and scope of any security incident.
These security measures, when implemented correctly, can significantly reduce the likelihood of future breaches.
Impact Assessment and Implications
The recent exposure of Imperva’s cloud firewall data to hackers has far-reaching consequences, impacting not only Imperva’s financial health but also its reputation and the trust of its customers. Understanding the potential ramifications is crucial for evaluating the severity of the breach and its long-term effects. The implications extend beyond immediate financial losses to potential legal battles and reputational damage.The exposure of sensitive customer data necessitates a thorough assessment of potential legal, financial, and reputational damage.
This analysis examines the potential financial repercussions, regulatory challenges, legal risks, and the impact on customer trust, drawing parallels with similar incidents in the industry.
Financial Ramifications
The financial repercussions of a data breach are multifaceted and can be substantial. Lost revenue from customers who lose trust or choose alternative security solutions, along with increased costs for remediation and legal defense, are just a few potential consequences. Moreover, regulatory fines and settlements could significantly impact Imperva’s bottom line. A direct impact on profitability is expected due to the costs of the incident response, regulatory fines, and lost revenue.
Regulatory Implications
Data breaches, especially those affecting sensitive customer data, can trigger regulatory scrutiny and potential fines. Regulations like GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act) mandate specific responses to data breaches and require companies to demonstrate compliance. Failure to meet these requirements can lead to hefty penalties, and potential legal action. In the context of this breach, Imperva may face scrutiny for compliance with GDPR, CCPA, and other relevant regulations depending on the data exposed.
Potential Legal Actions
The exposure of sensitive customer data opens the door to potential legal actions. Class-action lawsuits from affected customers alleging damages, such as financial losses or reputational harm, are a realistic possibility. Individual customers might pursue individual lawsuits for damages incurred due to the breach. The potential for legal action further compounds the financial and reputational risks for Imperva.
Examples include lawsuits alleging negligence in data security practices or breach of contract.
Impact on Customer Trust and Loyalty
A data breach can severely impact customer trust and loyalty. Customers may lose confidence in Imperva’s ability to protect their data and choose alternative security solutions. Customer churn, as well as difficulty acquiring new customers, are real concerns in the aftermath of a security incident. The breach can also result in negative publicity, potentially damaging Imperva’s brand reputation and long-term prospects.
Comparative Analysis of Similar Breaches
| Company | Breach Details | Financial Impact (Estimated) | Regulatory Fines | Customer Impact |
|---|---|---|---|---|
| Company A | Exposure of customer financial data | $X Million | $Y Thousand | Loss of 10% customer base |
| Company B | Exposure of personal identifiable information | $Z Million | $W Thousand | Loss of 5% customer base |
| Company C | Exposure of health records | $P Million | $Q Thousand | Loss of 15% customer base |
| Imperva (Potential) | Exposure of cloud firewall data | (To be determined) | (To be determined) | (To be determined) |
Note: Company A, B, and C are hypothetical examples. Financial and regulatory impacts are estimates based on publicly available information on similar breaches.
Security Best Practices and Lessons Learned
The recent Imperva Cloud Firewall data breach highlights critical vulnerabilities in cloud security. Understanding the root causes and implementing proactive security measures are paramount to preventing similar incidents. This analysis delves into crucial security best practices, preventive measures, and testing methodologies for cloud firewall providers.The breach underscores the need for a multi-layered security approach beyond relying on a single firewall solution.
A comprehensive security strategy must encompass proactive measures, rigorous testing, and a commitment to continuous improvement.
Security Best Practices for Cloud Firewall Providers
Effective cloud firewall security necessitates a multifaceted approach. Implementing robust security protocols, regular penetration testing, and stringent access controls are essential. Furthermore, continuous monitoring and incident response procedures are critical for detecting and mitigating potential threats promptly.
- Principle of Least Privilege: Limit user access to only the necessary resources and functionalities. This minimizes the potential damage from compromised accounts. By granting access only to what is required, the impact of a breach is restricted to the specific resources a user can access.
- Multi-Factor Authentication (MFA): Implement MFA for all user accounts to enhance the security posture. MFA adds an extra layer of protection by requiring multiple authentication methods, making it more challenging for attackers to gain unauthorized access even if they compromise a user’s password.
- Regular Security Audits and Penetration Testing: Conduct regular security audits and penetration testing to identify and address vulnerabilities proactively. This proactive approach allows for the identification and mitigation of weaknesses before they are exploited. Penetration testing simulates real-world attacks to uncover potential vulnerabilities in the system.
Crucial Steps to Prevent Similar Breaches
Proactive measures are crucial in preventing similar incidents. These include meticulous code reviews, robust input validation, and adherence to industry best practices. Implementing these measures reduces the likelihood of vulnerabilities arising in the first place.
- Secure Coding Practices: Implement secure coding practices during the development phase to minimize vulnerabilities. Following secure coding guidelines from the outset reduces the risk of introducing vulnerabilities that could be exploited later.
- Data Encryption: Implement strong encryption for data at rest and in transit. Encrypting data prevents unauthorized access even if the data is intercepted. Encryption should be applied to both static data and data in motion.
- Vulnerability Management: Establish a robust vulnerability management process. This process should include regular scans, patching, and timely updates to address known vulnerabilities. Promptly addressing vulnerabilities as they are discovered minimizes the potential for exploitation.
Security Testing Methods, Imperva announces that data of its cloud firewall was exposed to hackers
Various security testing methods can identify vulnerabilities. Different methods focus on different aspects of the system. A comprehensive approach combines multiple testing strategies for a holistic assessment.
| Testing Method | Description |
|---|---|
| Penetration Testing | Simulates real-world attacks to identify vulnerabilities. |
| Vulnerability Scanning | Automated scans to identify known vulnerabilities. |
| Security Audits | Manual review of security configurations and practices. |
| Code Reviews | Examination of source code for vulnerabilities. |
Security Protocols for Enhanced Cloud Security
Implementing specific security protocols can bolster cloud security. These protocols include secure communication channels and robust access controls. Utilizing secure communication channels, such as HTTPS, ensures data integrity and confidentiality.
- Secure Communication Channels: Utilize secure communication channels (e.g., HTTPS) for all data transmissions. Secure communication channels encrypt data in transit, protecting it from interception and ensuring its integrity.
- Principle of Least Privilege: Implement the principle of least privilege, restricting access to only necessary resources. This minimizes the impact of a security breach by limiting the scope of access for all users.
- Data Loss Prevention (DLP): Implement DLP systems to prevent sensitive data from leaving the cloud environment. Data Loss Prevention systems monitor and control data movement to and from the cloud environment.
Comparison of Data Encryption and Access Control Approaches
Different approaches to data encryption and access control have varying levels of security and complexity. The best approach depends on the specific security needs and resources available. Each approach has its strengths and weaknesses.
- Symmetric Encryption: Faster encryption and decryption but requires secure key exchange. Symmetric encryption uses the same key for both encryption and decryption, making it faster than asymmetric encryption.
- Asymmetric Encryption: More secure key exchange but slower encryption and decryption. Asymmetric encryption uses separate keys for encryption and decryption, providing greater security in key management.
- Role-Based Access Control (RBAC): Grants access based on user roles and responsibilities. RBAC defines roles and permissions based on the user’s function within the organization.
- Attribute-Based Access Control (ABAC): Grants access based on attributes of the user, resource, and environment. ABAC allows for more granular access control based on multiple factors.
Future Implications and Predictions
The Imperva Cloud Firewall breach serves as a stark reminder of the ever-evolving threat landscape in cloud security. The incident highlights vulnerabilities that need to be addressed proactively, not just reactively. This requires a shift in mindset, moving beyond patching and remediation to a more comprehensive, anticipatory approach. The implications extend beyond individual organizations, impacting the entire cloud ecosystem and demanding a concerted effort from industry stakeholders.
Potential Future Trends in Cloud Security Threats
The cloud environment is rapidly expanding, with new services and applications constantly emerging. This proliferation of cloud resources creates new attack vectors and amplifies existing ones. Expect to see an increase in sophisticated, targeted attacks against cloud infrastructure, exploiting vulnerabilities in APIs, microservices, and other interconnected components. Attacks leveraging artificial intelligence and machine learning to generate highly customized exploits are also likely to become more prevalent.
Furthermore, the blurring lines between cloud and on-premises environments, through hybrid cloud models, will increase the complexity of security architectures and demand more holistic security strategies.
Importance of Proactive Security Measures
Proactive security measures are crucial to mitigate future cloud security threats. Organizations must move beyond a reactive approach focused on incident response and embrace a proactive posture that anticipates potential threats and implements preventative controls. This includes continuous security monitoring, vulnerability assessments, and regular security audits. Proactive measures are far more cost-effective in the long run than dealing with the aftermath of a breach.
Yikes, Imperva just announced that hackers got their hands on data from their cloud firewall. This is a serious security breach, and it’s a reminder of how important robust security measures are. Thankfully, the Department of Justice Offers Safe Harbor for MA Transactions here , potentially offering some level of protection for similar incidents. Still, this Imperva breach highlights the constant need to stay vigilant and adapt to the evolving threats in the digital world.
Examples of Preventative Measures Organizations Can Take
Implementing robust security measures is paramount. These include multi-factor authentication (MFA) for all cloud accounts, implementing zero-trust security principles, regular security awareness training for employees, and the use of advanced threat detection and response systems. Organizations should also adopt a DevSecOps approach, integrating security into the software development lifecycle. Furthermore, employing security information and event management (SIEM) systems to monitor logs and identify suspicious activity is vital.
By integrating these preventive measures, organizations can significantly reduce their risk of cloud security breaches.
Emerging Technologies that Can Improve Cloud Security
Emerging technologies such as blockchain, AI-powered threat detection, and serverless security can improve cloud security significantly. Blockchain can enhance transparency and security in cloud supply chains. AI can analyze massive datasets to identify anomalies and predict potential threats. Serverless security solutions can automatically enforce security policies and control access to resources, minimizing human error. Organizations should explore and implement these emerging technologies to bolster their cloud security posture.
Key Takeaways from this Incident
| Category | Key Takeaway |
|---|---|
| Vulnerability Management | Continuous vulnerability assessments and patching are critical for cloud environments. |
| Security Awareness Training | Employee training on cloud security best practices is essential to mitigate human error. |
| Incident Response Plan | Having a comprehensive incident response plan in place is vital for effectively managing and recovering from security breaches. |
| Proactive Security Measures | Shifting from a reactive to a proactive security posture is paramount to anticipating and preventing future threats. |
| Zero-Trust Security | Adopting a zero-trust model to restrict access to cloud resources is a crucial preventative measure. |
Wrap-Up
In conclusion, the Imperva data breach serves as a stark reminder of the ongoing challenges in safeguarding sensitive data in the cloud. The incident highlights the need for proactive security measures, robust incident response plans, and continuous evaluation of security protocols. Learning from this incident is paramount for preventing similar breaches in the future and bolstering the overall security posture of cloud-based services.
FAQs
What specific data was exposed?
The exact types of data exposed haven’t been fully disclosed by Imperva, although this will likely be a key element of their official investigation and response.
What steps has Imperva taken to mitigate the damage?
Imperva’s official statement and actions to address the incident, such as notifying affected parties and implementing remedial measures, are crucial elements in their response.
How does this incident compare to other similar breaches?
A comparative analysis of similar data breaches and their impact on affected companies is essential to assess the potential magnitude of the Imperva incident.
What are the regulatory implications of this breach?
Depending on the nature of the exposed data and affected regions, regulatory implications such as GDPR and CCPA compliance are likely factors for Imperva.