India Paytm Mall Data Breach Password Leaks
India Paytm Mall suffers data breach leaking passwords, raising serious concerns about online security and user data protection. This incident highlights the vulnerability of personal information in the digital age, and the potential consequences for both individuals and companies. The scale of the breach, the types of data compromised, and the potential impact on users will be explored in detail, along with an analysis of Paytm’s response and the broader cybersecurity implications.
The breach reportedly exposed sensitive user data, including potentially compromised passwords. This has sparked widespread anxieties among affected users, raising questions about the adequacy of security measures employed by Paytm Mall. The incident also prompts a critical examination of industry best practices and the need for stronger data protection measures.
Overview of the Paytm Mall Data Breach
The recent data breach at Paytm Mall has raised significant concerns about online security. This incident highlights the vulnerability of user data in the digital age and the critical need for robust security measures. It’s a reminder that even large and established companies are not immune to cyberattacks.The incident involved a compromise of user data, potentially exposing sensitive information like passwords and other personal details.
While Paytm has confirmed the breach and stated that it has been addressed, the full extent of the damage and the long-term consequences for users remain to be seen. Understanding the nature of the breach, its potential impact, and the methods used is crucial for both users and businesses to enhance their security posture.
Scope of the Breach
The reported scope of the Paytm Mall data breach includes a significant number of user accounts. While the exact figure is not publicly available, the magnitude of the breach underscores the need for companies to take proactive steps to protect user data. This kind of breach can lead to the compromise of financial details, which could expose users to fraudulent activities and financial losses.
Beyond financial impact, the breach can erode user trust and damage the company’s reputation.
Types of Data Compromised
The compromised data likely included user credentials, such as passwords and usernames. This also potentially extended to other sensitive information like addresses, contact details, and transaction histories. The specific types of data compromised, and the extent of their exposure, remain uncertain without detailed public reports. The potential for identity theft and fraudulent activity should be a significant concern.
Potential Impact on Users
The potential impact on Paytm Mall users is substantial and multifaceted. Financial loss due to unauthorized transactions is a real concern. Furthermore, the reputational damage to the company could negatively affect user trust and future business dealings. The possibility of identity theft is a serious concern, and users should take steps to protect themselves. For example, a similar incident at a major online retailer could result in a significant decline in user traffic and sales as customers lose confidence in the platform’s security.
Reported Methods of the Breach
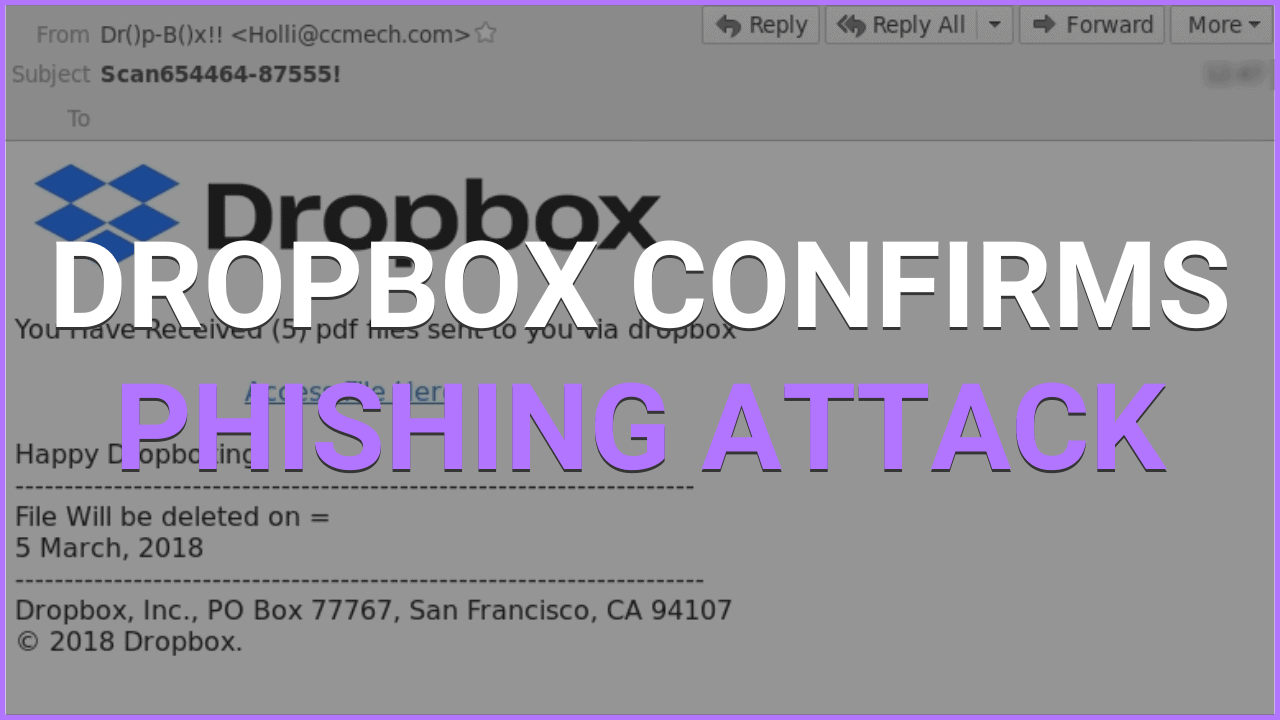
The exact methods used in the breach are not publicly available. However, common techniques used in data breaches often include exploiting vulnerabilities in software or systems, phishing attacks, or malware infections. It’s critical for companies to invest in robust security protocols and procedures to minimize the risk of future breaches.
Impact on Paytm
The recent data breach at Paytm Mall has the potential to inflict significant damage on the company, affecting its reputation, finances, and future operations. The leak of user passwords represents a serious security lapse, which could erode public trust and lead to significant customer churn.The scale of the impact will depend on several factors, including the number of compromised accounts, the extent of misuse, and Paytm’s response.
Ultimately, the consequences for Paytm will be far-reaching, and its handling of the situation will be crucial in determining its long-term health and success.
Reputation and Brand Image
The breach severely damages Paytm’s reputation for security and trustworthiness. A compromised user database creates a climate of distrust among customers, potentially leading to a decline in user confidence and adoption of the Paytm Mall platform. This negative perception could manifest in a loss of customer loyalty, reduced user engagement, and a decrease in new customer acquisition. Similar breaches in the past, such as the Equifax data breach, resulted in significant reputational damage and lasting negative impressions.
The long-term effects on Paytm’s brand image could be substantial and might take considerable time to repair.
Financial Repercussions
The financial consequences of a data breach like this are multifaceted. Lost revenue is a direct result of decreased customer trust and reduced usage. Customers may choose to avoid Paytm Mall or switch to competing platforms. Legal costs associated with investigations, potential lawsuits, and regulatory penalties are substantial and can cripple a company’s finances. The 2017 Capital One data breach, for instance, resulted in substantial financial losses, highlighting the potential severity of these costs.
The recent Paytm Mall data breach in India, exposing user passwords, highlights the urgent need for robust cybersecurity measures. While this incident is concerning, it’s worth noting that the Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ) is a positive step towards safeguarding sensitive information in certain legal contexts.
Ultimately, the Paytm breach serves as a harsh reminder of the critical importance of protecting personal data in the digital age.
Compensation demands from affected users also add to the financial burden.
Paytm’s Response to the Breach
The speed and effectiveness of Paytm’s response to the breach will significantly influence the overall impact. A swift and transparent response, including immediate notification to affected users, implementation of security enhancements, and proactive communication with regulatory bodies, can help mitigate the damage. Conversely, a slow or inadequate response will likely exacerbate the situation and prolong the negative consequences.
Unfortunately, specific details about Paytm’s response to the breach are currently unavailable. However, the company’s public statement on the matter, and the measures taken to secure user data, will be critical in determining how the situation unfolds.
Comparison with Other Breaches
| Company | Nature of Breach | Response Time | Public Communication | Security Enhancements |
|---|---|---|---|---|
| Paytm (Hypothetical) | Password Leak | (To be determined) | (To be determined) | (To be determined) |
| Equifax | Consumer Credit Data | Delayed | Unclear | Slow to implement effective solutions |
| Target | Retail Point of Sale Data | Delayed | Lackluster | Failed to adequately prevent future attacks |
This table presents a hypothetical comparison of Paytm’s potential handling of the breach versus the responses of other companies. The actual response from Paytm will need to be assessed against these examples to understand the extent of their impact on the company. It is important to note that every breach is unique, and responses must be tailored to the specific circumstances.
User Perspective

The Paytm Mall data breach has undoubtedly cast a shadow of anxiety and concern over millions of Indian users. The potential for fraudulent activities and the ensuing financial risks are understandably significant, prompting users to seek answers and solutions. Understanding the user’s perspective is crucial to assessing the full impact of this incident.The revelation of compromised passwords has understandably triggered a wave of apprehension amongst users.
This breach raises serious questions about the security measures implemented by Paytm Mall, and rightly so, prompting users to re-evaluate their online safety practices.
The recent Paytm Mall data breach in India, exposing user passwords, highlights the critical need for robust security measures. Similar vulnerabilities exist in cloud platforms like Microsoft Azure Cosmos DB, which, according to Azure Cosmos DB Vulnerability Details , are potentially susceptible to breaches. This underscores the ongoing struggle for secure online platforms, and the Paytm Mall incident serves as a harsh reminder of the risks involved.
User Concerns and Anxieties
Users are understandably concerned about the potential for identity theft, financial fraud, and unauthorized access to their personal information. The breach exposes a vulnerability that could lead to significant financial losses, including unauthorized transactions and the misuse of their sensitive data. This is not merely a theoretical concern; past data breaches have demonstrated the devastating real-world consequences of such vulnerabilities.
Potential Fraud Risks
The compromised data, including passwords, could be exploited for various fraudulent activities. Users risk unauthorized access to their Paytm Mall accounts, leading to the purchase of goods or services without their consent. This could also extend to unauthorized access to bank accounts linked to their Paytm accounts. Phishing scams and fraudulent websites impersonating Paytm Mall are also potential threats.
Steps to Mitigate Fraud Risks
Users should immediately take proactive steps to safeguard their accounts. This includes changing their Paytm Mall passwords to strong, unique combinations and enabling two-factor authentication. Regular monitoring of account activity is also essential, promptly reporting any suspicious transactions to Paytm. Crucially, users should exercise caution when clicking on links or downloading files from unknown sources, particularly those related to Paytm Mall.
User Demands for Compensation or Redress, India paytm mall suffers data breach leaking passwords
Users may demand compensation for the financial losses they may incur as a direct result of the breach. This could include reimbursement for unauthorized transactions or assistance with credit repair efforts. Furthermore, there may be demands for Paytm to take responsibility for the incident by implementing robust security measures and providing adequate redress to affected users.
Common User Reactions and Expectations
| User Reaction | User Expectation |
|---|---|
| Disappointment and frustration | Transparency and accountability from Paytm |
| Concern for personal safety | Stronger security measures from Paytm |
| Demand for action | Compensation for any financial losses |
| Fear of future incidents | Assurance of improved security protocols |
| Suspicion of fraudulent activity | Assistance in reporting and preventing fraud |
Cybersecurity Implications
The Paytm Mall data breach underscores critical vulnerabilities in the digital ecosystem, highlighting the urgent need for robust cybersecurity measures. The incident exposed a significant gap in security protocols, leading to a potential compromise of sensitive user data. This incident demands a deeper examination of the security posture of not just Paytm, but the broader e-commerce landscape in India and globally.
Vulnerabilities Exploited
The Paytm Mall breach likely involved multiple vulnerabilities. Commonly exploited weaknesses include weak or easily guessed passwords, outdated software, and insufficient multi-factor authentication. Unpatched security vulnerabilities in the Paytm Mall platform’s infrastructure and applications might have been exploited. Additionally, social engineering tactics could have played a role in gaining unauthorized access to user accounts.
Paytm’s Security Practices Compared to Industry Best Practices
A comparative analysis of Paytm’s security protocols against industry best practices reveals potential areas for improvement. Industry benchmarks emphasize regular security audits, penetration testing, and robust encryption protocols for sensitive data. Paytm’s adherence to these practices may need evaluation to ensure compliance with industry standards and prevent future breaches. Real-time threat monitoring and incident response plans are also critical components of a strong security posture.
Similar Data Breaches in E-commerce
Several e-commerce platforms globally have experienced data breaches. For instance, major retailers have faced compromises, leading to the leakage of customer data. These breaches highlight the recurring nature of vulnerabilities in e-commerce systems. The impact on consumer trust and brand reputation following such events is substantial. Understanding these past incidents provides crucial insights into common vulnerabilities and potential mitigation strategies.
Potential Long-Term Effects on Indian E-commerce
The Paytm Mall breach could have significant long-term consequences for the Indian e-commerce landscape. Consumer trust will likely be significantly impacted, potentially leading to a decrease in online transactions. Furthermore, increased regulatory scrutiny and stricter data protection laws may be introduced in response to this incident. Businesses may also face increased costs associated with implementing enhanced security measures.
The recent data breach at India’s Paytm Mall, exposing user passwords, highlights a critical need for better security practices. This incident underscores the urgent necessity for companies to adopt robust security measures, like those explored in articles on deploying AI code safety goggles to identify potential vulnerabilities. Deploying AI Code Safety Goggles Needed is crucial to prevent future breaches and protect user data.
Ultimately, Paytm Mall’s vulnerability serves as a stark reminder of the importance of proactive security measures in today’s digital landscape.
Ultimately, the industry will likely adapt and evolve to mitigate future risks and strengthen its security posture.
Legal and Regulatory Ramifications
The Paytm Mall data breach has serious implications beyond the immediate impact on user trust and financial security. A crucial aspect of this incident is the potential for legal and regulatory repercussions. India’s data protection landscape is evolving rapidly, and Paytm faces potential legal challenges from both affected users and regulatory bodies.
Relevant Data Protection Laws and Regulations in India
India has a growing framework of data protection laws. The Personal Data Protection Bill, 2019, is a significant step toward a comprehensive data protection regime. It Artikels principles for collecting, storing, and using personal data, including user rights like access, rectification, and erasure. While not yet enacted, the Bill’s provisions provide a framework for understanding the legal obligations surrounding data breaches.
Additionally, existing laws like the Information Technology Act, 2000, may also be invoked in cases of data breaches, particularly concerning the violation of user privacy.
Potential Legal Actions by Affected Users
Affected users, having suffered a significant breach of their personal data, might pursue various legal actions. These could range from class action lawsuits demanding compensation for financial losses, emotional distress, or reputational harm, to individual suits seeking specific remedies. The specific legal remedies available to users would depend on the specific details of the breach and the evidence presented.
Factors like the extent of the breach, the nature of the damages, and the evidence supporting the claims will influence the course of legal action.
Regulatory Scrutiny of Paytm
The data breach at Paytm is likely to attract scrutiny from regulatory bodies. The National Privacy Commission (NPC), the envisaged body under the Personal Data Protection Bill, 2019, is expected to have a significant role in investigating such breaches and enforcing the proposed legislation. The Information Technology Act, 2000, empowers the government to impose penalties on organizations for non-compliance, potentially leading to significant fines or other sanctions for Paytm.
The potential regulatory scrutiny would be based on the severity of the breach, the adequacy of Paytm’s security measures, and the company’s response to the incident.
Potential Legal Precedents from Similar Cases in Other Countries
| Country | Case Details | Key Legal Precedent |
|---|---|---|
| United States | Various data breaches, involving companies like Target and Equifax | Courts have established precedents for holding companies accountable for data breaches, potentially leading to significant monetary penalties and mandatory data security measures. |
| European Union | Breaches under the GDPR | The GDPR mandates strong data protection measures, allowing users to seek compensation and fines against companies that breach data protection regulations. |
| Canada | Breaches under the PIPEDA | Companies have been held accountable for breaches under the Personal Information Protection and Electronic Documents Act (PIPEDA), with penalties depending on the severity of the breach and the extent of damages to affected individuals. |
These examples from other countries highlight the increasing legal and regulatory pressure on organizations handling sensitive personal data. The precedents in other jurisdictions offer insights into potential outcomes in India.
Prevention and Mitigation Strategies: India Paytm Mall Suffers Data Breach Leaking Passwords

The Paytm Mall data breach serves as a stark reminder of the ever-present threat of cyberattacks in the digital age. While the immediate aftermath focuses on recovery and accountability, a crucial aspect remains: proactive measures to prevent future incidents. This necessitates a multi-faceted approach encompassing robust security protocols, user awareness, and a commitment to ongoing vigilance.
Strengthening Cybersecurity Protocols
Effective cybersecurity protocols are the cornerstone of a robust defense against data breaches. They encompass a range of technical and administrative controls designed to safeguard sensitive information. A critical element involves implementing multi-layered security measures that deter attackers at multiple points. These layers might include intrusion detection systems, firewalls, and encryption technologies.
- Implementing Multi-Factor Authentication (MFA): MFA adds an extra layer of security by requiring users to provide more than one form of verification to access accounts. This could involve a code sent to a mobile phone or a security token, making it significantly harder for unauthorized individuals to gain access, even if they obtain a password.
- Regular Security Audits and Penetration Testing: Regular assessments of security systems are vital to identify vulnerabilities before attackers exploit them. Penetration testing simulates real-world attacks to assess the effectiveness of existing defenses and uncover potential weaknesses.
- Data Encryption: Encrypting sensitive data, both in transit and at rest, is crucial to protect it from unauthorized access. This ensures that even if data is intercepted, it remains indecipherable without the proper decryption key.
Improving User Awareness
User education is paramount in mitigating the risk of data breaches. Users need to be aware of the potential threats and understand how to protect themselves. A well-informed user is the first line of defense against phishing scams and other malicious activities.
- Phishing Awareness Training: Educating users about phishing tactics is essential. Training should cover recognizing suspicious emails, links, and websites designed to trick users into revealing sensitive information.
- Strong Password Management: Creating and maintaining strong, unique passwords for each online account is critical. Avoid using easily guessed passwords and consider using a password manager to securely store and manage multiple passwords.
- Regular Software Updates: Keeping software and operating systems up-to-date is essential to patch security vulnerabilities. Out-of-date software is often a target for attackers due to known exploits.
Practical Tips for Personal Online Security
These practical tips can significantly enhance personal online security and reduce the risk of becoming a victim of a data breach.
- Avoid Public Wi-Fi: Using public Wi-Fi networks for sensitive activities like online banking is highly discouraged. These networks often lack the security measures necessary to protect your data from eavesdropping.
- Be Cautious of Downloads: Downloading files from untrusted sources is risky. Only download files from reputable sources and be wary of suspicious attachments or links.
- Monitor Account Activity: Regularly review your account activity for any unauthorized transactions or suspicious login attempts. Promptly report any anomalies to the respective platforms.
Future Trends
The Paytm Mall data breach serves as a stark reminder of the ever-evolving threat landscape in cybersecurity. As technology advances, so too do the methods and sophistication of cyberattacks. Understanding these future trends is crucial for organizations like Paytm to proactively fortify their defenses and protect user data.The digital world is becoming increasingly interconnected, creating new avenues for malicious actors to exploit vulnerabilities.
The rapid adoption of emerging technologies, coupled with the growing volume and complexity of data, exacerbates the challenges in safeguarding sensitive information. This necessitates a shift towards proactive and adaptive cybersecurity strategies.
Emerging Trends in Data Breaches
The methods used in data breaches are constantly evolving. Traditional methods like phishing and malware attacks remain prevalent, but new techniques like social engineering, leveraging artificial intelligence for automated attacks, and exploiting vulnerabilities in cloud environments are becoming more common. These new tactics require a broader understanding of potential threats beyond traditional security perimeters.
Evolving Landscape of Cybersecurity Threats
Cybersecurity threats are no longer confined to specific industries or geographies. The sophistication and frequency of attacks are increasing, and attackers are employing increasingly creative and targeted methods. This necessitates a proactive and adaptive approach to security that goes beyond traditional reactive measures.
Potential Impact of Artificial Intelligence on Cybersecurity
Artificial intelligence (AI) is revolutionizing many aspects of our lives, and cybersecurity is no exception. AI can be used to enhance security systems by automating threat detection, improving incident response, and even predicting potential attacks. However, AI also poses new risks, as attackers can leverage AI for automated attacks, making them more efficient and harder to detect. The use of AI in cybersecurity requires a careful balance between its benefits and potential risks.
This necessitates a thorough understanding of how AI can be both a tool for attackers and a tool for defenders.
Innovative Solutions to Combat Future Data Breaches
Several innovative solutions are being developed to address future data breaches. These include:
- Advanced threat detection and prevention systems: These systems leverage machine learning and AI to identify and respond to evolving threats in real-time. For example, systems can analyze network traffic patterns to identify anomalies that could indicate a malicious activity.
- Zero-trust security models: These models assume no implicit trust and verify every user and device attempting access to resources. This approach significantly reduces the attack surface and enhances security.
- Improved security awareness training: Regular training programs can equip users with the knowledge and skills to identify and report potential threats, such as phishing emails. Companies should emphasize the importance of recognizing and responding to sophisticated social engineering tactics.
- Enhanced data encryption and access controls: Implementing strong encryption protocols and robust access controls is critical in protecting sensitive data. Consider multi-factor authentication and regularly review access privileges.
Last Word
The Paytm Mall data breach underscores the urgent need for robust cybersecurity protocols in the digital age. The incident serves as a stark reminder of the risks associated with online transactions and the importance of safeguarding personal information. Users must take proactive steps to protect themselves, while companies like Paytm must prioritize enhanced security measures to prevent similar incidents in the future.
The long-term effects on the Indian e-commerce landscape remain to be seen, but the need for a strengthened cybersecurity infrastructure is undeniable.
Top FAQs
What steps can users take to mitigate fraud risks after a data breach?
Users should immediately change their passwords on all accounts associated with Paytm, monitor their financial statements closely for any unusual activity, and report any suspicious transactions to their respective banks. Users should also consider enabling two-factor authentication where available and be wary of phishing scams.
What are the potential legal actions affected users may take against Paytm?
Affected users may consider legal action against Paytm, potentially seeking compensation for financial losses, reputational damage, or other damages arising from the breach. The specific legal options and their likelihood of success will depend on the specifics of the breach and applicable Indian laws.
What are some common user reactions and expectations following a data breach like this?
Common user reactions include anxiety, distrust, and a desire for accountability. Users may expect prompt communication from Paytm, assurances about data security improvements, and potentially financial compensation or other redress.
What are the emerging trends in data breaches and cyberattacks?
Emerging trends in data breaches often involve sophisticated techniques, such as social engineering, ransomware, and the exploitation of vulnerabilities in software. The use of AI in both attack and defense is also a significant emerging trend.