XDR Cybersecurity Infrastructures Foundation
Is extended detection and response xdr the ultimate foundation of cybersecurity infrastructure – Is extended detection and response (XDR) the ultimate foundation of cybersecurity infrastructure? This exploration delves into the core components, advantages, and potential drawbacks of XDR as a foundational security strategy. We’ll examine how XDR integrates with existing security operations, automates tasks, and enhances threat detection across various network points. From its evolution and comparison to traditional methods like SIEM and SOAR, to its future trajectory and impact on security operations, we’ll cover the complete picture.
XDR systems offer a comprehensive approach to security by centralizing threat detection and response. This centralized view allows for a more holistic understanding of security events, improving incident response times and efficiency. By integrating with existing tools, XDR facilitates a more unified security posture, enabling organizations to effectively combat today’s sophisticated threats. This article will thoroughly examine the advantages and disadvantages of XDR as the cornerstone of a robust cybersecurity infrastructure.
Defining XDR
Extended Detection and Response (XDR) is a rapidly evolving security technology that promises a unified approach to threat detection and response across an organization’s entire security infrastructure. It integrates diverse security tools and data sources, enabling a more comprehensive view of security events and quicker, more effective incident response. Instead of relying on siloed solutions, XDR consolidates security data from various sources, providing a holistic view of threats.XDR systems leverage advanced analytics and machine learning to identify, prioritize, and investigate potential threats in real-time.
This capability differentiates XDR from traditional security solutions, which often require manual intervention for threat identification and response. The unification of data and automated responses are crucial characteristics that drive efficiency and effectiveness in today’s complex threat landscape.
Key Characteristics of XDR Systems
XDR systems are characterized by their ability to collect and analyze data from various security tools. This comprehensive data gathering provides a richer understanding of security events. They can correlate data across endpoints, networks, cloud environments, and applications to identify potential threats and vulnerabilities. XDR systems can automate many aspects of security operations, such as threat detection, investigation, and response, thereby reducing manual effort and increasing efficiency.
Crucially, they facilitate proactive threat hunting and prevention, allowing organizations to identify and mitigate potential risks before they escalate into full-blown incidents.
Functionalities of XDR Systems
XDR systems offer a broad range of functionalities to enhance security posture. These functionalities include threat detection and prevention, incident response, security information and event management (SIEM) capabilities, and automated threat hunting. This comprehensive approach enables a more holistic understanding of security events, allowing organizations to react more effectively to threats. XDR systems can also integrate with existing security tools and infrastructure, facilitating seamless integration and minimal disruption to existing operations.
Evolution of Security Solutions Leading to XDR
The evolution of security solutions from traditional, siloed tools to the unified XDR platform reflects the increasing complexity of modern threats. Early security solutions, like firewalls and antivirus software, focused on specific points of entry. Later, SIEM systems emerged to centralize log data from various sources. Security Orchestration, Automation, and Response (SOAR) platforms took this further by automating incident response tasks.
These tools, while improving security, often lacked the ability to correlate data from disparate sources and automate response across different security domains. The limitations of these traditional tools paved the way for XDR’s comprehensive approach to threat detection and response.
Comparison of XDR with Traditional Security Tools
| Feature | XDR | SIEM | SOAR |
|---|---|---|---|
| Data Source | Multiple (endpoints, network, cloud, applications) | Primarily logs from various sources | Data from SIEM, security tools |
| Data Analysis | Advanced analytics, machine learning | Statistical analysis, rule-based detection | Automation of incident response tasks |
| Threat Detection | Proactive, correlating data across multiple sources | Reactive, based on predefined rules | Assists in automating incident response workflows |
| Response Automation | Automated responses to threats | Requires manual response | Automates specific response tasks |
| Integration | Seamless integration with existing tools | Integration can be complex | Integrates with various security tools |
This table highlights the key differences between XDR and its predecessors, emphasizing the significant advancement in data aggregation, analysis, and response automation offered by XDR. XDR’s ability to correlate data from various sources and automate responses differentiates it from traditional security solutions.
XDR’s Role in Cybersecurity Infrastructure
Extended Detection and Response (XDR) is rapidly becoming a cornerstone of modern cybersecurity infrastructure. It moves beyond the limitations of siloed security tools, offering a unified platform for threat detection and response across the entire IT environment. This holistic approach promises improved visibility and faster reaction times, crucial for mitigating today’s sophisticated and multifaceted cyber threats.XDR is not simply another tool; it’s a fundamental shift in how organizations approach security.
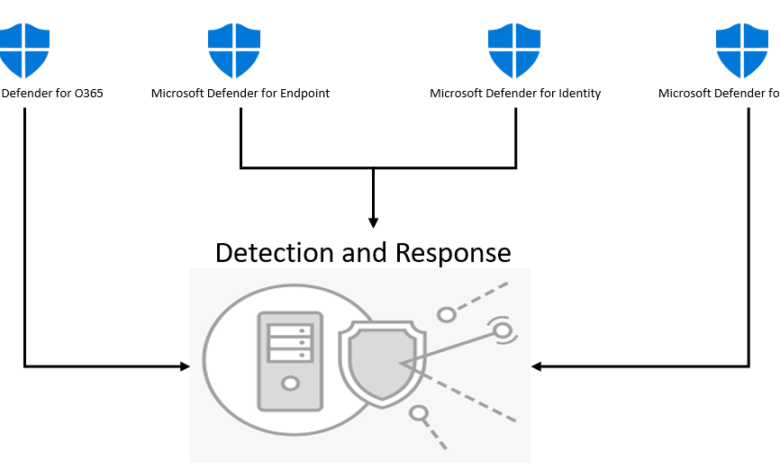
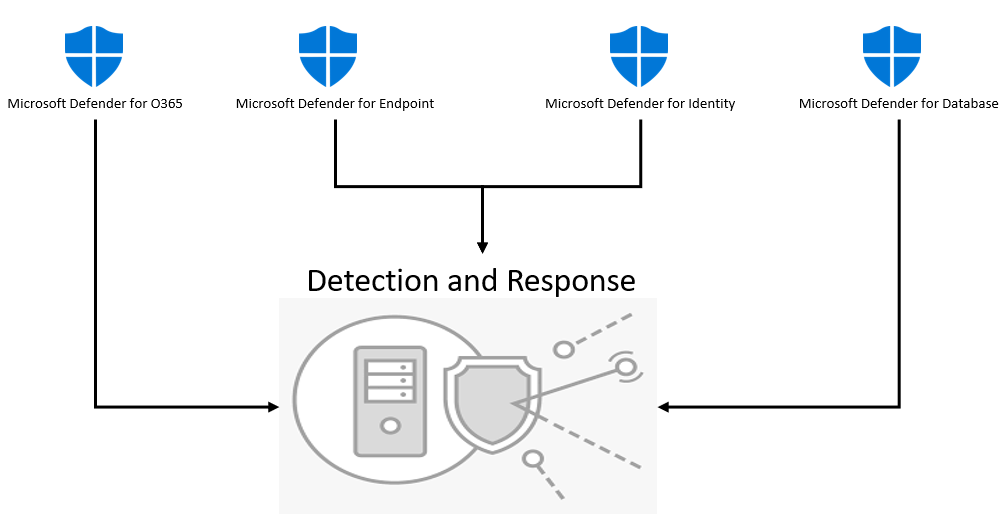
It integrates diverse security data streams, providing a consolidated view of threats. This unified view empowers security teams to make more informed decisions and implement more effective strategies. By combining data from various sources, XDR enables a comprehensive understanding of the attack surface, allowing for a more proactive and preventative security posture.
Core Components of a Comprehensive Cybersecurity Infrastructure
A robust cybersecurity infrastructure is built on several key components. These include robust endpoint security solutions, network security appliances, security information and event management (SIEM) systems, and cloud security controls. Each component plays a crucial role in securing different facets of the organization’s digital landscape. Furthermore, well-defined security policies, comprehensive incident response plans, and a culture of security awareness among employees are equally important.
These elements, when working together, form a layered defense against cyber threats.
How XDR Integrates into and Enhances the Infrastructure
XDR acts as a central nervous system for this infrastructure. It aggregates data from various sources—endpoints, networks, cloud environments, and applications—into a unified platform. This aggregation enables a holistic view of the threat landscape, offering a far more complete picture than any individual security tool can provide. The consolidated data facilitates correlation of seemingly disparate events, revealing patterns and indicators of compromise that might otherwise remain undetected.
This centralized approach drastically enhances the efficiency and effectiveness of security operations.
Potential Impact of XDR on Existing Security Operations
XDR significantly impacts existing security operations. The unified view of threats enables quicker threat identification and faster response times. This allows for more effective incident response, minimizing potential damage. Automation capabilities within XDR further reduce the workload on security teams, enabling them to focus on more strategic tasks and proactive threat hunting. In essence, XDR transforms security operations from reactive to proactive.
How XDR Facilitates Threat Detection Across Various Points in the Network
XDR employs advanced analytics to detect threats at various points in the network. This encompasses everything from suspicious user activity on endpoints to malicious traffic on the network. For example, XDR can detect unusual network behavior patterns that might indicate an intrusion. Similarly, XDR can identify malicious code execution on endpoints, enabling quick isolation and containment. This comprehensive approach allows for the detection and mitigation of threats across all stages of the attack lifecycle.
Stages of Threat Detection and Response with XDR’s Role
| Stage | Description | XDR’s Role |
|---|---|---|
| Threat Detection | Identifying potential security breaches and suspicious activities. | Collects and analyzes data from various sources, identifying anomalies and patterns that might indicate a threat. |
| Threat Analysis | Investigating the detected threats to understand their nature and impact. | Provides a consolidated view of the threat, enabling analysts to correlate events and understand the context of the activity. |
| Incident Response | Responding to a confirmed security incident, containing the threat, and recovering from the attack. | Facilitates automated response actions, isolating affected systems, and enabling the rapid containment of the threat. |
| Post-Incident Analysis | Analyzing the incident to improve future security posture. | Provides data insights to identify vulnerabilities and gaps in the security infrastructure, enabling the organization to learn from the incident. |
XDR as a Foundation
Extended Detection and Response (XDR) platforms are rapidly gaining traction as the cornerstone of modern cybersecurity infrastructures. Their comprehensive approach to threat detection and response, integrating disparate security tools into a unified platform, promises significant improvements in visibility and efficiency. However, the transition to an XDR-centric model isn’t without its complexities. This exploration delves into the advantages and disadvantages of XDR as a foundational security approach, considering implementation challenges and comparing it to other potential foundation models.XDR’s ability to consolidate security data from various sources provides a holistic view of threats.
This consolidated view allows for quicker threat identification, faster response times, and better incident management. However, this unified approach also presents certain limitations that must be carefully considered. The integration of disparate systems can introduce new vulnerabilities and complexity, potentially impacting the overall security posture if not carefully planned and executed.
Advantages of Using XDR as a Foundation
XDR platforms provide a centralized view of security events across the entire IT infrastructure. This single pane of glass allows for improved threat detection by correlating data from various security tools, enabling faster identification of anomalies and malicious activity. Enhanced threat hunting capabilities, driven by the centralized data, permit security teams to proactively identify and address emerging threats more effectively.
Furthermore, automated incident response workflows can be implemented within an XDR platform, enabling faster response times and reduced manual effort.
While XDR is a crucial component of modern cybersecurity, it’s not the sole solution. To truly fortify your infrastructure, you also need to address vulnerabilities at the code level. Think of deploying AI Code Safety Goggles Needed here as a crucial first step. Ultimately, a comprehensive approach, combining robust XDR with proactive code security, is the best way to build a truly impenetrable defense.
Disadvantages and Limitations of Solely Relying on XDR
While XDR offers significant advantages, relying solely on it can present some limitations. One significant drawback is the potential for data overload. The sheer volume of data generated by XDR platforms can be overwhelming, requiring sophisticated analytics and filtering capabilities to avoid drowning in irrelevant information. Another limitation is the inherent complexity of integrating diverse security tools and data sources into the XDR platform.
Careful planning, configuration, and ongoing maintenance are crucial to avoid creating new vulnerabilities or disrupting existing systems. Finally, a single point of failure exists if the XDR platform experiences issues, potentially crippling the organization’s security posture.
Challenges in Implementing XDR within Existing Infrastructure
Implementing XDR in an existing security infrastructure requires careful planning and execution. A critical challenge involves the integration of legacy systems, often requiring significant modifications or adaptations to ensure seamless data exchange. Another challenge is training security personnel on the new platform and its functionalities. Furthermore, migrating existing security data to the XDR platform may pose significant technical and logistical hurdles.
Finally, establishing effective security policies and procedures within the new XDR environment is critical to maximize its effectiveness.
Comparison of XDR with Other Potential Foundation Models
XDR is compared to other potential foundation models for cybersecurity, including Security Information and Event Management (SIEM) and a combination of point solutions. SIEM solutions primarily focus on log aggregation and correlation, lacking the advanced threat hunting and response capabilities of XDR. Using multiple point solutions can lead to fragmented visibility and response processes, making it difficult to correlate events across different systems.
XDR offers a unified approach that surpasses the limitations of these alternatives by combining the benefits of both SIEM and point solutions into one cohesive system.
Real-World Examples of Organizations Successfully Leveraging XDR
| Organization | Success Story |
|---|---|
| Financial Institution A | Improved threat detection and response by 30% due to enhanced visibility and automation capabilities. |
| Retailer B | Reduced average response time for security incidents by 25% using automated incident response workflows within the XDR platform. |
| Healthcare Provider C | Strengthened compliance posture by identifying and remediating vulnerabilities more quickly through enhanced threat hunting capabilities. |
XDR’s Impact on Security Operations
Extended Detection and Response (XDR) is revolutionizing security operations by automating tasks, accelerating incident response, and enhancing threat intelligence. This shift from reactive to proactive security posture is crucial in today’s complex threat landscape. XDR’s impact extends beyond just automating tasks; it fundamentally alters how organizations approach security, empowering them to respond more effectively and efficiently to threats.XDR platforms provide a unified view of security data across various sources, enabling analysts to identify and respond to threats more quickly and decisively.
This comprehensive approach reduces the time and resources needed to investigate and remediate incidents. The result is a strengthened security posture and a more agile approach to defending against ever-evolving cyber threats.
XDR’s Automation of Security Operations Tasks
XDR platforms automate many routine security operations tasks, freeing up security analysts to focus on more complex and strategic activities. This automation significantly improves efficiency and reduces the risk of human error. Specific tasks often automated include log aggregation, threat detection, and security alert prioritization. This allows security teams to address critical issues promptly and effectively. The automated analysis of vast amounts of security data significantly reduces the workload on analysts, enabling them to dedicate their time to high-level tasks.
Impact of XDR on Incident Response Time and Efficiency
XDR significantly shortens incident response time and increases efficiency. By correlating events from various sources, XDR platforms provide a more complete picture of an incident, enabling faster identification and containment. This faster response can minimize the impact of a security breach, reducing potential financial losses and reputational damage. XDR’s automated incident response capabilities are crucial for organizations of all sizes to efficiently manage and resolve security incidents, minimizing downtime and disruption.
XDR’s Enhancement of Threat Intelligence and Hunting Capabilities
XDR platforms enhance threat intelligence and hunting capabilities by providing a comprehensive view of security data. This comprehensive view allows security teams to identify emerging threats, patterns, and anomalies more effectively. XDR enables proactive threat hunting by identifying potential threats before they can cause significant damage. These capabilities allow security teams to be more proactive in identifying and mitigating threats, leading to a stronger security posture.
XDR’s Integration with Other Security Tools for a Holistic Approach
XDR’s integration with other security tools is a key factor in achieving a holistic security approach. This integration provides a unified view of security data across different tools, which is essential for effective threat detection and response. By integrating with existing SIEMs, firewalls, and endpoint detection and response (EDR) tools, XDR creates a cohesive security infrastructure. This integrated approach allows for more comprehensive threat detection, enabling security teams to react more swiftly and effectively.
Security Incident Response Workflow Leveraging XDR
| Step | Description | XDR Role |
|---|---|---|
| 1. Detection | Security tools detect a potential threat. | Aggregates data from various sources, identifies anomalies, and generates alerts. |
| 2. Alert Triage | Security analysts prioritize and assess alerts. | Provides structured, contextualized information, automating some triage steps. |
| 3. Investigation | Analysts investigate the root cause of the incident. | Provides detailed timeline view of events, correlating events across multiple systems. |
| 4. Containment | Implementing controls to isolate the threat. | Facilitates quick identification of affected systems and provides automated containment strategies. |
| 5. Remediation | Fixing vulnerabilities and restoring systems. | Provides insights into the source of the vulnerability and provides automated remediation recommendations. |
| 6. Post-Incident Analysis | Evaluating the incident and improving security posture. | Provides detailed reports, identifying patterns and potential improvements in detection and response. |
Future of XDR and Cybersecurity
The future of XDR is inextricably linked to the evolving landscape of cybersecurity threats. As threat actors become more sophisticated, XDR solutions must adapt and evolve to maintain their effectiveness. This involves not just expanding functionality but also integrating with emerging technologies to provide a more comprehensive security posture. The future of XDR is not just about reacting to attacks; it’s about proactively anticipating and mitigating them.XDR is poised to become the central nervous system of modern cybersecurity infrastructures.
While Extended Detection and Response (XDR) is a crucial component of modern cybersecurity, the recent Azure Cosmos DB Vulnerability Details highlight the importance of proactive security measures. Understanding vulnerabilities like those detailed in Azure Cosmos DB Vulnerability Details underscores how XDR systems can help identify and mitigate these issues, ultimately bolstering the overall security infrastructure. In the end, robust XDR remains a critical foundation for any comprehensive cybersecurity strategy.
This transformation is driven by the increasing complexity of attacks and the need for a unified view of security events. By providing a comprehensive, real-time picture of the entire security landscape, XDR empowers organizations to respond to threats more quickly and effectively, thus minimizing damage and downtime.
While XDR is undeniably a crucial component of modern cybersecurity, it’s not the sole foundation. Recent developments, like the Department of Justice Offers Safe Harbor for MA Transactions ( Department of Justice Offers Safe Harbor for MA Transactions ), highlight the need for a holistic approach. Robust security hinges on a layered defense, including strong policies, regular audits, and proactive threat intelligence.
Ultimately, XDR is a powerful tool, but not a magic bullet. A comprehensive strategy is still the best approach to ensuring comprehensive security.
Predicting Future XDR Trajectories
XDR is likely to transition from a reactive tool to a proactive security platform. This involves the use of advanced analytics and machine learning to predict potential threats before they materialize. By analyzing historical data, current trends, and even the patterns of seemingly benign activity, XDR will become more adept at identifying and classifying potential threats, minimizing the risk of vulnerabilities.
This shift will involve integrating more threat intelligence feeds and leveraging the power of AI for predictive analysis. A recent example of this is the development of XDR solutions capable of anticipating and mitigating zero-day exploits by identifying anomalous activity indicative of such attacks.
Emerging Trends and Advancements in XDR
Several emerging trends will significantly impact the future of XDR. These include:
- AI-Powered Threat Detection and Response: AI and machine learning algorithms will play an increasingly crucial role in identifying and responding to threats. This will enable XDR solutions to analyze massive volumes of security data, identify patterns indicative of malicious activity, and automatically respond to emerging threats.
- Enhanced Threat Intelligence Integration: XDR solutions will incorporate real-time threat intelligence feeds from various sources, including industry research, open-source intelligence, and threat feeds from reputable vendors. This real-time integration of threat intelligence will significantly improve threat detection and response capabilities.
- Zero Trust Security Integration: XDR will be integrated with zero-trust security architectures. This will ensure that only authorized users and devices can access critical resources, even within the organization’s network, mitigating the risk of insider threats and unauthorized access.
Impact of AI and Machine Learning on XDR, Is extended detection and response xdr the ultimate foundation of cybersecurity infrastructure
AI and machine learning will dramatically impact XDR’s ability to detect and respond to threats. These technologies will enable XDR to analyze vast quantities of security data, identify complex patterns, and automate responses. This will lead to faster incident response, improved threat detection accuracy, and a more proactive security posture. For example, AI-powered anomaly detection can identify unusual user behavior, unusual network activity, and suspicious file activity that could indicate a potential breach.
Evolution of XDR to Address Future Security Threats
The evolution of XDR will be crucial in countering emerging threats. Future XDR solutions will need to address new attack vectors, including cloud-based attacks, attacks on IoT devices, and the increasing use of sophisticated malware. This will necessitate the development of more advanced threat detection techniques, more robust threat intelligence integrations, and a greater focus on automated responses.
The development of XDR solutions that can adapt to these evolving threats is paramount for maintaining an effective security posture.
Key Features and Functionalities of Future XDR Solutions
The following table Artikels the key features and functionalities expected in future XDR solutions:
| Feature | Functionality |
|---|---|
| Advanced Threat Detection | Leveraging AI/ML to identify complex threats, zero-day exploits, and sophisticated malware. |
| Proactive Threat Prevention | Using predictive analytics to anticipate and mitigate threats before they occur. |
| Automated Response | Automating incident response procedures, minimizing human intervention in routine situations. |
| Real-Time Threat Intelligence | Integrating real-time threat intelligence feeds for comprehensive threat awareness. |
| Zero Trust Integration | Integrating with zero-trust security architectures for enhanced access control. |
| Multi-Cloud Support | Providing comprehensive security coverage across various cloud environments. |
Illustrative Case Studies: Is Extended Detection And Response Xdr The Ultimate Foundation Of Cybersecurity Infrastructure
XDR systems are not just theoretical constructs; they are actively deployed and proven effective in real-world scenarios. Understanding how they respond to and prevent incidents is crucial for appreciating their value. This section will explore hypothetical and real-world examples, highlighting the strengths of XDR in cybersecurity.
Hypothetical Cybersecurity Incident
A mid-sized financial institution experiences a sophisticated phishing campaign targeting senior executives. Attackers successfully gain initial access through a compromised employee email account. They then move laterally through the network, exploiting vulnerabilities in outdated software. The attack escalates to data exfiltration attempts. Without robust detection mechanisms, the breach could go undetected for days, allowing attackers to exfiltrate sensitive customer data.
XDR System Response
An XDR system, integrated with various security tools, would immediately detect anomalies in user behavior, like unusual login attempts and suspicious email activity. Real-time threat intelligence feeds would correlate these events with known phishing campaigns, raising red flags. The system would automatically block suspicious IP addresses and potentially contain the spread of malware. The ability to correlate events across multiple data sources (email logs, endpoint activity, network traffic) is critical.
The granular visibility offered by XDR allows for rapid identification of the compromised account, the lateral movement paths, and the attempts to exfiltrate data. This proactive response limits the damage.
Real-World XDR Case Study
A healthcare organization experienced a ransomware attack targeting patient data. An XDR system, integrated with their existing security infrastructure, detected suspicious network activity. The system immediately blocked the malicious actors’ attempts to encrypt files, quarantining the affected endpoints. Threat intelligence feeds quickly identified the ransomware strain, enabling the organization to deploy the correct decryption tools and mitigating the damage to sensitive patient records.
Lessons Learned
The healthcare example highlights the importance of proactive detection and response capabilities. XDR systems, by combining various data sources, can offer an unprecedented level of visibility. This visibility translates to quicker identification of threats, containment of damage, and ultimately, faster recovery. Organizations need to proactively integrate XDR into their security infrastructure and invest in continuous training and incident response planning to fully leverage its capabilities.
XDR Security Incident Response Workflow
- Detection: The XDR system identifies anomalous activity, like suspicious network traffic patterns, unusual user behavior, or malware infections. The system correlates these events with threat intelligence to determine the likelihood of a malicious attack.
- Analysis: Detailed analysis of the detected activity occurs. The system investigates the scope and impact of the incident, identifying compromised endpoints, data exfiltration attempts, and lateral movement patterns. This is crucial for determining the extent of the attack.
- Containment: Measures are immediately implemented to contain the incident. This may include isolating compromised systems, blocking malicious IP addresses, or implementing security controls to prevent further escalation. This limits the impact of the attack.
- Eradication: Active measures are taken to remove the malicious threat. This could involve removing malware from infected systems, restoring compromised data, and remediating vulnerabilities that attackers exploited. The focus here is on completely removing the threat.
- Recovery: The organization ensures business continuity. This includes restoring systems and data to their pre-incident state, ensuring compliance with regulations, and implementing preventative measures to prevent future attacks. This is the critical phase of getting back to normal operations.
End of Discussion
In conclusion, while XDR presents a compelling case as the foundation of modern cybersecurity infrastructure, it’s not a one-size-fits-all solution. Its advantages in automation, threat detection, and incident response are undeniable, but organizations must carefully weigh the potential disadvantages and implementation challenges before adopting it. A strategic approach that considers existing infrastructure, resources, and expertise is crucial. The future of XDR is promising, with continuous advancements likely to further enhance its capabilities.
However, organizations should remain adaptable, leveraging XDR alongside other technologies, to best defend against evolving threats.
Common Queries
Is XDR suitable for all organizations?
No, the suitability of XDR depends on factors like budget, existing infrastructure, and security expertise. Smaller organizations might find a more streamlined, focused solution more appropriate. A thorough assessment is needed to determine if XDR aligns with an organization’s specific needs.
What are the key challenges in implementing XDR?
Implementing XDR can be challenging due to the need for integration with existing systems, the potential for data silos, and the requirement for skilled personnel. Proper planning, resource allocation, and ongoing training are essential.
How does XDR improve threat intelligence?
XDR enhances threat intelligence by collecting and correlating data from various sources across the network. This allows for more comprehensive threat detection and quicker identification of patterns, enabling proactive responses.
What are the long-term implications of using XDR?
The long-term implications of XDR include a more efficient and automated security operations center, improved incident response times, and a more proactive approach to threat hunting. This leads to a stronger overall security posture.