Criminals Spy on You Connected Home Devices
Internet connected household electronics are helping criminals spy on you. From smart thermostats to security cameras, our homes are increasingly filled with internet-connected devices. While these gadgets offer convenience and automation, they also create new vulnerabilities, potentially opening doors for criminals to gather information and engage in surveillance. This exploration delves into the rise of these connected devices, their potential for misuse, the methods employed, and the impact on individuals and society.
We’ll also examine security measures and protective strategies.
The ease with which criminals can potentially access and utilize data from these devices is a serious concern. This information can be used to build detailed profiles of individuals, potentially leading to financial exploitation, emotional distress, and even physical harm. Understanding the risks and taking proactive steps to safeguard yourself is paramount.
The Rise of Connected Devices in Homes
The modern home is increasingly becoming a hub of interconnected devices, blurring the lines between our physical environment and the digital world. From simple timers to complex automation systems, these devices are transforming how we live, work, and interact with our homes. This evolution has been driven by advancements in technology, decreasing costs, and the growing demand for convenience and control.The increasing connectivity of household electronics reflects a broader trend towards the Internet of Things (IoT).
This trend connects everyday objects to the internet, enabling them to communicate and exchange data. This constant communication allows for a range of functionalities, from remote control to predictive maintenance, ultimately aiming to improve our daily routines and overall quality of life.
Historical Overview of Connectivity
Early examples of connected devices in homes include programmable thermostats and security systems. These early systems offered limited remote control and monitoring capabilities, paving the way for more advanced functionalities. The development of wireless communication technologies, such as Wi-Fi and Bluetooth, significantly expanded the potential for interconnectivity, leading to a surge in the number of smart home devices.
Types of Connected Household Electronics
A wide array of devices are now integrated into homes. Smart appliances, such as refrigerators, ovens, and washing machines, offer features like scheduling, remote monitoring, and even integration with other smart home systems. Smart lighting systems, security cameras, and door locks enable remote control and monitoring, enhancing security and convenience. These systems represent a significant leap forward from the basic functionalities of previous generations of appliances.
Evolution of Home Automation Systems
Home automation systems have evolved from simple, standalone devices to complex, interconnected platforms. These platforms use software and hardware to control and manage various aspects of the home, from lighting and temperature to security and entertainment. The increasing integration of cloud services has enabled users to access and control their home systems from anywhere in the world. This has significantly enhanced the ability to automate and manage a home remotely.
Sophistication of Connected Devices
Connected devices are becoming increasingly sophisticated, with advanced features like voice control, machine learning, and predictive maintenance. Voice assistants like Amazon Alexa and Google Assistant allow users to control various aspects of their home using voice commands, offering a hands-free and intuitive experience. Some smart appliances now use machine learning to optimize their performance and predict maintenance needs, potentially saving users time and money.
Comparison of Connected Devices
| Device Category | Features | Functionalities |
|---|---|---|
| Smart Appliances | Scheduling, remote monitoring, integration with other smart home systems | Controlling and managing appliances from a distance, optimizing energy consumption, predictive maintenance |
| Smart Lighting | Remote control, customizable lighting schedules, voice control | Creating ambiance, enhancing security, energy saving |
| Security Systems | Remote monitoring, motion detection, integration with other smart home systems | Enhanced security, peace of mind, remote access and control |
| Smart Thermostats | Programmable schedules, remote control, energy efficiency optimization | Maintaining comfortable temperatures, reducing energy consumption, automated temperature adjustments |
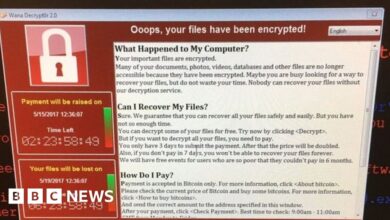
Potential for Criminal Surveillance
The proliferation of internet-connected devices in our homes presents a significant security risk. These devices, often lacking robust security measures, can be exploited by malicious actors to gain unauthorized access to sensitive personal data. This vulnerability extends beyond simple intrusions; it allows criminals to create detailed profiles of individuals, potentially leading to targeted harassment, fraud, or even physical harm.The inherent vulnerabilities in these connected devices create opportunities for criminal exploitation.
Weak passwords, outdated software, and insecure network configurations are common entry points. Criminals can leverage these weaknesses to gain access to the device and its associated network, potentially gaining control over the entire system. This access allows them to monitor activity, record data, and potentially control devices remotely. The potential for misuse is substantial.
Security Vulnerabilities in Connected Devices
Many connected devices, from smart thermostats to security cameras, rely on readily available and accessible internet connections. Unfortunately, these connections often lack adequate security measures. These vulnerabilities include default passwords that remain unchanged, insufficient or outdated encryption protocols, and poor authentication processes. These factors leave the devices susceptible to unauthorized access and manipulation.
Methods of Criminal Exploitation
Criminals employ various methods to exploit vulnerabilities in connected devices. They may use brute-force attacks to guess passwords, exploit known software vulnerabilities to gain unauthorized access, or even socially engineer users into revealing sensitive information. Phishing attempts targeting users, especially those connected to the device, are also a significant concern. In some cases, criminals may even attempt to gain physical access to the device to directly manipulate its settings.
Methods of Data Acquisition
Gaining access to a connected device often allows criminals to capture a wide range of data. This includes the device’s logs, internal communications, and user interactions. They might also utilize the device’s microphone and camera for audio and video recording. Malicious software (malware) installed on the device can further enhance their capabilities. By monitoring data streams, criminals can reconstruct events, track movements, and potentially intercept sensitive communications.
Types of Data Collected by Criminals
| Data Type | Description |
|---|---|
| Location Data | GPS coordinates, Wi-Fi access points, Bluetooth signals |
| Audio Recordings | Conversations, ambient sounds, and interactions |
| Video Recordings | Visual recordings from cameras |
| Device Activity Logs | Usage patterns, browsing history, and application activity |
| Personal Information | Usernames, passwords, addresses, and other identifiable details |
| Financial Information | Transactions, payment details, and banking information |
Creating Profiles of Individuals
Criminals can use the collected data to create detailed profiles of individuals. This process involves analyzing patterns in their behavior, interactions, and locations. By piecing together seemingly innocuous information, criminals can paint a comprehensive picture of a person’s life, potentially revealing their routines, preferences, and vulnerabilities. This profile can then be used to target the individual for various malicious activities.
For example, a criminal might use location data to know when a person is home alone, allowing them to target a home for robbery. Similarly, information about the user’s habits and routine can be used for fraud.
Methods of Surveillance
The proliferation of internet-connected devices in our homes has created a complex web of potential vulnerabilities. While these devices offer convenience and connectivity, they also present opportunities for malicious actors to collect and exploit personal data. This section explores the various methods criminals could utilize to conduct surveillance through these devices.Criminals can leverage the inherent functionalities of connected devices to gain unauthorized access to sensitive information.
Audio recording capabilities, often present in smart speakers and security systems, can be manipulated to record conversations and gather private details. Video cameras in smart home devices can potentially be used to record activities without the user’s knowledge, creating a continuous record of their lives. Location data, another critical element, can be exploited to track movements and patterns.
Understanding these methods is crucial to recognizing the risks and implementing necessary safeguards.
Audio Recording Exploitation
Smart speakers and other audio-enabled devices, designed for convenience, can become tools for covert surveillance. Criminals can potentially exploit vulnerabilities in these systems to activate recording features remotely, even without user interaction. Sophisticated techniques could involve manipulating the device’s software or exploiting weak authentication protocols to gain control. For example, a compromised smart speaker could record conversations in a home without the occupants’ awareness, potentially gathering information about daily routines, financial matters, or even sensitive conversations.
Furthermore, sophisticated audio processing could be used to extract specific information from recordings.
Video Camera Surveillance
Video cameras, increasingly prevalent in smart home security systems and other connected devices, can be used to record and transmit footage without the user’s knowledge. Criminals could exploit vulnerabilities to access these cameras, potentially gaining access to real-time video feeds of the interior of a home. This allows for monitoring of occupants’ activities, movements, and interactions, creating a comprehensive picture of daily life.
For instance, a compromised security camera could provide a criminal with a constant visual feed of a home, allowing them to monitor for valuable items, assess routines, and even identify potential targets for other crimes.
Location Data Exploitation
Connected devices often collect location data, which can be crucial for many functionalities, including location-based services and home automation. Criminals could exploit these data streams to track movements and create detailed profiles of an individual’s activities. For example, data from a smart thermostat or a fitness tracker could be used to determine the user’s routine, habits, and even their approximate location at any given time.
Combining location data with other information from connected devices could create a comprehensive and potentially harmful picture of an individual’s lifestyle.
Data Transmission and Storage Methods
The methods used for transmitting and storing data from connected devices are varied and can be exploited by criminals. Criminals might intercept data transmissions between the devices and the network, or they might gain unauthorized access to storage servers holding the data. For example, poorly secured Wi-Fi networks can be exploited to intercept data being sent from a smart home device to a cloud server.
Furthermore, weaknesses in data encryption can expose data during transmission or storage, potentially enabling criminals to access sensitive information.
Technical Aspects of Surveillance Methods
| Surveillance Method | Data Transmission | Data Storage | Technical Vulnerability |
|---|---|---|---|
| Audio Recording | Wi-Fi, Bluetooth, or Cellular | Cloud servers, local storage | Weak authentication, software vulnerabilities, compromised devices |
| Video Camera | Wi-Fi, Cloud Servers | Cloud servers, local storage | Vulnerable network configurations, insecure access points, software flaws |
| Location Data | Cellular, Wi-Fi, GPS | Cloud servers, local devices | Lack of encryption, data breaches, GPS spoofing |
The Impact of Criminal Activity

The rise of connected devices in our homes, while offering convenience, also presents a significant vulnerability to criminal activity. Knowing that your personal space might be under surveillance, even unknowingly, can have profound effects on your well-being, daily routines, and finances. The implications extend beyond the individual, affecting societal trust and potentially leading to a climate of fear and paranoia.The potential for criminal surveillance through connected devices is a serious concern, and its impact on individuals and society is multifaceted.
The psychological, financial, and social ramifications are substantial and deserve careful consideration. Understanding these impacts is crucial for developing effective preventative measures and fostering a more secure digital environment.
Psychological Impact
Awareness or suspicion of surveillance can create a significant psychological toll on individuals. Constant vigilance and anxiety about being observed can lead to feelings of isolation, distrust, and paranoia. This can manifest in various ways, including difficulty sleeping, increased stress levels, and a decline in overall mental well-being. In extreme cases, it can even lead to severe anxiety disorders.
Ever wondered how those smart appliances might be more than just helpful? Turns out, internet-connected household electronics are becoming surprisingly effective tools for criminals to potentially spy on us. This raises serious questions about security. That’s why deploying AI code safety goggles, like those discussed in Deploying AI Code Safety Goggles Needed , is crucial for creating more secure code in the digital world.
Ultimately, this means we need to be extra cautious about what devices we connect to the internet and what information they might be collecting. Protecting ourselves from these potential risks is a key concern for anyone using these technologies.
Victims might experience feelings of violation and loss of control over their private lives.
Impact on Daily Life
Criminal surveillance can drastically alter daily routines. Individuals might become hesitant to engage in normal activities, such as conversations with friends, or even using certain devices or apps, limiting their social interactions. They might avoid certain locations or modify their daily schedules to reduce the risk of being observed. For example, a person might stop using a smart speaker or avoid having online video calls if they suspect their home is being monitored.
Their trust in others, and even their own senses, can be compromised.
Financial Implications
The financial implications of criminal surveillance can be substantial. Victims may face significant costs associated with taking preventative measures, such as upgrading security systems, replacing compromised devices, or hiring cybersecurity experts. There could be additional costs associated with legal actions if the surveillance is illegal. Furthermore, the emotional distress caused by such surveillance can lead to lost productivity and reduced income.
The potential for reputational damage and loss of business opportunities is also a serious concern.
Social Implications
Widespread criminal surveillance can erode trust within communities. People may become reluctant to interact with others, fearing that their conversations or activities are being monitored. This can lead to social isolation and a decline in community spirit. The perceived threat of surveillance can also lead to increased distrust in government and law enforcement, potentially exacerbating social tensions.
It can also affect public trust in technology, leading to a reluctance to adopt new connected devices.
Consequences of Criminal Surveillance
| Aspect of Life | Potential Consequences |
|---|---|
| Psychological Well-being | Increased anxiety, stress, paranoia, distrust, social isolation |
| Daily Routines | Hesitancy to engage in normal activities, altered schedules, reduced social interaction |
| Financial Impact | Increased security costs, legal fees, lost productivity, reputational damage |
| Social Relations | Erosion of trust, social isolation, increased distrust in institutions |
| Overall Security | Decreased public safety, exacerbation of social tensions |
Security Measures and Countermeasures

The rise of internet-connected devices in our homes has undeniably increased our convenience, but it has also introduced a new vulnerability: potential criminal surveillance. Understanding and implementing robust security measures is crucial to mitigating this risk. This section will explore practical strategies for protecting yourself and your connected devices from malicious actors.Protecting your home network and its connected devices requires a multi-faceted approach.
Simply purchasing the latest security software is not enough. A proactive, layered defense, incorporating both technical and behavioral safeguards, is essential.
Technical Aspects of Protecting Connected Devices
Ensuring the security of your connected devices starts with choosing devices with strong security features. Look for devices with robust encryption protocols, like WPA3 for Wi-Fi, to protect your data in transit. Update your devices’ firmware regularly as these updates often include critical security patches.Device manufacturers play a crucial role in this. They must prioritize security throughout the design and development process.
Implementing robust default passwords and encryption methods from the outset can significantly reduce vulnerabilities. Open-source devices, when properly maintained, can also offer greater security options.
Security Protocols and Their Effectiveness
Various security protocols offer varying levels of protection. For instance, WPA3 Wi-Fi security protocols provide enhanced protection compared to older protocols like WPA2. Secure protocols for your internet connection are also crucial. Using a strong, unique password for your Wi-Fi network is a fundamental step in securing your home network from unauthorized access.
Device Manufacturer and Government Agency Roles
Device manufacturers bear a significant responsibility in ensuring the security of their products. They should actively work to address security vulnerabilities, releasing timely updates and patches. Government agencies also play a critical role in setting security standards and enforcing compliance, thereby contributing to a safer digital environment.
It’s unsettling how easily criminals can tap into our lives through internet-connected appliances. While the Department of Justice Offers Safe Harbor for MA Transactions here addresses some legal vulnerabilities, the reality remains that these seemingly innocuous devices can be used for nefarious purposes. This means that the potential for criminals to spy on us through these devices is still a serious concern.
Recommended Security Practices for Internet-Connected Household Electronics
| Device Category | Recommended Security Practices |
|---|---|
| Smart Home Hubs | Change default passwords, enable two-factor authentication where available, and regularly update firmware. |
| Smart TVs | Use strong passwords, disable remote access if not needed, and keep the device’s software up-to-date. |
| Smart Speakers | Change default passwords, limit the device’s access to sensitive information, and use strong encryption for voice communication. |
| Smart Lighting | Change default passwords, limit the device’s access to sensitive information, and use strong encryption for voice communication. |
| Smart Appliances | Use strong passwords, limit the device’s access to sensitive information, and keep the device’s software up-to-date. |
Illustrative Case Studies
The rise of smart home devices has brought unprecedented convenience, but it also presents new vulnerabilities. Understanding how these devices could be exploited is crucial for safeguarding our homes and personal information. This section explores hypothetical and real-world scenarios to illustrate the potential for criminal surveillance.The potential for criminal surveillance through smart home devices is real and requires proactive measures to mitigate the risk.
This section details hypothetical scenarios, demonstrating how attackers could leverage vulnerabilities in these devices, highlighting the importance of security awareness and robust security practices.
Hypothetical Case Study
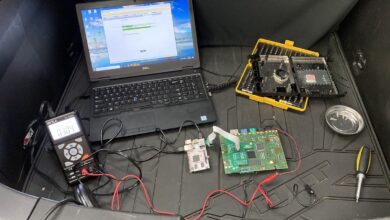
A family, the Smiths, installed a smart home system, including a connected thermostat, a smart lighting system, and a security camera. The system connected seamlessly to their home network, allowing remote control and monitoring. Unbeknownst to the Smiths, a malicious actor targeted their thermostat. The attacker exploited a known vulnerability in the thermostat’s firmware to gain remote access.
Once inside, they monitored the Smiths’ daily routines, meticulously recording temperature patterns, lighting schedules, and even the movements captured by the security camera. This allowed the attacker to understand the Smiths’ habits and schedule, potentially enabling further criminal activities.
Surveillance Methodology
The attacker leveraged a vulnerability in the thermostat’s firmware, allowing remote access and control. They used publicly available exploits and tools to gain access to the thermostat’s internal systems. This allowed them to collect data on the Smiths’ activities, without their knowledge.
Detection and Mitigation
The Smiths noticed unusual temperature fluctuations and inconsistent lighting patterns. Suspecting a problem, they consulted a cybersecurity professional who analyzed their network logs. The professional identified unauthorized access attempts on the thermostat, confirming the attack. The professional then recommended updating the thermostat’s firmware to the latest version, implementing a strong password for the device, and disconnecting the thermostat from the network.
Real-World Examples
Several incidents highlight the potential for malicious actors to leverage vulnerabilities in smart home devices. While specific details are often not publicly disclosed to protect victims, the common thread is the exploitation of vulnerabilities in connected devices. A recent report revealed an increase in the number of smart home devices targeted in attacks, emphasizing the need for increased security awareness and protection measures.
Common Elements in Real-World Incidents
| Element | Description |
|---|---|
| Vulnerable Device | Outdated firmware, weak passwords, or known vulnerabilities in the device’s software. |
| Attack Vector | Exploiting vulnerabilities through network connections, Wi-Fi, or other communication channels. |
| Data Collection | Monitoring routines, activities, and other sensitive information from the device. |
| Impact | Potential for theft, fraud, harassment, or other malicious activities. |
Illustrative Images of Vulnerable Devices
The proliferation of smart home devices has undeniably enhanced convenience, but it has also introduced new avenues for malicious actors. These interconnected gadgets, while seemingly harmless, often expose vulnerabilities that can be exploited for surveillance or other nefarious purposes. Understanding the design flaws and functionalities that make these devices susceptible to attack is crucial for mitigating risks and ensuring the safety of our homes.
Smart Security Cameras
Smart security cameras, often marketed for their convenience and remote accessibility, can be significant vectors for criminal surveillance. Their reliance on open Wi-Fi networks and cloud storage for video streaming makes them particularly vulnerable. Remote access features, designed for monitoring from anywhere, can be easily exploited by unauthorized individuals if not properly secured. The ability to remotely control camera functions like zoom and pan, combined with poor encryption protocols, can give attackers access to live feeds and even the ability to manipulate the device’s functionality for covert observation.
Smart TVs, Internet connected household electronics are helping criminals spy on you
Smart TVs, with their web browsing capabilities and integrated apps, provide a potential avenue for unauthorized access to personal data and activities. Their connectivity often involves weak encryption protocols, making them susceptible to attacks that compromise user data or provide access to the device’s functionalities. The ability to stream content from the internet can make them targets for malware injections, which can be used to capture keystrokes or record screen activity.
The device’s design often features numerous input points and connections, increasing the potential entry points for malicious code.
It’s unsettling how easily criminals can tap into our lives through internet-connected household devices. This vulnerability extends beyond our smart fridges and thermostats, however. Security flaws in systems like Microsoft Azure Cosmos DB, as detailed in Azure Cosmos DB Vulnerability Details , highlight the potential for data breaches in seemingly unrelated areas. This underscores the importance of maintaining strong security protocols on all our connected devices to prevent criminals from eavesdropping and gaining access to our private information.
Smart Refrigerators
Smart refrigerators, while seemingly innocuous, can be susceptible to various security breaches. Their connection to home networks and potential access to internal data, including user preferences and shopping habits, make them potential targets for surveillance. Design flaws, such as poorly secured APIs or inadequate authentication protocols, can lead to unauthorized access and data exfiltration. Their ability to store and access sensitive information, coupled with a lack of robust security measures, poses significant risks.
Smart Lighting Systems
Smart lighting systems, designed for energy efficiency and automated control, can be vulnerable to attacks that allow for manipulation of lighting patterns and schedules. The centralized control system and reliance on internet connectivity can be exploited by malicious actors. This ability to remotely control lighting can potentially be used for various nefarious purposes, such as surveillance or even psychological manipulation.
The device’s design, often focusing on simplicity and ease of use, can inadvertently compromise security.
Common Vulnerabilities Across Devices
| Device Category | Common Vulnerability | Example of Exploitation |
|---|---|---|
| Smart Security Cameras | Weak encryption, remote access, lack of authentication | Unauthorized access to live feeds, manipulation of camera functions |
| Smart TVs | Weak encryption, web browsing vulnerabilities, app security flaws | Malware injection, data capture, unauthorized access to personal information |
| Smart Refrigerators | Poorly secured APIs, inadequate authentication, lack of robust security | Unauthorized access to user preferences, data exfiltration |
| Smart Lighting Systems | Centralized control system, reliance on internet connectivity, lack of security measures | Manipulation of lighting patterns, surveillance, psychological manipulation |
Last Recap

In conclusion, the increasing connectivity of household electronics presents a real threat of criminal surveillance. While the convenience and automation offered by these devices are undeniable, the potential for misuse is significant. Individuals need to be aware of the risks, take necessary precautions, and advocate for stronger security measures from manufacturers and governing bodies. By understanding the methods of surveillance and implementing proactive security measures, we can mitigate the risks and ensure a safer digital environment for everyone.
User Queries: Internet Connected Household Electronics Are Helping Criminals Spy On You
What are some common types of internet-connected household electronics?
Smart thermostats, security cameras, smart speakers, smart lighting systems, and appliances like smart refrigerators and washing machines are just a few examples.
How can criminals potentially exploit the vulnerabilities in these devices?
Criminals can exploit vulnerabilities in the devices’ software, weak passwords, or lack of robust security protocols to gain unauthorized access.
What are some basic security measures I can take to protect myself?
Strong passwords, enabling two-factor authentication, regularly updating device software, and using a strong router password are good starting points. Consider using a Virtual Private Network (VPN) to encrypt your internet connection.
What role do device manufacturers play in preventing criminal activity?
Manufacturers have a responsibility to design and implement robust security measures into their products. Regular security updates and proactive responses to known vulnerabilities are crucial.