Interview with Dr. Arun Vishwanath Latest Cyberattacks
Interview with dr arun vishwanath on the latest cybersecurity attacks – Interview with Dr. Arun Vishwanath on the latest cybersecurity attacks dives deep into the rapidly evolving threat landscape. This insightful conversation explores everything from the motivations behind recent attacks to the critical impact on individuals, businesses, and even national infrastructure. Dr. Vishwanath shares his expert perspective on emerging trends, vulnerabilities, and, most importantly, how we can better protect ourselves from these threats in the future.
The interview covers a wide range of topics, from the common attack vectors like ransomware and phishing to the more sophisticated supply chain attacks. We’ll examine the potential damage, explore mitigation strategies, and gain valuable insights into Dr. Vishwanath’s predictions for future threats. Get ready to understand the ever-changing face of cybersecurity!
Introduction to Cybersecurity Attacks
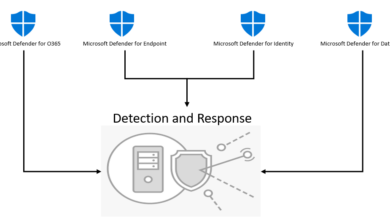
The cybersecurity landscape is constantly evolving, with new threats emerging and existing ones adapting. Recent years have witnessed a dramatic increase in sophisticated attacks targeting individuals, businesses, and critical infrastructure. These attacks exploit vulnerabilities in software, hardware, and human behavior, highlighting the need for robust defenses and proactive security measures. Dr. Vishwanath’s interview likely focuses on the growing sophistication and impact of these attacks, covering their various forms and potential consequences.The attacks discussed in the interview likely encompass a range of tactics, including ransomware, phishing, and supply chain attacks.
These methods exploit different weaknesses, from the vulnerabilities of software to the human tendency to trust. The consequences of these attacks can be devastating, impacting financial stability, reputation, and even public safety. The interview will likely delve into the specifics of these attacks, their methodologies, and how they can be mitigated.
Overview of the Current Cybersecurity Landscape
The current cybersecurity landscape is characterized by a complex interplay of evolving threats, vulnerabilities, and attack vectors. Attacks are becoming more sophisticated, often leveraging multiple techniques in coordinated campaigns. Sophistication is apparent in the targeted nature of attacks, often focusing on specific individuals, businesses, or critical infrastructure. Increased automation and the growth of the internet of things (IoT) introduce new attack surfaces.
Types of Cybersecurity Attacks
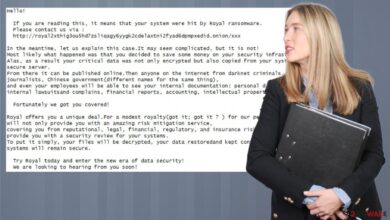
Dr. Vishwanath’s interview likely examines specific types of attacks, including ransomware, phishing, and supply chain attacks. Ransomware encrypts data, demanding payment for its release. Phishing deceives individuals into revealing sensitive information. Supply chain attacks compromise systems by targeting vulnerable components in the supply chain.
Potential Impact of Cybersecurity Attacks
The impact of these attacks can be severe across various sectors. Individuals may experience financial loss, identity theft, and emotional distress. Businesses face disruption, reputational damage, and financial losses. Critical infrastructure, such as power grids and healthcare systems, could experience widespread disruptions with potentially catastrophic consequences. Real-world examples of such attacks underscore the critical need for robust security measures.
Comparison of Attack Vectors
| Attack Vector | Method | Impact | Mitigation Strategies |
|---|---|---|---|
| Malware | Malicious software designed to damage, disrupt, or gain unauthorized access. | Data breaches, system compromise, financial loss. | Strong antivirus software, regular software updates, secure configurations. |
| Social Engineering | Manipulating individuals into revealing sensitive information or performing actions that compromise security. | Data breaches, unauthorized access, financial loss. | Security awareness training, robust authentication mechanisms, strong password policies. |
| Zero-Day Exploits | Exploits vulnerabilities in software that are unknown to the developers and security community. | Critical system compromise, widespread data breaches, significant financial losses. | Proactive vulnerability management, threat intelligence, and advanced threat detection systems. |
The table above illustrates the diverse nature of attack vectors and their potential consequences. Effective security strategies require a multi-faceted approach that addresses all possible avenues of attack.
Dr. Arun Vishwanath’s interview on the latest cyberattacks was fascinating, highlighting the ever-evolving threat landscape. A particularly worrying aspect discussed was a recent vulnerability in Azure Cosmos DB, as detailed in Azure Cosmos DB Vulnerability Details. This underscores the critical need for proactive security measures in cloud environments, a point Dr. Vishwanath further emphasized in the interview.
Dr. Vishwanath’s Perspective on Recent Cybersecurity Attacks
Dr. Arun Vishwanath, a leading expert in cybersecurity, offers valuable insights into the motivations and tactics behind recent attacks. His analysis delves into the evolving threat landscape, highlighting emerging vulnerabilities and the critical importance of proactive security measures. His perspective provides a crucial framework for understanding the current cyber threat environment and fortifying defenses.Dr. Vishwanath emphasizes that the motivations behind these attacks are multifaceted.
Financial gain remains a primary driver, with ransomware attacks targeting businesses and individuals for extortion. However, the motivations extend beyond financial incentives. Ideological motivations, political agendas, and even simple acts of vandalism are also factors in the current threat landscape. This demonstrates the importance of a comprehensive security strategy that considers diverse motivations.
Motivations Behind Recent Attacks
Dr. Vishwanath underscores the increasing sophistication and diversity of attacker motivations. While financial gain remains a prominent driver, political motivations and even personal vendettas are increasingly influencing cyberattacks. This shift demands a broader security strategy, moving beyond purely technical solutions to include understanding the socio-political context surrounding attacks.
Evolving Attack Tactics
Attackers are continually refining their tactics to exploit vulnerabilities in software and systems. Dr. Vishwanath notes a significant trend toward the use of automated tools and techniques for reconnaissance and attack delivery. This automation allows for faster and more widespread attacks, demanding a focus on proactive threat intelligence and incident response capabilities.
Vulnerabilities Identified in Recent Attacks
Dr. Vishwanath’s analysis identifies several recurring vulnerabilities across recent attacks. These include vulnerabilities in outdated software, inadequate patching procedures, and the increasing reliance on remote work environments. These factors have created significant attack surfaces, leaving organizations vulnerable to exploitation. A critical finding is the exploitation of weak or reused passwords, which often goes undetected for extended periods.
Dr. Arun Vishwanath’s interview on the latest cybersecurity attacks was fascinating, highlighting the evolving threat landscape. Interestingly, the recent Department of Justice Offers Safe Harbor for MA Transactions policy seems to address some of the vulnerabilities discussed. This all makes me wonder how these legal frameworks will impact the future of cybersecurity strategies.
This highlights the importance of strong password policies, multi-factor authentication, and regular security awareness training.
Common Attack Stages
Dr. Vishwanath emphasizes the importance of understanding the typical stages involved in a cyberattack. This knowledge enables proactive defense strategies by allowing organizations to identify potential threats earlier in the attack cycle.
| Attack Stage | Description | Example |
|---|---|---|
| Reconnaissance | Gathering information about the target system and network. | Scanning ports, probing for vulnerabilities. |
| Vulnerability Exploitation | Identifying and exploiting known or unknown weaknesses. | Exploiting a known SQL injection vulnerability. |
| Privilege Escalation | Gaining elevated access beyond the initial access point. | Using a compromised account to gain administrator rights. |
| Lateral Movement | Moving across the network to gain access to other systems. | Using compromised systems to access other systems on the network. |
| Data Exfiltration | Stealing sensitive data from the compromised system. | Downloading confidential files or databases. |
| Command and Control | Maintaining control over the compromised system. | Issuing commands and instructions to the compromised system. |
Impact and Consequences
Cybersecurity attacks are no longer isolated incidents; they represent a multifaceted threat with far-reaching consequences. The financial, reputational, operational, and even psychological toll can be devastating, impacting individuals, businesses, and entire nations. Understanding the diverse impact of these attacks is crucial for developing effective mitigation strategies.
Financial and Reputational Damage
Cyberattacks inflict significant financial losses through direct costs like ransom payments, recovery expenses, and lost productivity. The reputational damage, often lasting for years, can erode trust and customer loyalty, leading to substantial revenue loss. Consider the case of major retail breaches, where compromised customer data can lead to significant financial losses due to fraud and legal action. Furthermore, the reputational damage from a data breach can affect a company’s stock price and market valuation.
Operational Disruptions
Attacks can disrupt critical operations, halting production, affecting supply chains, and causing widespread service disruptions. For instance, a ransomware attack on a hospital could delay critical medical procedures, impacting patient care. Similarly, attacks on financial institutions can lead to transaction delays, impacting customers and the broader financial system. Operational downtime can have severe consequences for businesses and essential services.
Legal Ramifications
Legal implications are substantial, including potential lawsuits, regulatory fines, and criminal investigations. Data breaches often trigger legal action from affected individuals and regulatory bodies. The legal consequences can vary significantly depending on the jurisdiction and the specific regulations in place. For example, failure to comply with data privacy regulations like GDPR can lead to significant penalties.
Psychological and Social Impact
The victims of cybersecurity attacks often experience significant psychological distress, including anxiety, fear, and a sense of vulnerability. The emotional toll can be significant, especially when sensitive personal information is compromised. Large-scale attacks can have broader social impacts, eroding public trust in institutions and creating a sense of insecurity. For instance, the impact of a breach of a major social media platform could result in user mistrust and a decline in engagement.
Dr. Arun Vishwanath’s recent interview highlighted the escalating threat of cybersecurity attacks. Protecting against these evolving dangers requires a proactive approach, like implementing AI-powered code safety tools, as discussed in Deploying AI Code Safety Goggles Needed. This proactive approach is crucial to building more resilient systems against the ever-changing landscape of cyber threats, echoing the themes discussed in the interview.
Mitigation Strategies
A proactive approach to cybersecurity is essential. Implementing robust security measures and fostering a culture of security awareness can help mitigate risks. The following table Artikels key mitigation strategies discussed in the interview.
| Mitigation Strategy | Description |
|---|---|
| Strong Passwords and Multi-Factor Authentication (MFA) | Enhancing password complexity and implementing MFA can significantly reduce the risk of unauthorized access. |
| Regular Security Audits and Vulnerability Assessments | Identifying and addressing potential vulnerabilities is crucial. Proactive assessments can prevent attacks before they occur. |
| Employee Training and Awareness Programs | Educating employees about phishing scams, social engineering tactics, and other security threats is vital. |
| Incident Response Plan | Developing a comprehensive incident response plan ensures that organizations are prepared to handle and mitigate the effects of a cyberattack. |
| Data Encryption and Backup Systems | Protecting sensitive data through encryption and maintaining robust backup systems can limit the impact of a successful attack. |
Cybersecurity Defense Strategies
Strengthening cybersecurity defenses is not a passive exercise; it’s a dynamic process requiring constant adaptation and proactive measures. Dr. Vishwanath emphasizes the critical need to move beyond reactive measures and embrace a culture of security that anticipates and mitigates threats. This proactive approach, coupled with a robust incident response plan, is crucial in today’s complex threat landscape.
Proactive Security Measures
Proactive security measures are fundamental to a robust cybersecurity posture. They involve anticipating potential threats and implementing preventative measures before an attack occurs. This includes continuous monitoring of systems and networks, regular vulnerability assessments, and the implementation of strong security protocols. Companies must proactively address vulnerabilities before attackers exploit them. A crucial aspect is the use of advanced threat intelligence to stay ahead of emerging threats.
- Regular Security Audits: These audits help identify weaknesses in systems and applications, allowing for timely remediation. For example, a recent audit at a major financial institution uncovered a vulnerability in their payment processing system, allowing for a patch to be implemented before a potential breach.
- Employee Training and Awareness: Human error is a significant factor in many security breaches. Thorough employee training on phishing scams, social engineering tactics, and safe password practices is essential. This includes simulated phishing exercises to reinforce awareness and knowledge. For instance, a company found that its employees were frequently clicking on malicious links in phishing emails after a training program, showing a significant improvement in security awareness.
- Multi-Factor Authentication (MFA): Implementing MFA adds an extra layer of security, making it significantly harder for attackers to gain unauthorized access. MFA is now a standard best practice in most organizations.
Human Factors in Cybersecurity
Human error often plays a significant role in cybersecurity breaches. A crucial component of any defense strategy is recognizing the human element and proactively addressing vulnerabilities in human behavior. This involves educating employees about security threats, fostering a security-conscious culture, and implementing processes to mitigate risks related to human error.
- Security Awareness Programs: A strong security culture is built through consistent training and communication. Regular awareness programs can help employees recognize and avoid potential threats. For instance, a company that regularly holds security awareness training sessions saw a decrease in phishing attempts and data breaches. This reinforces the importance of regular and interactive training for employees.
- Incident Reporting Procedures: Establish clear guidelines on how employees should report suspected security incidents. Encouraging employees to report suspicious activities is crucial to detect and respond to threats early. An organization that implemented a robust incident reporting system quickly identified and contained a malware infection that could have resulted in a major data breach.
Incident Response Best Practices
A well-defined incident response plan is essential for managing and mitigating the impact of security incidents. This plan should Artikel procedures for detection, containment, eradication, recovery, and post-incident analysis. This helps organizations minimize damage and maintain business continuity.
| Phase | Best Practices |
|---|---|
| Detection | Implement intrusion detection systems, security information and event management (SIEM) tools, and establish a system for monitoring logs. |
| Containment | Isolate the affected systems or network segments to prevent further spread of the incident. |
| Eradication | Identify and remove the root cause of the incident. |
| Recovery | Restore affected systems and data to their previous operational state. |
| Post-Incident Analysis | Review the incident response process and identify areas for improvement. Analyze the incident to understand how it occurred and prevent future occurrences. |
Future Trends and Predictions
The landscape of cybersecurity is constantly evolving, driven by the rapid advancement of technology and the ingenuity of attackers. Predicting the future is inherently challenging, but by analyzing current trends, we can identify potential vulnerabilities and develop proactive strategies to mitigate risk. Dr. Vishwanath’s insights offer a valuable perspective on the emerging threats and technologies shaping the future of cybersecurity.
Emerging Attack Vectors and Vulnerabilities
The digital ecosystem is expanding, encompassing a wider array of interconnected devices and systems. This interconnectedness, while beneficial, also presents new attack surfaces. Exploiting vulnerabilities in IoT devices, cloud infrastructure, and software supply chains are key areas of concern. Sophisticated attacks leveraging artificial intelligence (AI) and machine learning (ML) are also expected to become more prevalent. For instance, AI-powered phishing campaigns can be highly personalized and targeted, making them harder to detect.
The rise of ransomware-as-a-service further democratizes malicious attacks, allowing less skilled actors to launch devastating campaigns.
Future of Cybersecurity Technology
The future of cybersecurity technology relies heavily on proactive measures and advanced tools. Artificial intelligence and machine learning are expected to play a crucial role in threat detection, analysis, and response. Zero-trust architectures, which verify every user and device before granting access, will become increasingly important in securing sensitive data. Blockchain technology has the potential to enhance security by creating tamper-proof records and ensuring data integrity.
For example, blockchain-based supply chain management systems can help track software components, reducing the risk of malicious code infiltration. Furthermore, advancements in quantum computing could potentially break current encryption methods, necessitating the development of post-quantum cryptography.
Importance of Continuous Learning and Adaptation
The ever-changing threat landscape necessitates a commitment to continuous learning and adaptation within the cybersecurity community. Cybersecurity professionals must stay updated on the latest techniques, vulnerabilities, and emerging threats. This involves actively participating in training programs, attending conferences, and engaging in continuous professional development. Staying abreast of the latest research and development in the field is paramount.
Furthermore, collaborative efforts between organizations, researchers, and government bodies are essential for sharing knowledge and best practices to bolster defenses. Cybersecurity professionals must adapt to the dynamic nature of the threats and be prepared to constantly learn and refine their skills.
Illustrative Examples: Interview With Dr Arun Vishwanath On The Latest Cybersecurity Attacks

Real-world cybersecurity attacks paint a stark picture of vulnerabilities and the persistent need for robust defenses. Understanding these incidents, including the tactics used, the responses implemented, and the lessons learned, is crucial for mitigating future threats. This section delves into specific examples, highlighting the importance of incident reporting and swift response in the face of cyberattacks.
The SolarWinds Supply Chain Attack
The SolarWinds Orion platform attack demonstrated the devastating potential of a supply chain compromise. Attackers exploited a trusted software provider, SolarWinds, to gain access to numerous organizations’ networks. This sophisticated attack leverages the principle of trust, infiltrating a seemingly secure environment through a compromised third-party tool.
- Attacker Methods: Attackers inserted malicious code into the SolarWinds Orion update, which was downloaded and installed by various organizations. This allowed them to gain initial access and then move laterally throughout the victim networks. The attackers meticulously crafted their approach to exploit vulnerabilities in the update process.
- Affected Parties’ Measures: Organizations that were affected by the attack had to undertake extensive forensic investigations, identify compromised systems, and implement remediation strategies. These included patching vulnerabilities, changing passwords, and implementing security monitoring tools.
- Importance of Incident Reporting and Response: The SolarWinds incident highlighted the importance of robust incident response plans and timely reporting. Early detection and rapid response significantly minimized the impact of the attack. Collaboration and information sharing among organizations and with security researchers were vital in understanding the attack’s scope and in developing mitigation strategies.
The WannaCry Ransomware Attack
The WannaCry ransomware attack exploited a vulnerability in Microsoft’s Windows operating system, impacting thousands of organizations and individuals worldwide. The attackers leveraged a known vulnerability to quickly and broadly distribute malicious software, demanding payment for the release of encrypted data.
- Attacker Methods: Attackers leveraged a publicly known vulnerability to rapidly spread the ransomware through vulnerable systems. This attack exemplified the risk posed by unpatched systems and the speed with which a sophisticated attack can propagate.
- Affected Parties’ Measures: Organizations and individuals had to grapple with the encryption of their data and the potential loss of critical information. Recovering from the attack involved complex decryption efforts, sometimes requiring the payment of the ransom, which is not always successful. Ultimately, many organizations had to rebuild systems and restore data.
- Importance of Incident Reporting and Response: The WannaCry incident underscored the importance of proactive vulnerability management and patching. Organizations should prioritize patching known vulnerabilities as soon as possible to minimize the risk of exploitation. The incident also demonstrated the need for robust backup and recovery plans to mitigate the impact of data loss.
The NotPetya Malware Attack
The NotPetya attack is notable for its destructive nature and its potential for widespread disruption. It is categorized as a wiper malware, designed to corrupt data rather than simply encrypt it.
- Attacker Methods: NotPetya exploited vulnerabilities in the Windows operating system to spread rapidly, causing significant damage. It was designed to propagate automatically and delete or corrupt data on affected systems.
- Affected Parties’ Measures: Organizations had to deal with widespread data corruption and significant operational disruptions. Recovering from the attack often required rebuilding systems from backups and potentially replacing critical data.
- Importance of Incident Reporting and Response: The NotPetya attack highlights the importance of robust incident response plans and disaster recovery procedures. Organizations must anticipate and plan for disruptive attacks that may compromise not only data but also the entire operational infrastructure.
Key Takeaways
Dr. Vishwanath’s insights into the recent surge in cybersecurity attacks offer crucial takeaways for individuals and organizations. Understanding the evolving threat landscape and implementing robust defense strategies are paramount in mitigating risks. These takeaways provide actionable steps to enhance cybersecurity posture and safeguard against potential future threats.
Summary of Key Points
The interview highlighted several key points regarding the current cybersecurity landscape. The increasing sophistication of attacks, coupled with the growing attack surface, necessitates a proactive and multi-layered approach to cybersecurity. Dr. Vishwanath emphasized the importance of not just reacting to attacks, but also proactively identifying and mitigating vulnerabilities. Organizations and individuals alike need to prioritize security awareness and adopt best practices to safeguard sensitive information.
Key Insights for Enhancing Cybersecurity Posture
Effective cybersecurity is a multifaceted process. A strong cybersecurity posture requires a comprehensive strategy encompassing technology, processes, and people. Organizations should implement robust security measures and train their personnel on recognizing and responding to potential threats. Individual users also play a vital role in safeguarding their information. Their actions directly influence the overall security of the systems they use.
Organizational Cybersecurity Strategies, Interview with dr arun vishwanath on the latest cybersecurity attacks
- Proactive Vulnerability Management: Regular security assessments and penetration testing are critical for identifying and patching vulnerabilities before attackers exploit them. This proactive approach prevents potential breaches and minimizes damage.
- Multi-Factor Authentication (MFA): Implementing MFA adds an extra layer of security by requiring multiple verification methods to access sensitive data. This significantly reduces the risk of unauthorized access, even if a password is compromised.
- Security Awareness Training: Employee training programs should educate staff on phishing scams, social engineering tactics, and other common threats. This empowers employees to identify and avoid potential attacks.
- Incident Response Planning: Developing and regularly testing incident response plans helps organizations effectively manage and mitigate the impact of security breaches. Having a well-defined plan allows for a swift and organized response, minimizing potential damage.
Individual Cybersecurity Practices
- Strong Passwords: Using strong, unique passwords for each online account is essential. Utilizing password managers can aid in creating and managing complex passwords.
- Regular Software Updates: Keeping software, operating systems, and applications updated mitigates known vulnerabilities. This helps prevent attackers from exploiting outdated software.
- Phishing Awareness: Be wary of suspicious emails, messages, and links. Verify the authenticity of requests before clicking on links or providing sensitive information.
- Secure Wi-Fi Usage: Using a VPN (Virtual Private Network) when connecting to public Wi-Fi networks protects sensitive data from eavesdropping.
Cost-Benefit Analysis of Security Measures
| Security Measure | Potential Costs | Potential Benefits |
|---|---|---|
| Vulnerability Management | Software licenses, consultant fees, staff time | Reduced risk of data breaches, financial losses, reputational damage |
| Multi-Factor Authentication | Implementation costs, potential user friction | Enhanced security, reduced unauthorized access, improved compliance |
| Security Awareness Training | Training materials, instructor fees | Increased security awareness, reduced susceptibility to phishing attacks, improved overall security posture |
| Incident Response Planning | Planning and testing costs, potential downtime | Reduced impact of breaches, quicker recovery, minimized data loss, improved reputation |
Final Conclusion
The interview with Dr. Arun Vishwanath offered a comprehensive look at the current cybersecurity landscape. Dr. Vishwanath’s insights were invaluable in understanding the motivations, tactics, and vulnerabilities behind recent attacks. He highlighted the critical importance of proactive measures and continuous adaptation to stay ahead of the curve.
The discussion emphasized the interconnectedness of individuals, businesses, and infrastructure in facing these challenges. We learned about the devastating consequences of cyberattacks and the essential steps towards strengthening our cybersecurity defenses. Ultimately, the interview underscored the need for ongoing vigilance and collaboration to navigate the complex world of cybersecurity.
User Queries
What are some common misconceptions about cybersecurity?
Many believe that only large corporations are targets for cyberattacks. However, individuals and small businesses are increasingly vulnerable. Strong passwords and updated software are essential defenses for everyone.
What role does human error play in cybersecurity incidents?
Dr. Vishwanath emphasizes that human factors are often a significant weakness in cybersecurity. Social engineering tactics, such as phishing emails, rely on exploiting human vulnerabilities. Employee training and awareness programs are crucial.
What are the most effective ways to mitigate supply chain attacks?
The interview highlights the importance of robust security protocols throughout the entire supply chain. This includes scrutinizing third-party vendors and implementing multi-layered security measures.
How can small businesses afford effective cybersecurity measures?
Small businesses can implement cost-effective strategies like multi-factor authentication, strong password policies, and regularly updating software. Free resources and affordable cybersecurity tools are available.